Wyndham Hotel Group Hacked
Via The Office of Inadequate Security.
If you stayed at a Wyndham hotel, check your mail, because you may be getting a letter from the chain telling you of a hack that occurred months ago.
In a letter [.pdf] to the New Hampshire Attorney General dated December 23, Wyndham Hotels and Resorts updated a notification sent to states attorney general back in early October about a breach involving their data center in Phoenix. The date of the breach and date of discovery were not indicated in the follow-up letter and the original notification to states attorney general is not currently available online.
More
here.
U.S. Toll in Iraq, Afghanistan

Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Friday, Jan. 2, 2009, at least 4,221 members of the U.S. military had died in the Iraq war since it began in March 2003, according to an Associated Press count.
The figure includes eight military civilians killed in action. At least 3,400 military personnel died as a result of hostile action, according to the military's numbers.
The AP count is the same as the Defense Department's tally, last updated Friday at 10 a.m. EST.
As of Friday, Jan. 2, 2009, at least 559 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Friday at 10 a.m. EST.
Of those, the military reports 406 were killed by hostile action.
More
here and
here.
And as always, the
Iraq Coalition Casualty Count keeps the grim watch on their website
here.
Honor the Fallen.
Some Kids' Cameras Coming With Viruses
Via WBZTV.com.
A popular digital camera for children is causing problems for at least one Minnesota family this Christmas. Some of Fisher-Price's Kid-Tough digital cameras have viruses that are affecting not just the camera, but computers as well.
Anna Tapper couldn't wait to tear open and try out her favorite present.
"I take pictures of lots of things," Anna said.
Her father, Jeff Tapper, said she had a big smile on her face the minute she knew what it was.
"She was glad to have her own camera and she didn't have to ask mom and dad for theirs and she could take as many pictures as she wanted," Tapper said.
When Tapper went to download her work, he found her camera had two viruses. Luckily, his anti-virus software spotted them before he downloaded them onto his computer. Without an up-to-date virus-fighter, his laptop could've been infected.
"Especially since it's a kid's digital camera it's the last thing you'd expect to have a virus on it," Tapper said.
More
here.
Hat-tip: Consumerist
Friday Monkey Blogging: Chimp Plays Surrogate to Tiger Cubs

As I mentioned a couple of months ago, I have started a regularly recurring blog entry meme every Friday afternoon, inspired by Bruce Schneier's regular series of "Friday Squid Blogging" posts, and my very own maddening Monkey Theory.
Here is this week's installment.
Via The Daily Mail.
When two white tiger cubs were born during a hurricane they had to be separated from their mother after their sanctuary flooded.
However they have since found an unlikely surrogate mother in chimpanzee Anjana, who has taken on the role of caring for the cubs.
The two-year-old chimp has been helping keeper China York care for the 21-day-old cubs at The Institute of Greatly Endangered and Rare Species (TIGERS) in South Carolina.
'Mitra and Shiva, were born during Hurricane Hannah,' said Dr Bhagavan, founder of TIGERS. "During that time everything flooded in the sanctuary and they had to be moved into the house as their mother became stressed.
'It was important for their safety that they were separated.'
Placed into the care of infant animal care giver China and her chimpanzee companion, Anjna, the cubs have become almost inseparable from their new motherly figures.
More
here.
Image source: Barry Bland / Barcroft Media / The Daily Mail
Gaza Cell Phones Targeted
Via Strategy Page.
As Israeli bombs began to fall on Gaza in the past week, Palestinians also found local radio and TV broadcasts interrupted, and replaced with messages from the Israeli armed forces, warning civilians, for their own safety, to stay away from Hamas personnel. Similar messages showed up on Palestinian cell phones. All this is nothing new.
During the last two years, Israeli Information War specialists hacked into the Syrian and Lebanese phone systems, and distributed messages meant to cause problems for Islamic terrorist groups. In the Syria incident, Israel sent thousands of messages to Syrians offering a $10 million reward for information on the whereabouts of missing Israeli soldiers. Syrian intelligence officials believed the campaign was more interested in recruiting intelligence agencies. Many Syrians thought it was all an attempt by their own government to find and identify disloyal citizens.
More
here.
Woman Fools Japan's Airport Security Fingerprint System

An AFP newswire article, via The Sydney Morning Herald, reports that:
A South Korean woman barred from entering Japan last year has reportedly passed through its immigration screening system by using tape on her fingers to fool a fingerprint reading machine.
The biometric system was installed in 30 airports in 2007 to improve security and prevent terrorists from entering into Japan, the Yomiuri Shimbun newspaper said.
The woman, who has a deportation record, told investigators that she placed special tapes on her fingers to pass through a fingerprint reader, according to Kyodo News.
Japan spent more than Y4 billion ($A64 million) to install the system, which reads the index fingerprints of visitors and instantly cross-checks them with a database of international fugitives and foreigners with deportation records, the Yomiuri Shimbun said.
More
here.
Hat-tip: Gizmodo
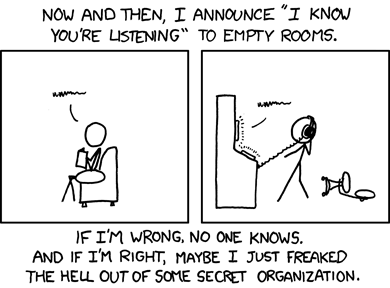
Classic xkcd: I Know You're Listening
Click for larger image.
We
love xkcd.
- ferg
Malware Blamed in Latest SAIC Breach
Via The Office of Inadequate Security.
Science Applications International Corporation ("SAIC"), recipient of a number of large government contracts, notified [.pdf] the New Hampshire Attorney General on December 9th of a security breach involving malware. The specific malware was not named, but was described as "designed to provide backdoor access."
If their description and explanation sounds familiar, it may be because SAIC had another breach almost a year ago where malware (a keylogger) also evaded their detection system. In that breach, it was mostly corporate account data at risk. The nature of the data in this most recent incident is of more concern due to its security implications.
More
here.
2009: The International Year of Astronomy

Via StarDate.org.
Astronomers are celebrating the 400th anniversary of the birth of modern observational astronomy in 2009. The International Year of Astronomy commemorates Galileo Galilei's first use of the telescope to study the night sky in 1609. He discovered that the surface of the Moon is rough, that the Milky Way consists of a vast number of stars, that Venus shows phases, and that moons orbit Jupiter.
His discoveries confirmed that Earth is not the center of the universe and demonstrated that the universe is both vast and dynamic -- discoveries that revolutionized human understanding of the cosmos and our place in it.
More
here.
Happy New Year

Happy New Year to All.
Mark Fiore: The New Year - On The March

More Mark Fiore brilliance on this New Year's Eve.
Via The San Francisco Chronicle.
Happy New Year - I wish all of you a new year of prosperity and happiness.
- ferg
2008: Another Brutal Year For Liberty

Glenn Greenwald writes on Salon.com:
Befitting an administration that has spent eight years obliterating America's core political values, its final year in power -- 2008 -- was yet another grim one for civil liberties and constitutional protections. Unlike the early years of the administration, when liberty-abridging policies were conceived of in secret and unilaterally implemented by the executive branch, many of the erosions of 2008 were the dirty work of the U.S. Congress, fueled by the passive fear or active complicity of the Democratic Party that controlled it.
The one silver lining is that the last 12 months have been brightly clarifying: It is clearer than ever what the Obama administration can and must do in order to arrest and reverse the decade-long war on the Constitution waged by our own government.
The most intensely fought civil liberties battle of 2008 -- the one waged over FISA and telecom immunity -- ended the way most similar battles of the last eight years have: with total defeat for civil libertarians.
More
here.
GeoPolitics: Russia's Woes Spell Trouble for The U.S.
Leon Aron writes in The Wall Street Journal:
Russia faces a particularly nasty version of the global recession (at a minimum), and perhaps an economic "perfect storm." Regardless of how bad its economy gets, two broad political trends, each carrying profound implications for Russia's foreign policy and U.S.-Russian relations, are bound to emerge.
The first will be a growing dissatisfaction with the government, which may lead to a political crisis. The second will be a reactionary retrenchment: increased internal repression and more of its already troubling foreign policy. Managing the relationship with Moscow in the face of these trends is something President-elect Barack Obama and his administration should start thinking about now.
More
here.
Muslim Hackers Attack Israeli Websites as Gaza Strikes Continue
Dan Kaplan writes on SC Magazine US:
Muslim hackers have launched a massive cyberattack, defacing more than 300 Israeli websites since the Jewish state began pounding Hamas targets in the Gaza Strip, a computer forensics expert said this week.
And operators of pro-Israeli websites operating in the United States should expect similar assaults to come their way, said Gary Warner, director of research in computer forensics at the University of Alabama at Birmingham.
"In the current situation, the hackers supporting Gaza clearly believe Israel and the U.S. are culpable," he wrote on his blog. "That means American webmasters may wish to be especially vigilant right now."
Warner called the spate of defacements a "Propaganda War," in which the Muslim hackers replace legitimate content with anti-Israeli and anti-United States messages.
More
here.
Toon of The Day: Change

Via: Daryl Cagle
Beltway Bandit Watch: Lockheed, Boeing Tap $11 Billion Cyber Security Market
Gopal Ratnam writes for Bloomberg News:
Lockheed Martin Corp. and Boeing Co., the world’s biggest defense companies, are deploying forces and resources to a new battlefield: cyberspace.
The military contractors, eager to capture a share of a market that may reach $11 billion in 2013, have formed new business units to tap increased spending to protect U.S. government computers from attack.
Chicago-based Boeing set up its Cyber Solutions division in August “because of a realization by the company that it’s a very serious threat,” Barbara Fast, vice president of the unit, said in an interview. “It’s not a question of if we’ll be attacked but when and so how will we be prepared.” Lockheed launched its cyber-defense operation in October.
More
here.
Hat-tip: CircleID
Adobe's Flash and Apple's Safari Fail a Privacy Test
Brad Stone writes on The New York Times' "Bits" Blog:
Mozilla’s Firefox, Google’s Chrome, Microsoft’s Internet Explorer and Apple’s Safari all compete to give users the most control over their online identities and the best protection from Web sites that use “cookies,” those unique identifiers that can track users online.
So how effective are the newest batch of browser privacy tools? Kate McKinley, a researcher at iSec Partners, a San Francisco security firm, sought to find out.
In a paper [.pdf] published Tuesday, Ms. McKinley found particular problems with Safari and concluded that none of the four major browsers extends its privacy protections to Adobe’s immensely popular Flash plug-in, which is used to display Web animations and video.
More
here.
Israeli Defense Forces Launches YouTube Gaza Channel
Max Socol writes on The Jerusalem Post:
In the midst of its Gaza operations, the IDF is entering yet another conflict zone: the Internet.
The Israeli army announced yesterday the creation of its own YouTube channel, through which it will disseminate footage of precision bombing operations in the Gaza Strip, as well as aid distribution and other footage of interest to the international community.
"The blogosphere and new media are another war zone," said Foreign Press Branch head Maj. Avital Leibovich. "We have to be relevant there," she said.
More
here.
Blair Still to be Top Spy, Despite Silence on Nomination
 Adm. Dennis C. Blair
Adm. Dennis C. Blair
Jeff Stein
writes on
SpyTalk:
Adm. Dennis C. Blair, the former Pacific forces commander who once coordinated military operations at the CIA, is still on tap to become the nation's next top intelligence officer, despite an unexplained delay of an official announcement from President-elect Obama, sources familiar with the process say.
Blair has been touted as a shoe-in for the nomination by unnamed congressional and other anonymous sources.
But weeks have passed since his name first surfaced as a cinch for the Obama administration's Director of National Intelligence (DNI).
Even in the absence of a formal announcement, however, Blair is being prepped for confirmation hearings on his expected nomination.
More
here.
U.S. Commission to Fund Research on China's Cyber Warfare Capabilities
Ben Bain writes on FCW.com:
A commission established by Congress to monitor issues important to the United States’ relationship with China is looking for a contractor to analyze the capabilities of the Chinese government and its affiliates to conduct cyberwarfare and exploit computer networks.
The U.S.-China Economic and Security Review Commission (USCC) issued a request for proposals Dec. 19 for a contract to produce a one-time unclassified report that would:
- Identify and assess major actors in China — state-affiliated and state-sponsored — who appear to be engaged in developing cyberwarfare capabilities.
- Explain how different organizations involved in those activities might be linked to one another.
- Assess the state of development of China's cyberwarfare doctrine.
- Provide a timeline of alleged Chinese-based hacking and intrusion into U.S. computer networks and those of U.S. allies.
- Analyze the vulnerabilities of U.S. government computer systems and civilian infrastructure and offer applicable policy recommendations.
USCC was created in October 2000 to investigate the national security implications of the trade and economic relationship between the United States and China and submit an annual report to Congress, with recommendations as appropriate. The leaders of the House and Senate appoint the commissioners.
More
here.
UK: Private Firm May Track All e-Mail And Calls
Alan Travis and Richard Norton-Taylor write on The Guardian:
The private sector will be asked to manage and run a communications database that will keep track of everyone's calls, emails, texts and internet use under a key option contained in a consultation paper to be published next month by Jacqui Smith, the home secretary.
A cabinet decision to put the management of the multibillion pound database of all UK communications traffic into private hands would be accompanied by tougher legal safeguards to guarantee against leaks and accidental data losses.
But in his strongest criticism yet of the superdatabase, Sir Ken Macdonald, the former director of public prosecutions, who has firsthand experience of working with intelligence and law enforcement agencies, told the Guardian such assurances would prove worthless in the long run and warned it would prove a "hellhouse" of personal private information.
"Authorisations for access might be written into statute. The most senior ministers and officials might be designated as scrutineers. But none of this means anything," said Macdonald. "All history tells us that reassurances like these are worthless in the long run. In the first security crisis the locks would loosen."
More
here.
Microsoft Removes Fake Security Software From 400,000 PCs
Gregg Keizer writes on CIO.com:
In the second month of a campaign against fake security software, Microsoft has booted the rogue application "Antivirus 2009" from almost 400,000 PCs, the company recently claimed.
December's version of the Malicious Software Removal Tool (MSRT), a free utility that Microsoft pushes to Windows users as part of Patch Tuesday, targeted one of the most popular phony security app, Antivirus 2009. According to Microsoft, the MSRT erased the fake from over 394,000 PCs in the first nine days after it released this month's edition on Dec. 9.
Last month, Microsoft trumpeted a similar cleaning operation against another family of bogus security software that it said had purged nearly a million machines of programs like "Advanced Antivirus," "Ultimate Antivirus 2008" and "XPert Antivirus."
More
here.
Researchers Use PlayStation Cluster to Forge a Web Skeleton Key
Kevin Poulsen writes on Threat Level:
A powerful digital certificate that can be used to forge the identity of any website on the internet is in the hands of in international band of security researchers, thanks to a sophisticated attack on the ailing MD5 hash algorithm, a slip-up by Verisign, and about 200 PlayStation 3s.
"We can impersonate Amazon.com and you won't notice," says David Molnar, a computer science PhD candidate at UC Berkeley. "The padlock will be there and everything will look like it's a perfectly ordinary certificate."
The security researchers from the U.S., Switzerland and the Netherlands planned to detail their technique Tuesday, at the 25th Chaos Communication Congress in Berlin.
More
here.
Napolitano Backs (Questionable) Security Tech
 Arizona Governor Janet Napolitano
Arizona Governor Janet NapolitanoThomas Frank
writes on
USA Today:
Gov. Janet Napolitano — President-elect Barack Obama's pick to run the Homeland Security Department — has strongly advocated using advanced security technology as a law enforcement tool, drawing praise from police and raising concern among civil liberties groups that warn about privacy invasion.
As Arizona's Democratic governor since 2003, Napolitano has:
- Pushed state police to use cameras that scan license plates of moving cars to find vehicles that are stolen or linked to a criminal suspect.
- Promoted "face-identification" technology that could help surveillance cameras find wanted people by comparing someone's face with a photo database of suspects.
- Signed a 2007 bill making Arizona one of 12 states that collect and store DNA samples of people accused but not convicted of certain crimes, including murder, burglary, sexual assault and prostitution.
- Proposed an optional state ID for legal citizens only that features a radio-frequency chip to allow authorities to read the card. State lawmakers blocked the effort this year.
"She sees technology as the panacea of all our law enforcement problems and immigration issues," said Alessandra Soler Meetze, head of Arizona's American Civil Liberties Union chapter. "It's like she's embracing these technologies without taking the time to appreciate the privacy implications."
More
here.
India: Chinese Mobile Handsets a Boon to Criminals?
Via The Times of India.
When 22-year old Jitendra Rathod was summoned to the Kanota police station and badly grilled for his alleged involvement in a kidnapping case, he was completely devastated. The police said that he had either kidnapped a girl from a village in the Kanota police station area or had aided the kidnappers. When he asked why he was being accused of this, the police told him that they had traced the mobile which the kidnapper had used.
Only then did Jitendra realize that the cute-looking Chinese mobile handset, he had bought recently was the cause of his woes. He claims that the culprit in the case has a Chinese mobile with the similar International Mobile Equipment Identity (IMEI) number due to which cops were harassing him.
This is just an example of what kind of security threat the Chinese mobile phones are posing. As it has become a much sought after product in the mobile phone market in the city these days, there are many victims of this national phenomena. This problem has recently come to the notice of central intelligence and security agencies after the recent terror strikes.
More
here.
Malicious Software Poses Growing Threat to U.S. Security
Loren B. Thompson writes for UPI:
Today, digital networks are so ubiquitous that their sudden disappearance would lead to economic collapse, and yet many people are barely aware they are relying on networks when they turn on the lights, go to the grocery store or seek medical care.
But the same features that make digital networks pervasive in everyday life also make them ready conduits for viruses, worms and other forms of malicious software that can destroy the wealth and welfare of unsuspecting users.
More ominously, clever attackers potentially can manipulate the system so it ceases to function entirely, leading to widespread deprivation, disorder and even defeat at the hands of a foreign power.
Recent trends in the evolution of cyber threats have led many experts to believe the danger is growing worse.
More
here.
Canada: Paying for E911 And Not Getting It - A Dangerous Proposition

Grant Robertson writes in The Globe and Mail:
Every month when cellphone bills arrive, Northern Canadians are forced to pay for a 911 service they can't access.
In recent years, cellphone companies have collected millions of dollars in 911 fees in less-populated regions across Canada where the emergency number is not offered, including Yellowknife.
Those charges are part of a much larger figure that is collected each year in the name of 911.
A Globe and Mail investigation into Canada's lagging 911 system has determined at least $13-million a month is collected in 911 fees on wireless bills across the country. However, the money is not necessarily spent on emergency services – even in places where 911 service is offered.
Instead, Industry Canada documents obtained through access to information laws show the government has been advised that some of the money is padding general revenues of the wireless industry.
More
here.
State Bank of India Shuts Website After Hackers Break In
Via The Business Standard.
The State Bank of India, the country’s largest bank, has had to shut down its corporate website after overseas hackers tried to break in.
While the bank said that transactions took place through www.onlinesbi.com, a senior SBI source said that the transactions were slow as the entire system was under watch.
The country’s largest bank decided to shut down its corporate website www.sbi.co.in on Wednesday evening when hackers blocked some of the pages. The bank also noticed unusually high traffic on its website on Wednesday.
Subsequently, the website was blocked with a ‘service unavailable’ or ‘our site is under maintenance’ pasted on www.sbi.co.in.
“We have informed the Reserve Bank of India and the cyber cell of the Mumbai Police, which are looking into the issue,” said a senior bank executive. The police and SBI suspect that the hackers are based overseas.
A Mumbai Police officer said that the cyber cell was investigating the complaint but did not share details: “It is big and the implications may be large.”
More
here.
Update: Via
The Times of India.
2008 Story of The Year: Barack Obama - The Road To The White House

Via 60 Minutes/CBS News.
60 Minutes and correspondent Steve Kroft began chronicling President-elect Barack Obama's road to the White House nearly two years ago, as the candidate declared his candidacy.
Over the course of the campaign, Kroft interviewed the long-shot candidate, his family and his closest advisors, for what turn out to be perhaps the biggest story in American political history.
More
here.
San Francisco Computer Engineer, Terry Childs, To Stand Trial
Bob Egelko writes on The San Francisco Chronicle:
A judge has ordered a computer engineer to stand trial on tampering charges for allegedly taking over the cyberspace network he designed for the city of San Francisco and refusing to reveal the passwords to access the system.
After an eight-day preliminary hearing, Superior Court Judge Paul Alvarado ruled Wednesday that prosecutors had produced enough evidence of Terry Childs' probable guilt to hold him for trial on four felony charges of tampering with a computer network, denying other authorized users access to the network and causing more than $200,000 in losses.
Childs, 44, of Pittsburg has been held in jail since July 13 on $5 million bail. He is scheduled to be arraigned Jan. 13.
Childs was a network administrator at San Francisco's Department of Telecommunication Information Services, where he worked for five years. The network he created and ran, FiberWAN, allows the city's computers to communicate with each other and handles 60 percent of the city's information, including sensitive law enforcement, payroll and jail booking records.
More
here.
Hat-tip: Pogo Was Right
FBI Notes 'Uptick' in Employment Scams
Tom Ramstack writes in The Washington Times:
Rising unemployment is turning more job seekers into victims of Internet scams.
The FBI is tracking an increase in Web-related schemes that promise large paychecks for a few hours of work per week from home. In some cases, the victims are unwittingly laundering ill-gotten money for unnamed "overseas investors."
"We are aware of what we would call a slight uptick in reports of fraud involving work-at-home scams," said Brian Hale, FBI spokesman.
The FBI's figures do not yet document the increase in the scams because they occurred only "in recent months" as unemployment rates continue rising, he said.
More
here.