U.S. Toll in Iraq, Afghanistan

Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Saturday, July 18, 2009, at least 4,327 members of the U.S. military had died in the Iraq war since it began in March 2003, according to an Associated Press count.
The figure includes nine military civilians killed in action. At least 3,460 military personnel died as a result of hostile action, according to the military's numbers.
The AP count is one fewer than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
As of Saturday, July 18, 2009, at least 667 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Friday at 10 a.m. EDT.
Of those, the military reports 499 were killed by hostile action.
More
here and
here.
Honor the Fallen.
Symbian Admits Trojan Slip-Up
Tom Espiner writes on C|Net News:
The Symbian Foundation has acknowledged that its process for keeping malicious applications off Symbian OS-based phones needs improvement, after a Trojan horse program passed a security test.
The botnet-building Trojan, which calls itself "Sexy Space," passed through the group's digital-signing process, Symbian's chief security technologist Craig Heath said Thursday. Heath said the group is working on improving its security-auditing procedure.
"When software is submitted, we do try to filter out the bad eggs," Heath told ZDNet UK. "When apps are submitted, they are scanned. We are looking at how they could be scanned better."
Developers must submit the mobile applications they build to the Symbian Foundation for checking for the applications to be accepted by handsets with the Symbian operating system. Once the submission has been accepted, the applications are digitally signed by Symbian. Digital signatures, which are cryptographic security features, are designed to provide an amount of assurance that software for download comes from a trusted source.
The first stage of Symbian's signing process, antivirus scanning, is done automatically using an antivirus engine. Once an application has been submitted and scanned, random samples are then submitted for human audit.
More
here.
Former Boeing Engineer Convicted in Theft of Space Shuttle Secrets for China
Louis Chunovic writes on GSN.com:
A former Rockwell and Boeing engineer, who held a "secret" security clearance when he worked on the Space Shuttle program for those two companies, has been convicted on charges of economic espionage and acting as an agent of the People’s Republic of China.
Technology he stole included Boeing trade secrets related to the Space Shuttle program and the Delta IV rocket, according to the Department of Justice.
Dongfan "Greg" Chung, 73, was employed by Rockwell International from 1973 until its defense and space unit was acquired by Boeing in 1996. Chung is a native of China who became a naturalized U.S. citizen. He retired in 2002, but the following year returned to Boeing as a contractor, a position he held until September 2006.
On Sept. 11, 2006, FBI and NASA agents searched Chung’s house and found more than 250,000 pages of documents from Boeing, Rockwell and other defense contractors inside the house and in a crawl space underneath the house. Among the documents found in the crawl space were scores of binders containing decades’ worth of stress analysis reports, test results and design information for the Space Shuttle.
More
here.
The NSA Wiretapping Story That Nobody Wanted
Robert McMillan writes on PC World:
They sometimes call national security the third rail of politics. Touch it and, politically, you're dead.
The cliché doesn't seem far off the mark after reading Mark Klein's new book, "Wiring up the Big Brother Machine ... and Fighting It." It's an account of his experiences as the whistleblower who exposed a secret room at a Folsom Street facility in San Francisco that was apparently used to monitor the Internet communications of ordinary Americans.
Klein, 64, was a retired AT&T communications technician in December 2005, when he read the New York Times story that blew the lid off the Bush administration's warrantless wiretapping program. Secretly authorized in 2002, the program lets the U.S. National Security Agency (NSA) monitor telephone conversations and e-mail messages of people inside the U.S. in order to identify suspected terrorists. Klein knew right away that he had proof -- documents from his time at AT&T -- that could provide a snapshot of how the program was siphoning data off of the AT&T network in San Francisco.
More
here.
In Passing: Walter Cronkite

Firefox 3.5.1 Now Available
Get it.
Security fixes in 3.5.1:
MFSA 2009-41 Corrupt JIT state after deep return from native function
- ferg
Internet Thieves Raid Hong Kong Bank Accounts
A DPA newswire article, via Enterprise Security Today, reports that:
Hong Kong banks have been ordered to step up online security measures after it emerged that thieves had stolen more than 289,000 Hong Kong dollars (37,000 US dollars) in a series of Internet bank raids, officials confirmed Tuesday.
The Hong Kong Monetary Authority (HKMA) said the money was stolen in three separate incidents in which people's accounts were accessed by thieves who first infected their computers with viruses that stole bank account login details.
Eight banks have been targeted since April, according to a report in the South China Morning Post.
In a statement, the HKMA confirmed it had issued a circular ordering all banks to step up security measures, such as instantly alerting customers by text message or other means every time an online transfer to a third-party is made from their accounts.
More
here.
CEO of Antivirus Vendor AVG to Step Down
Robert McMillan writes on PC World:
After two years at the job, the CEO of Dutch antivirus seller AVG Technologies is stepping down.
AVG said Thursday that it is looking for a replacement for CEO JR Smith who can take the company public. Smith remains CEO for now, and is expected to stay on in another capacity after his replacement is found, said company spokeswoman Siobhan MacDermott.
The company also plans to expand its senior management team and is looking at creating new positions for a chief operations officer and senior vice president of business development, MacDermott said. "We need more senior management to manage more people as we add them and grow the business," she said.
Founded by two Czech entrepreneurs in 1991, AVG is now owned by three investment firms: majority stakeholder Enterprise Investors, Benson Oak and Intel Capital. It employs about 350 people and boasts more than 80 million users worldwide. It is best known for its free antivirus software, called AVG Free.
More
here.
Experts Link Flood of 'Canadian Pharmacy' Spam to Russian Botnet Criminals
Ellen Messmer writes on NetworkWorld:
The world's currently most voluminous spam generator, “Canadian Pharmacy,” is clogging networks with come-ons for male-enhancement drugs and painkillers -- and there’s growing belief it has a link to Russian cybercrime groups selling counterfeit medicines.
In this case, "Canadian Pharmacy," hyping itself as “the #1 Internet Online Drugstore,” is neither Canadian nor a pharmacy. In fact, "Canadian Pharmacy" doesn’t appear to exist as an established Web site but only a shifting hyperlink in a spam message generated by about eight crime botnets.
Spam volumes as a whole skyrocketed 60% between January and June to 150 billion messages a day, according to a report released this week by Marshal8e6, a vendor of Web and anti-spam security products, which says so-called “pharmaceutical spam,” or “pharma spam” for short, constitutes 75% of that.
More
here.
Researcher: Conficker Authors Prepping for Next Stage
Robert Westervelt writes on SearchSecurity.com:
The vast army of zombied machines—thanks to the cybercriminals behind the Conficker worm—have gone silent over the last several months. But one security expert, who has been studying the worm since it began propagating, finds this inactivity troubling and believes its authors are planning the next chapter of Conficker.
Mikko Hyppönen of F-Secure Corp. plans to present his research at the Black Hat Briefings in Las Vegas later this month. Hyppönen, who is also a member of the Conficker Working Group, is intrigued by the worm's sophistication, which allowed it to spread so quickly. Still, the researcher believes the worm's authors are relatively new to the scene, since Conficker spread too quickly making it a high profile nemesis of security researchers.
"I think the biggest mystery in the whole Conficker operation is the motive," Hyppönen said. "How come a group who is capable of pulling something of this magnitude off doesn't seem to be interested in actually using this massive botnet they created?"
The worm used algorithms never seen before by researchers. It was protected with the MD6 cryptographic hash algorithm. The method slowed researchers trying to block the worm and allowed it to quickly infect machines. The domain generation system, used by the worm to check for orders and its USB spreading algorithm also helped the malicious code to infect more computers. When Conficker peaked in January the worm's authors had over 10 million machines at their disposal, yet they did nothing with those machines.
More
here.
Computers Breached at San Diego Cancer Center
Angelica Martinez writes on The San Diego Union-Tribune:
A letter has been sent to 30,000 patients of UCSD's Moores Cancer Center after a hacker breached the center's computers and gained access to patients' personal information.
The letter, dated July 9, was sent as a precaution to inform patients that the computers were compromised on June 26, said DeAnn Marshall, UCSD Health Sciences chief of marketing and communications officer.
The computer servers affected contained information such as patients' names, dates of birth, medical record number, diagnosis and treatment dates back to 2004, Marshall said. The vast majority of patients' information did not include Social Security numbers, she said.
More
here.
Mark Fiore: Jobless Jack

More Mark Fiore Brilliance.
Via The San Francisco Chronicle.
- ferg
Cloud Storage Stymied by USA Patriot Act
A ComputerWorld article by Robert L. Mitchell, via PC World, reports that:
Weak privacy laws make the U.S. an unfriendly place for non-U.S. companies to host data, says one user of cloud storage services.
And that could be bad news for some U.S.-based cloud storage vendors. While the customer's data may be stored in the cloud, cloud storage service providers must store the bits on the ground somewhere. Some Canadian and European firms worry that if that data sits on devices maintained on U.S. soil it will be subject to surrepticious peeks by certain U.S. government agencies.
That prospect bothers some business customers of COOP Systems' Web-based business continuity management software, who don't want their data subject to prying eyes of the U.S. government. They simply won't host their data in a U.S.-based cloud - period. The problem, says COOP CEO Chris Alvord, are generally inadequate legal protections for hosted data in the U.S.- and the government's power to snoop.
"We believe that legal exposure is inevitable, especially the Patriot Act provisions," Alvord says. So COOP, which uses Verizon's Remote Backup & Restore service, will be moving some of its operations to a Verizon facility based in Toronto. That location, he says "will be for Canadian and European [companies] that can't expose their data in the U.S."
More
here.
Feds Say 'Dragnet' Surveillance Lawsuit Threatens Security
David Kravets writes on Threat Level:
Citing the state secrets privilege and other legal claims, the Obama administration urged a federal judge here Wednesday to dismiss a lawsuit claiming Americans’ electronic communications are being siphoned to the National Security Agency without warrants.
During a two-hour hearing, a top-ranking Justice Department litigator declined to confirm or deny the existence of what the Electronic Frontier Foundation described in its lawsuit as ongoing “dragnet” surveillance, which the EFF hopes the lawsuit will stop.
“President Obama inherited a number of surveillance activities,” Anthony Coppolino, special litigation counsel for the administration, told U.S. District Judge Vaughn Walker. “There remain rare occasions where the privilege has to be invoked to prevent harm to national security.”
Coppolino added that the government is immune from lawsuits regarding the conduct at issue. Surveillance, he said, “is the crown jewel of the National Security Agency.”
More
here.
Theft of Twitter Documents from Google Apps Raises Cloud Security Concerns
Jon Brodkin writes on NetworkWorld:
Questions about cloud security and the feasibility of storing critical information in Web-based services are being raised in the wake of a hacking incident involving Twitter and Google Apps.
A hacker obtained and distributed more than 300 confidential documents pertaining to Twitter's business affairs that were stored on Google Apps.
Insufficient password strength has been pegged as a root cause, but industry observers are debating whether Google or Twitter is most at fault. "It's not clear to me whether it's a black mark on Google or a black mark on Twitter at this point," says Pund-IT analyst Charles King.
Shortly after the data theft was reported, Twitter CEO Evan Williams used his own Twitter account to note that he was "having a bad night."
More
here.
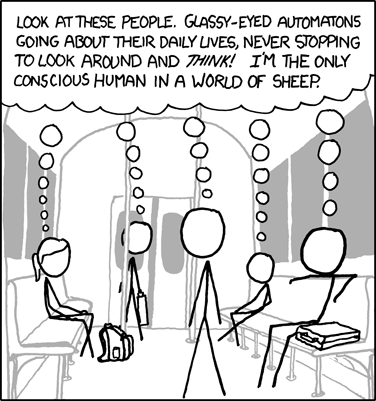
Classic xkcd: Sheeple
Click for larger image.
We love
xkcd.
- ferg
SAIC Acquires Cyber Security Firm Atlan
Via UPI.
U.S. company Science Applications International Corp. Monday announced the acquisition of cybersecurity product testing company Atlan Inc.
SAIC acquired Virginia-based Atlan, a provider of Federal Information Processing Standard validation testing among other testing capabilities, in a move to expand its capabilities and offerings in the cybersecurity market.
As part of the acquisition Atlan's employees will become a part of the SAIC Intelligence and Information Solutions business unit's Accredited Testing and Evaluation Laboratories.
More
here.
Researcher: Middle East Blackberry Update Spies on Users
Kim Zetter writes on Threat Level:
A Blackberry update that a United Arab Emirates service provider pushed out to its customers contains U.S.-made spyware that would allow the company or others to siphon and read their e-mail and text messages, according to a researcher who examined it.
The update was billed as a “performance enhancement patch” by the UAE-based phone and internet service provider Etisalat, which issued the patch for its 100,000 subscribers.
The patch only drew attention after numerous users complained that it drained their Blackberry battery and slowed performance, according to local publication ITP.
Nigel Gourlay, a Qatar-based programmer who examined the patch, told ITP that the patch contained “phone-home” code that instructed the Blackberries to contact a server to register. But once the patch was installed, thousands of devices tried to contact the server simultaneously, crashing it and causing their batteries to drain.
More
here.
Data Stolen in U.S., South Korea Cyber Attacks
An AP newswire article, via The New Zealand Herald, reports that:
Hackers extracted lists of files from computers they contaminated with the virus that triggered cyber attacks in the United States and South Korea, say Seoul police.
The attacks, in which floods of computers tried to connect simultaneously to a single website to overwhelm the server, caused outages on prominent government-run sites in both countries.
The finding means hackers not only used affected computers for web attacks, but also tried to steal information from them. That adds to concern contaminated computers were ordered to damage their own hard disks or files after the web assaults.
Still, the new finding does not mean information was stolen from attacked websites, such as those of the White House and South Korea's presidential Blue House, police said. It also does not address suspicions about North Korea's involvement.
Police reached those conclusions after studying an analysis of about two dozen computers - a sample of the tens of thousands of the infected computers, said An Chan Soo, a senior cyber attack investigator. Only lists of files were extracted, not the files.
More
here.
Quote of The Day: Marc Sachs
"We know how to deal with these attacks. This is not a technical issue, it's a leadership issue."
Marc Sachs, quoted by Shaun Waterman.
3 Reasons Why U.S. Cyber Security Sucks
Michael Tanji writes on Danger Room:
Good news, cybersecurity nerds: You ain’t running out of work, anytime soon. As last week’s cyber panic about North Korea showed, when there isn’t a teenager-simple denial-of-service attack that delays your access to a government website, there is a voracious hype machine that feeds on the tiniest slivers of data – both significant and trivial – and expels massive quantities of fear and misinformation. And where there’s cyber fear, there’s cybersecurity work to be done.
It’s sad that this sham is allowed to continue unabated. But worse still, it’s dangerous. Despite the expenditure of tens of billions of dollars and countless studies on what needs to happen (not to mention all the offices, centers and commands, that are supposed to implement those reports), we’re still largely screwed when it comes to threats of the online variety.
The problem is multifaceted, but can be broken down into three meta-categories [...]
More
here.
Cyber Security: Senate Bill Would Make International Cooperation a Priority
Ben Bain writes on FCW.com:
A new Senate bill would encourage the secretary of state to work with other governments to further cooperation on cybersecurity and would require the secretary to submit a report to Congress about those efforts.
The legislation, introduced by Sen. Kirsten Gillibrand (D-N.Y.) on July 10, states the secretary should work with other governments to:
- Develop cooperative activities.
- Encourage international cooperation for improving cybersecurity.
- Develop safeguards for privacy, freedom of speech and commercial transactions to be included in agreements or other cybersecurity activities.
The bill would require the secretary to submit a detailed report to congressional committees about actions taken to meet these goals in 270 days of the legislation’s enactment.
“Relevant international cybersecurity agreements focus only on issues relating to cyber crime and common operating standards, and have not been signed by certain countries from which cyberattacks may be launched,” the bill states.
More
here.
Patch Tuesday: Microsoft Patches 9 Bugs, Leaves One Open for Hackers
Gregg Keizer writes on ComputerWorld:
Microsoft today delivered six security updates that patch nine vulnerabilities, fixing two bugs already being used by hackers but leaving one still open to exploit.
Of the six bulletins, three patched some part of Windows, while the remainder plugged holes in Publisher, Internet Security and Acceleration Server (ISA) and Microsoft's virtualization software. Six of the nine bugs were ranked critical, Microsoft's highest ranking in its four-step score, while three were tagged as "important," the next-lowest label.
More
here.
Cyber Attacks Traced to the U.S., Britain
Kim Zetter writes on Threat Level:
International fingerpointing in the recent cyberattacks against U.S. and South Korean web sites has widened to include the UK, as researchers examining the attacks trace them to a server in the United Kingdom.
But the UK company that owns the server says it, in turn, traced the attacks to a VPN connection originating in Miami, Florida.
With hawks in Congress and the press urging President Obama to launch an all-out cyber war in retaliation for the website outages, things are looking bad for the Sunshine State. Though it should be noted that the Miami connection was likely just another proxy used by the hacker, who could be based in the U.S. or anywhere else.
Researchers at Bkis Security in Hanoi, who reported findings about the UK server on their company’s blog, say that the denial-of-service attacks that struck more than three dozen government and commercial sites last week were launched from more than 166,000 computers in 74 countries controlled by a server in the UK. The IP range for the server is 195.90.118.xxx, which is registered to Global Digital Broadcast, which streams digital TV content from Latin America to consumers.
A company representative was unavailable for comment.
More
here.
UK, Not North Korea, Source of DDoS Attacks, Researcher Says
Martyn Williams writes on PC World:
The U.K. was the likely source of a series of attacks last week that took down popular Web sites in the U.S. and South Korea, according to an analysis performed by a Vietnamese computer security analyst.
The results contradict assertions made by some in the U.S. and South Korean governments that North Korea was behind the attack. Security analysts had been skeptical of the claims, which were reportedly made in off-the-record briefings and for which proof was never delivered.
The week-long distributed denial of service attack involved sending multiple requests to a handful of Web sites from tens of thousands of computers so the sites became overloaded. Among the sites taken offline at some time during the week were those of the U.S. Departments of Transportation and Treasury, the U.S. Federal Trade Commission, the South Korea's president's home page, the South Korean national assembly and U.S. Forces Korea.
The computers used to send the flood of requests had been infected with a virus that allowed attackers to use them anonymously.
More
here.
Invisible IPv6 Traffic Poses Serious Network Threat
Carolyn Duffy Marsan writes on CIO.com:
Experts say that most U.S. organizations have hidden IPv6 traffic running across their networks, and that few network managers are equipped to see, manage or block it. Increasingly, this rogue IPv6 traffic includes attacks such as botnet command and controls.
"If you aren't monitoring your network for IPv6 traffic, the IPv6 pathway can be used as an avenue of attack," says Tim LeMaster, director of systems engineering for Juniper's federal group. "What network managers don't understand is that they can have a user running IPv6 on a host and someone could be sending malicious traffic to that host without them knowing it."
Most U.S. network managers are blind to rogue IPv6 traffic because they don't have IPv6-aware firewalls, intrusion detection systems or network management tools. Also, IPv6 traffic is being tunneled over IPv4 connections and appears to be regular IPv4 packets unless an organization has deployed security mechanisms that can inspect tunneled traffic. (See also: 5 of the biggest IPv6-based threats facing CIOs.)
"At least half of U.S. CIOs have IPv6 on their networks that they don't know about, but the hackers do," says Yanick Pouffary, technology director for the North American IPv6 Task Force and an HP Distinguished Technologist. "You can't ignore IPv6. You need to take the minimum steps to secure your perimeter. You need firewalls that understand IPv4 and IPv6. You need network management tools that understand IPv4 and IPv6."
More
here.
Why Feds Can't Stop Cyber Attacks
Gregg Carlstrom writes on The Federal Times:
Cyberattacks targeting dozens of government and business Web sites last week were “primitive” and “just a nuisance,” not very different from the attacks that target federal systems on a daily basis, experts say — but they still caught the federal government by surprise.
Experts say the sluggish reaction highlights the need for a single White House official who can coordinate a federal response to a cyberattack.
But they also say agency Web sites shouldn’t have been overwhelmed in the first place by such a primitive attack. Several agencies struggled for days to get their Web sites back online. The Transportation Department’s site was down for almost a full day; the Federal Trade Commission Web site went offline during the Fourth of July weekend and remained largely inaccessible until the evening of July 6.
That could have been prevented, experts say, if the government had better security standards in place and if agencies had invested in newer technology for their Web sites.
The federal government refuses to comment on the attacks — it refuses to even confirm that they happened. But experts say the federal response to this fairly unsophisticated attack raises troubling questions about the government’s ability to stand up to a more serious threat.
“Some agencies didn’t do well here dealing with low-level threats. What would happen with a more sophisticated attacker?” asked James Lewis, a senior fellow at the Center for Strategic and International Studies.
More
here.
Under Pressure From Trademark Interests, ICANN Undoes GNSO Reforms
Milt Mueller writes on the IGP Blog:
A little-noticed outcome of the Sydney ICANN meeting (overshadowed by the excitement surrounding the selection of its new CEO) was a shockingly flagrant display of how arbitrary and unfair ICANN can be. A year ago a Board Governance Committee recommended, and the full Board adopted, a proposal to give civil society and commercial user interests the same number of votes (6) on the GNSO Council. The action was intended to correct what was widely perceived as an indefensibly unfair distribution of votes, in which trademark/ commercial interests were given nine votes and noncommercial interests only three. The rebalancing was first proposed in an independent, expert evaluation of the GNSO by the London School of Economics, and later endorsed by the Board. A July 2008 GNSO committee - which included representatives of the trademark and commercial users - also endorsed the idea of representational parity.
But when faced with the prospect of equal representation of commercial and noncommercial user interests, the commercial user groups revolted. Having lost the fight against parity on principle grounds, they shifted tactics and "went negative," claiming that the Noncommercial Users Constituency was not "representative enough" and did not warrant additional representation. The staff and Board were inundated with non-stop criticism of this sort for months. Numerous threats about withdrawing from the GNSO were made.
And yet, in Sydney the Board's Structural Improvements Committee turned a deaf ear to the vibrant new participation and caved in to the incessant pressure of the commercial interests. Two decisions, almost unbelievable in the degree to which they discriminate against civil society and completely ignore public comments, emerged from the Sydney meeting.
More
here.
DoD Seeks Defense Against Denial-of-Service Attacks
Ben Bain writes on FCW.com:
The Defense Information Systems Agency wants commercial products that could help network administrators detect and react to distributed-denial-of-service (DDoS) attacks, according to a request for information posted today.
In such attacks, an individual or group attempts to bring down a Web site by overwhelming it with traffic.
The agency is interested in solutions that could give administrators a clear and timely picture of what is happening on their networks, alert them in the event of suspicious activity and provide options for mitigating attacks, the notice states.
“The goal of this solution is to detect and mitigate all DDoS attempts to disrupt [Defense Department] network communications and to detect internal assets displaying anomalous behavior across the Internet-to-NIPRnet boundary,” the notice states.
More
here.
LexisNexis Warns of Breach After Alleged Mafia Bust
Robert McMillan writes on ComputerWorld:
Information broker LexisNexis has warned more than 13,000 consumers, saying that a Florida man who is facing charges in an alleged mafia racketeering conspiracy may have accessed some of the same sensitive consumer databases that were once used to track terrorists.
Lee Klein, 39, of Boynton Beach, Fla., was charged by the U.S. Department of Justice (DOJ) in May following an undercover sting operation that netted 11 suspects from an alleged South Florida crew of the Bonanno crime family.
On Friday, the office of the New Hampshire Attorney General posted a letter [.pdf] that LexisNexis sent out to consumers last month, warning that Klein may have used his access to LexisNexis' Seisint databases "in order to perpetrate certain crimes."
LexisNexis has had problems with credit card fraudsters using its database in the past, but Klein's alleged crimes are different.
In court filings, the DOJ said Klein would provide Bonanno family members with names, addresses and account numbers as part of a fake check-cashing operation. But he's also accused of using computer databases to get information on potential extortion or assault targets as well as "individuals suspected by the Enterprise members of being involved with law enforcement."
More
here.
Microsoft Admits New ActiveX Zero-Day Bug
Gregg Keizer writes on ComputerWorld:
For the second time in a week, Microsoft is warning users that hackers are exploiting an unpatched, critical bug in a company-made ActiveX control, putting people running Internet Explorer (IE) at risk.
The company has been busy lately acknowledging "zero-day" vulnerabilities. Today's admission was the third in the last two months, and the fifth since February.
According to the security advisory Microsoft released early Monday, the vulnerability is in Office Web Components, a set of ActiveX controls for publishing Office content to the Web, and for displaying that content in IE. The bug is in the ActiveX control that displays Excel spreadsheets within IE, Microsoft said.
More
here.
Report: 73% of U.S. Businesses Breached
Alex Goldman writes on internetnews.com:
The fourth annual U.S. Encryption Trends Study was released today by The Ponemon Institute. The study says that 73 percent of surveyed businesses have experienced a data breach in the past year, up from 60 percent in the 2008 study. The report was sponsored by encryption supplier PGP Corp.
"A data breach is defined as the loss or theft of confidential or sensitive data including information about people and households," said Dr. Larry Ponemon, chairman and founder of The Ponemon Institute, in an e-mail to InternetNews.com.
The numbers are comparable to a similar study released last week concerning UK businesses. There, the Ponemon Institute found that 70 percent had been breached in the last year.
The report was based on surveys with nearly a thousand (997) U.S.-based executives.
More
here.
Beckstrom Defends U.S.-Based ICANN
Eric Pfanner writes in The New York Times:
The U.S.-based agency that regulates Internet addresses, facing criticism that it is too America-centric, remains the best guardian of a “single, unified, global Internet,” according its new chief executive.
Rod Beckstrom, a technology entrepreneur and former U.S. government Internet security official, took over this month as head of the Internet Corporation for Assigned Names and Numbers, succeeding Paul Twomey, an Australian.
As use of the Internet expands around the world, there have been rising calls for a new way of overseeing some of its basic functions, including the allocation of domain suffixes like .com and .org. This duty, and other important technical functions, have been in the hands of ICANN, a private, nonprofit organization based in Marina Del Rey, California, for the past decade, under an agreement with the U.S. Commerce Department.
“There will always be different voices out there, but the ultimate proof that ICANN is functioning properly is that the Internet is functioning properly,” Mr. Beckstrom said by telephone last week.
More
here.