U.S. Toll in Iraq

Via The Boston Globe (AP).
As of Saturday, May 10, 2008, at least 4,074 members of the U.S. military have died in the Iraq war since it began in March 2003, according to an Associated Press count.
The figure includes eight military civilians. At least 3,322 died as a result of hostile action, according to the military's numbers.
The AP count is the same as the Defense Department's tally, last updated Friday at 10 a.m. EDT.
More
here.
And as always, the
Iraq Coalition Casualty Count keeps the grim watch on their website
here.
Honor the Fallen.
Security Flaw Turns Gmail Into Open-Relay Server
Joel Hruska writes on ARS Technica:
A recently-discovered flaw in Gmail is capable of turning Google's e-mail service into a highly effective spam machine. According to the Information Security Research Team (INSERT), Gmail is susceptible to a man-in-the-middle attack that allows a spammer to send thousands of bulk e-mails through Google's SMTP service without fear of detection.
This attack bypasses both Google's identity fraud protection mechanisms and the current 500-address limit on bulk e-mail.
More
here.
New Hampshire Police Employee Charged With Using Police Information to Help Others Avoid Arrest
An AP newswire article, via The Boston Globe, reports that:
A Concord Police Department employee has been charged with using police information to help others avoid arrest.
Jodi Dukette, 38, of Allenstown was passing along internal police information last month that she obtained the department's computer network, police said.
She was arrested Thursday and charged with two counts of computer crimes, three counts of obstructing government administration and hindering apprehension.
The police said she helped her stepson, Justin Lee, avoid arrest by giving him a ride from Concord to her home, while two police agencies were looking for him.
Police did not identify the others who allegedly benefited from the police information and did not say why they were wanted.
More
here.
e-Records Haunt OSC Chief
Richard W. Walker writes on FCW.com:
Following a raid by federal authorities on the U.S. Office of Special Counsel last week, critics of embattled OSC chief Scott Bloch are questioning whether the office can continue to carry out its mission with Bloch leading it. OSC protects federal employees from prohibited personnel practices, especially reprisal for whistle-blowing.
Two members of Congress have called for Bloch to resign, and other observers question whether the office can be effective with its controversial chief under renewed scrutiny.
Federal agents raided Bloch’s office in Washington and his home May 6, seizing computer files and documents as part of an ongoing investigation into possible obstruction of justice. Bloch had not been arrested or charged with a crime as this issue went to press.
More
here.
IT Didn't Fail Myanmar During Cyclone, People Did
Dan Nystedt writes on InfoWorld:
The growing disaster in Myanmar caused by Cyclone Nargis could have been at least party avoided had people living in the path of the storm been warned, the head of the Association of Southeast Asian Nations (ASEAN) said Thursday.
The storm warning systems and cyclone watch centers in place were all up and running, but the cyclone's path to Myanmar across the Bay of Bengal on the Indian Ocean rim has been left out of the storm warning system, said Surin Pitsuwan, Secretary-General of ASEAN in a speech in Jakarta on Thursday.
Now, an estimated 100,000 people lay dead in the country and over a million people are homeless.
It's the second time people have failed to avert disaster in Asia despite having the right technology in the right place, he said. The first time was the 2004 Indian Ocean earthquake and tsunami. People in Hawaii knew a tsunami was coming ashore, but they did not know who to call, he said.
More
here.
Hackers Find a New Place to Hide Rootkits
Robert McMillan writes on InfoWorld:
Security researchers have developed a new type of malicious rootkit software that hides itself in an obscure part of a computer's microprocessor, hidden from current antivirus products.
Called an SSM (System Management Mode) rootkit, the software runs in a protected part of a computer's memory that can be locked and rendered invisible to the operating system but which can give attackers a picture of what's happening in a computer's memory.
The SMM rootkit comes with keylogging and communications software and could be used to steal sensitive information from a victim's computer. It was built by Shawn Embleton and Sherri Sparks, who run an Oviedo, Florida, security company called Clear Hat Consulting.
The proof-of-concept software will be demonstrated publicly for the first time at the Black Hat security conference in Las Vegas this August.
More
here.
Proposed Cyber Security Bill to Pressure DHS
Rob Lemos writes on SecurityFocus:
Rep. Jim Langevin, D-RI, introduced a bill on Wednesday that aims to hold the U.S. Department of Homeland Security responsible for investigating every cyber attack and for shoring up its network security.
The bill would better define the roles and responsibilities of the agency's chief information officer, require that the department reduce the number of successful attacks against its networks and mandate that the DHS investigate the state of contractors' network security before signing a contract with them. The bill comes after more than a year of investigations by the House of Representative's Committee for Homeland Security into cybersecurity breaches at numerous government agencies. Rep. Langevin heads up the Subcommittee on Emerging Threats, Cybersecurity and Science & Technology, which has held most of the hearings on the issues.
More
here.
Note: Also,
nice commentary by Mike Masnick on this foolishness over on techdirt.com. :-)
FBI is Called Slow to Join the Terrorism Fight
Richard B. Schmitt writes in The Los Angeles Times:
Nearly seven years after the Sept. 11 attacks, the FBI "has yet to make the dramatic leaps necessary" to become an effective intelligence-gathering organization and protect the country from terrorism, a congressional analysis released Thursday said.
The Senate Intelligence Committee recommended that the bureau yield more of its historic autonomy to the Office of the Director of National Intelligence and that "performance metrics and specific timetables" be established to address a variety of shortcomings.
The panel found widespread problems in the FBI intelligence program, including gaps in the training and deployment of hundreds of analysts hired since Sept. 11, 2001, to assess threats to the nation. Field Intelligence Groups, which are considered the front lines of the intelligence effort in FBI field offices around the country, are "poorly staffed, are led overwhelmingly by special agents, and are often 'surged' to other FBI priorities," the report said.
The bureau has also struggled to fill key national security and intelligence positions at FBI headquarters. The report found that more than 20% of the supervisory positions in the section at headquarters that covers Al Qaeda-related cases were vacant.
More
here.
FBI Says the Military Had Bogus Computer Gear
John Markoff writes in The New York Times:
Counterfeit products are a routine threat for the electronics industry. However, the more sinister specter of an electronic Trojan horse, lurking in the circuitry of a computer or a network router and allowing attackers clandestine access or control, was raised again recently by the F.B.I. and the Pentagon.
The new law enforcement and national security concerns were prompted by Operation Cisco Raider, which has led to 15 criminal cases involving counterfeit products bought in part by military agencies, military contractors and electric power companies in the United States. Over the two-year operation, 36 search warrants have been executed, resulting in the discovery of 3,500 counterfeit Cisco network components with an estimated retail value of more than $3.5 million, the F.B.I. said in a statement.
The F.B.I. is still not certain whether the ring’s actions were for profit or part of a state-sponsored intelligence effort. The potential threat, according to the F.B.I. agents who gave a briefing at the Office of Management and Budget on Jan. 11, includes the remote jamming of supposedly secure computer networks and gaining access to supposedly highly secure systems. Contents of the briefing were contained in a PowerPoint presentation leaked to a Web site, Above Top Secret.
A Cisco spokesman said that the company had investigated the counterfeit gear seized by law enforcement agencies and had not found any secret back door.
More
here.
Defense Tech: China's Cyber Forces
Via Defense Tech.
China is well known for its global cyber espionage efforts. And while the United States has received most of the media attention given to cyber attacks, we are not the only ones dealing with this issue. India is now pointing the finger at China, claiming they have systematically launched a series of attacks on sensitive information systems and networks of Indian agencies. India rapidly responded and now has cyber-security forces down to the division-level to guard against cyber wars. But is that really enough given China's stated ambitions?
China's Cyber Warfare Doctrine is designed to achieve global "electronic dominance" by 2050 which would include the capability of disruption of the information infrastructure of their enemies. This doctrine includes strategies that would disrupt financial markets, military and civilian communications capabilities as well as other parts of the enemy's critical infrastructure prior to the initiation of traditional military operations. With all the attacks that have been attributed to China, there has to be significant intelligence out there about techniques, cyber weapons and strategies that have been used in these cyber assaults. The proliferation of China's cyber capabilities will be the topic of a Congressional hearing in DC on May 20th.
More
here.
IRS Website Opens Door to Phishers

Chris Soghoian writes on the C|Net "surveill@nce st@te" Blog:
A new IRS Web site that allows taxpayers to check on the status of their refund checks could lead to users being phished.
The new "Where's my stimulus payment?" site asks taxpayers to enter in their Social Security number, and a few other trivial bits of information before informing the user of the amount of their refund, and the date it will be sent out.
While no doubt useful, this Web site sets a horrible example, and encourages dangerous behavior by users. Furthermore, in the hands of someone who knows the last four digits of a taxpayer's Social Security number, it could be used as an oracle (by submitting multiple requests) to determine the full SSN of a taxpayer.
More
here.
Image source: C|Net
U.S. Senate Report: Extremists Hone Internet Skills
Thomas Ferraro writes for Reuters:
Al Qaeda and other radical groups have dramatically increased their use of the Internet in recent years to lure and train recruits worldwide, a U.S. Senate report warned on Thursday.
The report by the Senate Homeland Security Committee found that these groups run production houses and distribution centers that digitally send anti-American messages to thousands of Web sites around the globe.
"Terrorists, whom some dismiss as people living in caves, are as sophisticated in their communication abilities today as most members of 'Generation Y,'" said committee Chairman Joseph Lieberman, a Connecticut independent.
"America is now vulnerable not just to attacks plotted by terrorists oceans away, as was the case with 9/11, but also to terrorism conceived within our own borders," Lieberman said.
More
here.
Spammers Abuse Yahoo's DomainKeys Authenticated Mail
Via heise Security News.
Spammers are abusing Yahoo's mail servers to bypass filters, according to the MessageLabs monthly report for April 2008 [.pdf]. They are digitally signing their email headers using Yahoo's DomainKeys Identified Mail (DKIM), thereby convincing spam filters that the email is legitimate.
Spammers are not sending their messages using Yahoo's web front end, but instead using the company's SMTP servers that allow Yahoo users to use any email client. According to MessageLabs, most of the spam sent in this manner using Yahoo Mail comes from the Yahoo! Plus server, which is a premium service. To create Yahoo accounts, Spammers are using automatic scripts, which, according to MessageLabs, are able to crack captchas.
In particular, the Spam clique known as Canadian Pharmacy uses Yahoo's servers. The report says this group used more than 1100 specially created email accounts during the period under review.
More
here.
Srizbi Botnet Spams 60 Billion Messages a Day
Darren Pauli writes on Computerworld Australia:
The Srizbi botnet has stormed over its competition to become the Internet's biggest spammer.
Researchers claim the botnet is responsible for 50 percent of all spam, and is the biggest of its kind in history.
It's 300,000 zombie computers are being worked hard. The much larger Storm Worm required about 500,000 nodes - with some figures even suggesting anywhere between 1 million to 50 million -- to deliver 30 percent of global spam.
Joe Stewart, director at US consultancy Secure Works, said the Srizbi Trojan is the biggest botnet in history and the most powerful. He said Srizbi, aka "Cbeplay" and "Exchanger", can blast out 60 billion messages a day.
More
here.
'I Was A Teenage Bot Master'
Dan Goodin writes on The Register:
One day in May 2005, a 16-year-old hacker named SoBe opened his front door to find a swarm of FBI agents descending on his family's three-story house in Boca Raton, Florida. With an arm in leg in casts from a recent motorcycle accident, one agent grabbed his good arm while others seized thousands of dollars worth of computers, video game consoles and other electronics. His parents looked on.
At that moment, some 2,700 miles away, in the Los Angeles suburb of Downey, California, the FBI was serving a separate search warrant on Jeanson James Ancheta, SoBe's 20-year-old employer and hacking mentor. It was the second time in six months Ancheta had been raided by the FBI, - a clear sign, had either bothered to notice, that their year-long botnet spree was unravelling.
More
here.
China Won't Guarantee Web Freedom Over Olympics
Ben Blanchard writes for Reuters:
China will not guarantee it won't censor the Internet over this summer's Beijing Olympics, nor can it guarantee to stamp out piracy of Olympic-branded goods, officials said on Thursday.
Wang Wei, executive vice president of the Beijing Olympic organizers, had promised media would have "complete freedom" to report over the event, but rights groups have regularly criticized China's commitment to that pledge.
China maintains a tight grip over the Internet, whose use is exploding in the world's most populous nation, preventing access to sites it considers anti-government, such as those of the banned spiritual group Falun Gong or Tibet independence groups.
More
here.
Chinese Espionage Alert in Belgium
Adrie van der Luijt writes on Director of Finance:
The Belgian government has warned of Chinese cyber attacks on its computer systems.
Justice minister Jo Vandeurzen said on Friday that the national intelligence service had traced attacks on governmental computer systems back to China.
So-called spyware - software used to obtain information from computers without authorisation - was found attached to emails sent to Belgium state departments.
"China is especially interested in Belgium, not just because we host the headquarters of both NATO and the European Union, but because of our ties with Africa," the minister said.
China obtains vast quantities of natural resources from Africa to fuel its booming industries.
The Dutch national intelligence service reported last week that similar attacks on high-security IT systems had taken place in The Netherlands.
These attacks were also traced back to China and focused on information related to the energy sector.
More
here.
Via InfoSec News.
U.S. Toll in Iraq

Via The Boston Globe (AP).
As of Wednesday, May 7, 2008, at least 4,073 members of the U.S. military have died in the Iraq war since it began in March 2003, according to an Associated Press count.
The figure includes eight military civilians. At least 3,319 died as a result of hostile action, according to the military's numbers.
The AP count is two more than the Defense Department's tally, last updated Wednesday at 10 a.m. EDT.
More
here.
And as always, the
Iraq Coalition Casualty Count keeps the grim watch on their website
here.
Honor the Fallen.
Mark Fiore: The United States of Guilt-by-Association

More Mark Fiore brilliance.
Enjoy!
- ferg
Via The San Francisco Chronicle.
Robotraff: A Hacker's Go-To For Clicks
Brian Krebs writes on Security Fix:
Anyone who doubts that Internet click fraud has become a big money maker should take a look at a Russian Web site called Robotraff.com, which bills itself as "the first stock exchange of Web traffic."
Set up a free account at Robotraff and you're ready to buy or sell Web traffic. Got 30,000 hacked personal computers under your thumb? Super! Now you can use those systems to generate a steady income just by pointing them at Web sites requested by a buyer.
Or maybe you're just getting started and you can't be bothered to build your own army of hacked PCs the old-fashioned way? No problem! Now you can set up a Web site that tries to exploit Web browser or browser plug-in vulnerabilities and simply buy all the traffic you need.
More
here.
Big Vendors Still Very Tardy on Fixing Security Flaws
Ryan Naraine writes on the eWeek "Security Watch" Blog:
Some of the biggest names in the IT software business still are very lax when it comes to fixing security holes reported by third-party brokers.
According to a list maintained by TippingPoint's Zero Day Initiative, Microsoft, Novell, Oracle, Computer Associates and Hewlett-Packard are among the vendors most tardy about shipping fixes for known flaws that could be used in code execution attacks.
Microsoft, for example, has nine "high risk" vulnerabilities on the list. Three of the nine Microsoft product flaws were reported more than 404 days ago.
More
here.
Mozilla: Firefox Plugin Shipped With Malicious Code - UPDATE
Robert McMillan writes on PC World:
Mozilla warned Wednesday that a malicious program inserted adware code into a Firefox plugin that has been downloaded thousands of times over the past three months.
Because of a virus infection, the Vietnamese language pack for Firefox 2 was polluted with adware, Mozilla security chief Window Snyder said in a blog posting. "Everyone who downloaded the most recent Vietnamese language pack since February 18, 2008 got an infected copy," she wrote. "Mozilla does virus scans at upload time but the virus scanner did not catch this issue until several months after the upload."
Mozilla is now going to add additional scans of its software to prevent this kind of thing from happening in the future, she said.
More
here.
UPDATE: 9 May 2008, 16:49 PDT: An update & clarification FAQ on this issue is available
here at the "Mozilla: For the Record" blog.
-ferg
Zero-Day Treasure Hunt: Researcher Hides IE Attack on The Web
Robert McMillan writes on InfoWorld:
Security researcher Aviv Raff has published code that would allow someone to take control of a computer running Internet Explorer, but there's a catch. He's not saying exactly where he's hidden the attack.
"Somewhere in my blog, I embedded a proof-of-concept code that exploits this zero-day vulnerability," Raff wrote in a Wednesday blog posting. A zero-day attack is a previously undisclosed software flaw that has not been fixed by the software maker.
The bug, which affects Internet Explorer 7 and IE 8, could allow an attacker to run unauthorized software on a victim's computer. Raff informed Microsoft of the flaw on Tuesday and the software vendor has not yet patched it, Raff said.
Microsoft didn't get much time to fix the bug, but Raff said he didn't feel that Microsoft would address the issue quickly unless he went public with the vulnerability.
More
here.
FBI Targets Internet Archive With Secret 'National Security Letter', Loses
Ryan Singel writes on Threat Level:
The Internet Archive, a project to create a digital library of the web for posterity, successfully fought a secret government Patriot Act order for records about one of its patrons and won the right to make the order public, civil liberties groups announced Wednesday morning.
On November 26, 2007, the FBI served a controversial National Security Letter on the Internet Archive's founder Brewster Kahle, asking for records about one of the library's registered users, asking for the user's name, address and activity on the site.
The Electronic Frontier Foundation, the Internet Archive's lawyers, fought the NSL, challenging its constitutionality in a December 14 complaint to a federal court in San Francisco. The FBI agreed on April 21 to withdraw the letter and unseal the court case, making some of the documents available to the public.
More
here.
Hacker Kept on News Corp. Payroll After Accused of Piracy
Tori Richards writes for Reuters:
A high-ranking News Corp official testified on Tuesday that he kept two hackers on the payroll for years after one of them was accused of infiltrating the security system of rival satellite television company DISH Network Corp.
Abraham Peled, a member of News Corp's executive management committee headed by Rupert Murdoch and CEO of affiliate NDS Group, said he continued to employ Christopher Tarnovsky after he was told by another former hacker that Tarnovsky posted information on the Internet to let users unscramble DISH's network and receive free service.
More
here.
McAfee: Trojan Adware Hiding in MP3s
Robert McMillan writes on PC World:
Adware pushers have found a new way to trick you into downloading their annoying products: fake MP3 files.
On Tuesday, security vendor McAfee reported that it's seen a huge spike in fake MP3 files spreading on peer-to-peer networks. Although the files have names that make them look like audio recordings, they're really Trojan horse programs that try to install a shoddy media player and adware on your computer, said Craig Schmugar, a researcher with McAfee.
More
here.
'Crimeware' Server Exposes Breadth of Data Theft
William Jackson writes on GCN.com:
Last month Researchers at online security company Finjan uncovered a 1.4 gigabyte cache of stolen data from North America, Europe, the Middle East and India on a Malaysian server that provided command and control functions for malware attacks in addition to being a drop site for data harvested from compromised computers.
“This is a unique example of what we have been talking about for the last year,” said Yuval Ben-Itzhak, chief technical officer at Finjan. Online thieves are using sophisticated tools to plant malicious code on legitimate Web pages, compromising visiting PCs and stealing data.
The data included 5,388 unique log files collected in just a three-week period. The files included personal and business e-mails, medical records, and financial log-in and transaction information with not only credit card and account numbers but also passwords and security codes. Although the trend of using Web exploits to steal and market personal data has been identified for some time, the discovery of the cache still was an eye-opener, Ben-Itzhak said.
More
here.
Washingtonpost.com Wants Identities of Readers Who Post Comments
Greg Sandoval writes on the C|Net News Blog:
If Jim Brady had his way, there would be no guaranteed anonymity for those who post comments to Washingtonpost.com.
Brady, executive editor of The Washington Post's online division, said during a panel discussion at the Digital Hollywood conference here that he would like to see a technology that could identify people who violate site standards--and if need be--automatically kick them off for good.
More
here.
Programming Note: Very Light Posting Again Today
Busy, busy with my day job today. Light posting later today.
Cheers,
- ferg
Tech Groups Back Kaspersky in Fight Against Zango
Brian Krebs writes on Security Fix:
A broad coalition of technology groups today told a federal appeals court to toss out a lawsuit that adware maker Zango is continuing to pursue against computer security vendor Kaspersky Lab, arguing that to do otherwise would harm consumers and the future of the security software market.
In May 2007, Bellvue, Wash.-based Zango -- a company that makes software to serve pop-up ads and tracks users' activities on behalf of online marketers -- sued Kaspersky, charging that the company interfered with its business by removing its "adware" without first alerting the user.
More
here.
Note: I personally support Kaspersky Labs and their position.
-ferg
Programming Note: Very Light Posting Today
My day job has me very busy today in meetings, etc. -- posting will be very light today and tomorrow.
Cheers!
-ferg
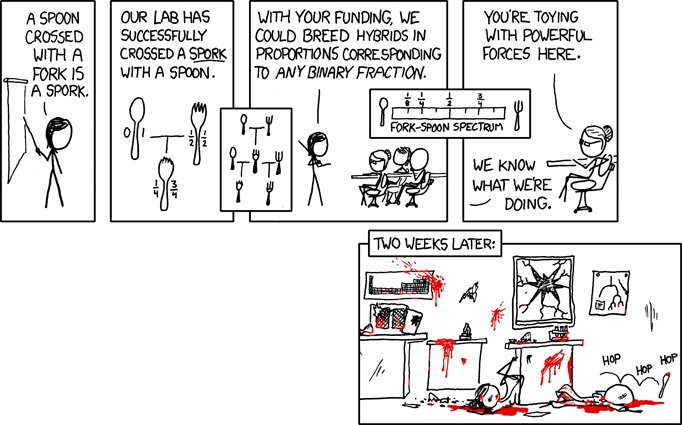
xkcd: Forks and Spoons
Click for larger image.
We
love xkcd.
- ferg
China Mounts Cyber Attacks on Indian Websites
Via The Times of India.
China’s cyber warfare army is marching on, and India is suffering silently. Over the past one and a half years, officials said, China has mounted almost daily attacks on Indian computer networks, both government and private, showing its intent and capability.
The sustained assault almost coincides with the history of the present political disquiet between the two countries.
According to senior government officials, these attacks are not isolated incidents of something so generic or basic as "hacking" — they are far more sophisticated and complete — and there is a method behind the madness.
Publicly, senior government officials, when questioned, take refuge under the argument that "hacking" is a routine activity and happens from many areas around the world. But privately, they acknowledge that the cyber warfare threat from China is more real than from other countries.
More
more.
Hat-tip: Flying Hamster
The Kent State Tragedy: 38 Years Later

We will always mourn the senseless tragedy at Kent State, 4 May 1970.Never Forget.