U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Saturday, Dec. 2, 2006, at least 2,887 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,316 died as a result of hostile action, according to the military's numbers.
The AP count is four higher than the Defense Department's tally, last updated Friday at 10 a.m. EST.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casuality Count website
here.
FCC Chairman Moves to End AT&T Impasse
Jim Puzzanghera writes in The Los Angeles Times:
The chairman of the Federal Communications Commission moved Friday to break an impasse over approval of AT&T Inc.'s purchase of BellSouth Corp. by trying to force a commissioner who recused himself to cast the tie-breaking vote.
In a letter to congressional leaders, Chairman Kevin J. Martin said he had asked the FCC's general counsel to review Commissioner Robert M. McDowell's recusal. A fellow Republican, McDowell has declined to participate in the review of the deal because he had worked for a trade association of smaller phone companies that opposes the roughly $80-billion merger.
With McDowell on the sideline, the commission has been split evenly between Republicans and Democrats. Martin said he wanted the FCC to approve the deal unconditionally, and Republican Deborah Taylor Tate was expected to back him.
More
here.
Homeland Security 'Network of Networks' Faces Privacy Challenges
Shaun Waterman writes on Government Technology:
A new plan from the U.S. intelligence czar will use state police-run intelligence fusion centers as the hubs for a national network of officials from different agencies and levels of government sharing information about terrorism.
In a move likely to rattle privacy mavens, the three year plan for implementing the congressionally mandated Information Sharing Environment, or ISE, also lays out policy designed to ease sharing intelligence with foreign governments, and proposes to widen the definition of terrorism information that can be shared.
More
here.
New Hampshire GOP Settles Phone-Jamming Lawsuit
An AP newswire article by Kathy McCormack, via FoxNews.com, reports that:
The New Hampshire Democratic Party, which had sought compensation in an Election Day 2002 phone-jamming scheme, settled its lawsuit against the GOP for an undisclosed amount, state Republicans said Friday.
The announcement came just days before the case was expected to go to trial on Monday in Hillsborough County Superior Court.
Republicans had hired a telemarketing firm to place hundreds of hang-up calls to phone banks for the Democratic Party and the Manchester firefighters union, a nonpartisan group offering rides to the pools. Service was disrupted for nearly two hours.
More
here.
Nicotine Tech: Worker Fired for Smoking Off-Job
Outrageous.
Aaron Gouveia writes on Cape Cod Online:
Scott Rodrigues took a drug test in August when he started his new job as a lawn-care technician.
It came back negative for any and all illegal substances.
Then on Sept. 1, Rodrigues' 30th birthday, he was fired.
The Scotts Miracle-Gro Co., a multibillion-dollar corporation, terminated Rodrigues because his urine test turned up traces of nicotine. While smoking cigarettes is legal, Scotts implemented a policy earlier this year forbidding all employees from smoking both on and off the job.
More
here.
(
Props, Flying Hamster.)
Five Agencies Combine Efforts in Search for Kim Family
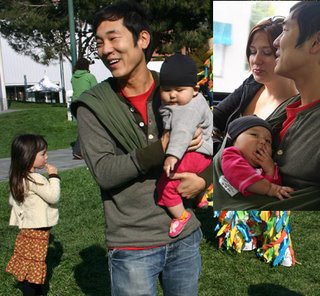
 James Kim and his daughters Penelope, 7, and Sabine, 7 months, went on a road trip to Oregon.
James Kim and his daughters Penelope, 7, and Sabine, 7 months, went on a road trip to Oregon.
Image source: San Francisco Chronicle / Kim Family Photo
Elizabeth Fernandez
writes in
The San Francisco Chronicle:
Authorities began an aerial search Friday in Oregon for four members of a San Francisco family who went on a Thanksgiving road trip to the Pacific Northwest and were last seen a week ago.
A command center was established in Salem, Ore., to coordinate the search efforts of five agencies -- the National Guard, the California Highway Patrol, the Coast Guard, the Oregon State Police and the Douglas County (Ore.) Sheriff's Department, authorities said.
More
here.
Seagate CEO: I Help People 'Watch Porn'
A Fortune magazine article by Jeffrey M. O'Brien, via CNN/Money, reports that:
Sitting at the arm of a tech CEO during a corporate dinner is rarely as interesting as you might imagine. Usually, the CEO stays on message throughout the meal as a PR flak hovers, smiles, nods and prods the conversation along. Just keep the drinks coming, guys.
Not so with Bill Watkins, the mercurial, salty-mouthed Texan who runs the $15 billion hard-drive king Seagate Technology. At a San Francisco dinner on Tuesday evening, he was candid about his company's ultimate mission: "Let's face it, we're not changing the world. We're building a product that helps people buy more crap - and watch porn."
More
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Friday, Dec. 1, 2006, at least 2,886 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,316 died as a result of hostile action, according to the military's numbers.
The AP count is three higher than the Defense Department's tally, last updated Friday at 10 a.m. EST.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casuality Count website
here.
Picture of the Day: Blair, Uk ID Card Protest, Hitler, etc.

Full story & links here, at 27B Stroke 6.
Enjoy. Or not...
Massive U.S. Terror Screening Program Draws Outrage
An AP newswire article by Michael J. Sniffen, via The Washington Post, reports that:
A leader of the new Democratic Congress, business travelers and privacy advocates expressed outrage Friday over the unannounced assignment of terrorism risk assessments to American international travelers by a computerized system managed from an unmarked, two-story brick building in Northern Virginia.
Incoming Senate Judiciary Chairman Sen. Patrick Leahy of Vermont pledged greater scrutiny of such government database-mining projects after reading that during the past four years millions of Americans have been evaluated without their knowledge to assess the risks that they are terrorists or criminals.
More
here.
China a Major Cyberthreat, U.S. Commission Warns
Josh Rogin writes on FCW.com:
China is fielding information warfare units and developing anti-satellite capabilities aimed at countering U.S. military technology, according to a U.S. congressional commission.
China’s cyberwarfare strategy has switched from a defensive to an offensive posture, with the goal of attacking enemy networks and denying adversaries access to information, said the U.S.-China Economic and Security Review Commission (USCC) in its annual report, released Nov. 16. Chinese strategy focuses on U.S. systems that perform command and control or deliver precision weapons, the report states.
More
here.
Freedom Wireless Sues Five Companies in Patent Case
Via Reuters.
Wireless technology company Freedom Wireless Inc. said on Friday it sued five wireless carriers and services providers -- including Cingular Wireless and Ericsson -- over patent infringement charges.
The company said it filed two patent infringement lawsuits in federal court in Texas against Cingular and Ericsson Inc., and another targeting Alltel Corp., Comverse Technology Inc. and VeriSign Inc..
More
here.
FBI Taps Cell Phone Mic as Eavesdropping Tool
Declan McCullagh and Anne Broache write on C|Net News:
The FBI appears to have begun using a novel form of electronic surveillance in criminal investigations: remotely activating a mobile phone's microphone and using it to eavesdrop on nearby conversations.
The technique is called a "roving bug," and was approved by top U.S. Department of Justice officials for use against members of a New York organized crime family who were wary of conventional surveillance techniques such as tailing a suspect or wiretapping him.
More
here.
Real Security: Spy Case Raises Questions on Radiation Response
A Reuters newswire article, via MSNBC, reports that:
If the poisoning of one man can pose such a serious test for the British government, how would it handle a full-scale radiological attack?
A week after former Russian spy Alexander Litvinenko was killed by the radioactive poison Polonium 210, some security analysts see major flaws in the emergency response system and question its ability to cope with a larger crisis.
Among their chief concerns is the three weeks it took for doctors to establish that the dying Litvinenko had been poisoned by a nuclear substance.
More
here.
Toon: Holiday Anxiety
Click for larger image.
Update: Mystery Hacker Breaks Into Naval War College Computer System
Maddy Sauer writes on ABC News' "The Blotter":
The Web site and computer system at the Naval War College have been offline for more than two weeks following a mysterious hacking incident. The hacker broke into unclassified sections of the network, which include the e-mail system for staff and students, most of which are senior level members of the military.
While this is not the first time a Naval computer system has been taken offline due to an intrusion, one expert says two weeks is a long time for the system to be down.
More
here.
Vietnam Jails S. Korean for Setting up VoIP Services
An AFP newswire article, via Yahoo! News, reports that:
A Vietnamese court has sentenced a South Korean businessman to 16 years' jail for illegally setting up internet-based telephone services in the communist country, a justice official said.
Ko Don Chul, 46, was found guilty of setting up the telecommunications systems in five locations in Hanoi and Ho Chi Minh City that used the Internet and avoided government telephone charges on overseas calls, the official said.
The Hanoi people's court on Thursday sentenced Ko after a two-day trial in which prosecutors claimed his activities had led to losses of over 1.1 million dollars in government revenues, said a court official asking not to be named.
More
here.
Leahy: Terror Screening Oversight a Must
An AP newswire article, via SFGate.com, reports that:
The incoming Senate Judiciary chairman pledged greater scrutiny Friday of computerized government anti-terrorism screening after learning that millions of Americans who travel internationally have been assigned risk assessments over the last four years without their knowledge.
"Data banks like this are overdue for oversight," said Sen. Patrick Leahy, D-Vt., who will take over Judiciary in January. "That is going to change in the new Congress."
The Associated Press reported Thursday that millions of Americans and foreigners crossing U.S. borders in the past four years have been assessed by the computerized Automated Targeting System, or ATS, designed to help pick out terrorists or criminals.
The travelers are not allowed to see or directly challenge these risk assessments, which the government intends to keep on file for 40 years. Under specific circumstances, some or all data in the system can be shared with state, local and foreign governments and even some private contractors.
More
here.
Australia: Telstra Attacked Over 'Pathetic' Broadband Speed
Paul McIntyre writes in The New Zealand Herald:
After the stunning A$15.3 billion (NZ$17.6 billion) sale of the third tranche of Telstra shares a few weeks back, the federal Government and the competition regulator were in another punch-up this week with the telco giant over pathetic broadband internet speeds.
Telstra refuses to run an ADSL2+ network five to 40 times faster than it does because it claims it needs regulatory certainty to ensure rivals can't piggy-back its infrastructure too cheaply.
But that argument came in for a blistering attack by the head of the competition watchdog, Graeme Samuel, who accused the telco of using subterfuge on regulation for a broader agenda.
More
here.
Defense Tech: DoD Eyes Ex-CIA Strategist For Key Post
An InsideDefense.com article by Jason Sherman, via Military.com, reports that:
The Pentagon may tap the principal architect of CIA efforts to drive the Soviet army from Afghanistan in the 1980s to oversee the Defense Department’s special operations policy and conventional military transformation efforts, according to defense officials.
Sources say the White House is considering Michael Vickers, the director of strategic studies at the Center for Strategic and Budgetary Assessments, to be assistant secretary of defense for special operations/low-intensity conflict and interdependent capabilities, a newly designed post that is expected to have wide-ranging influence in shaping counterterrorism strategies and weapon system investment decisions.
More
here.
Feds Crack Down on Teen, Preteen 'Model' Websites
Mike Brunker writes on MSNBC:
The operators of dozens of teen and preteen “modeling sites” that critics say are nothing more than eye candy for pedophiles have been indicted by a federal grand jury in Alabama for allegedly trafficking in “visual depictions of minors engaging in sexually explicit conduct.”
The indictment, unsealed this week in Birmingham, Ala., charges Webe Web Corp. of Fort Lauderdale, Fla., and its principals, Marc Evan Greenberg and Jeffrey Robert Libman, with 80 counts of conspiracy and interstate trafficking of the images of teen and preteen girls on dozens of Web sites operated by the company. Both men were arrested Tuesday in Fort Lauderdale and are due to be arraigned on Friday.
Photographer Jeff Pierson of Brookwood, Ala., also was charged with two counts of using a computer to “transport child pornography in interstate commerce” from January 2003 through 2004. Authorities said Pierson is cooperating with prosecutors.
More
here.
World AIDS Day 2006

Lawsuit Seeks Data on Covert DHS Program
Via UPI.
Students at the Yale Law School in New Haven, Conn. are suing the federal government for more information about Operation Front Line.
The Hartford Courant reported on Nov. 29 that Operation Front Line is a classified program conducted by the Department of Homeland Security to gather information on immigrants considered national security threats.
More
here.
TransUnion Credit Bureau Security Breached
Via KXAN.com.
TransUnion Credit Bureau is investigating who was able to get into their database and illegally download hundreds of people's personal information.
The victims are now being told they'll have to monitor their credit report every month to make sure no one is abusing their identity.
There are three major credit bureaus in this country. They have access to all of our credit information.
According to the information we have, four different scam companies across the country got more than 1,700 people's credit information after someone obtained the TransUnion log in information from a courthouse in Kingman, Arizona.
More
here.
Botnets Could Hack Any Site
Paul Kedrosky writes on Seeking Alpha:
There is a story floating around that U.S. financial firms have been warned of an al Qaeda cyber attack today. According to the story, the attack would be directed against banks and online stock trading firms.
Could al Qaeda take down a few banks and brokers?
Let's start by assuming that an online broker/bank has somewhere between 100 mbps and 1Gbps in bandwidth. Let's further assume that you need not saturate that entire pipe on your own, that, for the sake of argument, you need only get to 25%, assuming normal traffic flows. In other words, you'd need to produce a sustained 250 mbps, assuming 1 Gbps pipes to an eTrade.
For sure al Qaeda would need a few computers to do that sort of thing. And they'd need to have varying IP addresses, or they'd be blocked almost immediately.
So, could al Qaeda do it? You bet: via botnets. The largest botnet that has been taken down so far was 120,000 nodes, which is far more than you'd need for this job. A typical hacker estimate is that you can take down your average corporate site with a 500 to 1,000-machine botnet, and so let's say you need to rent access to a 5,000 to 10,000-machine botnet to do a bank or broker. [In case you're curious, large botnets have been shown to suck up as much as 40 Gbps in bandwidth.]
More
here.
Romanian Indicted for Hacking U.S. Computers
An AP newswire article, via Yahoo! News, reports that:
A Romanian national was indicted on charges of hacking into more than 150 U.S. government computers, causing disruptions that cost NASA, the Energy Department and the Navy nearly $1.5 million.
The federal indictment charges Victor Faur, 26, of Arad, Romania with nine counts of computer intrusion and one count of conspiracy. He faces up to 54 years in prison if convicted of all counts, said Thom Mrozek, spokesman for the U.S. attorney's office.
Faur was being prosecuted by authorities in Romania on separate computer hacking charges, Mrozek said Thursday, and will be brought to Los Angeles upon resolution of that case. It was not known whether Faur had retained a lawyer in the United States.
The U.S. government alleges Faur was the leader of a hacking group called "WhiteHat Team," whose main goal was to break into U.S. government computers because they are some of the securest in the world.
More
here.
New Rules Compel Firms to Track E-Mails
An AP newswire article, via The Washington Post, reports that:
U.S. companies will need to keep track of all the e-mails, instant messages and other electronic documents generated by their employees thanks to new federal rules that go into effect Friday, legal experts say.
The rules, approved by the Supreme Court in April, require companies and other entities involved in federal litigation to produce "electronically stored information" as part of the discovery process, when evidence is shared by both sides before a trial.
More
here.
Security Of Electronic Voting Is Condemned
Cameron W. Barr writes in The Washington Post:
Paperless electronic voting machines used throughout the Washington region and much of the country "cannot be made secure," according to draft recommendations issued this week by a federal agency that advises the U.S. Election Assistance Commission.
The assessment by the National Institute of Standards and Technology, one of the government's premier research centers, is the most sweeping condemnation of such voting systems by a federal agency.
More
here.
MPAA Kills Anti-Pretexting Bill
What a crock.
Ryan Singel writes on Wired News:
A tough California bill that would have prohibited companies and individuals from using deceptive "pretexting" ruses to steal private information about consumers was killed after determined lobbying by the motion picture industry, Wired News has learned.
The bill, SB1666, was written by state Sen. Debra Bowen, and would have barred investigators from making "false, fictitious or fraudulent" statements or representations to obtain private information about an individual, including telephone calling records, Social Security numbers and financial information. Victims would have had the right to sue for damages.
The bill won approval in three committees and sailed through the state Senate with a 30-0 vote. Then, according to Lenny Goldberg, a lobbyist for the Privacy Rights Clearinghouse, the measure encountered unexpected, last-minute resistance from the Motion Picture Association of America.
"The MPAA has a tremendous amount of clout and they told legislators, 'We need to pose as someone other than who we are to stop illegal downloading,'" Goldberg said.
More
here.
Thought of the Day

Home Computers, PDAs Targeted in New Electronic Discovery Rules
Via Government Technology News.
Home computers, text messages, PDAs and Internet service providers may be open to discovery during litigation because of changes in federal law, according to attorney Barney Robinson of Butler Snow, O'Mara, Stevens & Cannada, PLLC. "Mountains of data will be at risk, so companies need to take action now," he said.
The changes in the law, which take effect December 1, 2006, widen the scope of electronic discovery, handing plaintiff attorneys a powerful new too, according to Butler Snow in a release.
More
here.
C|Net Editor James Kim, Family Missing
Leslie Katz
writes on the
C|Net Gadgets Blog:
The 35-year-old Kim, his wife Kati, and daughters Penelope (4 years) and Sabine (7 months) left their home in San Francisco last week on a road trip to the Pacific Northwest. They were last seen on Saturday, November 25, in Portland, Ore., according to the San Francisco Police Department, which has opened a missing persons' investigation. They were driving a 2005 silver Saab station wagon with California personalized plates of "DOESF."
Those with information about the Kim family's whereabouts are asked to contact the SFPD immediately--at 415-558-5508 during normal business hours and at 415-553-1071 after-hours. The Portland Police Department can be reached at 503-823-4000.
More
here:
Data on U.S. Military's Iraqi Operations Leaked onto Internet
Via Breitbart News.
Internal data such as information concerning U.S. military operations in Iraq have recently been leaked to the Internet from a privately owned personal computer of an Air Self-Defense Force member loaded with a file sharing software, ASDF investigations have shown.
The information on transport operations and personnel deployment of the U.S. military in Iraq in June and July was given as confidential data from the U.S. military and its leak could have posed a serious threat to the safety of foreign troops operating in Iraq. The ASDF said, "The situation has changed from the time then and it will therefore have no impact."
An analysis of the hard disk drive that included the information indicated the data were leaked on Friday, the investigations showed.
More
here.
San Francisco Nears WiFi Deal
Sarah Jane Tribble writes in The Mercury News:
San Francisco's wait for citywide wireless is nearing an end, a city official said Thursday.
Chris Vein, director of the city's technology office, said he expects contract negotiations with the joint Google and Earthlink team that was awarded the nearly 50-square-mile project will end within the month. The city's board of supervisors should begin reviewing the contract in January and, if approved, installation will begin next year, he said.
More
here.
Orwellian Nightmare: Man Mistakenly Arrested as Terrorist Suspect Wins Case, Apology
Bryan Denson writes on The Oregonian:
Brandon Mayfield, the Portland-area lawyer wrongly linked to the deadly Madrid, Spain, train bombings of 2004, accepted a $2 million settlement Wednesday in his lawsuit against the federal government, setting up a legal showdown over the constitutionality of the USA Patriot Act.
The United States will pay the convert to Islam $1.9 million for the emotional toll he suffered from two weeks of imprisonment as a material witness to a crime he knew nothing about, with another $100,000 going to his wife and three children for their suffering.
The government also agreed to destroy all materials seized from Mayfield's home and office. And it agreed to issue the 40-year-old lawyer another apology for FBI foulups that matched him to a fingerprint found in Madrid, leading to his investigation as a possible terrorist.
More
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Thursday, Nov. 30, 2006, at least 2,885 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,314 died as a result of hostile action, according to the military's numbers.
The AP count is four more than the Defense Department's tally, last updated Thursday at 10 a.m. EST.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casuality Count website
here.
ATM Systems Called 'Unsafe'
Bob Sullivan writes on The Red Tape Chronicles:
Researchers who work for an Israeli computer security company say they have discovered a fundamental weakness in the system that banks use to keep debit card PIN codes secret while they are transported across bank networks – a flaw that they say could undermine the entire debit card system.
The U.S. Secret Service is investigating the matter, and MSNBC.com obtained a memo compiled by the agency that indicates that organized criminals are systematically attempting to subvert the ATM system and unscramble encrypted PIN traffic.
The report has ignited a debate within the banking industry, with many financial industry experts downplaying the seriousness of the flaw and outside experts divided on its implications. But there is no disputing the impact that such a hack would have if successful.
More
here.
U.S. Commerce Department Extends .com Contract with VeriSign
Grant Gross writes on InfoWorld:
The U.S. Department of Commerce (DOC) has approved an agreement for VeriSign Inc. to continue to operate the .com domain for six more years, despite objections about pricing and security.
The department has approved the .com agreement submitted by the Internet Corporation for Assigned Names and Numbers (ICANN), the nonprofit organization that oversees the Internet’s technical infrastructure, VeriSign announced Thursday. The current .com contract expires in late 2007.
More
here.
TSA Employees Missing Hundreds of Uniforms and Badges
Via WMC-TV (Memphis).
Federal records obtained by our sister station in Nashville show screeners across the country have lost hundreds of their uniforms and credentials over the past two years. That includes 15 at both Memphis and Nashville International Airports.
A total of 88 were gone from Atlanta's airport.
It's something that disturbs aviation security expert Karl Delaguerra.
"No terrorist act is conducted without prior surveillance and that's been proven for years," he says.
Getting past security might not be a problem either. Undercover cameras have caught people in TSA uniforms breezing through. One man was seen entering a no-entry zone.
More
here.
(
Props, Flying Hamster.)
Off Topic: Flying Spaghetti Monster Holiday Pageant

Pennsylvania DMV Computers with Personal Data Stolen
An AP newswire article by Michael Rubinkam, via The Boston Globe, reports that:
Thieves stole equipment from a driver's license center and got away with computers containing personal information on more than 11,000 people, state officials said Thursday.
The thieves got a camera and a printer during the break-in late Tuesday, plus enough card stock and laminate to make about 750 fake licenses, said Betty Serian, Pennsylvania Department of Transportation deputy secretary, at a news conference Thursday.
They also stole two computers containing data on 11,384 people.
The information included names, addresses, dates of birth, drivers' license numbers and at least partial Social Security numbers. The data included complete Social Security numbers for 5,348 people, officials said.
More
here.
Report: U.S. Navy Satcom Performance Impedes Warfighters
Bob Brewin writes on FCW.com:
The performance of Navy shipboard satellite systems operating in the super high-frequency (SHF) and extremely high-frequency (EHF) bands is inadequate to support warfighting needs, according to a message the service sent in September.
The Navy sent the message internally to all commands but did not publicly release it. It summarizes the service’s top 10 command, control, communications and computer (C4) priorities and problems.
The message, which Federal Computer Week obtained this week, states that poor antenna reliability hampers EHF and SHF satellite communications. A lack of spare parts frequently prolongs outages on Navy ships.
More
here.
Gapingvoid: What a Coincidence...
Via gapingvoid.com. Enjoy!
Judges Fear Dangers of Online 'Rat' Site
An AP newswire article by Matt Apuzzo, via The Boston Globe, reports that:
Police and prosecutors are worried that a Web site claiming to identify more than 4,000 informants and undercover agents will cripple investigations and hang targets on witnesses.
The Web site, WhosaRat.com, first caught the attention of authorities after a Massachusetts man put it online and named a few dozen people as turncoats in 2004. Since then, it has grown into a clearinghouse for mug shots, court papers and rumors.
More
here.
ICANN Says 'No' to .travel Typo Search
Nate Mook writes on BetaNews:
The Internet Corporation for Assigned Names and Numbers (ICANN) has rejected a request by the operator of the .travel top-level domain name to redirect all mis-typed and non-existent Web addresses to a search service, much like VeriSign's controversial "Site Finder."
Tralliance, which was appointed by ICANN -- the non-profit group that governs the Internet DNS system -- to managed .travel registrations, wanted to direct users to a page that contained travel-related search results for the term they had typed in, along with offering to register the name if they were eligible. The .travel domains are restricted to companies in the travel industry.
More
here.
U.S. Warns of Possible al-Qaida Cyber Attack
Via MSNBC.
The U.S. government has notified U.S. private financial services of a call by the al-Qaida terrorist network for a cyber attack against U.S. online stock trading and banking Web sites beginning Friday, officials said.
Almost immediately, however, other officials downplayed the risk of any danger to U.S. financial institutions.
NBC News' Pete Williams reported that a unit of the Homeland Security Department sent out an advisory to banks, saying that a jihadist Web site posted an “aspirational” item, which said it would be a good thing to carry out cyber attacks on the U.S. financial industry to retaliate for abuses at the Guantanamo Bay prison facility.
More
here.
Vista Vulnerable to Malware from 2004
Righto. "The most secure OS ever..."
Tom Espiner writes on ZDNet UK:
Microsoft's Vista may be vulnerable to at least three pieces of widespread malware, two of which date back to 2004 , according to security vendor Sophos.
At least three well-known Internet worms -- labelled Stratio-Zip, Netsky-D and MyDoom-O by Sophos -- are able to execute on the OS, according Sophos.
These worms comprise 39.7 percent of all malware currently in circulation, according to the security vendor. The MyDoom and Netsky variants were first detected back in 2004.
More
here.
Network Attack Disables U.S. Naval War College - UPDATE
Josh Rogin writes on FCW.com:
Computer and e-mail systems are off-line at the Naval War College following a network intrusion Nov. 15. After the attack, the Defense Department raised its information warfare awareness level to Information Condition (Infocon) 4.
Navy officials declined to comment on the source of the attack.
The attack was an insolated incident and has not affected other parts of DOD, [an official] said. Meanwhile, the college’s systems have been removed from DOD’s Global Information Grid so that investigators can examine the extent of the intrusion and upgrade firewalls and other security measures, [the official] said.
More
here.
Update 11/30 17:45: Bill Gertz at The Washington Times alludes to Chinese hackers
here.
American Travelers to Get Secret 'Risk Assessment' Scores
Via The EFF.
An invasive and unprecedented data-mining system is set to be deployed on U.S. travelers Monday, despite substantial questions about Americans' privacy. In comments sent to the Department of Homeland Security (DHS) today, the Electronic Frontier Foundation (EFF) asked the agency to delay the program's rollout until it makes more details available to the public and addresses critical privacy and due process concerns.
The Automated Targeting System (ATS) will create and assign "risk assessments" to tens of millions of citizens as they enter and leave the country. Individuals will have no way to access information about their "risk assessment" scores or to correct any false information about them. But once the assessment is made, the government will retain the information for 40 years -- as well as make it available to untold numbers of federal, state, local, and foreign agencies in addition to contractors, grantees, consultants, and others.
More
here.
UK Hacking Case Leads to Calls for Tougher Privacy Laws
Sandra Laville and Owen Gibson write on The Guardian.co.uk:
Revelations of a sustained bugging campaign targeting two government ministers, a newspaper editor, an England footballer and a string of celebrities prompted calls yesterday for tougher sentences for the buying and selling of confidential personal data.
The government's information commissioner spoke out after Clive Goodman, the News of the World's royal editor, admitted at the Old Bailey yesterday to tapping into mobile phones belonging to aides of the Prince of Wales and his son, Prince William, over a 20 month period.
More
here.
Programming Note
I've been very, very busy the past two days and have not had much of an opportunity to post -- my apologies.
I will try to get caught up this evening...
- ferg
Can The U.S. Government Shutdown A Website Without A Court Order?
Ryan Singel has been a busy boy over on 27B Stroke 6 today:
Can the feds order a take down of a website without getting a court order?
That's exactly what the Transportation Security Administration seems to have done with security researcher Christopher Soghoian's boarding pass generator. That was taken down by his hosting provider DreamHost two days after it was posted, presumably after the government delivered a copy of the takedown notice handed to him by FBI agents (Soghoian's home was raided the next day, but he is not being prosecuted).
Beyond this
initial nugget, also see
here,
here, and
here.
29 November 1777: Happy Birthday, San José
 Image source: Wikipedia, © Matthew Hendricks
Image source: Wikipedia, © Matthew Hendricks
Via Wikipedia.
San José is the third-largest city in California, and the tenth-largest in the United States. It is the county seat of Santa Clara County. For the past several years, it has held the title of The Safest Big City in America. San Jose is located in Silicon Valley, at the south end of the San Francisco Bay. With a population of 953,679, San Jose is the largest city in Northern California.
Originally known as El Pueblo de San José de Guadalupe, it was founded on November 29th, 1777 as the first town in the Spanish colony of Nueva California, which later became Alta California. The city served as a farming community to support Spanish military installations at San Francisco and Monterey. After California gained statehood in 1850, San Jose served as its first capital.
After over 150 years as an agricultural center, increased demand for housing from soldiers and other veterans returning from World War II and starting families, as well as aggressive expansion during the 1950s and 1960s led to San Jose being a bedroom community for Silicon Valley in the 1970s, which attracted more businesses to the city. By the 1990s, San Jose's central location within the booming technology industry in the area earned the city the nickname as the Capital of Silicon Valley.
On April 3, 1979, the city council adopted San José as the spelling of the city name on the city seal and official stationery; however, the name is still more commonly spelled without the diacritical mark. The official name of the city is The City of San José.
More here.
AT&T, Wal-Mart Team-Up to Sell DSL
Leslie Cauley writes on USA Today:
AT&T will start promoting its high-speed Internet service Wednesday in 570 Wal-Mart stores across the phone company's 13-state footprint.
The Wal-Mart deal is the latest partnership for the carrier that now has 4,000 retail outlets for its communications products including voice, wireless, high-speed data and video.
More
here.
Gapingvoid: Crude, But Effective
Via gapingvoid.com. Enjoy!

New Charges in Pellicano Wiretapping Case
An AP newswire article, via The Boston Globe, reports that:
A former phone company employee acquitted in September of perjury has been indicted by a federal grand jury on similar charges stemming from the wiretapping case against Hollywood private investigator Anthony Pellicano.
The grand jury returned the three-count indictment against Joann Wiggan, 52, on Nov. 22 but it wasn't released until Tuesday by the U.S. attorney's office. If convicted of the three perjury counts, Wiggan faces a maximum of 15 years in prison.
An arraignment has yet to be scheduled.
Previous updates
here,
here, and
here.
More
here.
Tipping of the Scales: Judge Strikes Bush's Terror List
An AP newswire article by Linda Deutsch, via SFGate.com, reports that:
A federal judge struck down President Bush's authority to designate groups as terrorists, saying his post-Sept. 11 executive order was unconstitutionally vague, according to a ruling released Tuesday.
The Humanitarian Law Project had challenged Bush's order, which blocked all the assets of groups or individuals he named as "specially designated global terrorists" after the 2001 terrorist attacks.
"This law gave the president unfettered authority to create blacklists," said David Cole, a lawyer for the Washington, D.C.-based Center for Constitutional Rights that represented the group. "It was reminiscent of the McCarthy era."
More
here.
Federal Reserve E-Banking System Outages
Brian Krebs writes on Security Fix:
A system widely used by U.S. banks to process large volumes of payroll, credit and debit card transactions experienced intermittent outages on Monday and Tuesday, possibly due to some sort of malfunction or communications failure in portions of the Federal Reserve's "automated clearing house" (ACH) network, Security Fix has learned.
Security Fix received an anonymous tip from an individual who claimed to work at a mid-sized bank that experienced trouble transferring ACH files across the Fed's network between 10:00 p.m. ET and 3:00 a.m. ET on Nov. 27 and 28. The source said a Federal Reserve technician reported that the problem was affecting numerous financial institutions across the country on Monday.
More
here.
Oracle's Claim That is 'Leading the Industry' in Plugging Security Holes is Greeted with Chuckles - UPDATE
Tom Sanders writes on vnunet.com:
Oracle has lashed out against security experts who criticized the company's security record.
The database vendor is "leading the software industry in terms of responsible development and security," charged Eric Maurice, manager for security in Oracle's global technology business unit in a posting on a company blog.
More
here.
UPDATE 11/28 20:15 PST: Apparently, the "Week of Zero-Day Oracle Bugs"
has been canceled.
Jack Cafferty on the DoJ Investigation of Warrantless Eavesdropping

We love ya, Jack.
Via Crooks and Liars.
When The Cafferty File starts off with Jack saying "the following story comes from the land of make believe or believe-it-or-not", you know what follows is going to be ridiculous and todays 4 o'clock question was no exception.
More here.
Venezuelan Election Using Paper Trail To Verify E-Voting Is Accurate
Mike Masnick writes on techdirt.com:
While some say that it's impossible to have a secure and accurate election using e-voting machines, having some sort of paper trail backup certainly goes a long way towards relieving the biggest fears associated with e-voting machines.
While we don't yet have them in the US, Venezuela's national election this coming weekend will have a verifiable paper trail associated with each voting machine.
More
here.
Report: U.S. DoD Investigates YouTube Video of U.S. Troops
Greg Sandoval writes on the C|Net Media Blog:
The U.S. Department of Defense is investigating at least two video clips that appear to show American soldiers in an unfavorable light during contacts with Iraqi children, according to a report in the British newspaper, the Metro.
A clip found on YouTube titled "Iraqi Kid Runs For Water" appears to show U.S. soldiers taking delight in watching children chase their truck in the hope the soldiers will make good on their offer of a water bottler.
"You want some water? Keep running," shouts a soldier, who laughs and asks, presumably whoever is taping the scene "Are you getting this?"
Another video features a soldier complaining about orders forbidding him from using deadly force against rock-throwing children.
More
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Tuesday, Nov. 28, 2006, at least 2,881 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,308 died as a result of hostile action, according to the military's numbers.
The AP count is one more than the Defense Department's tally, last updated Tuesday at 10 a.m. EST.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casuality Count website
here.
Universal to Seek Money for Each iPod Sold
Nate Anderson writes on ARS Technica:
And so it begins. Universal Music Group exec Doug Morris told the Reuters Media Summit that his company is interested in receiving a cut of the profits from each iPod sold.
Universal believes that much of the music on portable players is illegal, and the company argues that it deserves a share of the profits from such devices in order to make up for the money lost in album sales.
More
here.
Politics: 1 Picture > 1K Words

Apple Patches 31 Security Holes
Brian Krebs writes on Security Fix:
Apple Computer today released software updates to fix at least 31 separate security flaws in computers powered by different versions of its Mac OS X operating systems.
Users can download the free updates using OS X's Software Update feature, or directly from Apple Downloads.
More
here.
U.S. Navy Eyes Fighting in Cyberspace
An InsideDefense.com article by Rati Bishnoi, via Military.com, reports that:
Chief of Naval Operations Adm. Michael Mullen has tasked an exclusive strategy development group with creating new concepts that will help the service fight adversaries in cyberspace, Inside the Pentagon has learned.
In an Oct. 16 memorandum, Mullen calls on the Strategic Studies Group to give him a "high-level blueprint that encompasses your longer-term view, as well as a roadmap that includes immediately actionable steps -- operational, process, and technological -- that our Navy may take to begin developing the capabilities" needed to master the cyberspace warfare domain in the next 25 years.
The one-page document is addressed to the group's director, retired Adm. James Hogg, and is titled "Strategic Studies Group XXVI Theme -- 'Fighting in Cyberspace in 2030.'"
More
here.
1,245 Secret CIA Flights That Never Happened
Brian Ross and Maddy Sauer report on ABC News' "The Blotter":
The CIA flew 1,245 secret flights into European airspace, according to a European Parliament draft report obtained by ABC News.
The report is the result of a year-long investigation into secret CIA "extraordinary rendition" flights and prisons in Europe.
No European country has officially acknowledged being part of the program.
More
here.
Polonium-210 For Sale On The Web
Antone Gonsalves writes on InformationWeek:
The radioactive material that killed a former Russian spy in Britain can be bought on the Internet for $69.
Polonium-210, which experts say is many times more deadly than cyanide, can be bought legally through United Nuclear Scientific Supplies, a mail-order company that sells through the Web, based in Sandia Park, N.M. Chemcial companies sell the Polonium-210 legally for industrial use, such as removing static electricity from machinery. United Nuclear claims that it's "currently the only legal Alpha source available without a license."
More
here.
Google Search Device Flaw Leaves Sites Open to Phishing Attacks
Ericka Chickowski writes on SC Magazine Online:
Hackers and security experts made public a vulnerability in Google's search appliances that is leaving hundreds of major organizations such as the U.S. Food and Drug Administration, Stanford University and the National Hockey League open to phishing attacks.
The flaw exposes websites that use Google Search Appliance and Google Mini devices. It is a cross-site scripting (XSS) error in the systems' Unicode Transformation Format (UTF) character encoding that makes it possible for hackers to create malicious links that appear to point to trusted sites.
More
here.
New Version of Skype Now Even Harder to Detect
John E. Dunn writes on TechWorld:
Skype-blocking companies have been scrambling to update their products after the recent release of a new version of the software that is even harder to detect and block.
The beta of version 3.0 was made available only two weeks ago and, as expected, the client has been re-engineered to make its presence on network traffic tougher to spot, according to leading Skype-blocking outfit iPoque.
More
here.
Blowing Up Scientific Equipment in the Name of Security
Jeffrey W. Peters writes in The Minneapolis Star Tribune:
Anne Jefferson has a piece of advice for travelers: Be sure to check the trunk of your rental car.
Jefferson, 27, a Winona native, recently minted Ph.D. and researcher in the geosciences department at Oregon State University, concluded a combined business and holiday trip to Minnesota on Sunday, dropping off a rental car at Minneapolis-St. Paul International Airport before boarding a plane to Portland, Ore., with her husband.
By the time they arrived there, armed officers were waiting for them, and in the Twin Cities, portions of the Lindbergh terminal parking ramp had been closed for about two hours after authorities found a suspicious looking device in the spare tire compartment of the couple's rental car.
It was actually equipment that Jefferson had been using in her research on water temperatures in stream channels. She intended to mail it back to Oregon, but she just forgot about it.
Officers with the Bloomington Police Department bomb squad destroyed it.
More
here.
Boarding Pass Hacker Breaks Silence
Image source: Boing Boing
Brian Krebs
writes on
Security Fix:
Chris Soghoian, the Indiana University doctoral student whose online demonstration of serious flaws in airport security prompted an FBI investigation, broke his silence this week after the government terminated its investigation into the matter.
Soghoian had refused to talk to the media ever since the FBI visited his home in Bloomington, Ind., on Oct. 27 and carted away computers and other equipment. The federal action came in response to Soghoian's decision to post a tool on his Web site that would allow someone to print a fake boarding pass that could be used to evade the "no-fly" list -- a key government tool in keeping suspected terrorists off of airplanes.
In an interview with Security Fix on Saturday, Soghoian said he was ready to set the record straight now that the FBI had ended its investigation and the local U.S. attorney had declined to press charges. A spokesperson for the FBI's Indianapolis field office confirmed that the investigation was closed on Nov. 14.
More
here.
Hacker Redirects Bank Customers To Phony Site
Via KMBC-TV (Kansas City).
More than 100 people who went online Friday to do some banking wound up victims of a scam, officials said.
Community America Credit Union confirmed to KMBC that a hacker managed to redirect people from the company's Web site to a phony site.
Community America said it caught the intrusion within a few minutes, but about a dozen people accessed the phony site.
More
here.
(
Props, Flying Hamster.)
Arbor: IRC Bot attacking Symantec Overflow
Jose Nazario has a great write-up:
Back in May of this year, Symantec released an avisory entitled SYM06-010: Symantec Client Security and Symantec AntiVirus Elevation of Privilege. Those that took the time to read it beyond the title noticed that this isn’t just a local privilege elevation exploit. It’s an out and out remote stack overflow using a specific service (TCP port 2967).
We started tracking possible exploit activity for this vulnerability in early June using an ATF policy to detect scans and exploit, with our thinking that someone would surely take an interest. Activity for this policy quickly dropped off our radar, buried underneath some juicy Windows and VNC holes that people focused on. We didn’t see many scanners for this service, and only a burst of a scan early last week.
That is, until now, in late November, when we see a bot using an exploit for this (and lots of people are curious). We had a look at the bot, and found that it’s a new exploit plugin for a garden variety SDBot. This thing’s a beast! It’s huge, not unlike a bloated bot that someone’s thrown everything into.
More
here.
UK: Voluntary Code for Blogs 'Needed'
Via The BBC.
Blogs and other internet sites should be covered by a voluntary code of practice similar to that for newspapers in the UK, a conference has been told.
Press Complaints Commission director Tim Toulmin said he opposed government regulation of the internet, saying it should a place "in which views bloom".
But unless there was a voluntary code of conduct there would be no form of redress for people angered at content.
He spoke during a session on free speech at a London race conference.
More
here.
Quote of the Day: Michael Penkala
"When they let us in the lobby there at Wal-Mart, I was on the floor coughing up blood and telling the workers to take the wallet out of my pocket and give it to my friends so they could continue waiting in line and purchase the PS3s. For some reason I wasn't thinking about my wound, I was all about those PlayStations."
- Michael Penkala, who was first in line at a Wal-Mart store in Putnam, Connecticut, waiting with three friends for Sony's next-generation game console to go on sale. Penkala was shot in the chest by a shotgun blast when he refused to give a robber the $2,600 he had in his possession.
Gingrich Says U.S. Government May Have To Limit Free Speech In Terror War

Un-freeking-believable.
This guy either has industrial-sized balls, or is a complete idiot.
Or both.
Via WCSH6.com.
Former House Speaker Newt Gingrich used a New Hampshire event dedicated to freedom of speech to say the United States will have to re-examine that constitutional right as it fights terrorism.
Speaking in Manchester Monday night, Gingrich said the country may need a different set of rules to reduce terrorists' ability to use the Internet and free speech to recruit and get out their message.
The former speaker also said he won't decide whether to run for president until September 2007.
He spoke at the annual Nackey S. Loeb First Amendment award dinner.
More
here.
Earthlink Chalks Up Alexandria, Virginia, in Wi-Fi Portfolio
Via Government Technology.
EarthLink today announced that its proposal to build, own and operate a municipal wireless network in the city of Alexandria has been selected, and the franchise agreement, in the form of a city ordinance, will be introduced at the City Council meeting scheduled for Tuesday, November 28th.The approximately 16-square-mile Wi-Fi mesh network will provide affordable, high-speed Internet access for the residents of and visitors to the city of Alexandria.
After a period for public review and comment, the franchise is scheduled to be formally awarded to EarthLink at City Council's meeting on Saturday, December 16th. EarthLink has emerged as one of the leaders in municipal Wi-Fi development, having been awarded contracts in Philadelphia; Anaheim, California; Milpitas, California; and New Orleans.
More
here.
Heads Up: U.S. Businesses Forced to Change the Way They Save Data on Dec. 1
Chris Preimesberger writes on eWeek:
U.S. businesses are going to have to change the way they handle electronically stored information when new federal rules go into effect Dec. 1.
The new regulations, adopted by the U.S. Supreme Court in April, say businesses must be able to quickly find such data when required by the federal court.
That means that every electronic document stored by businesses—e-mail, instant messages, financials, voice mail and all text and graphical documents—must be easily retrievable.
More
here.
DoD Report to Detail Dangers of Foreign Software
Gary Anthes writes on ComputerWorld:
A U.S. Department of Defense task force early next year plans to warn the Pentagon of a growing threat to national security from adversaries who could insert malicious code in software developed overseas.
The Defense Science Board, a military/civilian think tank within the DOD, will issue a report that calls for a variety of prevention and detection measures but stops short of recommending that all software procured by the military be written in the U.S., said the head of the task force that has been studying the so-called foreign influence issue.
More
here.
Political Toon: Misplaced Priorities
Click for larger image.
U.S. Nuclear Plant Info Available to Public?
Lisa Myers, Amna Nawaz & the NBC Investigative Unit:
What if an airplane were to crash into a nuclear plant? How long would it take terrorists to penetrate security barriers outside nuclear facilities? What are the most vulnerable parts of a nuclear plant to attack in order to inflict maximum damage?
The answers to all those questions, and many more, are available to the public, as NBC News discovered in a recent hidden-camera investigation. Accessing that very information — along with thousands of other sensitive documents from the Nuclear Regulatory Commission (NRC) — is as easy as walking into a public library, finding the right files, printing them out and walking out with the documents in hand, no questions asked.
Many of the documents we were able to access were among the thousands of files the NRC pulled from its Web site after 9/11, deemed too sensitive to be available to the public. But that same effort to clean out sensitive information, it seems, was never made with NRC’s document collections in public libraries across the country.
More
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Monday, Nov. 27, 2006, at least 2,880 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,308 died as a result of hostile action, according to the military's numbers.
The AP count is five more than the Defense Department's tally, last updated Monday at 10 a.m. EST.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casuality Count website
here.
FBI Drops Another Patriot Act Demand But Keeps Gag on ISP
Via The ACLU.
After more than two years in a legal battle with the American Civil Liberties Union, the FBI has abandoned a Patriot Act demand for the subscriber records of a small Internet Service Provider. The ACLU welcomed the decision but criticized the FBI for refusing to lift a gag order that prevents the provider from disclosing its identity.
The FBI announced that it is dropping its national security letter in legal papers made public today.
More
here.