Terrorists Slip Past TSA's Scientifically Untested Behavioral Threat Detection Program
Matthew Harwood writes on Security Management:
At least 17 suspected terrorists have evaded federal officers trained to spot suspicious behavior or signs of deception under an aviation security program the Government Accountability Office (GAO) describes as scientifically unreliable.
The GAO reports [.pdf] that the Transportation Security Administration (TSA) deployed the Screening of Passengers by Observation Techniques (SPOT) program "without first validating the scientific basis for identifying suspicious passengers in an airport environment."
Rep. John Mica (R-FL), the ranking member of the House Committee on Transportation and Infrastructure, seized on the report as one more instance of TSA ineffectiveness and waste. In a letter addressed to Homeland Security Secretary Janet Napolitano yesterday, Mica urged [.pdf] the secretary "to initiate immediate efforts for the reevaluation and reorganization of the entire TSA, a bureaucracy that has ballooned in size and cost, and... is teetering on the verge of disaster."
Rep. Mica also assailed the SPOT program's effectiveness, noting 17 suspected terrorists moved through eight SPOT airports on at least 24 different occasions. One of those suspected terrorists was the failed Times Square bomber Faisal Shahzad, who made it onboard an Emirates flight to Dubai at New York City's JFK Airport despite being on the terrorist watchlist and passing through a security checkpoint where the SPOT program operates. Federal authorities arrested Shahzad onboard the flight before it could take off.
More
here.
U.S. Intelligence Director Dennis Blair to Resign
 Dennis Blair
Dennis Blair
An AP newswire
article by Eileen Sullivan, via
MSNBC.com, reports:
National Intelligence Director Dennis Blair said Thursday he is resigning, ending a tumultuous 16-month tenure marked by intelligence failures and turf wars among the country's spy agencies.
Blair, a retired Navy admiral, is the third director of national intelligence, a position created in response public outrage over the failure to prevent the Sept. 11, 2001, terrorist attacks.
In a message to his work force, Blair said his last day would be May 28.
Two government officials said several candidates have been interviewed for the national intelligence director's job, which is to oversee the nation's 16 intelligence agencies. Both officials spoke on condition of anonymity because the announcement had not yet been made.
His term in office was marked by turf battles with the CIA director and controversial public comments in the wake of the abortive Christmas Day jetliner bombing.
More
here.
Bank of America Hires Former DHS Security Executive
Penny Crosman writes on Bank Systems & Technologies:
Bank of America has created a new position for data security — called "partnership executive for cybersecurity and identity management" — and hired Gregory Garcia, former assistant secretary for the Office of Cybersecurity and Communications in the U.S. Department of Homeland Security, to fill it.
According to his Wikipedia page, Garcia oversaw the National Cyber Security Division, the Office of Emergency Communications, and the National Communications System in Homeland Security from 2006 to 2008. He managed a $500 million annual budget and several hundred government employees and contractors by the time of his departure from the public sector.
In his new role at Bank of America, Garcia will lead the bank's relationships with public and private partners in cybersecurity and identity management and will contribute to the bank's strategies in those areas.
More
here.
Travelers to Australia to be Searched for Porn
Asher Moses writes on The Age:
Australian customs officers have been given new powers to search incoming travellers' laptops and mobile phones for pornography, a spokeswoman for the Australian sex industry says.
Fiona Patten, president of the Australian Sex Party, is demanding an inquiry into why a new question appears on Incoming Passenger Cards asking people if they are carrying "pornography".
Patten said officials now had an unfettered right to examine travellers' electronic devices, marking the beginning of a new era of official investigation into people's private lives. She questioned whether it was appropriate to search people for legal R18+ and X18+ material.
“Is it fair that customs officers rummage through someone's luggage and pull out a legal men's magazine or a lesbian journal in front of their children or their mother-in-law?” she said.
"If you and your partner have filmed or photographed yourselves making love in an exotic destination or even taking a bath, you will have to answer 'Yes' to the question or you will be breaking the law."
Customs confirmed the new reference to "pornography" on the Incoming Passenger Cards and the search powers, acknowledging that searches conducted by officers may involve the discovery of "personal or sensitive possessions".
More
here.
Mark Fiore: Inky Al-Jihadi

More Mark Fiore brilliance.
Via The San Francisco Chronicle.
- ferg
Harris' New Cyber Center Cloaked in Secrecy
David Hubler writes on Washington Technology:
Harris Corp. is building what it calls the nation’s first cyber integration center to provide government and commercial customers with a specialized managed hosting service in a trusted environment.
The new Harris Cyber Integration Center will be located in a recently acquired 140,000-square-foot facility in the mid-Atlantic region, according to a company announcement today.
Harris officials won’t disclose the center’s precise location yet for security reasons, saying only it will be within driving distance of the Washington, D.C., metropolitan area.
The company expects it to be fully operational by the end of the year.
More
here.
U.S. Judge Sides With Anonymous Online Flamers
Bob Egelko writes on The San Francisco Chronicle:
In a victory for anonymous critics of corporations, a federal judge in San Francisco has rejected a company's attempt to force Yahoo to identify the online commenter who called the firm's chief executive a "known liar" who believes "humanity exists to be fleeced."
"The First Amendment protects the rights of individuals to speak anonymously," U.S. District Judge Susan Illston said in ruling against USA Technologies. She said a target of anonymous online attacks must have evidence that the postings violated its rights and caused serious harm before enforcing a subpoena to disclose the speaker's identity.
USA Technologies filed a suit in its home state of Pennsylvania in August 2009 against the poster known as Stokklerk and sent a subpoena to Yahoo, which hosts a message board about the company, demanding the person's Web address. The suit claimed defamation and securities fraud, alleging that Stokklerk had financial interests in denigrating the company.
More
here.
U.S. House Votes to Expand National DNA Arrest Database
Declan McCullagh writes on C|NET News:
Millions of Americans arrested for but not convicted of crimes will likely have their DNA forcibly extracted and added to a national database, according to a bill approved by the U.S. House of Representatives on Tuesday.
By a 357 to 32 vote, the House approved legislation that will pay state governments to require DNA samples, which could mean drawing blood with a needle, from adults "arrested for" certain serious crimes. Not one Democrat voted against the database measure, which would hand out about $75 million to states that agree to make such testing mandatory.
"We should allow law enforcement to use all the technology available to them...to reduce expensive and unjust false convictions, bring closure to victims by solving cold cases, better identify criminals, and keep those who commit violent crime from walking the streets," said Rep. Harry Teague, the New Mexico Democrat who sponsored the bill.
But civil libertarians say DNA samples should be required only from people who have been convicted of crimes, and argue that if there is probable cause to believe that someone is involved in a crime, a judge can sign a warrant allowing a blood sample or cheek swab to be forcibly extracted.
"It's wrong to treat someone as guilty before they're convicted," says Jim Harper, director of information policy studies at the Cato Institute. "It inverts the concept of innocent until proven guilty."
More
here.
Rogue ISP Ordered to Liquidate, Pay FTC $1.08 Million
Casey Johnston writes on ARS Technica:
A rogue Internet service provider that hosted and participated in the distribution of spam, malware, and porn has finally been shut down as a result of a request made by the FTC to a district court judge. The ISP, 3FN, has had its servers and assets seized and has been ordered to turn over $1.08 million of its proceeds to the FTC.
The FTC first charged 3FN in June 2009 with a number of… really bad things. These included active recruiting of and working with criminals to distribute content such as spyware, trojan horses, phishing schemes, and pornography—including child porn. The FTC says 3FN advertised its services to like-minded people in the "darkest corners" of the Internet, like chat rooms for spammers.
3FN was accused of deploying and operating botnets and bot herders to send spam and execute denial-of-service attacks. It hosted the command-and-control servers that were responsible for the communication of information between the bot herders it recruited and the zombie computers used to mount attacks.
Though the FTC set its sights on taking 3FN down nearly a year ago, they've struggled to fully bring the ISP to its knees. 3FN operated under a number of names, including Triple Fiber Network, APS Telecom, APX Telecom, APS Communication, APS Communications, and Pricewert LLC, making it difficult to corral.
More
here.
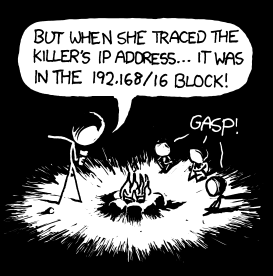
Classic xkcd: Campfire Horror Tales
We
love xkcd.
Rock on!
- ferg
Fraud Bazaar Carders.cc Hacked
Brian Krebs:
Carders.cc, a German online forum dedicated to helping criminals trade and sell financial data stolen through hacking, has itself been hacked. The once-guarded contents of its servers are now being traded on public file-sharing networks, leading to the exposure of potentially identifying information on the forum’s users as well as countless passwords and credit card accounts swiped from unsuspecting victims.
The breach involves at least three separate files being traded on Rapidshare.com: The largest is a database file containing what appear to be all of the communications among nearly 5,000 Carders.cc forum members, including the contents of private, one-to-one messages that subscribers to these forums typically use to negotiate the sale of stolen goods. Another file includes the user names, e-mail addresses and in many cases the passwords of Carder.cc forum users.
More
here.
Man Accused of DDoS'ing Conservative Talking Heads
Dan Goodin writes on The Register:
Federal prosecutors have accused a man of carrying out a series of botnet offenses including attacks that brought down the websites of conservative talking heads Bill O'Reilly, Ann Coulter, and Rudolph Giuliani.
Mitchell L. Frost was an undergraduate student at the University of Akron at the time of the DDoS, or distributed denial-of-service, attacks, which lasted over a five-day period in March 2008, prosecutors alleged in court documents. The attacks on billoreilly.com, anncoulter.com and joinrudy2008.com "rendered each website inoperable, at least temporarily, and required intervention and repair by the owners of such sites, and caused damages or losses which exceeded $5,000," they wrote.
More
here.
Marcus Ranum: U.S. Hypocrisy in China 'Cyber War'
Karen Dearne writes on Australian IT:
The recent China-US "cyberwar" exposed American hypocrisy on the issues of government surveillance and censorship, according to a US-based expert on security system design.
"Why is the country with the best technology for online surveillance of its citizens' communications taking other nations to task over censorship and free speech?" Mr Ranum, chief security officer of Tenable Network Security, challenged a packed forum at AusCERT 2010.
"For years, the US has embraced portions of the hacker community into our labs to build cyber-weapons, and there's government funding connections between our offensive weapons writers and our defensive weapons writers.
"We own the search engines everybody uses, and the incredibly valuable data they produce.
"So it's bizarre that in the recent exchange of accusations over China targeting dissident supporters of the Dalai Lama, no country asked the US to rein in its own cyber-hackers."
Mr Ranum said it wasn't necessary for US authorities to engage in cyber-spying or collect information from botnets because "by law, every carrier in the US has to back up all their systems so the FBI can do wiretaps".
More
here.
Note: Good point, Marcus!
- ferg
Cyberwar Cassandras Get $400 Million in Conflict Cash
Noah Shachtman writes on Danger Room:
Coincidences sure are funny things. Booz Allen Hamilton — the defense contractor that’s become synonymous with the idea that the U.S. is getting its ass kicked in an ongoing cyberwar — has racked up more than $400 million worth of deals in the past six weeks to help the Defense Department fight that digital conflict. Strange how that worked out, huh?
Everyone in the Pentagon from Defense Secretary Bob Gates on down says that the military needs to cut its reliance on outside contractors. But few firms are as well-connected as Booz Allen, the one-time management consultancy that today pulls in more than $2.7 billion in government work. And few firms sound the alarm as loudly about a crisis that they’re in the business of fixing. Back in February, for instance, former National Security Agency director and Booz Allen Hamilton executive vice president Mike McConnell declared that “the United States is fighting a cyber-war today, and we are losing.” The White House’s information security czar is one of many experts who calls such rhetoric overheated, at best. That hasn’t stopped Booz Allen from pocketing hundreds of millions of dollars from Washington to wage those battles.
More
here.
In Passing: Ronnie James Dio