June 25: First 'Full Earth' of Summer 2006
Today's New Moon is the first of the summer, and the first "Full Earth" of the summer, as well.
Via StartDate.org.
Living on the Moon would be harsh. There's no air, the temperatures range from extreme heat to extreme cold, and lunar dust would get into every nook and cranny of a moonbase. But there would be at least one treat that you couldn't experience anywhere else: a full Earth hanging in the night sky.
In fact, there's a full Earth today. That's because the Moon is new. It's crossing the line between Earth and the Sun, so it's lost in the Sun's glare. It'll return to view as a thin crescent in the west in early evening in a day or two.
At new Moon, it's nighttime for the lunar hemisphere that faces Earth. But as seen from the Moon, Earth is in full daylight, so it casts a lot of light across the lunar landscape. Earth covers about 13 and a half times as much area as the full Moon does as seen from Earth. And on average, every square mile of Earth reflects between three and four times as much sunlight back into space as the same area on the Moon. When you put the numbers together, it means that a full Earth is about 40 times brighter than a full Moon.
To make it even more interesting, from any given point on the Moon, Earth appears to stand in the same position in the sky all the time; it doesn't rise or set, it just hovers in the same spot. So as the hours passed, you'd see different portions of Earth rotate into view. And as the days passed, you'd see Earth go through its own cycle of phases. That includes new Earth -- when the Moon is full.
Link.
Om Malik: Sidekick 3 Sells for $4050 on eBay
Om Malik
writes on his
Next Generation blog:
Now some of us have been lucky enough to test out the Sidekick 3 - for instance, The Engadget Boys and Phone Scoop Gang - but even they could not have predicted the mad dash for the new Danger Hiptop, aka T-Mobile Sidekick 3.
One of these puppies just sold for a whopping $4050 on eBay. Not bad for a product that is soon to hit the market, and will be pushed hard by both T-Mobile, and Danger. The phone/communicator is going to cost $300 and is likely to be available later this week. Still, this does indicate good times ahead for Danger and T-Mobile. It is a nice device - with a far superior keyboard compared to the Sidekick 2, bluetooth, ability to play music and even vCard support.
With all the celebrities (and some infamous people like Paris Hilton) pimping it out, expect this one to be a monster hit.
More
here.
25 June 1981: Microsoft Becomes Incorporated
00:01
Via Wikipedia.
Days after reading the January 1, 1975, issue of Popular Electronics that demonstrated the Altair 8800, Bill Gates called the creators of the new microcomputer, MITS (Micro Instrumentation and Telemetry Systems), offering to demonstrate an implementation of the BASIC programming language for the system. Gates had neither an interpreter nor an Altair system, yet in the eight weeks before the demo he and Allen developed the interpreter. The interpreter worked at the demo and MITS agreed to distribute Altair BASIC.
Gates left Harvard University, moved to Albuquerque, New Mexico where MITS was located, and founded Microsoft there. The name Microsoft, without the hyphen, was first used in a letter from Gates to Allen on November 29, 1975, and on November 26, 1976 the name became a registered trademark.
The company's first international office was founded on November 1, 1978, in Japan, entitled "ASCII Microsoft" (now called "Microsoft Japan"). On January 1, 1979, the company moved from Albuquerque to a new home in Bellevue, Washington. Steve Ballmer joined the company on June 11, 1980, and would later succeed Bill Gates as CEO.
The company restructured on June 25, 1981, to become an incorporated business in its home state of Washington (with a further change of its name to "Microsoft, Inc."). As part of the restructuring, Bill Gates became president of the company and Chairman of the Board, and Paul Allen became Executive Vice President.
More
here.
UK: IT Expert Worked With July 7 Bombers & Warned Police
Ed Vulliamy writes in The Guardian Unlimited:
A computer expert who worked alongside two of the July 7 bombers claims today that he tried to warn the police about their activities almost two years before the suicide attacks.
Speaking for the first time about his work, Martin Gilbertson, 45, says he produced anti-western propaganda videos, secured websites and encrypted emails for Muslims who were involved in an Islamic bookshop and a youth centre attended by bombers Mohammad Sidique Khan and Shehzad Tanweer. Mr Gilbertson was also employed to establish firewalls that would safeguard both places from outside interference.
By October 2003, he says he was so alarmed by what he was producing in Beeston, West Yorkshire that he went to the local Holbeck police station, saying he had material and names he wanted to deliver to anti-terrorist officers. He was told to post his material, and did so, to West Yorkshire police headquarters in Wakefield. The package contained DVD material he had compiled for circulation by the bookshop, a list of names including Khan and Tanweer and a covering letter giving a contact telephone number.
He claims he heard nothing until he was interviewed three times by two officers from the Metropolitan police, having contacted them after the explosions.
More
here.
Australia: Broadband Subscription Usage Hits 3M
Via Australian IT.
Australia now has more than 3 million broadband internet services, up 78 per cent on the 1.8 million recorded in March 2005.
Of the 3.16 million services recorded at the end of March, 2.3 million were on ADSL services, the latest figures from the Australian Competition and Consumer Commission's Snapshot of Broadband Deployment report show.
But other forms of broadband, such as wireless, were also growing, ACCC commissioner Ed Willet said.
More
here.
Picture of the Day: Man Eats 22 Hotdogs in 12 minutes
Pat Philbin of Moonachie, N.J., shows off his trophy after winning the New Jersey Regional competition of the Nathan's Famous 2006 Hot Dog Circuit, Friday, June 23, 2006, at the New Jersey Turnpike's Molly Pitcher Travel Plaza in Cranbury, N.J. Philbin won after eating 22 hot dogs in 12 minutes and will compete in the 91st Fourth of July International Hot Dog-Eating Contest to take place in Coney Island, N.Y.
Image source: Boston Globe / AP Photo / George Olivar
Story
here.
Connecticut DMV Workers Charged with Selling Registration Info
An AP newswire article, via The Boston Globe, reports that:
Two employees of the [Connecticut] state Department of Motor Vehicles are accused of conspiring to sell car registration information to a New York dealer.
Jason Rodriguez, 36, and Omayra Vargas, 35, both of Hartford, were arrested this week and charged with conspiracy to receive a bribe and committing a computer crime, police said.
Rodriguez and Vargas, who both worked in the DMV's office in Wethersfield, allegedly conspired to accept a bribe from the dealer in return for giving him details about certain older, potentially valuable cars owned by Connecticut residents, police said.
That dealer, 43-year-old Robert Russo of Commack, N.Y., was arrested in May on bribery charges in connection with the alleged incident, police said.
More
here.
Political Toon: Torture Etiquette
Click for larger image.
U.S. Plays Terror Card in Hearing on AT&T Wiretap Lawsuit
Bob Egelko writes in The San Francisco Chronicle:
A lawsuit accusing AT&T of illegally collaborating in government electronic surveillance will help terrorists communicate "more securely and more efficiently'' unless it is promptly dismissed, a Bush administration lawyer argued in a packed San Francisco courtroom Friday.
If the privacy-rights case is allowed to proceed, AT&T will have to admit or deny that it gave the National Security Agency access to its telephone and e-mail networks and database so the government could eavesdrop on communications between Americans and suspected terrorists in other countries, said Assistant Attorney General Peter Keisler.
An admission either way by AT&T would betray "a state secret of the highest order,'' he said.
When Chief U.S. District Judge Vaughn Walker pointed out that the alleged cooperation of AT&T and other telecommunications companies has been widely reported in the press, Keisler said public confirmation or denial would allow terrorists to replace suspicion with certainty.
More
here.
U.S. Officials Defend Bank Data Tracking
Greg Miller and Josh Meyer write in The Los Angeles Times:
In response to the Sept. 11 attacks, the Treasury Department sought to enlist a reluctant ally. The world's banking industry long had been loath to give up data on its customers, so U.S. investigators issued a subpoena for just a narrow slice of information from a worldwide financial consortium.
The reply stunned Treasury officials.
The consortium couldn't extract the shards of data that U.S. terrorism analysts were looking for, so it offered something far more generous.
"They said, 'We'll give you all the data,' " Treasury Secretary John W. Snow said Friday during a news conference in which he defended the espionage program.
More
here.
24 June 1948: Start of the Berlin Blockade
00:01
Loading milk on a West Berlin-bound plane.
Image source: Wikipedia
Via Wikipedia.
The Berlin Blockade (June 24, 1948 to May 11, 1949) became one of the first major crises of the new Cold War, when the Soviet Union blocked railroad and street access to West Berlin. The crisis abated after the Soviet Union did not act to stop American, British and French humanitarian airlifts of food and other provisions to the Western-held sectors of Berlin; referred to as Operation Vittles. The Berlin Blockade was one of the largest blockades in history.
When World War II ended in Europe on May 8, 1945, Soviet and Western (U.S., British, and French) troops were located in arbitrary places, essentially, along a line in the center of Europe. From July 17 to August 2, 1945, the victorious Allied Powers reached the Potsdam Agreement on the fate of post-war Europe, calling for the division of a defeated Germany into four occupation zones (thus reaffirming principles laid out earlier by the Yalta Conference), and the similar division of Berlin into four zones, later called East Berlin and West Berlin. The French, U.S., and British sectors of Berlin were deep within the Soviet occupation zone, and thus a focal point of tensions corresponding to the breakdown of the Western-Soviet wartime alliance.
More
here.
Echoes of Watergate in NSA Coutroom
Kevin Poulsen writes on Wired News:
It was perhaps inevitable that someone would compare President Bush's extrajudicial wiretapping operations to Richard Nixon's 1970s-era surveillance of journalists and political enemies. Both were carried out by Republican presidents; both bypassed the courts; both relied on the cooperation of U.S. telecommunications companies.
But there's some irony in the fact that it was AT&T to first make the comparison in a federal courtroom here, while defending itself from charges of complicity in Bush's warrantless spying.
More
here.
Personal Data of 28,000 U.S. Sailors Found on Internet Web Site
An AP newswire article, via MSNBC, reports that:
Personal data, including the Social Security numbers of 28,000 sailors and members of their families, have been found on a civilian Web site, triggering a criminal investigation.
The Navy said Friday the information was in five documents and included people’s names, birth dates and Social Security numbers.
Navy spokesman Lt. Justin Cole would not identify the Web site or its owner, but said the information had been removed. He would not provide any details about how the information ended up on the site.
More
here.
Text Messaging Used as Malware Lure
Ryan Naraine writes on eWeek:
Botnet herders have found a crafty new way to lure computer users to maliciously rigged Web sites—via text messaging on cell phones.
The latest social engineering trick is to send SMS (short messaging service) alerts to mobile phones with a warning that the target has subscribed to an online dating service that racked up expensive charges on cell phone bills.
The message includes a URL for the user to unsubscribe to avoid the $2 per day charges.
According to a warning from anti-virus vendor CA, the URL points to a Web site rigged with Win32/Bambo.CF, a Trojan horse program used by identity thieves to hijack sensitive user information.
More
here.
The Best Regulations Telco Money Can Buy
Via SaveTheInternet.com.
Charles Cooper, the executive editor at CNet, wrote an article today about the way telcos spin and deceive lawmakers into voting against the best interests of their constituents.
“Since the completion of last year’s telecommunications mega-mergers, small and medium-size businesses have been getting hosed–with Uncle Sam playing the role of complicit bystander,” he writes.
Cooper is referring to the SBC-AT&T and Verizon-MCI mergers announced in 2005. Telco lobbyists spun these mergers as pro-consumer and pro-business developments.
But since the late fall, prices for local private lines have done the opposite — increasing for both consumers and businesses. “Maybe I missed the fine print on the press releases but how do they square price increases with the public interest?” Cooper asks.
Today, these newly re-assembled telco giants are spending tens of millions of dollars to spin lawmakers with the same arguments against Net Neutrality. But decision makers in Washington might want to check voters’ pocketbooks before rubber stamping legislation to gut Net Neutrality.
More
here.
Symantec to Exit Security Appliance Business
Paul F. Roberts writes on InfoWorld:
Symantec laid off staff and said it is shaking up its network and gateway security business this week, ending the company's experiment with security hardware appliances.
The company said it will reduce future investment in the SGS (Symantec Gateway Security), SNS 7100 (Symantec Network Security), and SGS Advanced Manager 3.0 appliances, according to a statement provided to InfoWorld.
The announcement is evidence that Symantec is shifting its strategy away from being a "one stop shop" for security wares, and will focus on lucrative security management and services, said John Pescatore, a vice president at Gartner.
More
here.
U.S. Republicans Reject Trucking Security Provision
Via UPI.
Republicans in the U.S. Congress this week defeated a provision that would have boosted security for the U.S. trucking industry.
The Homeland Security Economic Security Subcommittee of the U.S. House of Representatives unanimously approved a bill Thursday that would establish regulations for the trucking industry, but Republicans defeated a Democratic amendment that would have required additional security measures for the shipment of dangerous materials, CongressDaily reported Thursday.
The bill directs the U.S. Department of Homeland Security to designate which materials being transported throughout the United States by truck should be considered security sensitive. The list would differentiate between hazardous materials that need extra security provisions and other cargo. Individuals transporting security sensitive materials would have to undergo a fingerprint background check before being issued a permit, CongressDaily said.
More
here.
Goofy Product of the Day: Jesus-Themed Adhesive Bandages
Image source: Gizmodo
Via Gizmodo.
Let the Good Lord heal your wicked wounds with these Jesus bandages from Archie McPhee. One box contains 15 bandages that were blessed by the Pope during a special “Bless This Mess” ceremony at the Vatican. Also in the box is a free toy!
As you can see in the picture, portraits of Our Lord and Savior, which look like they were lifted from every scene in The Da Vinci Code, grace each and every bandage. These “designer bandages” (would Jesus approve of his face being used to sell trinkets?) might not heal you any faster, but then again, did he ever think that people would be promoting his name in sports arena with rock music blaring?
In any event, you can grab these spiritually fulfilling bandages for $4.95 per tin. Be on the lookout for Archie McPhee-branded indulgences this fall.
More
here.
It Must Be Friday: Clowns Sabotage Nuke Missile Site

Image source: Defense Tech
On Tuesday morning, a retired Catholic priest and two veterans put on clown suits, busted into a nuclear missile launch facility, and began beating the silo cover with hammers, in an attempt to take the Minuteman III missile off-line. Seriously.
The trio -- members of the Luck, Wisconsin group Nukewatch -- said the break-in was part of "a call for national repentance" for the Hiroshima and Nagaski A-bombings in 1945.
The activists used bolt-cutters to get into the E-9 Minuteman II facility, located just northwest of the White Shield, North Dakota. "Using a sledgehammer and household hammers, they disabled the lock on the personnel entry hatch that provides access to the warhead and they hammered on the silo lid that covers the 300 kiloton nuclear warhead," the group said in a statement. "The activists painted 'It's a sin to build a nuclear weapon' on the face of the 110-ton hardened silo cover and the peace activists poured their blood on the missile lid."
This was all done while wearing face paint, dunce caps, misfitting overalls, and bright yellow wigs.
More
here.
AMD Chooses Saratoga County NY for Microchip Plant
An AP newswire article, via SFGate.com, reports that:
Semiconductor maker Advanced Micro Devices Inc., lured by about $1 billion in state incentives, will build a multibillion dollar chip manufacturing plant in upstate New York, creating 2,000 permanent jobs, a state Assemblyman said Friday.
AMD, based in Sunnyvale, Calif. chose to locate the new $3.5 billion plant on a 600-acre site in Malta, about 25 miles north of Albany, said Assemblyman Ronald Canestrari, an Albany County Democrat.
"It's a done deal," Canestrari said.
More
here.
Library Director Under Fire for Refusing to Release Private Data Without Subpoena
Merry Firschein writes on NorthJersey.com:
Library Director Michele Reutty is under fire for refusing to give police library circulation records without a subpoena.
Reutty says she was only doing her job and maintaining the privacy of library patrons. But the mayor called it "a blatant disregard for the Police Department," which needed her help to identify a man who allegedly threatened a child.
Reutty, the director for 17 years, now faces possible discipline by the library board. Members of the Borough Council have suggested she receive punishment ranging from a letter of reprimand in her personnel file to a 30-day unpaid suspension. But the Library Board of Trustees said it would reserve judgment until a closed-door hearing next month.
More
here.
Study: U.S. Not Prepared for Net Attacks
Ed Oswald writes on BetaNews:
If the United States were to suffer from a catastrophic Internet disruption, it is likely that there would be a significant impact to both homeland and economic security. A report issued by the Business Routable Friday claims that the country is ill prepared for such an event.
The Business Roundtable is made of 160 CEOs from America's largest companies. The group says that there is too much ambiguity in what the response would be from both the public and private sectors.
More
here.
The New SETI@Home: Search for Evildoers on Domestic Soil
Via Good Morning, Silicon Valley (GMSV).
"The University of California at Berkeley's SETI@home, a scientific experiment that used Internet-connected computers to download and analyze radio telescope data in the Search for Extraterrestrial Intelligence (SETI), proved once and for all that no intelligent life exists in the universe. Bad news for them; good news for us! Now the NSA is free to use the name and the idea in its search for evildoers on domestic soil."
- The Huffington Post announces NSA SETI@Home
Verizon to End Service on Commercial Airplanes
Ken Belson writes on The New York Times:
Verizon Airfone, whose handsets have graced the backs of airline seats for more than two decades, will shut down its phone service on commercial airliners before the end of the year.
Verizon Communications, Airfone's parent company, has decided instead to focus on its faster-growing broadband, cellular and television businesses, Jim Pilcher, the director of marketing at Verizon Airfone, said today.
More
here.
European Telcos Face Data Retention Cost Issues
Ray Le Maistre writes on Light Reading:
A new European data retention directive designed to help law enforcement agencies tackle terrorist threats is set to cost Europe's telecom operators and ISPs a collective fortune, and it will likely provide rich pickings for storage vendors and integrators.
The European Union's Directive 2006/24/EC "on the retention of data generated or processed in connection with the provision of publicly available electronic communications services or of public communications networks" is already in legal force. It was hurried through the European Parliament following the terrorist attacks in Madrid (2004) and London (2005).
The debate on the directive is over. As a law, it's now a "must do," and a mandatory compliance date is set. The directive's requirements need to be implemented by the EU's 25 member states by September 15, 2007.
By that date, fixed and mobile telecom operators and ISPs will need to have data storage and retrieval systems in place that can deliver on the directive's exacting requirements. Based on a cost assessment by one country, the collective cost to EU service providers is set to be in the hundreds of millions of dollars.
More
here.
Gapingvoid: Eating Children
Via gapingvoid.com. Enjoy!

Apocalyptic Evangelical Online Game Chock Full of Spyware
Chris Williams writes on The Register:
Watchers of right-wing Christian groups in the States say a new apocalyptic videogame released by cultish Revelations-based fiction series Left Behind is riddled with spyware.
Developers have incorporated software from an Israeli firm called Double Fusion. It incorporates video advertising and product placement into the game, and reportedly records players' behaviour, location, and other data to be uploaded to Left Behind's Bible-powered marketing machine.
Aimed at 13 to 34-year-old males, Left Behind: Eternal Forces casts the player as a director of God's Earthly militia, left behind in the Rapture to roam the streets of New York, battling Satan's minions and shooting unbelievers.
More
here.
EURid: Cybersquatters Can Get Rich if They're Quick
Via OUT-LAW.com.
Cybersquatters who broke the rules when registering .eu domains can be stripped of them at any time, says .eu registry EURid. But if they manage to sell their domains before being caught, they can keep the proceeds, according to the registry.
Bitter controversy has surrounded the 'sunrise' period of the new domain, launched in April. Several existing domain registrar firms, including GoDaddy, have accused US profiteers of using a lax EURid system to stockpile valuable domain names against its rules.
EURid now says that it will confiscate domains at any time if they are found to have broken the rules. "If we find that someone has provided inaccurate or misleading information in the registration then we will take that domain off them," said EURid spokesman Patrik Linden. "We can do that at any time."
More
here.
Verizon Working to Recover Deleted 911 Calls in Massachusetts
Linda Rosencrance writes on ComputerWorld:
Verizon Communications Inc. is working to recover recordings of approximately 1.5 million 911 calls and radio communications accidentally deleted by a subcontractor during an upgrade of 911 equipment at the Massachusetts State Police Headquarters in Framingham, Mass.
According to a Verizon spokesman, a technician at Needham, Mass.-based Dictronics Inc. was doing a planned upgrade last week of a digital recorder used for 911 emergency calls and radio communications between troopers and headquarters. The work is part of a general contract for upgraded 911 equipment between the commonwealth of Massachusetts and Verizon.
After the work on June 13, Verizon officials were informed by the state police that up to 11 months' worth of recordings -- both calls and data -- were no longer accessible. Verizon spokesman John Bonomo said a preliminary analysis indicates that the incident may have been the result of an error by a Dictronics technician.
More
here.
Google Offloads Baidu Investment
Via The BBC.
Google has sold its stake in rival Chinese internet search firm Baidu.com.
The US company confirmed that it had disposed of its 2.6% holding in Baidu - acquired before the latter's 2005 stock market flotation - on Wednesday.
Baidu is the leading web search firm in China, a market in which Google lags behind the domestic provider.
Analysts always saw Google's purchase of Baidu shares as a strategic move and Google said it now wanted to focus on its own Chinese business.
More
here.
Mobile Phone Users Warned of Lightning Strike Risk
A Reuters newswire article, via Yahoo! News, reports that:
People should not use mobile phones outdoors during thunderstorms because of the risk of being struck by lightning, doctors said on Friday.
They reported the case of a 15-year-old girl who was using her phone in a park when she was hit during a storm. Although she was revived, she suffered persistent health problems and was using a wheelchair a year after the accident.
"This rare phenomenon is a public health issue, and education is necessary to highlight the risk of using mobile phones outdoors during stormy weather to prevent future fatal consequences from lighting strike injuries," said Swinda Esprit, a doctor at Northwick Park Hospital in England.
More
here.
Kentucky Blocks State Workers' Access to Blog
An AP newswire article by Joe Biesk, via Yahoo! News, reports that:
Kentucky officials are blocking state employees' Internet access to a political blog that has been critical of Gov. Ernie Fletcher, who was indicted earlier this year in connection with a state hiring scandal.
The blocked Web sites include entertainment and humor sites, online auctions and blogs, but Mark Nickolas, operator of http://www.bluegrassreport.org, said he believes his site was targeted for its political content.
"It's outrageous; it shows that we are in the People's Republic of Kentucky now — that government will block political speech that it does not approve of," Nickolas said.
More
here.
Sunnyvale Man Sentenced to 14 Years for ID Theft
Leslie Griffy writes in The Mercury News:
A Sunnyvale [California] man was sentenced today to 14 years in prison for identity theft as part of a more than $1 million real estate scam.
John Shaw, 47, faced up to 27 years after being convicted last year on 14 felony counts, including forgery, grand theft, identify theft, recording false documents, conspiracy, intimidating a witness and perjury.
A licensed real estate agent, Shaw assumed the identities of at least five people, mostly his clients, and purchased real estate in their names. He then sold the property to other names he assumed, pocketing the profits.
More
here.
I Have One Simple Request: To Have Sharks With Frickin' Laser Beams Attached to Their Heads!
 Dr. Evil
Dr. EvilOf course, that quote came from "
Austin Powers: International Man of Mystery", but I digress.
This real-life AP
story comes to us via
USA Today:
Alongside the submarines, ships and airplanes participating in large-scale military exercises in the Pacific this month, a team of sea lions and dolphins are expected to patrol the sea.
These marine animals will be flown in from San Diego for simulated mine recovery and mine detection during the biennial RIMPAC war games.
Six bottle-nosed dolphins would find the mines, while four California sea lions would help recover them.
More
here.
23 June 1991: Happy 15th Birthday, Sonic the Hedgehog
00:01
Sonic's appearance on his 15th birthday.
Image source: Wikipedia
Via Wikipedia.
Sonic the Hedgehog is a video game character, protagonist of a series of games released by Sega, as well as numerous spin-off comics, cartoons and books.
The first game in the franchise was released in 1991 in order to provide Sega with a mascot to rival Nintendo's flagship character Mario. Since then, Sonic has become one of the best-known video game characters, with his series having sold over 44 million copies.
Sonic is a blue anthropomorphic hedgehog with the ability to run at the speed of sound, a talent which forms a major part of the gameplay of the series. He is 15 years old, 100 centimeters (3 ft 3 in) tall, and weighs 35 kilograms (77 lb). His birthday is June 23rd.
More
here.
Ex-Computer Associates Executive Pleads Guilty
An AP newswire article, via The Los Angeles Times, reports that:
A former executive with Computer Associates International Inc. pleaded guilty to obstructing justice by trying to buy the silence of potential witnesses in a stock fraud scandal at one of the world's largest software companies, prosecutors said.
Thomas Bennett, 50, faces as many as five years in prison at sentencing Oct. 12. Bennett was senior vice president in charge of business development for Long Island, N.Y.-based Computer Associates, which since has become known as CA Inc.
Federal prosecutors in Brooklyn, N.Y., alleged that Bennett conspired with other executives to secretly manipulate more than $2 billion in revenue from 1999 to 2000 to prop up the company's stock price.
More
here.
Torrentspy Names Alleged MPAA Hacker
Greg Sandoval writes on C|Net News:
A month after accusing the Motion Picture Association of America of conspiring to commit data theft, the operators of a file search engine presented more details regarding the alleged relationship between the MPAA and a man who admits hacking the small company's network.
Valence Media, the parent company of Torrentspy.com, charges the MPAA paid the Canadian resident $15,000 for information on Torrentspy and its executives, according to documents filed Thursday with U.S. District Court for the Central District of California in Los Angeles.
More
here.
U.S. Government Mining Banking Data in Anti-Terror Effort
Josh Meyer and Greg Miller write in The Los Angeles Times:
The U.S. government, without the knowledge of many banks and their customers, has engaged for years in a secret effort to track terrorist financing by reviewing confidential information on transfers of money between banks worldwide.
The program, run by the Treasury Department, is considered a potent weapon in the war on terrorism because of its ability to clandestinely monitor financial transactions and map terrorist webs.
Current and former officials at multiple U.S. agencies acknowledged the program's existence, but spoke on condition of anonymity, citing its sensitive nature. "We're very, very protective of it," said a senior U.S. official familiar with the program. "It is extremely valuable."
The program is part of an arsenal of aggressive measures the government has adopted since the Sept. 11 terrorist attacks that yield new intelligence, but also circumvent traditional safeguards against abuse and raise concerns about intrusions on privacy.
More
here.
N.Y. Lawmaker Drops Suit Claiming Google Profits From Child Porn
An AP newswire article, via SFGate.com, reports that:
A suburban politician has dropped a federal lawsuit that had claimed the search engine company Google Inc. profits from child pornography.
Jeffrey Toback, a member of the Nassau County Legislature, filed suit in May claiming Google had "paid links" to Web sites containing child pornography. "They take money from these sites," he said.
A Google spokesman at the time denied the allegations and said the company takes numerous steps to prevent access to child pornography.
More
here.
Senate Committee Chairman Says 'No' to Net Neutrality
Wayne Rash writes on eWeek:
Senator Ted Stevens (R-AK) told eWEEK on June 22 that he does not want any sort of net neutrality legislation to be part of the telecom bill currently being debated by the Senate Commerce, Science and Transportation Committee.
The committee held a markup session on Senate Bill 2686, the Communications, Consumers' Choice and Broadband Deployment Act of 2006 on the afternoon of June 22.
A markup session is when the Senate committee considers amendments to the current version of a bill before it goes before the full Senate for a vote.
The June 22 meeting was the first in what promises to be a long series of meetings extending over the course of several days or weeks.
The bulk of the debate was aimed at two areas: funding communications initiatives for the War on Terrorism and for VOIP (voice over IP) legislation.
More
here.
Jail Time for Payola Search Engines?
Andrew Orlowski writes on The Register:
A South Carolina senator has proposed that search engines which offer pay-to-play deals should face sanctions - including jail time for the company executives.
The latest amendment to this year's doorstop telecomms legislation, S.2686, was tabled by Jim DeMint (R), and targets search sites which "prioritize or give preferential or discriminatory treatment in the methodology used to determine Internet-search results based on an advertising or other commercial agreement with a third party".
Violators would face a $5m fine - and executives would be liable for a custodial sentence.
More
here.
Privacy Advocates Slam AT&T on Customer Records
Ritsuko Ando writes for Reuters:
Privacy advocates slammed AT&T Inc. on Thursday for declaring that it owned its Internet and video customers' account information and could hand the data over to law enforcement if needed.
AT&T on Wednesday updated its privacy policy, which came as the company and other phone operators faced lawsuits claiming they aided a U.S. government domestic spying program by inappropriately handing over millions of call records.
More
here.
U.S. House Panel Approves Wiretap Inquiry Resolution
Stephanie Sonntag writes for UPI:
GOP lawmakers are threatening to pass a "resolution of inquiry" forcing the handover of documents about the president's program of warrantless wiretapping.
The House Judiciary Committee approved a Democrat-sponsored "resolution of inquiry" Wednesday requiring the administration to turn over records concerning any government requests for "access to telephone communications records of persons in the United States" not made under the 1978 Foreign Intelligence Surveillance Act or other criminal statutes.
At the committee meeting, Chairman F. James Sensenbrenner Jr., R-Wisc., expressed his frustration with the administration, which has stonewalled congressional requests for information about the controversial program -- designed to monitor telephone calls, e-mails and other electronic communications into and out of the United States by people believed linked to terrorist groups like al-Qaida.
"I have concerns about the justice department's lack of cooperation in providing the committee information," Sensenbrenner said, adding that the committee ought to approve the resolution to "send the administration a message."
More
here.
Nine Indicted In Debit Card Skimming Scheme: $1 Million In Losses
Laurie Sullivan writes on TechWeb News:
Federal authorities arrested eight defendants accused of skimming bank account information from debit cards from more than 100 people at restaurants in Southern California. The information was used to steal money from the victims' bank accounts and purchase Postal money orders, a U.S. Postal Inspector said Wednesday.
Investigators for the three agencies involved in the arrests -- the United States Postal Inspection Service, IRS Criminal Investigation, and U.S. Immigration and Customs Enforcement -- believe the scheme resulted in the theft of more than $1 million.
More
here.
Boeing Evaluating the Future of Connexion
A Reuters newswire article, via Yahoo! News, reports that:
Boeing Co. on Thursday said it is evaluating the prospects for Connexion, its in-flight Internet venture, but declined to comment on a press report that the company may sell or close the unit.
The Wall Street Journal reported in Thursday's editions that Boeing may dump Connexion, which has failed to turn a profit in six years.
More
here.
Online Game Becomes Sexploitation Site
Fiore Mastroianni reports on ABC News' "The Blotter":
In an attempt to avoid traceable e-mails, pedophiles are using online games, including Sony's Everquest, to target and communicate with their victims, according to federal investigators.
Federal prosecutors in Illinois today announced the arrest of 40-year-old John Wayne Malone, of Pittsburgh, Texas, for using Everquest to lure a 14-year-old girl in Moline, Ill. into sending provocative, naked photos of herself and participating in online sex chats.
He was charged with sexual exploitation of a minor and receiving pornographic material over the internet, officials said.
According to an affidavit filed in the case, Malone used the Everquest characters "Elveron" and "Bezapada" to make and continue contact with the girl.
More
here.
City of Austin Needs Emergency Geek Squad
Amy Hadley writes on News8Austin:
When Katrina evacuees headed to Austin, they needed to be able to communicate.
Pete Collins, chief information officer for the city of Austin, made sure people had the technology they needed.
While the job got done, Collins wants to smooth out the operations, if it happens again.
"I need to put an IT group together, a response group for the city. That way, if we have this happen again, I have this resource pool that's already pre-defined," Collins said.
Collins is calling companies to find out what they can do in the next disaster.
The city is also looking for 100 tech savvy volunteers to make up the Technical Response Team.
More
here.
FTC Laptop Theft Exposes Consumer Data
...and the beat goes on. Unbelievable.
Brian Krebs writes on Security Fix:
The Federal Trade Commission -- an agency whose mission includes consumer protection and occasionally involves suing companies for negligence in protecting customer information -- today disclosed a recent theft of two laptop computers containing personal and financial data on consumers.
In a statement, the FTC said two employee laptops were stolen from a locked vehicle. The PCs contained data on about 110 people that was "gathered in law enforcement investigations and included, variously, names, addresses, Social Security numbers, dates of birth, and in some instances, financial account numbers."
The commission said it has "no reason to believe the information on the laptops, as opposed to the laptops themselves, was the target of the theft. In addition, the stolen laptops were password protected and the personal information was a very small part of several thousand files contained in one of the laptops." The agency also said it would offer affected individuals one year of free credit monitoring.
More
here.
Experimental Military Microsatellites Reach Orbit
A Spaceflight Now article by Justin Ray, via Space.com, reports that:
An experimental U.S. military project to characterize the performance of two micro-satellite trailblazers operating 22,300 miles (35,888 kilometers) above Earth and a prototype maneuvering motor for small spacecraft began with a beautiful blastoff from Cape Canaveral Wednesday evening.
The Micro-Satellite Technology Experiment, or MiTEx, was successfully delivered into space by Boeing's workhorse Delta 2 rocket. Launch from pad 17A occurred at 6:15 p.m. EDT (2215 GMT) after a short delay to clear both a technical issue with the payload and any boats from the restricted waters under the rocket's flight path.
The swift half-hour ascent by the three-stage rocket put MiTEx into an elliptical geosynchronous transfer orbit to mark the 67th consecutive successful Delta 2 mission dating back to 1997 and the 120th success overall in 122 flights since 1989.
More
here.
U.S. Inter-Agency Feud Disrupts Data Flow on Terror
Siobhan Gorman writes in The Baltimore Sun:
Nearly five years after the Sept. 11 attacks, the Departments of Justice and Homeland Security continue to clash over who is in charge of coordinating and vetting information on terrorism. As a result, state and local authorities continue to get conflicting or incomplete information - sometimes none at all - on threats inside the United States, officials say.
The feud over control of the information caused federal agencies last week to miss a White House deadline for outlining how it should be distributed to state and local authorities, intelligence and counterterrorism officials said yesterday.
More
here.
UK: Web Paedophile Sentenced to Nine Years
Via The BBC.
A sex offender who was caught through an anti-paedophile website has been given a nine-year jail term for sexual grooming and pornography offences.
Lee Costi, 21, was sentenced at Nottingham Crown Court where he admitted grooming schoolgirls for sex.
Costi, from Haslemere in Surrey, was caught when a Nottingham girl told her mother about his chatroom messages.
He was the first to be caught in a police internet operation called the Virtual Global Taskforce.
More
here.
Ben Edelman: Spyware Showing Unrequested Sexually-Explicit Images
A ZenoTecnico ad, edited to cover sexually-explicit areas.
Image source: BenEdleman.org
The guru of all things Adware & Spyware,
Ben Edelman, doesn't post very often over on his blog -- but when he does, they are well worth reading.
Today, Ben
writes:
Are pop-up ads anything more than an annoyance? For advertisers they can certainly be a bad deal -- particularly when spyware-delivered pop-ups cheat advertisers through PPC [Pay Per Click] click fraud, PPC syndication fraud, affiliate fraud, banner farms, or other improper ways of getting paid. For users, pop-ups in overwhelming quantities may cause substantial harm -- especially because pop-up-delivering spyware reduces computer speed and reliability, and because spyware transmits sensitive user information to remote servers.
But spyware-delivered pop-ups can do more than annoy. They can also offend. Consider spyware that shows sexually-explicit (most would say, pornographic) pop-ups. When such ads appear unrequested, they're likely to be shown to users who don't want to see sexually-explicit material. It's a troubling practice -- but all too common even among "adware" vendors that claim to have improved their practices. Meanwhile, some old tricks remain -- like pop-ups with their "X" buttons off-screen, making the ads particularly hard to close.
Much more
here.
User Friendly: People Just Don't Appreciate th RIAA
Via UserFriendly.org.
Click for larger image.
Preview of the ICANN Marrakech Meeting
Kieren McCarthy writes on The Register:
There will be much to discuss at ICANN's Marrakech meeting which kicks off this Saturday, but one question rises about all others: what will happen to the internet on 30 September 2006?
ICANN has its own agenda to discuss, but that agenda and what people actually want to discuss are a little different. As is the fundamental issue that everyone at that meeting should be talking about. This is our account of what is likely to happen, why, and what it all means.
More here on ICANN's agenda items
here.
Thieves Targeting GPS Units in Cars
Richard Willing writes in USA Today:
Thieves might not want to steal your car as much as the high-tech stuff you carry in it — digital BlackBerries, iPods and especially your fancy GPS system, according to the FBI.
The most recent crime statistics show that motor vehicle theft last year remained nearly the same as in 2004. But thefts of parts and accessories from vehicles, including high-intensity xenon headlights and Global Positioning System devices, has jumped 30% since 2000, the FBI reports.
More
here.
BlueGene/L Breaks Another Speed Record
David Needle writes on internetnews.com:
The Department of Energy's National Nuclear Security Administration (NNSA) and IBM today announced the world's fastest supercomputer has outdone itself. In its latest testing, IBM said its BlueGene/L (BG/L) achieved a sustained performance of 207.3 trillion floating-point operations per second (teraFLOPS), a new record for floating-point performance.
IBM said its software researchers were able to improve performance with new mathematical libraries that take better advantage of the dual-core architecture of the floating point unit of the PowerPC 440 processor used in Blue-Gene/L. A year ago, BG/L's floating point performance was less than 100 teraFLOPS.
More
here.
Senate Panel Poised for Net Neutrality Vote
Anne Broache writes on C|Net News:
The tussle over Net neutrality regulations appears to be nearing its final stages in Congress.
The Senate Commerce Committee plans to begin on Thursday afternoon what is likely to turn into many hours of debate on a broad, contentious communications bill. Committee aides said they expect scores of amendments and, if feasible, a final vote by day's end--though some said the proceeding could stretch into next week.
More
here.
'I See,' said The Blind Man: Congress Can't Investigate Spies, it Says
Via UPI.
The U.S. Congress' investigative arm says that it cannot effectively oversee the nation's spy agencies without cooperation from the intelligence committees.
"For us to undertake such work would require the sponsorship of the Senate Select Committee on Intelligence or the House Permanent Select Committee on Intelligence," Derek Stewart of the Government Accountability Office told lawmakers last week.
"While we have the authority to do such work, we lack the cooperation we need to get our job done in that area," continued Stewart. "As a result, unless and until we receive such cooperation, and given GAO's limited recourse, we will continue our long-standing policy of not doing work that relates directly to intelligence matters unless requested to do so by one of the select intelligence committees."
More
here.
Wireless Piggybacking Lands Man In Trouble
Via KATU2 (Portland, Oregon).
Brewed Awakenings, with its pithy name, artful drinks and wireless Internet service, has found itself unexpectedly percolating on the forefront of high-tech law.
"He doesn't buy anything," Manager Emily Pranger says about the man she ended up calling 911 about. "It's not right for him to come and use it."
Pranger says 20-year-old Alexander Eric Smith of Battle Ground sat in the parking lot in his truck for three months, spending hours at a time piggybacking on the coffee shop's wireless Internet service for free.
When deputies told Smith to knock it off, he came back and is now charged with theft of services.
As it turns out, Smith is a Level One Sex Offender, but whether he in fact committed a crime by not buying a single tall latte before accessing the Internet, well that remains to be seen. The sheriff's office and prosecutors are now reviewing the case.
More
here.
Former CIA Officers Join Northern Virginia Firm
Renae Merle writes in The Washington Post:
Former CIA director George J. Tenet and two other agency veterans are joining the advisory board of the Analysis Corp., a small Fairfax company that has tapped into the government's growing reliance on private sector intelligence firms.
Since stepping down from the CIA in 2004, Tenet has been teaching diplomacy at Georgetown University, his alma mater, and has taken at least one other position, joining the board of Guidance Software Inc., a California technology firm. His position at the Analysis Corp. will reunite Tenet with his former chief of staff and former CIA deputy executive director John O. Brennan, who is the president and chief executive of the firm.
More
here.
Spike in Laptop Thefts Stirs Jitters Over Data
Petula Dvorak writes in The Washington Post:
It has become the police-blotter item of our age: A small-time burglar swipes a laptop and fences it for a quick $200 at a pawnshop.
But increasingly, these petty crimes are causing anxiety in executive suites across the country as one corporation after another alerts customers that laptops holding troves of sensitive records have been stolen.
Week after week, Americans who conscientiously shred every piece of mail and all credit card receipts learn that their personal information was stored in the laptop of a low-level employee who casually took it out of the office and that it has ended up in the hands of some penny ante crook.
More
here.
Hackers Break into U.S. Agriculture Dept. Computers
An AP newswire article by Libby Quaid, via Yahoo! News, reports that:
A hacker broke into the Agriculture Department's computer system and may have obtained names, Social Security numbers and photos of 26,000 Washington-area employees and contractors, the department said Wednesday.
Agriculture Secretary Mike Johanns said the department will provide free credit monitoring for one year to anyone who might have been affected.
The break-in happened during the first weekend in June, the department said. Technology staff learned of the breach on June 5 and told Johanns the following day but believed personal information was protected by security software, the department said.
However, on further analysis, staff concluded that data on current or former employees might have been accessed and informed Johanns on Wednesday, according to the department.
The department said it notified law enforcement agencies. Its inspector general is investigating the break-in.
More
here.
22 June 1633: Galileo Forced to Recant Heliocentric Theory
00:01
Galileo facing the Roman Inquisition, 1857 painting by Cristiano Banti.
Image source: Wikipedia
Via Wikipedia.
Pope Urban VIII personally asked Galileo to give arguments for and against heliocentrism in the book, and to be careful not to advocate heliocentrism. He made another request, that his own views on the matter be included in Galileo's book. Only the latter of those requests was fulfilled by Galileo. Whether unknowingly or deliberate, Simplicius, the defender of the Aristotelian Geocentric view in Dialogue Concerning the Two Chief World Systems, was often caught in his own errors and sometimes came across as a fool.
This fact made Dialogue Concerning the Two Chief World Systems appear as an advocacy book; an attack on Aristotelian geocentrism and defense of the Copernican theory. To add insult to injury, Galileo put the words of Pope Urban VIII into the mouth of Simplicius. Most historians agree Galileo did not act out of malice and felt blindsided by the reaction to his book. However, the Pope did not take the public ridicule lightly, nor the blatant bias. Galileo had alienated one of his biggest and most powerful supporters, the Pope, and was called to Rome to explain himself.
With the loss of many of his defenders in Rome because of Dialogue Concerning the Two Chief World Systems, Galileo was ordered to stand trial on suspicion of heresy in 1633. The sentence of the Inquisition was in three essential parts:
- Galileo was required to recant his heliocentric ideas, which were condemned as "formally heretical".
- He was ordered imprisoned; the sentence was later commuted to house arrest.
- His offending Dialogue was banned; and in an action not announced at the trial, publication of any of his works was forbidden, including any he might write in the future.
In modern terms, we consider Galileo's views on heliocentricity to be no fundamental advance. The Sun is no more the center of the universe than the Earth is (indeed, the question has no meaning, as apparently all locations can be equally regarded as the "center" of the universe).
The Catholic Church held to the prevailing scientific opinion of the day, which was that the Earth was the center of the universe. Thus, for moderns, the key issue of this controversy was not the objective correctness of the theories being debated, but rather the morality of institutions (or persons) using brute force to shape acceptance of scientific beliefs.
More
here.
Researchers Hack Wi-Fi Driver to Breach Laptop
Robert McMillan writes on InfoWorld:
Security researchers have found a way to seize control of a laptop computer by manipulating buggy code in the system's wireless device driver.
The hack will be demonstrated at the upcoming Black Hat USA 2006 conference during a presentation by David Maynor, a research engineer with Internet Security Systems and Jon Ellch, a student at the U.S. Naval postgraduate school in Monterey, California.
The two researchers used an open-source 802.11 hacking tool called LORCON (Lots of Radion Connectivity) to throw an extremely large number of wireless packets at different wireless cards. Hackers use this technique, called fuzzing, to see if they can cause programs to fail, or perhaps even run unauthorized software when they are bombarded with unexpected data.
Using tools like LORCON, Maynor and Ellch were able to discover many examples of wireless device driver flaws, including one that allowed them to take over a laptop by exploiting a bug in an 802.11 wireless driver. They also examined other networking technologies including Bluetooth, Ev-Do (EVolution-Data Only), and HSDPA (High Speed Downlink Packet Access).
More
here.
Bad Week for Excel: Third Microsoft Excel Exploit Posted
Robert McMillan writes on NetworkWorld:
Excel users have one more reason to worry. On Tuesday, a hacker published code that takes advantage of an unpatched flaw in the Microsoft spreadsheet software, the third such exploit to be disclosed in the past week.
This attack could be used to run unauthorized software on a PC, but it requires that the victim first be tricked into opening an Excel document, according to an alert published on the Securitytracker.com Web site.
The attack takes advantage of Adobe's Flash technology, which can be used to provide graphics and animation to Excel documents. "When the target user opens the Excel file, the [malicious] Flash code will execute automatically without user interaction," the alert states.
More
here.
More Telco-Sponsored Net Nuetrality Propaganda
This banner ad showed up atop one of the MSNBC story pages this afternoon, just as the massive (and sneaky) telecom "reform" legislation sponsored by Sen. Ted Stevens (R.-Alaska) is being debated in Washington.
This
"Internet of The Future" ad comes to us from the same folks who sponsor the
"Hands Off the Internet" campaign -- the telcos.
Ya gotta see this here:
http://www.internetofthefuture.org/
House Will Move on NSA Wiretapping Law
Via UPI.
The chairman of the House intelligence committee has agreed to hold hearings about legislation to regulate the president's program of warrantless wiretaps.
Rep. Pete Hoekstra, R-Ill., made the commitment in an exchange with the senior-most Democrat on the committee, Rep. Jane Harman, D-Calif., on the House floor Tuesday.
The program -- under which the National Security Agency listens to the phone calls of terrorist suspects into and out of the United States -- was initiated by President Bush in Ovtober 2001, but only reveled to the public by leaks to the New York Times last year.
More
here.
AT&T Re-Writes the Rules: Your Data Isn't Yours
David Lazarus writes in The San Francisco Chronicle:
AT&T has issued an updated privacy policy that takes effect Friday. The changes are significant because they appear to give the telecom giant more latitude when it comes to sharing customers' personal data with government officials.
The new policy says that AT&T -- not customers -- owns customers' confidential info and can use it "to protect its legitimate business interests, safeguard others, or respond to legal process."
The policy also indicates that AT&T will track the viewing habits of customers of its new video service -- something that cable and satellite providers are prohibited from doing.
Moreover, AT&T (formerly known as SBC) is requiring customers to agree to its updated privacy policy as a condition for service -- a new move that legal experts say will reduce customers' recourse for any future data sharing with government authorities or others.
More
here.
Shocker: Data Brokers Invoke Fifth Amendment
Jeffery Silva writes on RCR Wireless News:
Eleven data-broker executives invoked their Fifth Amendment right against self-incrimination, refusing to answer questions of the House Commerce oversight and investigations subcommittee about deceptive practices for acquiring and selling mobile phone records and other customer information to banks, major corporations, law enforcement, news outlets and others.
The revelation earlier this year that Internet data brokers were using fraudulent means to help secure customer cell phone records ignited a flurry of lawsuits and investigations by federal and state officials.
Despite refusal of data brokers to testify, the House Commerce Committee Chairman Joe Barton (R-Texas) vowed to continue the investigation and said he would meet with House Majority Leader John Boehner (R-Ohio) this afternoon to ask why a committee-passed bill outlawing fraudulent access to phone records—a practice called pre-texting—was suddenly pulled from a scheduled House vote on May 2.
In a May 11 letter to House Speaker Dennis Hastert (R-Ill.), ranking House telecom and Internet subcommittee member Edward Markey (D-Mass.) referred to speculation the House Intelligence Committee blocked full House consideration of the phone-records bill because some lawmakers want an exemption from the legislation’s privacy protection provisions for intelligence gathering activities.
More
here.
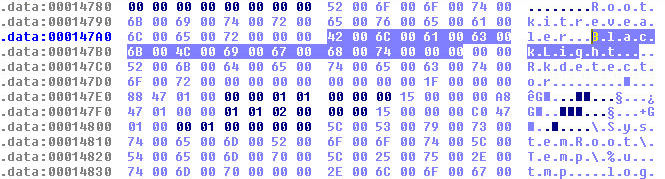
F-Secure: Hiding the Unseen
Mailbot.AZ also attempts to detect and avoid some of the more popular rootkit detectors.
Image source: F-Secure
Antti
writes over on the
F-Secure "News from the Lab" Blog:
Many of our readers have probably heard of Alternate Data Streams (ADS) on NTFS. They're not that well documented and there are only a few tools that can actually handle them. Lately we've been looking at variants of the Mailbot family that use hidden streams to hide themselves.
Let's take Mailbot.AZ (aka Rustock.A) as an example. There's only a single component lying on the disk, and that is a kernel-mode driver. It's stored as hidden data stream attached to the system32 folder (yes, folders can have data streams as well)! Saving your data into Alternate Data Streams is usually enough to hide from many tools.
However, in this case, the stream is further hidden using rootkit techniques, which makes detection and removal quite challenging. Because Mailbot.AZ is hiding something that's not readily visible, it's very likely that many security products will have a tough time dealing with this one.
We've just released a new version of our BlackLight rootkit scanner (Build 2.2.1041) that can detect current variants of Mailbot.
More
here.
Newsweek: Protecting Covert CIA Operatives' Identities
Answer: Make sure your spouse doesn't end up on the bad side of the Bush administration.
Sorry -- I couldn't resist.
Mark Hosenball writes in Newsweek:
Financial records and résumés are available with a few keystrokes, so the CIA must adapt the cover stories and fake IDs used by U.S. spies.
In a recent report, the Senate intel committee said it was "concerned" the agency has not modernized its methods for establishing "nonofficial cover" — known as NOC — for CIA officers who want to operate overseas but away from official outposts like U.S. embassies and consulates.
More
here.
NASA's Chandra X-Ray Telescope Solves Black Hole Paradox
Via NASA.
Black holes light up the universe and astronomers may finally know how. New data from NASA's Chandra X-ray Observatory show for the first time powerful magnetic fields are the key to these brilliant and startling light shows.
It is estimated up to one quarter of the radiation in the universe emitted since the big bang comes from material falling towards supermassive black holes, including those powering quasars, the brightest known objects. For decades, scientists have struggled to understand how black holes, the darkest objects in the universe, can be responsible for such prodigious amounts of radiation.
New X-ray data from Chandra give the first clear explanation for what drives this process: magnetic fields. Chandra observed a black hole system in our galaxy, known as GRO J1655-40 (J1655, for short), where a black hole was pulling material from a companion star into a disk.
More
here.
Photo of the Day: Stonehenge's Day in the Sun
A man stands on top of Stonehenge as the sun rises on June 21, 2006 in Amesbury, England. An estimated 19,000 people celebrated the start of the longest day of the year at the 5,000-year-old stone circle. Only four arrests were made at the all night party.
Image source: C|Net / Daniel Berehulak / Getty Images
FIFA Voices Doubts on South African IT for 2010 World Cup
Daniel Thomas writes on Computing (UK):
FIFA has started preparations for the 2010 World Cup in South Africa, but has expressed concerns that the country’s IT infrastructure is inadequate in its present state.
Football governing body FIFA is hoping to reuse large parts of the technology infrastructure from this month’s tournament in Germany, but says lack of bandwidth could make it difficult to run accreditation, event management and football results systems in the same way.
More
here.