JFK Assassination Anniversary Marked at Dallas Shooting Site

An AP newswire article by Andre Coe, via ABC News, reports that:
About 500 people crowded Saturday into the plaza where John F. Kennedy was shot 45 years ago, all agreeing it was right to remember a pivotal moment in American history, even if they didn't all believe the official line.
People stood shoulder to shoulder and bowed their heads during a moment of silence at 12:30 p.m. Some hawked JFK memorabilia or pitched conspiracy theories to visitors. Others offered firsthand accounts of their memories of the killing.
More
here.
JFK - The Movie

Interestingly enough, I've been watching the movie "JFK" on AMC tonight, which is the infamous rabble-rousing film directed by Oliver Stone that brought the assassination of JFK back into the spotlight over 15 years ago.
It's a great film, and if you've never seen it, you really should -- there are issues in the film that are based on fact (some are embellished a bit for dramatic license), some of which the public were never really clued into after the Warren Commission was concluded and published.
All in all, the assassination of John F. Kennedy began a new age in balancing the ultra-secret U.S. national security apparatus, the public interest, justice, and truth (although some are inclined to believe that we may never actually know what really occurred).
In any event, it's a very enjoyable film.
- ferg
22 November 1963: John F. Kennedy Assassinated
 John F. Kennedy motorcade, Dallas, Texas, Nov. 22, 1963.
John F. Kennedy motorcade, Dallas, Texas, Nov. 22, 1963.
The assassination of John F. Kennedy, the thirty-fifth President of the United States, took place on Friday, November 22, 1963, in Dallas, Texas, USA at 12:30 p.m. CST (18:30 UTC).
John F. Kennedy was fatally wounded by gunshots while riding with his wife Jacqueline Bouvier Kennedy in a Presidential motorcade.
The ten-month investigation of the Warren Commission of 1963–1964, the United States House Select Committee on Assassinations (HSCA) of 1976–1979, and other government investigations concluded that the President was assassinated by Lee Harvey Oswald. This conclusion was initially met with widespread support among the American public (1964–66), but polls conducted after the original 1966 Gallup poll show as much as 80% of the public hold beliefs contrary to these findings.
The assassination is still the subject of widespread speculation and has spawned numerous conspiracy theories, though none of these theories has been proven. In 1979, the House Select Committee on Assassinations (HSCA) found both the original FBI investigation and the Warren Commission Report to be seriously flawed.
The HSCA also concluded that there were at least four shots fired and that it was probable that a conspiracy existed. Later studies, including one by the National Academy of Sciences, have called into question the accuracy of the evidence used by the HSCA to support its finding of four shots.
Much more
here.
Image source: Wikimedia / U.S. Library of Congress
UK: Computer Virus in Hospitals May Have Been Planted Deliberately
Andrew Alderson writes on The Telegraph.co.uk:
Operations and blood testing have been postponed, and accident and emergency services have been disrupted after the computer service, used by up to 8,000 staff, had to be shut down.
One member of staff said it was feared that a computer expert, possibly a disgruntled former employer, had deliberately spread the virus. "This is a huge mess. It is a devastating incident – and probably a deliberate act," he said.
The three hospitals affected are St Bartholomew's Hospital, the Royal London Hospital and the London Chest Hospital, as well as an administrative headquarters.
A spokesman for the Barts and The London NHS Trust said yesterday: "This was a major internal incident."
More
here.
Belated Friday Monkey Blogging: Friendly Female Macaque Monkeys Love a Good Gossip

As I mentioned a few weeks ago, I have started a regularly recurring blog entry meme every Friday afternoon, inspired by Bruce Schneier's regular series of "Friday Squid Blogging" posts, and my very own maddening Monkey Theory.
Here is this week's installment (albeit a day late).
Via The Mail Online.
Female macaque monkeys love a good gossip as much as their chatty human counterparts, research has shown.
Scientists spent three months listening to a mixed group of macaques living on Cayo Santiago island off Puerto Rico.
They discovered that, just as with humans, the female of the species was more talkative than the male.
The experts counted the grunts, coos and 'girneys' - friendly chit-chat between two individuals - while ignoring calls specifically used when in the presence of food or a predator.
Female macaques were found to make 13 times as many friendly noises as males.
They were also much more likely to chat to other females than males.
The scientists believe this is because female macaques form solid, long-lasting bonds.
They stay in the same group for life, and rely on their female friends to help them look after offspring.
In contrast males, who rove between groups throughout their life, chatted to both sexes equally.
More
here.
Image source: The Mail Online
U.S. Toll in Iraq, Afghanisatn

Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Friday, Nov. 21, 2008, at least 4,202 members of the U.S. military have died in the Iraq war since it began in March 2003, according to an Associated Press count.
The figure includes eight military civilians killed in action. At least 3,393 military personnel died as a result of hostile action, according to the military's numbers.
The AP count is one fewer than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
As of Friday, Nov. 21, 2008, at least 556 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Friday at 10 a.m. EDT.
Of those, the military reports 404 were killed by hostile action.
More
here and
here.
And as always, the
Iraq Coalition Casualty Count keeps the grim watch on their website
here.
Honor the Fallen.
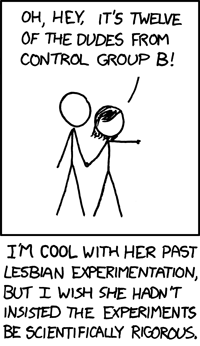
Classic xkcd: Experimentation
We
love xkcd!
Enjoy!
- ferg
ResellerClub to Take Over EstDomains' Domains
Via Domain Name Wire.
Although ICANN has not announced it yet, it appears that domain registrar ResellerClub is taking over domains managed at domain registrar EstDomains, which is losing its accreditation.
ResellerClub has emailed customers of EstDomains to tell them that it will be taking over.
More
here.
Hat-tip: Alex
Security Fix: Spamhaus: Microsoft Now 5th Most Spam Friendly ISP
Brian Krebs writes on Security Fix:
Microsoft is rising quickly on a running list of the Top 10 Worst Spam Service ISPs as maintained by Spamhaus.org, a group that tracks unsolicited commercial e-mail.
The software giant debuted on the list earlier this month at number 9 (one being the worst), and has slid over the past few days down to number 5. Spamhaus says spammers and scam artists are abusing Microsoft's live.com and livefilestore.com properties to redirect visitors to sites that peddle fake pharmacy products, porn and Nigerian 419 scams.
Richard Cox, Spamhaus's chief information officer, said spammers advertise the links at Microsoft's properties by the tens of thousands at a time, because they know anti-spam groups are unlikely to block Microsoft properties outright.
More
here.
Security Fix: Web Fraud 2.0: Faking Your Internet Address
Brian Krebs writes on Security Fix:
One of the casualties from the unplugging of McColo Corp. is fraudcrew.com, a Web service that offered paying customers the ability to hide their identities online by routing their traffic through computers controlled by others.
Fraudcrew, which has not been charged with any crime, offered subscribers a point-and-click way to mask the source of their Internet connections, so that Web sites could not tell the true location of visitors using the service. The site was advertised heavily on Russian online forums catering to computer hacking and identity theft.
There are a number of services like those offered by Fraudcrew (Security Fix profiled another one earlier this year) that not only aid in hiding one's identity online, but could also defeat security measures put in place by financial institutions. Many online banks will check to see whether the customer's Internet address is coming from a location already associated with the customer's user name and password, or at least from a geographic location that is close to where the customer lives.
More
here.
When Everyone Can Mine Your Data
Taylor Buley writes on Forbes.com:
Roelof Temmingh has a knack for stirring up trouble. The 35-year-old South African electronic engineer has fought legal battles with financial institutions, developed theoretical models for cyberterrorism and served as a technical adviser for a book about how hackers could take over the continent of Africa.
But Temmingh's latest exploit could make the most last impact. He has created a tool he calls Maltego that lets just about anybody do the kind of data mining that in the past only fraud investors, government specialists and hackers typically could do. Since Temmingh released the first commercial version of Maltego this past summer, even several national intelligence agencies have made use of the software, he says.
Temmingh's software scans open data repositories on the Web and allows users to match the results with their own data. (He calls this approach "open-source intelligence.") The data are then graphically depicted. The commercial version of Maltego lets users save these visualizations in popular data formats like XML so the information can be used by other programs.
More
here.
Hat-tip: Pogo Was Right
DoD Confirms Computer Virus in Networks
William H. McMichael and Bruce Rolfsen write in The Army Times:
The Defense Department confirmed Friday that a virus has infected some of its computer networks but declined to identify the infection, say whether it was a direct attack on the networks or confirm published directives that ban the use of portable storage media such as thumb drives.
“We are aware of a global virus for which there are some public alerts,” said Bryan Whitman, Pentagon spokesman. “And we’ve seen some of this on our networks. We’re taking steps to identify and mitigate the virus.”
Whitman wouldn’t characterize the infection further except to call it a “global issue” that also is affecting worldwide networks outside the Defense Department.
He also declined to confirm a ban on the use of thumb drives, although the ban was spelled out in at least two recent Air Force directives, one of which says the order comes from the Defense Department command that oversees the military computer domains shared by all the services.
More
here.
Interesting: MI6's Secret London Tunnels
Via The Economist.
Pedaling to work each day, I spend most of the journey looking out for London’s deadly, articulated “bendy buses”. The 60-foot beasts can happily scissor a cyclist while turning, so as I speed along High Holborn I have never given much of a second glance to the buildings that whizz past on each side.
That might be why I have never noticed anything unusual about 39 Furnival Street. A brick building in a row of offices, its black double-doors are unmarked and unremarkable. But if you stop for a moment and look up, you might reconsider that judgment. Above the entrance is an industrial-size cast-iron pulley—odd in a street of legal firms. Above that, curiouser still: a wide, gaping air vent of the sort that you might see at the top of a mine-shaft.
What lies inside was once subject to the Official Secrets Act. But now this mysterious property is up for sale, and so I find myself with a few other journalists on the other side of the doors, signing consent forms and handing in my mobile phone (whose signal had mysteriously vanished as soon as I crossed the threshold). A lift takes us down 100 feet, deeper than the London Underground, which we can hear rumbling above us. A set of atom-bomb-proof doors are swung open and we step out into the secret of Furnival Street: the Kingsway tunnels, a miniature city beneath a city.
More
here.
Details Emerge About Bush Administration's Cyber Plan
Wyatt Kash writes on GCN.com:
A new layer of details surrounding President Bush’s Comprehensive National Cyber Security Initiative emerged from a speech delivered by a senior federal official in Washington yesterday.
Steven Chabinksy, deputy director for the Joint Interagency Cyber Task Force, Office of the Director of National Intelligence, shed new light on 12 core initiatives that are part of the president’s cyber security plan. Much of the security plan, introduced last January under National Security Presidential Directive 54/Homeland Security Presidential Directive 23, has remained classified. And only limited amounts of information about the initiative have been made public.
Reciting concerns that new vulnerabilities, strong adversaries, and weak situational awareness were resulting in “untrusted systems,” Chabinsky outlined the objectives and rationale behind 12 “discreet initiatives” in the CNCI plan.
More
here.
Spammers Look East After McColo Shutdown
John Leyden writes on The Register:
One week after rogue ISP McColo was shut down spam levels have yet to return to normality. But security experts are under no illusions that this represents anything more than a temporary reprieve, which will probably come accompanied by a change in tactics by spammers.
The volume of spam in circulation fell by as much as two thirds after upstream providers pulled the plug on McColo, which harboured many of the command and control servers that controlled the world's spam distribution. Immediately prior to McColo’s shut down, these three botnets were ranked first, second and fifth the world’s most prolific sources of spam, altogether responsible for nearly 70 per cent of junk mail, according to net security firm Marshal8e6.
McColo hosted the command and control infrastructure for three of the world’s most prolific spam botnets: Srizbi, Mega-D and Rustock. IT systems were also used to peddle porn, support credit card fraud and other nefarious cybercrime activities.
These operations were too profitable to be abandoned, so its no surprise that backup connectivity systems were used over the following weekend to hand over control of compromised systems to servers in Russia. Security watchers reckon that the shutdown of McColo - which follows clampdowns against EstDomains and Intercage, other ISPs criticised for hosting dubious customers - will encourage cybercrooks to look east.
More
here.
Banking's Data Security Crisis
Andy Greenberg writes on Forbes.com:
Countrywide Financial may have become a poster child for U.S. financial institutions ruined by poisonous subprime loans--but junk assets, it turns out, weren't the only element of Countrywide's inner workings that were rotten.
So, allegedly, was one senior financial analyst in the company's subprime mortgage division. According to the reports of FBI officials who arrested him in August, 36-year-old Rene Rebollo spent his Sunday nights last summer copying a total of more than 2 million of Countrywide's customer records to a flash drive and selling the data to identity thieves.
Rebollo's case isn't as unique as banks would like to believe. If the wounded financial industry and its confused customers weren't suffering enough, add another crisis to the list: Cybersecurity and privacy analysts say American banks and financial services organizations are facing a major spike in data breaches, many of which are caused by company insiders siphoning sensitive data for profit.
More
here.
Obama's Cell Phone Records Improperly Accessed
Via CNN.com.
Records from a cell phone used by President-elect Obama were improperly breached, apparently by employees of the cell phone company, his transition team said Thursday.
Spokesman Robert Gibbs said the team was notified Wednesday by Verizon Wireless that it appears an employee improperly went through billing records for the phone, which Gibbs said Obama no longer uses.
In an internal company e-mail obtained by CNN, Verizon Wireless President and CEO Lowell McAdam disclosed Wednesday that "the personal wireless account of President-elect Barack Obama had been accessed by employees not authorized to do so" in recent months.
McAdam wrote in the e-mail that the phone in question has been inactive for "several months" and was a simple voice flip-phone, meaning none of Obama's e-mail could have been accessed.
The CEO also wrote the company has alerted "the appropriate federal law enforcement authorities."
Gibbs said that while the Secret Service has been notified, he is not aware of any criminal investigation. He said he believes it was billing records that were accessed.
More
here.
Kidnapped Hacker Found in Turkey, Arrested
Kevin Poulsen writes on Threat Level:
A Turkish computer hacker and informant who'd been allegedly kidnapped and tortured by a notorious ATM swindler was arrested this week, according to a report from the Turkish press.
Turkish police arrested Mert Ortac on computer hacking charges on Tuesday, reports Haber 7. Ortac, known under the hacker handle Kier, is an associate of another Turkish hacker called Cha0, who allegedly abducted him earlier this year.
More
here.
Programming Note: Happy 20th Anniversary, Trend Micro

Not a big deal, but I was off-line for a few hours this evening, attending a small party up in San Francisco celebrating Trend Micro's 20th Anniversary.
Any chance to have face-time with my CEO, a few drinks, good sushi, and good conversation is always a welcome distraction in my book.
It was fun.
Now, back to work. :-)
- ferg
IETF: Should We Ignore The Kaminsky DNS Bug?
Carolyn Duffy Marsan writes on NetworkWorld:
The Internet engineering community is grappling with what to do about a serious flaw in the DNS discovered this summer, and the ongoing debate brings to mind a famous quotation from Voltaire: "The perfect is the enemy of the good."
At issue is whether the group should use its resources to encourage DNS registries, ISPs and enterprises to upgrade to the ultimate DNS security solution known as DNSSEC; or whether it should tweak the DNS protocols to address the so-called Kaminsky bug as an interim step. The issue is being debated at a meeting of the IETF, the Internet's leading standards body, being held here [Minneapolis] this week.
More
here.
U.S. Panel Warns of Chinese Espionage
An AP newswire article by Foster Klug, via SFGate.com, reports that:
China has accelerated computer espionage attacks on the U.S. government, defense contractors and American businesses, a congressional advisory panel said Thursday.
The U.S.-China Economic and Security Review Commission also said in its annual report to lawmakers that aggressive Chinese space programs are allowing Beijing to more effectively target U.S. military forces.
"China is stealing vast amounts of sensitive information from U.S. computer networks," said Larry Wortzel, chairman of the commission set up by Congress in 2000 to advise, investigate and report on U.S.-China issues.
The commission of six Democrats and six Republicans said in the unanimously approved report that China's massive military modernization and its "impressive but disturbing" space and computer warfare capabilities "suggest China is intent on expanding its sphere of control even at the expense of its Asian neighbors and the United States."
The commission recommended that lawmakers provide money for U.S. government programs that would monitor and protect computer networks.
More
here.
Under Worm Assault, U.S. Military Bans Disks, USB Drives
Noah Shachtman writes on Danger Room:
The Defense Department's geeks are spooked by a rapidly spreading worm crawling across their networks. So they've suspended the use of so-called thumb drives, CDs, flash media cards, and all other removable data storage devices from their nets, to try to keep the worm from multiplying any further.
The ban comes from the commander of U.S. Strategic Command, according to an internal Army e-mail. It applies to both the secret SIPR and unclassified NIPR nets. The suspension, which includes everything from external hard drives to "floppy disks," is supposed to take effect "immediately." Similar notices went out to the other military services.
In some organizations, the ban would be only a minor inconvenience. But the military relies heavily on such drives to store information. Bandwidth is often scarce out in the field. Networks are often considered unreliable. Takeaway storage is used constantly as a substitute.
The problem, according to a second Army e-mail, was prompted by a "virus called Agent.btz." That's a variation of the "SillyFDC" worm, which spreads by copying itself to thumb drives and the like. When that drive or disk is plugged into a second computer, the worm replicates itself again — this time on the PC. "From there, it automatically downloads code from another location. And that code could be pretty much anything," says Ryan Olson, director of rapid response for the iDefense computer security firm. SillyFDC has been around, in various forms, since July 2005. Worms that use a similar method of infection go back even further — to the early '90s. "But at that time they relied on infecting floppy disks rather than USB drives," Olson adds.
More
here.
New York Police Fight U.S. DoJ Over Eavesdropping
 New York City Police Commissioner Raymond W. Kelly
New York City Police Commissioner Raymond W. Kelly
David Johnston and William K. Rashbaum
write in
The New York Times:
An effort by the New York Police Department to get broader latitude to eavesdrop on terrorism suspects has run into sharp resistance from the Justice Department in a bitter struggle that has left the police commissioner and the attorney general accusing each other of putting the public at risk.
The Police Department, with the largest municipal counterterrorism operation in the country, wants the Justice Department and the Federal Bureau of Investigation to loosen their approach to the federal law that governs electronic surveillance. But federal officials have refused to relax the standards, and have said requests submitted by the department could actually jeopardize surveillance efforts by casting doubt on their legality.
Under the law, the government must in most cases obtain a warrant from the special Foreign Intelligence Surveillance Court before it can begin electronic monitoring of people suspected of spying or terrorism. The requests are subjected to sharp scrutiny, first by lawyers at the F.B.I., then by lawyers at the Justice Department, and finally by the court itself.
New York’s department, as a local police force, cannot apply directly, but must seek warrants through the F.B.I. and the Justice Department. The police want those agencies to expedite their requests, and say that the federal agencies unfairly blocked the city’s applications for surveillance warrants, first in June and then in September. The disagreement, in which the Bush Justice Department has taken a more cautious approach than police officials, is something of an unexpected twist for an administration that has more often seemed willing to stretch legal boundaries to fight terrorism.
More
here.
Off Topic, Yet Offensive: Bush Set To Ease Endangered Species Rules
An AP newswire article, via MSNBC.com, reports that:
Animals and plants in danger of becoming extinct could lose the protection of government experts who make sure that dams, highways and other projects don't pose a threat, under a regulation the Bush administration is set to put in place before President-elect Obama can reverse them.
The rules must be published Friday to take effect before Obama is sworn in Jan. 20. Otherwise, he can undo them with the stroke of a pen.
The Interior Department rushed to complete the rules in three months over the objections of lawmakers and environmentalists who argued that they would weaken how a landmark conservation law is applied.
More
here.
Mark Fiore: Big Three Owner's Manual

More Mark Fiore brilliance.
Via The San Francisco Chronicle.
- ferg
Mexico: Arrest of Interpol Official Sparks Security Breach Concerns
Via CNN.com.
A vicious turf war between drug cartels and Mexican authorities that has left as many as 4,300 dead so far this year may have caused a breach in the internal security systems of Interpol, the international police organization.
Interpol, which is based in France, announced Wednesday it is sending a team of investigators to Mexico to investigate the possibility that its communications systems and databases are not being used for legitimate law enforcement purposes. The prospect was raised after the arrest of the top official working with the agency in the country.
Ricardo Gutierrez Vargas, director for International Police Affairs at Mexico's Federal Investigative Agency and the head of Mexico's Interpol office, was placed under house arrest Sunday, the attorney general's office said Tuesday.
More than 30 officials have been arrested since July in connection with the anti-corruption Operation Limpieza, an ongoing investigation into information leaks by law enforcement officials to drug traffickers, said Niverda Amado, a government press secretary in Mexico City.
More
here.
Turkey: Man Captured in Diyarbakır - Turns Out To Be PKK Hacker
Via Today's Zaman.
A man taken into custody on suspicion of theft last week has admitted that he is a hacker working for the terrorist Kurdistan Workers' Party (PKK), police investigators said Wednesday.
A police search of a computer belonging to R.Ç., 20, who was stopped in Diyarbakır on suspicion of theft, has revealed files containing classified information belonging to institutions including the General Staff and the National Intelligence Organization (MİT).
A search of the computer, seized coincidentally during a police raid against the sellers of stolen goods in Diyarbakır, revealed that the suspect had not only sent MİT documents to the PKK, but also had an "online friendship" with Murat Karayılan, the commander of PKK militants in northern Iraq. R.Ç. was arrested on Nov. 14 on charges of "acquiring state secrets and confidential documents in the name of the PKK terrorist organization".
More
here.
Hat-tip: Dissent
OSCE: Cyber Crime as Destructive as Credit Crisis
A Reuters newswire article, via eWeek, reports that:
Cybercrime is likely to wreak as much havoc as the credit crisis in the coming years if international regulation is not improved, some of the world's top crime experts said on Wednesday.
Damage caused by cybercrime is estimated at $100 billion annually, said Kilian Strauss, of the Organization for Security and Cooperation in Europe (OSCE).
"These criminals, they outsmart us ten, or a hundred to one," Strauss told Reuters, adding more internet experts were needed to investigate and tackle cybercrime.
Criminal organizations are exploiting a regulatory vacuum to commit internet crimes such as computer spying, money-laundering and theft of personal information, and the scope for damage is vast, experts told a European Economic Crime conference in Frankfurt.
More
here.
Voluntary Cyber Security Approach Not Good Enough
Ben Bain writes on Washington Technology:
The market-based, voluntary approach that the Bush administration has used to encourage companies to improve cybersecurity is not sufficient and the incoming Obama administration should form a cybersecurity social contract with industry based on economic incentives, according to a new report by a trade association.
The Internet Security Alliance (ISAlliance) released a report yesterday suggesting a cybersecurity social contract through which government would encourage and reward corporations by potentially working cybersecurity into procurement and loan processes, along with possible awards programs that could be used as marketing advantages.
The group said the voluntary approach laid out by the Bush administration has not been sufficient because it is missing incentives to encourage companies to invest beyond their corporate interests and for the greater public good of cybersecurity. The organization said government mandates were not the right approach, in part because of the global nature of the Internet and the negative effects they could have on U.S. industry.
More
here.
Polish Internal Security Agency Authorises The Scanning of Address Data on Letters
Via heise Security UK.
In a pilot project at the Posnan postal sorting office, Poland's largest internal security agency ABW has collected the sender and recipient information on letters as well as the relevant graphological details. Founded in 2002, the government agency for internal security deals with Poland's anti-terror policies, counterintelligence, prosecution of industrial and organised crime and anti-corruption measures.
As reported by the Dziennik daily newspaper – Google translation here, a modern scanner system is used for collecting the data and graphological details of senders and recipients in the city of Posnan, for forwarding to the ABW. The security agency intends to use this information for establishing a database that will allow the surveillance of all letter correspondence.
More
here.
UK: BNP Wants Police Probe After Membership List Published
Gavin Cordon writes on The Independent UK:
The far-right British National Party has demanded a police investigation after a full list of party members was posted on the internet.
The party said in a statement posted on its website that the list with the names, addresses and contact details of more than 12,000 individuals was "essentially genuine".
The list, which includes details of the jobs and in some cases the hobbies and qualifications of the members, claims to include former police officers as well as members of the armed forces.
BNP leader Nick Griffin said: "We'll be asking the police to investigate. It's a list which is now just over a year old.
"Having spent a lot of money to secure our members' privacy we are disappointed that it's been breached."
More
here.
Wiretapping in Russia (Too)
Robert Amsterdam:
It is not just an American problem... the following exclusive translation from News.ru reports that the Ministry of Information has announced that all telephone and internet service providers must allow unrestricted wiretapping and monitoring access for the FSB, despite the constitutional requirement of a court order.
We know from experience that this system has been in place for several years, but it is just now that the Ministry is making it publicly known.
Much more
here.
Hat-tip: Global VoicesNote: Yes, I realize that this blog post is from March 2008, but since I just came across it, it's news to me (well not really, but you get my meaning...)
-ferg
Jailed Russian Ex-Diplomat Leaves U.S. for Moscow
 Vladimir Kuznetsov
Vladimir KuznetsovA former Russian UN official, sentenced by a U.S. court to four years and three months in prison on money laundering charges, has left for Moscow after being handed over to Russian officials.
Kuznetsov, 50, who worked for the United Nations Advisory Committee on Administrative and Budgetary Questions, was arrested in September 2005 after borrowing $300,000 from a Russian colleague. U.S. investigators said that he was aware the funds had been acquired by criminal means.
The Russian held diplomatic immunity as a UN employee, but the status was revoked by Kofi Annan, the then-secretary general, paving the way for the FBI to arrest him.
The ex-diplomat was sentenced in October of 2007 by a U.S. district court, and was also ordered to pay a total of $73,000 in fines.
More
here.
Economic Bust, Cybercrime Boom
Andy Greenberg writes on Forbes.com:
The first ripples of a growing wave of cybercrime may be appearing.
In the physical world, the connection between declining business and crime is simple enough: As the above-ground economy suffers, the underground economy swells. The connection between economic trouble and cybercrime is trickier to prove. But as the economy slows, some crime watchers see signs that a portion of newly unemployed skilled tech workers are turning to the theft and exploitation of sensitive data even as the existing cybercriminal economy is finding new ways to exploit consumer confusion around the banking meltdown.
Meanwhile data on industry spending for security suggests that companies are preparing for the worst. Fear about the downturn's consequences for data protection has kept the cybersecurity industry practically recession-proof, even as other IT spending slumps.
More
here.
U.S. Teen Hacker 'DShocker' Confesses Three-Year Crime Spree
Dan Goodin writes on The Register:
A juvenile hacker with a reputation for stirring up trouble in online gaming groups has admitted to multiple computer felonies, including cyber attacks that overwhelmed his victims with massive amounts of data and the placing of hoax emergency phone calls that elicited visits by heavily armed police teams.
Known by the online handle of Dshocker, the 17-year-old Massachusetts hacker also admitted he breached multiple corporate computer systems, called in bomb threats and engaged in credit card fraud. The defendant, who was identified only by the initials N.H., pleaded guilty to charges in court documents that included one count each of computer fraud and interstate threats and four counts of wire fraud.
More
here.
European Commission Consults on Network and Information Security
Via OUT-LAW.com.
The European Commission has launched a consultation on how it can strengthen the European Union's response to computer attacks. The Commission is canvassing views ahead of a debate early next year about an EU-wide co-ordination of computer security.
A statement from the Commission said that responses to cyber-attacks from individual countries were inadequate and that countries must act together to ensure that information and networks are safe for users.
The Commission is holding an online consultation until January next year, when the results will be used to determine whether a coordinated policy will form a part of planned telecoms law reforms.
"Network and information security challenges will require a strong, coordinated European response," said the Commission statement. "Recent cyber-attacks targeting individual countries have shown that one country on its own can be very vulnerable."
In 2004 the Commission established the European Network and Information Security Agency (ENISA) to advise on and publicise the problems of network and information security. But after a 2007 Commission investigation found ENISA's impact to be "below expectations", it proposed transferring security concerns to a new telecoms regulator.
More
here.
UK: Computer Virus Affects Hospitals
Via The BBC.
Three London hospitals have been forced to shut down their entire computer systems for at least 24 hours after being hit by a virus.
St Bartholomew's (Barts) in the City, the Royal London Hospital in Whitechapel and The London Chest Hospital in Bethnal Green are affected.
A spokesman said well-rehearsed emergency procedures were in place.
More
here.
Hat-tip: Security Watch
Security Fix: 'Network Identity Theft' Politely Avenged
Brian Krebs writes on Security Fix:
A massive swath of some 65,536 unique Internet addresses that appear to have been swiped from early Internet pioneers by a convicted spammer has been reclaimed by Internet regulators, Security Fix has learned.
In April, Security Fix reported that a huge block of Internet addresses once assigned to San Francisco Bay Packet Radio -- an organization that was involved way back in the 1970s in testing the predecessor to the global commercial Internet that we all use today -- was being used to send e-mail for a company called MediaBreakaway. That company's chief executive is Scott Richter -- a self-avowed "spam king" who has been sued by a number of the Internet's biggest players -- including Microsoft and Myspace -- for sending spam.
When I was first presented with this information, I put the relevant questions to the American Registry for Internet Numbers (ARIN) -- one of five regional Internet registries worldwide that is responsible for allocating IP addresses. At the time, the ARIN people were very interested in the information I was reporting, but very reluctant to comment about it.
More
here.
Dead Network Provider Arms Rustock Botnet From The Hereafter
Dan Goodin writes on The Register:
McColo, a network provider that was yanked offline following reports it enabled more than half the world's spam, briefly returned from the dead over the weekend so it could hand-off command and control channels to a new source, security researchers said.
The rogue network provider regained connectivity for about 12 hours on Saturday by making use of a backup arrangement it had with Swedish internet service provider TeliaSonera. During that time, McColo was observed pushing as much as 15MB of data per second to servers located in Russia, according to Paul Ferguson, a security researcher for anti-virus software maker Trend Micro.
The brief resurrection allowed miscreants who rely on McColo to update a portion of the massive botnets they use to push spam and malware. Researchers from FireEye saw PCs infected by the Rustock botnet being updated so they'd report to a new server located at abilena.podolsk-mo.ru for instructions. That means the sharp drop in spam levels reported immediately after McColo's demise isn't likely to last.
More
here.
McColo: How Can So Much Spam Come From One Place?
Brian Krebs writes in The Washington Post:
At roughly 4:30 p.m. Eastern time last Tuesday, the volume of junk e-mail arriving at inboxes around the world suddenly plummeted by at least 65 percent, an unprecedented drop caused by what is believed to be a single, simple act.
According to security experts, one Silicon Valley based computer firm was playing host to computers of various organizations that controlled the distribution of much of the world's spam. Confronted with evidence tracing the spam activity back to the hosting firm, McColo Corp., Internet service providers pulled the plug, severing McColo's online connections.
By nearly all accounts, spam volumes have remained at far diminished levels, though experts interviewed for this story expect spam to soon bounce back or even exceed previous levels. But the question remains: How could such a massive concentration of spam activity be hosted for so long from the servers at a single U.S.-based facility, in the belly of the security and tech community in Silicon Valley?
More
here.
Note: Krebs has an accompanying article on this topic on
Security Fix here.
-ferg
U.S. Man Admits Illegal Space Data Exports to China
A Reuters newswire article, via Forbes.com, reports that:
Shu Quan-Sheng, 68, a native of China who is a naturalized U.S. citizen, entered the guilty plea in federal court in Norfolk, Virginia.
Shu is the president, secretary and treasurer of AMAC International, a high-tech company in Newport News, Virginia, that has offices in Beijing.
Shu admitted that from 2003 through October of 2007 he violated the U.S. arms export control law by providing China with assistance in the design and development of a cryogenic fueling system for space launch vehicles.
He admitted that in 2003 he violated the same law by exporting to China military technical data from a document about designing and making a liquid hydrogen tank and various pumps, valves, filters and instruments.
More
here.
FOIA Docs Show Feds Can Lojack Mobiles Without Telco Help
Julian Sanchez writes on ARS Technica:
Courts in recent years have been raising the evidentiary bar law enforcement agents must meet in order to obtain historical cell phone records that reveal information about a target's location. But documents obtained by civil liberties groups under a Freedom of Information Act request suggest that "triggerfish" technology can be used to pinpoint cell phones without involving cell phone providers at all.
Triggerfish, also known as cell-site simulators or digital analyzers, are nothing new: the technology was used in the 1990s to hunt down renowned hacker Kevin Mitnick. By posing as a cell tower, triggerfish trick nearby cell phones into transmitting their serial numbers, phone numbers, and other data to law enforcement. Most previous descriptions of the technology, however, suggested that because of range limitations, triggerfish were only useful for zeroing in on a phone's precise location once cooperative cell providers had given a general location.
This summer, however, the American Civil Liberties Union and Electronic Frontier Foundation sued the Justice Department, seeking documents related to the FBI's cell-phone tracking practices. Since August, they've received a stream of documents—the most recent batch on November 6—that were posted on the Internet last week. In a post on the progressive blog Daily Kos, ACLU spokesperson Rachel Myers drew attention to language in several of those documents implying that triggerfish have broader application than previously believed.
More
here.
Off Topic Geek: New Star Trek Movie Trailers Released

SoftLayer Technologies - Does the Cyber War 'Buck' Stop There?
Via IntelFusion.
President Truman made “The buck stops here” famous, but it remains as apropos today as it was back then. In this case, the question of where the buck stops is pertinent to any investigation into Cyber War operations.
As an example, SoftLayer Technologies (based in Plano, TX) leased an IP block to an unregistered company, Innovations IT Solutions Corp., operating out of a mail drop in London, which in turn hosted the Web forum StopGeorgia.ru, which was one of the coordinating points for the Russian hacker attacks against Georgia.
Had SoftLayer done even a minimum amount of due diligence, it would have discovered the flimsy background of its customer. In fact, as a company that StopBadware.org lists in their top ten worst network block owners and that the recent "McColo Cyber Crime USA" report lists in their top 5, you’d think that the executives at SoftLayer would be happy to up their scrutiny of their prospective customers. So far, no joy.
More
here.
Cyber Crooks Launch DDoS Assault On Anti-Fraud Site
John Leyden writes on The Register:
Unidentified miscreants have launched a denial of service attack on a UK-based anti-fraud website.
Bobbear.co.uk, which fights money laundering by warning about groups attempting to recruit mules, was left unreachable on Monday after coming under a distributed denial of service attack. Net security firm Sophos reports that the site was taken out by an assault from a botnet of compromised PCs that began late on Sunday. The timing of the assault coincides with the launch of Get Safe Online week in the UK.
It's pretty clear that Russian criminals are behind the attack and it is still continuing, site admin Bob Harrison told El Reg. "Undoubtedly it is simply a response to the work I do in highlighting the mainly Russian money laundering and reshipping frauds that are currently plaguing the internet and wrecking the lives of innumerable victims."
Harrison has reported the attack to the Met's computer crime unit and to Russian domains linked to the assault, more details of which can be found here.
More
here.
McColo -- Who Was Behind It?

Via The Threat Expert Blog.
Last week we all witnessed the shutdown of the hosting provider McColo that was widely known for its affiliation with cyber criminals.
An attempt to understand what McColo business was and who stood behind it led to some interesting discoveries.
According to the evidence mined from multiple underground forums, McColo company was established by a 19-year old Moscow student. His name was Nikolai and his nickname was Kolya-McColo - hence, the name of his "business".
Nikolai, the founder of McColo, died in a tragic accident in September 2007 during the drag racing on the streets of Moscow. At the time of the accident, he was in the car with his friend Jux. Their car has crashed into the pole at the speed of 200 Km/h - it was virtually torn in half...
More
here.
Image source: Threat Expert BlogSee also: The Lexsi-CERT Blog entry '
McColo Exposed'.
Toon of The Day: No Escape

By Mike Luckovich, via Truthdig.com.
Off Topic: 'In Soviet Russia, Time Travels You'
Via Neat-O-Rama (with props to Yakov Smirnoff).
Ever wonder what it would be like to be an oppressed citizen in the USSR in 1984? Here’s your chance. For a mere 220 American Dollars you can visit the newest, hippest theme park in Lithuania and be swept back into the glory days of Soviet Russia.
A past bunker of the Soviet Union has now been converted to a historical reenactment site.
More
here.
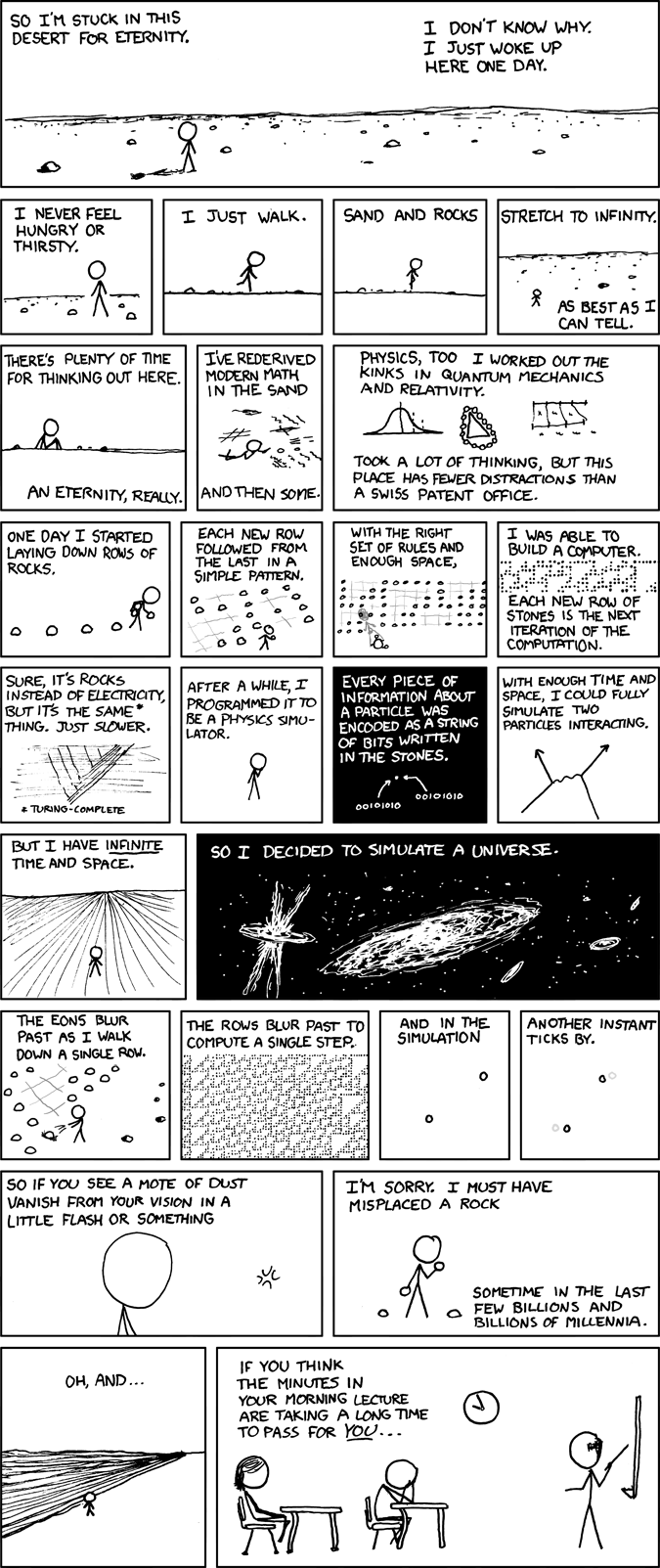
Classic xkcd: Vast Mental Array
Click for larger image.
We
love xkcd.
Enjoy!
- ferg
UK Identities Sold For £80 Online
Dominic Casciani writes for The BBC:
Internet fraudsters sell complete financial identities for just £80, according to an online safety group.
The details packaged and sold online include names, addresses, passport numbers and confidential financial data such as credit card numbers.
With six out of 10 people now managing finances online, experts say the public needs to do more to prevent e-crime.
The figure comes in data released as part of a week highlighting ways to protect identities online.
The Get Safe Online group, which is backed by police, government and banks, says ID theft is a serious problem because of an international trade in stolen identities and data.
More
here.
China: PLA Armor Brigade Exercise Fails Due to Computer Virus

Via The Dark Visitor.
According to news.ifeng, an unidentified PLA armor brigade was the victim of a computer virus that caused electronic ammunition resupply orders to show up blank. During the force-on-force, Red and Blue exercise, operations were hampered due to a computer virus that left the main attack force without ammunition resupply.
During the exercise, the Red Army basic command post, command and control station, received information from the main attack force that 3/4 of their ammunition had been depleted. A resupply order was immediately sent to the rear command post. However, after transmission, the order form appeared blank.
Ten minutes later, the main attack force once again sent a request for ammunition resupply. They were told to wait, that the request for resupply had already been processed. In the end, the main attack force had no hope of getting their ammunition. The ammunition was exhausted, people died [...in exercise simulation. -ferg] and the exercise was lost.
More
here.
Image source: Army Recognition