U.S. Toll in Iraq, Afghanistan

Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Saturday, Nov. 15, 2008, at least 4,200 members of the U.S. military have died in the Iraq war since it began in March 2003, according to an Associated Press count.
The figure includes eight military civilians killed in action. At least 3,390 military personnel died as a result of hostile action, according to the military's numbers.
The AP count is four higher than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
As of Saturday, Nov. 15, 2008, at least 555 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Friday at 10 a.m. EDT.
Of those, the military reports 403 were killed by hostile action.
More
here and
here.
And as always, the
Iraq Coalition Casualty Count keeps the grim watch on their website
here.
Honor the Fallen.
McColo Back on The Air: Does Telia Have A Clue? - UPDATE

Yes, McColo is back on the air.
With all of the damning evidence [.pdf] of illegal criminal activity inside of McColo, does Telia have the slightest idea?
Good question.
- ferg
UPDATE: 16 Nov 2008, 09:45 PST: Thanks to the assistance of some good folks at Telia, McColo has been disconnected (again):
AS Adjancency Report
26780 MCCOLO - McColo Corporation
Adjacency: 1 Upstream: 1 Downstream: 0
Upstream Adjacent AS list
AS1299 TELIANET TeliaNet Global Network
NOT Announced
This AS is not currently used to announce prefixes in the global routing table, nor is it used as a visible transit AS.
Prefixes added and withdrawn by this origin AS in the past 7 days.
- 208.66.192.0/22 Withdrawn
- 208.72.168.0/21 Withdrawn
- 208.72.173.0/24 Withdrawn
- ferg
Off Topic: More Threats Against Obama Since Election

An AP newswire article, via MSNBC.com, reports that:
Threats against a new president historically spike right after an election, but from Maine to Idaho law enforcement officials are seeing more against Barack Obama than ever before.
The Secret Service would not comment or provide the number of cases they are investigating. But since the Nov. 4 election, law enforcement officials have seen more potentially threatening writings, Internet postings and other activity directed at Obama than has been seen with any past president-elect, said officials aware of the situation who spoke on condition of anonymity because the issue of a president's security is so sensitive.
More
here.
Toon of The Day: White House Transition Tour

Image source: Bill Sanders
FOX News: Cyber Criminals Break Into IMF Computer Systems
Richard Behar writes on FOX News:
Another major international financial institution has had its computer system attacked by unknown cyber-hackers, FOX News has learned.
The discovery of the assault last week threw into crisis the Washington, D.C. based International Monetary Fund (IMF), which offers emergency financial aid to countries faced with balance-of-payments problems, and provoked a shutdown of IMF computers that lasted for several days.
In October, FOX News reported that the computer system at the World Bank had also been hacked over a period of months.
FOX News has been unable to determine what, if any, information may have been obtained by the hackers. The IMF denies any critical intrusion took place.
The spyware discoveries came at a particularly sensitive time for the international bailout institution, which along with the World Bank is expected to play a central role in trying to combat global financial turmoil. The pair of institutions are described on the IMF's website as the "twin intergovernmental pillars supporting the structure of the world's economic and financial order."
Both will be intensively discussed at this weekend's meeting of G-20 nations in Washington, hosted by President Bush, in the effort to put global finance back on a stable basis.
More
here.
Friday Monkey Blogging: Brain Signal Device Helps Monkeys With Paralyzed Wrists Play Computer Games

As I mentioned a few weeks ago, I have started a regularly recurring blog entry meme every Friday afternoon, inspired by Bruce Schneier's regular series of "Friday Squid Blogging" posts, and my very own maddening Monkey Theory.
Here is this week's installment.
An AP newswire article by Malcolm Ritter, via ABC News, reports that:
Monkeys taught to play a computer game were able to overcome wrist paralysis with an experimental device that might lead to new treatments for patients with stroke and spinal cord injury.
Remarkably, the monkeys regained use of paralyzed muscles by learning to control the activity of just a single brain cell.
The result is "an important step forward," said Dawn Taylor of Case Western Reserve University in Cleveland, who studies the concept of using brain signals to overcome paralysis. She wasn't involved in the new work.
The device monitored the activity of a brain cell and used that as a cue to stimulate wrist muscles electrically. Researchers found it could even use brain cells that normally had nothing to do with wrist movement, said study co-author Chet Moritz.
More
here.
Image source: Yves Herman / Reuters / ABC News
Image of The Day: Scam FAIL

Via the Fail Blog.
Enjoy!
- ferg
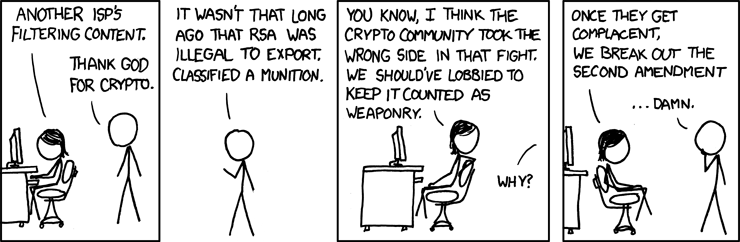
Classic xkcd: Legal Hack
Click for larger image.
We
love xkcd!
Enjoy.
- ferg
In a New History of NSA, Its Spies' Successes Are [Redacted]
Siobhan Gorman writes in The Wall Street Journal:
For much of its history, the government's most-secretive intelligence agency sought to conceal its very existence.
So it was a surprise last year when university researchers persuaded the National Security Agency to hand over a top-secret, 1,000-page account of its Cold War spying.
George Washington University plans to release the report today, giving historians a rare look inside the agency that gathers intelligence through eavesdropping. But one thing appears to be missing: Many of its biggest successes.
Not wanting to reveal too much, NSA blanked out sensitive chunks of the account that, according to intelligence experts, appear to chronicle espionage breakthroughs. What remains makes it appear that the world's largest ear has been a bit deaf.
According to the declassified report, government eavesdroppers generated half of their intelligence reports just after World War II from listening in on the French. Code breakers missed a key tip-off in the Cuban Missile Crisis. The report also suggests that, for the most part, the government couldn't crack high-grade Soviet communications codes between World War II and the 1970s.
More
here.
U.S. Intelligence Agencies Compete for Obama's Attention
Mark Hosenball and Michael Isikoff write on Newsweek.com:
Within hours of Obama's victory, the CIA appears to have touched off jostling among intelligence agencies. On Nov. 5, the day after the election, CIA Director Michael Hayden sent a message to agency employees affirming the "central part" that the CIA would play in the "Intelligence Community's outreach to the President-elect."
Hayden's message noted that McConnell would "launch" the intelligence community's first official briefing of the president-elect and his "incoming administration." The message went on to note that the CIA had "already prepared a great deal of information" about itself for Obama's team.
Citing Hayden's unclassified message, media outlets published stories about how the CIA had mobilized rapidly to provide Obama with the same kind of daily intelligence feed President Bush receives from McConnell. Last Monday, however, the Web site of the intel czar carried its own statement reasserting its central role in the transition process.
More
here.
Web-Borne Malware Targets Unexpected Industries
Neil Roiter writes on SearchSecurity.com:
The unprecedented barrage of Web-borne malware in 2008 is falling in very unexpected patterns, striking users in select -- and somewhat surprising -- verticals in far greater numbers than others.
A study, The Vertical Risk: Web-Delivered Malware Impact [.pdf] by Industry by ScanSafe Inc., analyzed how many times its Web security service blocked malware when users browsed compromised Web pages. The result showed the highest incidence in four startling verticals: energy and oil, pharmaceutical and chemical, engineering and construction, and transportation.
At the other extreme with the lowest incidence of blocking Web malware, were aviation and automotive, healthcare and insurance.
The question the research leaves unanswered is: "Why?"
More
here.
Internet Drug Peddlers Raided in Nine Countries
Via CBC News.
Authorities in nine countries have raided businesses suspected of supplying medicines illegally over the internet in an unprecedented global swoop co-ordinated by Interpol, officials said on Thursday.
The operation, codenamed Pangea, involved dozens of locations in Canada, Britain, Germany, Ireland, Israel, New Zealand, Singapore, Switzerland and the United States.
The raids on Wednesday mark the first time that such action has been taken on an international scale, an Interpol spokeswoman said.
Illicit sales of medicines via the web are a growing problem, since many of the products are counterfeits of dubious quality and potentially dangerous.
More
here.
Mark Fiore: State-Run Sacrament

More Mark Fiore brilliance.
Via The San Francisco Chronicle.
Enjoy.
- ferg
Termination of Registrar EstDomains to Go Ahead
Via ICANN.org.
The termination of ICANN-accredited registrar EstDomains is to go ahead, effective 24 November 2008.
On 28 October 2008, ICANN sent a notice of termination to EstDomains, Inc. (EstDomains) based on an Estonian Court record reflecting the conviction of EstDomains' then president, Vladimir Tsastsin, of credit card fraud, money laundering and document forgery.
Pursuant to Section 5.3 of the Registrar Accreditation Agreement (RAA), ICANN may terminate the RAA before its expiration when, "Any officer or director of [a] Registrar is convicted of a felony or of a misdemeanor related to financial activities, or is adjudged by a court to have committed fraud or breach of fiduciary duty, or is the subject of judicial determination that ICANN deems as the substantive equivalent of any of these; provided such officer or director is not removed in such circumstances."
ICANN received a response from EstDomains on 29 October in which it indicated that the Estonian Court record on which ICANN relied was not final and had been appealed. ICANN pended the termination of EstDomains' RAA to analyze the claims made by EstDomains and to obtain independent information regarding the status of the alleged appeal.
On 7 November 2008, EstDomains was informed that, based on ICANN's findings, ICANN was proceeding with the termination of EstDomains' RAA, effective 24 November 2008.
More
here.
Alleged Host of Internet Spam Groups is Cut Off
Brian Krebs writes in The Washington Post:
The gleaming, state-of-the-art, 30-story office tower in downtown San Jose, Calif., hardly looks like the staging ground for a full-scale cyber crime offensive against America. But security experts say a relatively small Web hosting firm at that location is home to servers that help manage the distribution of the majority of the world's junk e-mail.
According to these experts, the servers are operated by McColo Corp., a Web hosting company that has emerged as a major U.S. staging ground for international firms and syndicates that are involved in everything from the remote management of millions of compromised computers to the sale of counterfeit pharmaceuticals and designer goods, fake security products and child pornography.
But the company ceased to be reachable yesterday online, when two Internet providers turned off MoColo's connectivity to the Internet.
Officials from McColo did not respond to multiple e-mails, phone calls and instant messages left at the contact points listed on the company's Web site. It's not clear what, if anything, U.S. law enforcement is doing about the alleged activity happening at McColo. An FBI spokesman declined to offer a comment for this story. The U.S. Secret Service could not be immediately reached for comment.
Also unclear is the extent to which McColo could be held legally responsible for the activities of the clients for whom it provides hosting services.
More
here.
Internet Thieves Make Big Money Stealing Corporate Info
Byron Acohido writes on USA Today:
An innocuous posting appeared on a Houston-based technology company's internal website on a recent Friday afternoon.
A couple of workers saw it, and obeyed instructions to click on a Web link. The posting seemed trustworthy. It was on an employees-only message board. And the link referenced news about a favorite company charity.
By clicking on the link, the workers infected their PCs with a virus that shut down the company's antivirus defenses, says Don Jackson, director of Threat Intelligence at Atlanta-based SecureWorks, who investigated the break-in. As a rule, tech security firms help clients under non-disclosure agreements.
The virus swiftly located — and infected — some 300 other workstation PCs, silently copying the contents of each computer's MyDocuments folder. It transmitted the data across the Internet to a gang of thieves operating out of Turkey.
More
here.
Waging War In The Non-Existent Battlefield Of Cyberspace
A UPI newswire article by Lawrence Sellin, via SpaceWar, reports that:
Prompted by the collapse of the Soviet Union and the Internet revolution, Network Centric Warfare has become one of the latest iterations in attempts by the Department of Defense to formulate a coherent framework to transform our military forces and address future threats. It became the centerpiece of former Secretary of Defense Donald Rumsfeld's attempt to transform the U.S. military.
"We must achieve: fundamentally joint, network-centric, distributed forces capable of rapid decision superiority and massed effects across the battlespace," Rumsfeld said. "Realizing these capabilities will require transforming our people, processes, and military forces. U.S. forces must leverage information technology and innovative network-centric concepts of operations to develop increasingly capable joint forces. New information and communications technologies hold promise for networking highly distributed, joint and multinational forces."
As military historian and theorist Frederick W. Kagan once suggested, NCW diminished Pentagon angst by providing that framework to transform the force. That is, build everything around the network. The concrete manifestation was investment in precision munitions, the communications and analytical tools needed to provide them with targets, and the platforms needed to launch them.
More
here.
U.S. Intelligence Policy to Stay Largely Intact
Siobhan Gorman writes in The Wall Street Journal:
President-elect Barack Obama is unlikely to radically overhaul controversial Bush administration intelligence policies, advisers say, an approach that is almost certain to create tension within the Democratic Party.
Civil-liberties groups were among those outraged that the White House sanctioned the use of harsh intelligence techniques -- which some consider torture -- by the Central Intelligence Agency, and expanded domestic spy powers. These groups are demanding quick action to reverse these policies.
Mr. Obama is being advised largely by a group of intelligence professionals, including some who have supported Republicans, and centrist former officials in the Clinton administration. They say he is likely to fill key intelligence posts with pragmatists.
More
here.
No Prison Time for Romanian Hacker Who Targeted NASA and U.S. Navy Networks
Lucian Constantin writes on Softpedia:
Victor Faur from Arad, Romania, caught the international headlines in 2006, when he was indicted in the U.S. for one count of conspiracy and nine of computer intrusion, for obtaining unauthorized access to systems belonging to several government institutions. After a trial that lasted almost a year, a local Romanian court sentenced him to 16 months in prison, and requested that he pay $240,000 in restitution to the affected parties.
According to the evidence, Mr. Faur, going by the online nickname of SirVic, was the leader of a group of hackers known as the WhiteHat Team, who used the Undernet IRC network to communicate. From November 2005 to September 2006, he personally hacked into systems belonging to the U.S. Navy, NASA and the Department of Energy, from his home in Romania, thus transforming one of the NASA computers into an online chat server.
The U.S. authorities claimed that the damages caused amounted to $1.5 million, but Faur argued in his defense that he only hacked into those systems in order to prove that they were vulnerable, and that he did not cause any damage to them. According to him, he only targeted those servers because their group held regular contests to determine who was more skilled, and could hack into the most secure systems. In addition, he said that the accounts used to access the NASA servers had been provided to him by another Romanian hacker from Constanta, whom he only knew online.
The hacker could not be extradited because the agreement signed between Romania and the U.S. dated back to 1921, and did not include the new IT-related offenses. As a result, the U.S. authorities accepted him to be judged in Romania. According to Romanian law, if he had been found guilty on all accounts, Faur would have risked a maximum sentence of 12 years in prison, compared to the 54 years of prison time he might have received if judged in the U.S.
More
here.
Microsoft Security Patch Was Seven Years in the Making
Robert McMillan writes on PC World:
Some security patches take time.
Seven-and-a-half years, in fact, if you count the time it's taken Microsoft to patch a security issue in its SMB (Server Message Block) service, fixed Tuesday. This software is used by Windows to share files and print documents over a network.
In a blog posting, Microsoft acknowledged that "Public tools, including a Metasploit module, are available to perform this attack." Metasploit is an open-source toolkit used by hackers and security professionals to build attack code.
According to Metasploit, the flaw goes back to March 2001, when a hacker named Josh Buchbinder (a.k.a Sir Dystic) published code showing how the attack worked.
More
here.
McColo: Major Source of Online Scams and Spams Knocked Offline - UPDATE
Brian Krebs writes on Security Fix:
A U.S. based Web hosting firm that security experts say was responsible for facilitating more than 75 percent of the junk e-mail blasted out each day globally has been knocked offline following reports from Security Fix on evidence gathered about criminal activity emanating from the network.
For the past four months, Security Fix has been gathering data from the security industry about McColo Corp., a San Jose, Calif., based Web hosting service whose client list experts say includes some of the most disreputable cyber-criminal gangs in business today.
On Monday, Security Fix contacted the Internet providers that manage more than 90 percent of the company's connection to the larger Internet, sending them information about badness at McColo as documented by the security industry.
More
here.
UPDATE: 19:33 PST: See also
"The McColo Cyber Crime Report" at
HostExploit.com.
Major Vulnerabilities in Critical Infrastructure Exposed
Robert McMillan writes on Computerworld UK:
Computer systems that run the world's critical infrastructure are not secure and the people running them are concerned.
A survey released yesterday (10 November) asked management, network engineers and administrators in nine infrastructure industries about the state of cyber security in the US, Canada, and Europe.
Insiders felt that all of these industries, save financial services, were unprepared for cyberattacks. These unready industries included: water, utilities, oil and gas, telecommunications, transportation, emergency services, chemical and the shipping industry.
And that's bad news because more than half of them said that their companies had already been hit with some sort of cyber incident, data leak, or insider attack. Another 14 percent said they were expecting something like this to happen in the next year.
More
here.
Salute: Veterans Day 2008

Judge Rules Against White House in E-Mail Case
An AP newswire article, via The New York Times, reports that:
A federal judge ruled against the Bush administration in a court battle over the White House’s problem-plagued e-mail system.
The judge, Henry H. Kennedy Jr. of the United States District Court, said two private groups, Citizens for Responsibility and Ethics and the National Security Archive, may pursue their case as they press the administration to recover millions of possibly missing electronic messages.
The administration had argued that the courts did not have the power to order the White House to retrieve any missing messages. A document obtained by The Associated Press in August said the White House was missing as many as 225 days of e-mail dating to 2003 and invited companies to bid on a project to recover them.
More
here.
Australia: Russian Link in $4500 Online Theft
Karen Dearne writes on Australian IT:
Forensic investigators have traced evidence of a theft of $4500 from a Sydney woman's online bank account to a Russian server holding many more sensitive details captured by a Trojan horse hidden on her computer.
Sandra Bridekirk's brush with cybercrime began when she noticed two unauthorised deductions - each for $1485 - from her account with a major bank on two days last week.
When she rang the bank, she was told a third payment was programmed to occur that day. "The scary thing was that the transactions had been done with my personal access number and my password, and even my husband doesn't know those," she said.
"It was set up to keep taking money out - the sum is apparently just under our daily limit - every day until it was all gone."
Ms Bridekirk was told the payments had been made to an interstate bank account. The third transaction was stopped, but $3000 has been frozen until her bank and police finish their investigations. A further shock awaited Ms Bridekirk when an examination of her computer revealed all of her web credentials had been stolen - including all her user names and passwords, and her email address lists.
More
here.
One in Four DNS Servers Unpatched for Kaminsky Security Flaw, Study Finds
Brian Prince writes on eWeek:
New research offers a peak into the state of security of domain name server security – and it’s not all pleasing to the eye.
In an annual study of domain name servers (DNS) connected to the Internet by The Measurement Factory, it was uncovered that roughly one in four DNS servers does not perform source port randomization, despite the publicity surrounding the DNS vulnerability reported by security researcher Dan Kaminsky earlier this year.
The study, which was sponsored by Infoblox, also found that more than 40 percent of Internet name servers allow recursive queries. With the study estimating 11.9 million name servers are reachable from the Internet, the percentages means millions of name servers may be open to cache poisoning and distributed denial of service attacks.
More
here.
Japan: Hacking Arrests Doubled in 2007
Martyn Williams writes on CIO.com:
Arrests associated with unauthorized access to computers more than doubled in Japan in 2007 compared to the previous year, according to figures released by Japan's Ministry of Justice.
During 2007 a total of 1,442 arrests were made, up 703 arrests a year earlier, reported the ministry in its annual White Paper on Crime. The figure is 10 times the number of arrests made in 2003 for violations of the same law.
The country also saw a rise, although a much more modest one, in the number of crimes involving computers. There were a total of 3,918 arrests for such crimes, up 9 percent on the year.
More
here.
Toon of The Day: A Brief Lesson in Internet Filtering For Australia
.
 Click for larger image
Click for larger image.
Secret Order Lets U.S. Raid Al Qaeda in Many Countries
Eric Schmitt and Mark Mazzetti write in The New York Times:
The United States military since 2004 has used broad, secret authority to carry out nearly a dozen previously undisclosed attacks against Al Qaeda and other militants in Syria, Pakistan and elsewhere, according to senior American officials.
These military raids, typically carried out by Special Operations forces, were authorized by a classified order that Defense Secretary Donald H. Rumsfeld signed in the spring of 2004 with the approval of President Bush, the officials said. The secret order gave the military new authority to attack the Qaeda terrorist network anywhere in the world, and a more sweeping mandate to conduct operations in countries not at war with the United States.
More
here.
Bush Spy Revelations Anticipated When Obama Is Sworn In
Ryan Singel writes on Wired News:
When Barack Obama takes the oath of office on January 20, Americans won't just get a new president; they might finally learn the full extent of George W. Bush's warrantless domestic wiretapping.
Since the New York Times first revealed in 2005 that the NSA was eavesdropping on citizen's overseas phone calls and e-mails, few additional details about the massive "Terrorist Surveillance Program" have emerged. That's because the Bush Administration has stonewalled, misled and denied documents to Congress, and subpoenaed the phone records of the investigative reporters.
Now privacy advocates are hopeful that a President Obama will be more forthcoming with information. But for the quickest and most honest account of Bush's illegal policies, they say don't look to the incoming president. Watch instead for the hidden army of would-be whistle-blowers who've been waiting for Inauguration Day to open the spigot on the truth.
"I'd bet there are a lot of career employees in the intelligence agencies who'll be glad to see Obama take the oath so they can finally speak out against all this illegal spying and get back to their real mission," says Caroline Fredrickson, the ACLU's Washington D.C. legislative director.
More
here.
Internet Attacks Grow More Potent
John Markoff writes in The New York Times:
Attackers bent on shutting down large Web sites — even the operators that run the backbone of the Internet — are arming themselves with what are effectively vast digital fire hoses capable of overwhelming the world’s largest networks, according to a new report on online security.
In these attacks, computer networks are hijacked to form so-called botnets that spray random packets of data in huge streams over the Internet. The deluge of data is meant to bring down Web sites and entire corporate networks. Known as distributed denial of service, or D.D.O.S., attacks, such cyberweapons are now routinely used during political and military conflicts, as in Estonia in 2007 during a political fight with Russia, and in the Georgian-Russian war last summer. Such attacks are also being used in blackmail schemes and political conflicts, as well as for general malicious mischief.
A survey of 70 of the largest Internet operators in North America, South America, Europe and Asia found that malicious attacks were rising sharply and that the individual attacks were growing more powerful and sophisticated, according to the Worldwide Infrastructure Security Report. This report is produced annually by Arbor Networks, a company in Lexington, Mass., that provides tools for monitoring the performance of networks.
The report, which will be released Tuesday, shows that the largest attacks have grown steadily in size to over 40 gigabits, from less than half a megabit, over the last seven years. The largest network connections generally available today carry 10 gigabits of data, meaning that they can be overwhelmed by the most powerful attackers.
More
here.