U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Saturday Sept. 15, 2007, at least 3,780 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,086 died as a result of hostile action, according to the military's numbers.
The AP count is seven higher than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
FBI Calls CAN-SPAM Law 'Effective Tool'
A NetworkWorld article by Cara Garretson, via PC World, reports that:
While fighting cybercrime has become a bigger problem for law enforcement over the past 10 years, given increased involvement from organized-crime groups, officials are seeing some results from recent legislation and international coordination efforts.
Although the CAN SPAM Act has garnered criticism for not having enough teeth since it was passed in 2003, federal law enforcement is finding it effective in fighting spam of late, says Thomas Grasso, supervisory special agent with the FBI's National Cyber-Forensics and Training Alliance, who spoke at the Security Standard conference in Chicago last week.
One of the major challenges to U.S. law enforcement is the fact that so many cybercriminals operate overseas. But Grasso says there have been developments in international coordination as well.
More
here.
ADP Says Hackers Targeted Clients in Phishing Scam
Via Reuters.
Automatic Data Processing, the payroll processor, on Friday said hackers stole business contact information about clients from a third-party database and were now sending bogus and potentially harmful e-mails.
ADP said the information taken did not contain social security numbers, bank accounts, passwords or confidential data. ADP said its own systems were not attacked.
However, the stolen e-mail addresses were being used to send bogus e-mails that look like they have a valid ADP address. The fictitious e-mails, which began appearing about 24 hours earlier on Thursday, have "malicious" attachments and are believed to have been sent to compromise data of the recipients, ADP said.
More
here.
Terrorist Threat Risk Leaked on P2P Net
A ComputerWorld article by Jaikumar Vijayan, via PC World, reports that:
Officials at consulting firm Booz Allen Hamilton Inc. are looking into how a Fox News reporter acquired a confidential terrorist threat assessment on Chicago over a public file-sharing network.
Larry Yellen, an investigative reporter with WFLD Fox News in Chicago, on Tuesday reported that he recently used a peer-to-peer (P2P) program called LimeWire to obtain the Booz Allen document. The firm authored the document in 2002.
George Farrar, a spokesman for Booz Allen, Thursday confirmed the incident and said the document was commissioned by the Federal Transit Administration (FTA) five years ago. It was one of 35 threat assessments of the nation's bus and rail systems that Booz Allen was commissioned to do by the agency.
More
here.
Defense, Homeland Security Can't Pass Audits
An AP newswire article, via MSNBC, reports that:
Ten years after Congress ordered federal agencies to have outside auditors review their books, neither the Defense Department nor the newer Department of Homeland Security has met even basic accounting requirements, leaving them vulnerable to waste, fraud and abuse.
An Associated Press review shows that the two departments’ financial records are so disorganized and inconsistent that they have repeatedly earned “disclaimer” opinions, meaning that they simply cannot be fully audited.
“It means we really can’t put any faith in the numbers they use,” said Ross Rubenstein, who teaches public administration at Syracuse University’s Maxwell School.
More
here.
U.S. Toll in Iraq, Afghanistan
Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Friday, Sept. 14, 2007, at least 3,779 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,086 died as a result of hostile action, according to the military's numbers.
The AP count is six higher than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
As of Friday, Sept. 14, 2007, at least 374 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Sept. 8, 2007.
Of those, the military reports 248 were killed by hostile action.
More
here and
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
GNSO Consideration of Proposed Changes to WHOIS
Via ICANN.
In March, 2007, a WHOIS Task Force convened by the GNSO Council in June, 2005 completed its final report. The Task Force was asked to address important questions related to WHOIS. Key questions included the purpose of WHOIS service, which information should be available to the public, how to improve WHOIS accuracy and how to deal with conflicts between WHOIS requirements and relevant privacy laws. In the final report, a simple majority of members of the WHOIS Task Force endorsed a proposal called the "Operational Point of Contact" (OPOC).
Under OPOC, every registrant would identify a new operational contact and the technical and administrative contact details would no longer be displayed. The final WHOIS Task Force Report of 12 March, 2007 is posted at http://gnso.icann.org/issues/whois-privacy/whois-services-final-tf-report-12mar07.htm.
Public comments are invited via email until 00:00 UTC (17:00 PDT) on 30 October 2007 on the GNSO Council's WHOIS reports and recommendations.
Submit comments to: whois-comments-2007@icann.org.
View comments at http://forum.icann.org/lists/whois-comments-2007/
More
here.
Facebook Banner Ad Serves Up Exploits
Robert Vamosi writes on the C|Net News Blog:
Security researcher Roger Thompson got a surprise the other night when he borrowed a computer to view a friend's Facebook blog--Internet Explorer wanted to download some malicious Microsoft Data Access Components (MDAC) objects. That didn't seem right, so he tried another computer, and said "I got extra copies of the browser starting, and ads being served."
Thompson is no stranger to such tricks. He heads Exploit Prevention Labs, a company that specializes in finding and mitigating browser exploits found on Web pages. This attack really surprised him. It uses an exploit of MS06-014, which means if your computer has been updated with the latest patches from Microsoft issued since September 2006, you won't experience a thing. But if you haven't updated your Windows computer in more than one year, you'll be subjected to a barrage of unwanted adware.
More
here.
Quote of the Day: Weston Kosova
"If C-Span had sponsored a 'Blood and Treasure' drinking game, everyone in the hearing room would have been drunk before noon."
- Weston Kosova, writing in Newsweek.
Interpol Database on Terrorists Dramatically Grows
Via UPI.
Interpol said Friday its database on suspected terrorists has increased from 2,800 in 2002 to 11,800 now.
"Our database on suspected terrorists has increased from 2,800 in 2002 to 11,800 at present. We know that terrorists will travel on aliases and we have a database on stolen passports and travel documents," said Ronald Noble, secretary general of Interpol. He was in New Delhi to attend a three-day conference on cybercrime.
Noble said the transfer of funds through illegal channels and electronic routes for financing terrorist attacks worldwide was a difficult area, and member countries would have to work out measures to put an end to this practice. He said it was the most complex area of the investigation to track down people not known as suspected terrorists and companies not linked to terrorism.
More
here.
Hacked GOP Website Infects Visitors With Notorious Bot-Making Malware
Gregg Keizer writes on ComputerWorld:
A Republican Party Web site has been hacked, and for some time it has been spreading a variation of the long-running Storm Trojan horse to vulnerable visitors, a security researcher said today.
This is the first time that Storm has taken to the Web for its victims, said Dan Hubbard, head of research at San Diego-based Websense Inc. "The big news is that Storm has added infecting sites to its arsenal," said Hubbard.
Storm debuted in January but only cracked the top malware lists early this summer, and has become infamous for its ability to adapt its infection strategies.
More
here.
In Your Face: New Storm Spam Gets Right to the Point
 Click for larger image.
Click for larger image.Any spam that starts out by saying:
"OK! I'll get right to the point. I have large amount of funds on numerous bank accounts which needs to be laundered. I need your help to do that. You'll get 10% of each transaction coming into your bank account." "I can provide transaction of up to $5000."
...and also claims to be
"completely legal" is bound to spell trouble.
Yet, this is the latest "direct marketing"
social-engineering tactic being used by the Storm puppet-masters, and it contains links which lead to the website/forum pictured above.
And it has badness written all over it.
Other domains being served by this domain's nameservers have already been RBL'd:
 Click for larger image.
Click for larger image.Also, the nameservers are registered with a domain registrar in China, and the IP addresses are actually located in France (and elsewhere).
So, let's be careful out there.
Credit where credit is due: Symantec
Germany Backs Online Monitoring to Fight Terrorism
Via Reuters.
German Chancellor Angela Merkel said on Friday that Germany must allow security services to use the Internet to track terrorist suspects' online movements.
"It can't be that we create a space in which terrorists are completely safe and the state can't enter it," Merkel said in reference to the Internet at a conference in Berlin.
Interior Minister Wolfgang Schaeuble, a member of Merkel's Christian Democrats, is pushing to get clearance for Germany's Federal Crime Office (BKA) to carry out online searches.
More
here.
Boot Virus Shipped on German Laptops
Via Virus Bulletin News.
A consignment of laptops from German manufacturer Medion, sold through German and Danish branches of giant retail chain Aldi, have been found to be infected with the boot sector virus 'Stoned.Angelina', first seen as long ago as 1994 and last included on the official WildList in 2001.
According to German sources, anywhere between 10,000 and 100,000 systems may be infected, but as the machines apparently ship without floppy drives the virus is unlikely to spread. The systems come pre-installed with Windows Vista and Bullguard anti-virus, which will warn of the 'harmless' infection on booting the machines, but is unable to remove it.
More
here.
TJX Data Criminal Gets Five Years in Prison
Jon Brodkin writes on NetworkWorld:
The leader of an identity theft ring that stole credit card numbers from TJX has been sentenced to five years in prison and fined $600,000.
Irving Escobar of Miami, Fla., pleaded guilty to charges of an “organized scheme to defraud” in March and was sentenced this week, Florida Attorney General Bill McCollum announced Thursday.
Escobar and his team used stolen data to make counterfeit credit cards, which they used to buy gift cards at Wal-Mart and Sam’s Club. They redeemed the gift cards for jewelry and electronic equipment in what McCollum calls “a modern-day version of money laundering” that resulted in a loss of $3 million nationwide.
More
here.
TD Ameritrade Says Someone Stole Customer Information
An AP newswire article by Josh Funk, via The Chicago Tribune, reports that:
TD Ameritrade Holding Corp. said Friday one of its databases was hacked and contact information for its more than 6.3 million customers was stolen.
A spokeswoman for the Omaha-based brokerage said more sensitive information in the same database, including Social Security numbers and account numbers, does not appear to have been taken.
The company would not share many details of its investigation, including when the hack took place, because it is still looking into the theft and is cooperating with investigators from the FBI.
More
here.
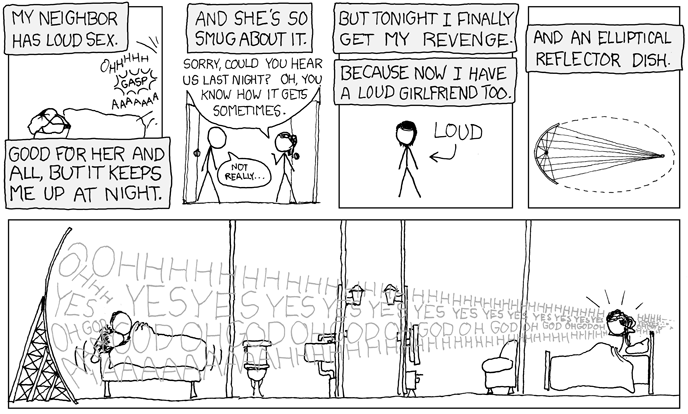
xkcd: Loud Sex
Click for larger image.
We
love xkcd.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Thursday, Sept. 13, 2007, at least 3,777 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,086 died as a result of hostile action, according to the military's numbers.
The AP count is four higher than the Defense Department's tally, last updated Thursday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
U.S. Consulate Website in St. Petersburg Hacked
Robert McMillan writes on InfoWorld:
Security vendors are warning that two U.S. Department of State Web sites based in Russia could contain malware and should be avoided.
The most serious compromise was on the Web site for the U.S. Consulate General for St. Petersburg. About a week ago, researchers at Sophos PLC discovered that the site had been hacked and was apparently serving up malicious software to visitors.
The compromise seems to have been short-lived. By the time researchers were able to check the site manually, the infection had been cleaned up. By looking at a cached version of the page in question, however, they were able to find the malicious code in question.
A State Department spokeswoman said she was unaware of any breach.
More
here.
SecureWorks: Analysis of Storm Worm DDoS Traffic
Via The SecureWorks Blog.
The Peacomm (Storm Worm) botnet is known to launch DDoS attacks against networks which appear to be investigating the botnet — the cyber equivalent of explosive reactive armor. It is still unclear whether the decisions to launch an attack are made by the botnet, a human operator, or both. In exploring this, SecureWorks was able to compile and analyze information regarding timing and types of traffic that may help victims of these distributed denial-of-service attacks mitigate the impact.
If triggering an attack is a decision made by the botnet that logic would be on the C&C (command-and-control) servers. Researchers have found no code in the Trojan client-side executable for triggering a DDoS attack.
The attacks do show signs of being automated. Certain actions reliably trigger attacks.
More
here.
Storm ALERT: Now Using Malicious Domain Name - UPDATE
 Click for larger image.
Click for larger image. While the Storm worm/botnet
has been using spams touting an "NFL Game Tracker" sites--which are, ironically, actually being hosted on Storm-compromised victim PCs-- to lure unwitting users to infected themselves, they have now registered a domain name that uses
fast-flux techniques to avoid consistent detection of the infected hosts (and it's nameservers) actual location(s).
Be forewarned: Do not surf to this domain.
Checking server [whois.estdomains.com]
Results:
Registration Service Provided By: LOMTI INC.
Contact: +351.3456712
Domain Name: FREENFLTRACKER.COM
Registrant:
PrivacyProtect.org
Domain Admin (contact@privacyprotect.org)
P.O. Box 65
All Postal Mails Rejected, visit Privacyprotect.org
Monster
null,2680 AB
NL
Tel. +45.36946676
Creation Date: 13-Sep-2007
Expiration Date: 13-Sep-2008
Domain servers in listed order:
ns13.freenfltracker.com
ns12.freenfltracker.com
ns11.freenfltracker.com
ns10.freenfltracker.com
ns9.freenfltracker.com
ns8.freenfltracker.com
ns7.freenfltracker.com
ns6.freenfltracker.com
ns5.freenfltracker.com
ns4.freenfltracker.com
ns3.freenfltracker.com
ns2.freenfltracker.com
Administrative Contact:
PrivacyProtect.org
Domain Admin (contact@privacyprotect.org)
P.O. Box 65
All Postal Mails Rejected, visit Privacyprotect.org
Monster
null,2680 AB
NL
Tel. +45.36946676
And, of course, ESTdomains is located in Russia, so the possibility of getting the domain suspended is somewhere in the neighborhood of slim & none.
We call this a "Double Flux" botnet because not only are the IP addresses constantly changing for the primary domain (FREENFLTRACKER.COM), but so are the nameserver IP addresses -- all of which are actually Storm-infected hosts of unwitting PCs.
Bad Ju-Ju.
- fergUPDATE: 13:45 PDT: Interesting enough, the WHOIS registration information for this domain now says:
Status:SUSPENDED
Note: This Domain Name is Suspended. In this status the domain name is InActive and will not function.
While that may, or may not, be true, it is still resolving at this moment. I'll see if it is just a DNS cache "ghost" in a few hours...
- ferg
Tokelau Cashes In On Domain Name
Claudine Beaumont writes in The Telegraph.co.uk:
Tokelau – comprised of three coral atolls that lie about 500 miles north of Western Samoa, halfway between New Zealand and Hawaii – has licensed the website domain extension assigned to the island, and is using the money it earns from the project to pay for computers and internet access.
Just as the United Kindgom was given the “.uk” suffix for use in website addresses, Tokelau was granted the “.tk” suffix for its website addresses.
In 2001, the island’s government was approached by Joost Zuurbier, an internet entrepreneur, with a view to his company licensing the rights to the website extension and sharing some of the revenue generated from these sites with the Tokelau government and its people.
Since the service launched in 2005, more than 1.6 million domain names with the “.tk” suffix have been created worldwide, and around 10,000 new sites are registered on a daily basis.
More
here.
California Moves Closer to Passing Data Breach Law
Jim Carr writes on SC Magazine Online:
California is a single signature away from passing a closely watched US bill that would require retailers to reimburse banks and credit unions for the costs of data breaches.
The California State Assembly this week unanimously ratified amendments to its assembly bill added by the state senate a week ago.
The bill, known as the Consumer Data Protection Act, now requires just the signature of California Governor Arnold Schwarzenegger to become law.
He is expected to sign the bill, and Keri Bailey, a state legislative and regulatory lobbyist for the California Credit Union League, said if he does - and he has until about mid-October to do so - California will become the second state with such a law; Minnesota has already passed similar legislation.
More
here.
Germany Arrests 10 in Global Internet Scam Raids
Via Reuters.
German police have arrested 10 people suspected of being involved in an international Internet scam which could have cost victims hundreds of thousands of euros, the Federal Police Office said on Thursday.
An 18-month-long probe resulted in raids in several German cities and the arrests of 10 Russians, Ukrainians and Germans who police think were involved in "phishing" -- or tricking people into revealing personal or financial details.
The group targeted bank customers who received emails purportedly from organizations like eBay Inc and Deutsche Telekom, said the office.
Attached to the emails was so-called Trojan horse software which records data entered in computers.
More
here.
Off Beat: One of My Own LOLcats... Timmeh
 Timmeh
TimmehWe have several related, grey,
polydactyl cats who have more than their normal complement of fingers and toes.
This little guy is
Timmeh -- named for the
"handi-capable" Timmy in Southpark.
Enjoy.
- fergImage made with LolCat Builder.
Interpol Wants Cyber Crime Combat Centers
An AP newswire article, via The Globe and Mail, reports that:
Interpol proposed on Wednesday the creation of global and regional anti-crime centres to fight criminal activity online and respond quickly to emergency cybercrime alerts.
The Internet should not be allowed to become a place where criminals have the upper hand and can escape punishment, Interpol Secretary-General Ronald K. Noble told an international cybercrimes conference in New Delhi.
Officials from 37 countries discussed identity theft, online bank fraud, Internet gaming and the risks of online terrorist activity during a two-day conference in the Indian capital. It was organized by France-based Interpol, the world's largest international police organization, with 186 member countries.
Creating global and regional anti-crime centres "is an ambitious idea, but we are determined to turn (it) into a reality because this problem is too big for even the G-8 and Council of Europe," Noble said. "It requires a truly global response."
The centres would help law enforcement around the world with investigations, training and accessing resources from a combined team of police officers and computer experts, he said.
More
here.
Online Retailer Fraud Losses Should Act As Warning
Via ComputerWorld UK.
[UK Retailer] Next has admitted its Next Directory online and catalogue business has suffered fraud losses of several million pounds in the first half of the year.
And the news has prompted security firms to warn that businesses are risking reputational damage where they fail to guard against external and internal security threats.
More
here.
U.S. Toll in Iraq, Afghanistan
Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Wednesday, Sept. 12, 2007, at least 3,773 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,085 died as a result of hostile action, according to the military's numbers.
The AP count is eight higher than the Defense Department's tally, last updated Wednesday at 10 a.m. EDT.
As of Wednesday, Sept. 12, 2007, at least 374 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Sept. 8, 2007.
Of those, the military reports 248 were killed by hostile action.
More
here and
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Intel Czar Mike McConnell Admits Testimony 'Error'
Michael Isikoff and Mark Hosenball write on Newsweek:
In a new embarrassment for the Bush administration top spymaster, Director of National Intelligence Mike McConnell is withdrawing an assertion he made to Congress this week that a recently passed electronic-surveillance law helped U.S. authorities foil a major terror plot in Germany.
The temporary measure, signed into law by President Bush on Aug. 5, gave the U.S. intelligence community broad new powers to eavesdrop on telephone and e-mail communications overseas without seeking warrants from the surveillance court. The law expires in six months and is expected to be the subject of intense debate in the months ahead.
On Monday, McConnell—questioned by Sen. Joe Lieberman—claimed the law, intended to remedy what the White House said was an intelligence gap, had helped to “facilitate” the arrest of three suspects believed to be planning massive car bombings against American targets in Germany. Other U.S. intelligence-community officials questioned the accuracy of McConnell's testimony and urged his office to correct it.
More
here.
Scientists Use the 'Dark Web' to Snag Extremists and Terrorists Online
Via The National Science Foundation (NSF).
Terrorists and extremists have set up shop on the Internet, using it to recruit new members, spread propaganda and plan attacks across the world. The size and scope of these dark corners of the Web are vast and disturbing. But in a non-descript building in Tucson, a team of computational scientists are using the cutting-edge technology and novel new approaches to track their moves online, providing an invaluable tool in the global war on terror.
Funded by the National Science Foundation and other federal agencies, Hsinchun Chen and his Artificial Intelligence Lab at the University of Arizona have created the Dark Web project, which aims to systematically collect and analyze all terrorist-generated content on the Web.
More
here.
Microsoft Updates Windows Without Users' Consent
Scott Dunn writes on Windows Secrets:
In recent days, Windows Update (WU) started altering files on users' systems without displaying any dialog box to request permission. The only files that have been reportedly altered to date are nine small executables on XP and nine on Vista that are used by WU itself. Microsoft is patching these files silently, even if auto-updates have been disabled on a particular PC.
It's surprising that these files can be changed without the user's knowledge. The Automatic Updates dialog box in the Control Panel can be set to prevent updates from being installed automatically. However, with Microsoft's latest stealth move, updates to the WU executables seem to be installed regardless of the settings — without notifying users.
More
here.
Markey Renews Calls for FCC Investigation Into Wiretapping
Jeffrey Silva writes on RCR Wireless News:
House telecom subcommittee Chairman Edward Markey (D-Mass.) repeated his call for the Federal Communications Commission to investigate widespread allegations of telecom privacy law violations by intelligence agencies that received cooperation from telecom carriers in anti-terrorist surveillance efforts.
“More than a year ago, I asked [FCC] Chairman [Kevin] Martin to exercise his authority as the head of the independent agency responsible for the enforcement of our nation’s communications laws to investigate the very serious reports that the intelligence agencies were using telephone companies to obtain phone records illegally,” said Markey in his latest letter to the FCC chief. “The continued reports of government intelligence agencies running roughshod over telecommunications privacy laws make it clear that the FCC should not wait to initiate this investigation.”
After Markey wrote Martin in March to ask him to launch an investigation into whether telecom privacy laws have been broken, the FCC chairman wrote Attorney General Alberto Gonzales to verify that the agency could not conduct such a probe because it would violate federal laws governing disclosure of state secrets. Gonzales, who recently announced his resignation, has yet to respond to Martin.
More
here.
Gromozon Malware Digitally Signed by Thawte

Alex Eckelberry writes on the Sunbelt Software Blog:
Gromozon (here as “Newtech, Inc. Panama”), one of the most notorious pieces of spyware out there, is digitally signed by Thawte (part of Verisign). This isn't the first time spyware has been signed by a certificate authority.
Wow -- it's stuff like this that sometimes makes you just throw your hands in the air. - ferg
More here.
Image source: Sunbelt Software
Image of the Day: Rat Chat

"If you do a pointless chat, you are helping spying rat."
Via A Soviet Poster a Day.
China Says It Has Suffered 'Massive' Internet Spy Damage
Chris Buckley writes for Reuters:
China has suffered "massive" losses of state secrets through the Internet, a senior official said, as China faces reports that it has raided the computer networks of Western powers.
Vice Minister of Information Industry Lou Qinjian said his country was the target of a campaign of computer infiltration and subversion and proposed a raft of counter-measures including toughened censorship, new security bodies and commercial controls.
He did not address recent Western allegations of cyber-spying against China.
More
here.
FISA Geek Alert: All Known Changes to FISA Since 9/11
Courtesy of Beverley Lumpkin via The POGO Blog.
David Kris has produced the single most valuable document ever created for the FISA nerd: a copy of the law as originally written in 1978, with all the changes enacted since Sept. 11, 2001, with each change helpfully color-coded (in SIX different colors!) so that you can keep track of what was added or subtracted when. I have been wallowing in it for the past 24 hours and highly recommend it.
More here.
Australia: China's Cyber Raid on Agencies
Patrick Walters writes on Australian IT:
China has allegedly tried to hack into highly classified government computer networks in Australia and New Zealand as part of a broader international operation to glean military and commercial secrets from Western nations.
The Howard Government yesterday would neither confirm nor deny that its agencies, including the Defence Department, had been subject to cyber attack from China, but government sources acknowledge that thwarting such assaults is a continuing challenge.
"It's a serious problem, it's ongoing and it's real," one senior government source told The Australian.
Western intelligence experts say that China has also targeted the US, Canada, Germany and Japan as part of its global intelligence-gathering effort.
More
here.
Who Needs Hackers? Complex Systems Break in Complex Ways
John Schwartz writes in The New York Times:
“We don’t need hackers to break the systems because they’re falling apart by themselves,” said Peter G. Neumann, an expert in computing risks and principal scientist at SRI International, a research institute in Menlo Park, Calif.
Steven M. Bellovin, a professor of computer science at Columbia University, said: “Most of the problems we have day to day have nothing to do with malice. Things break. Complex systems break in complex ways.”
When the electrical grid went out in the summer of 2003 throughout the Eastern United States and Canada, “it wasn’t any one thing, it was a cascading set of things,” Mr. Bellovin noted.
That is why Andreas M. Antonopoulos, a founding partner at Nemertes Research, a technology research company in Mokena, Ill., says, “The threat is complexity itself.”
More
here.
Online Thugs Assault Sites That Specialize in Security Help
Erik Larkin writes on PC World:
The good guys are taking a hit in the ongoing online war between the thugs who profit from phishing and malware, and those who work to stop them.
For two weeks, Web sites like CastleCops.com, which offers help to those hit by malware and also actively works to shut down malicious Web sites, have been under attack. In what's known as a distributed denial of service, black hats are flooding CastleCops with a barrage of garbage data in an attempt to overwhelm the site and knock it offline.
More
here.
Bin Laden, Brought to You by...
Joby Warrick writes in The Washington Post:
Early yesterday morning, a South Carolina Web designer who works at home managed to scoop al-Qaeda by publicly unveiling its new video, a feat she has accomplished numerous times since 2002. Within hours, cable news stations were broadcasting images of Osama bin Laden commemorating the Sept. 11, 2001, terrorist attacks, and crediting the 50-year-old woman, who uses the pseudonym Laura Mansfield.
A similar event occurred on Friday, when another group beat al-Qaeda by nearly a full day with the release of the first video images of bin Laden to appear publicly since 2004. That group, known as the SITE Institute, provided the tape to government agencies and news organizations, at a time when many well-known jihadist Web sites were literally silenced, shut down in a powerful cyberattack by unknown hackers.
More
here.
Cyber Spies Target Silent Victims
Andy Greenberg writes on Forbes.com:
The U.S. Department of Defense confirmed last week that cyberspies have been sifting through some government computer systems. What wasn't said: The same spies may have been combing through the computer systems of major U.S. defense contractors for more than a year.
"There's been a massive, broad and successful series of attacks targeting the private sector," says Alan Paller, director of the SANS Institute, a Bethesda, Md.-based organization that hosts a response center for companies with cybersecurity crises. "No one will talk about it, but companies are creating a frenzy trying to stop it."
Paller believes that the 10 most prominent U.S. defense contractors--including Raytheon, Lockheed Martin, Boeing, and Northrop Grumman--have, for the past 14 months, been the victims of the same sort of cyberespionage that has recently plagued the Pentagon.
He and other experts warn that the classified military technology research held by these private sector companies is even more vulnerable to hackers than the data stored on government computers. And while the U.S. government publicizes its security breaches, researchers say these commercial contractors almost always keep their data losses out of the public eye.
More
here.
University Researchers Analyze China's Internet Censorship System
Via Government Technology.
The "Great Firewall of China," used by the government of the People's Republic of China to block users from reaching content it finds objectionable, is actually a "panopticon" that encourages self-censorship through the perception that users are being watched, rather than a true firewall, according to researchers at UC Davis and the University of New Mexico.
The researchers are developing an automated tool, called ConceptDoppler, to act as a weather report on changes in Internet censorship in China. ConceptDoppler uses mathematical techniques to cluster words by meaning and identify keywords that are likely to be blacklisted.
More
here.
Russia Launches New Military Satellite
An Interfax newswire article, via Space.com, reports that:
The Russian Space Forces launched a Kosmos-3M rocket carrying a military satellite from the Plesetsk space center on Tuesday, Lt. Col. Alexei Zolotukhin, a spokesman for the Russian Space Forces, told Russia's Interfax News Agency.
The satellite will serve the Russian Defense Ministry's purposes and will join the Russian military satellite constellation, he said.
More
here.
Security at Job Websites Faulted
Joseph Menn writes in The Los Angeles Times:
In the face of criticism that they provided fertile ground for Web predators, online job sites have responded by posting warnings about work-at-home schemes and positions forwarding money or potentially stolen goods.
But they have failed to adopt straightforward reforms that could have prevented the rampant fraud that recently swept Monster.com, security experts say. Two of the recommended safeguards: more rigorous background checks to certify that employers are legitimate and identity authentication methods that make it harder for hackers to access the database.
"They should read the job descriptions and ask themselves if they sound like legal jobs -- that's the least they could do," said Elisa Felix, a San Diego communications worker who responded to a 2005 ad by "Heinkel Intersales" and wound up in a scam funneling stolen money abroad. "I had a trust in CareerBuilder that they would only post a legitimate job."
More
here.
Bizzaro: Internet Thief Claims Venus Williams Wants To Eat His Head
Paul McDougall writes on InformationWeek:
Proving that anyone really can file a lawsuit, serial plaintiff and convicted online ID thief Jonathan Lee Riches has launched a claim against the U.S. Open and tennis stars Serena and Venus Williams.
In handwritten papers filed last week in U.S. District Court in Virginia, Riches claims that the tennis balls used at the recent U.S. Open in New York were comprised of "electrons and neutrons stolen from my head" and that Venus and Serena Williams "told me they want to eat my head for supper." Riches also says he taught Venus to play table tennis in county jail.
Riches currently resides in federal prison in Salters, South Carolina, where he is serving time for his role in an Internet identity theft scam that lured its victims to a phony AOL site. He has become so infamous for whiling away his days in the slammer by filing outrageous lawsuits that there is now a Wikipedia page devoted to his efforts.
More
here.
Quote of the Day: The Onion

"President Bush's Homeland Security adviser Frances Townsend referred to the figurehead of Al-Qaeda as 'virtually impotent.' What do you think?"
"Ouch. That's gotta hurt much more than actually being captured."
- The Onion. Touché.
Web Servers Used by the Military and the Government Highly Vulnerable
Via heise Security News.
While all the world holds the Chinese responsible for a number of cyber attacks, governments and military officials are themselves partly to blame because they fail to keep their servers protected properly. Instead of forcing expert attackers to resort to highly specialized tools, too many systems practically welcome them in. For instance, the US media have reported new cases of unsafe configuration and inadequate administration of a number of online servers used by the military in an unspecified country in Europe.
Supposedly protected data are reputedly accessible via an SQL injection vulnerability. To make matters worse, the operator apparently did not even close the hole when notified, which is all the more surprising since knowledge about such vulnerabilities and how to protect against them has long been commonplace.
More
here.
Six Years On: What Hath September 11th Wrought?

Never Forget.
But also never forget this:"After six years, America's post-9/11 discourse has not changed much. Politicians and journalists still present most homeland security debates as tradeoffs between security and liberty. But the Bush Administration's most severe security measures since 9/11 are actually premised on radically different tradeoff: pursuing security by sacrificing the rule of law itself."
Let us heal, as a Nation, as United States -- as a United People.
But never let your individual liberties be eroded in the process of defending ourselves from terrorism. Never.
The United States Constitution is a living document, and should not be so easily disenfranchised -- as the current administration is attempting to accomplish in it's efforts to establish an "Unitary Executive" power structure.Take back our government -- an ideal that is worth your efforts. Let us realize a "...government of the people, by the people, for the people..." and let us hope it shall not perish from this earth.
"A house divided against itself cannot stand."
More
here.
See also:
Reuters ALERTNET Factbox: Attacks of Sept. 11, 2001.
Image source: Stan Honda / AP
Quote of the Day: Shaun Waterman
"Auditors found that, in 45 percent of those cases, the records of the complainant needed to be corrected because they had inaccurate information in them, or deleted altogether."
- Shaun Waterman, writing in an UPI analysis that "... a third of U.S. watch list wrong."
CSOs Still Clinging to Firewalls
Via CSO Online.
Although attracting support worldwide, American businesses aren’t necessarily buying into the Jericho Forum’s urging to rely less on hardened perimeter security -- firewalls and intrusion detection -- in favor of tougher internal security.
The forum, which is made up of CSOs from some of the largest international corporations, says it sees growing adoption of its once-radical idea that businesses should reduce dependence on firewalls as a way to defend against Internet threats. Nearly half -- 45% -- of those polled by the forum say they are implementing network security that complies with forum recommendations.
Forty-eighty percent say they agree strongly that such a security realignment actually improves their companies’ ability to do business, according to a survey of forum members. About half the members responded to the survey, 64% European and 29% American.
More
here.
Ex-FBI Hacker Informant Arrested for Alleged Wire Fraud
Henry K. Lee writes in The San Francisco Chronicle:
A computer expert who served as a confidential source for an elite FBI computer crime squad has been arrested on wire-fraud charges, five years after being released from federal prison for hacking into government computers.
Max Ray Butler, 35, also known as Max Vision, was arrested Wednesday on a federal arrest warrant issued in Pennsylvania, authorities said. He was charged a day earlier with wire fraud, identity theft and access-device fraud.
The alleged crimes happened from October through December in Allegheny County, Pa. Further details of the case were unavailable, as the affidavit from a U.S. Secret Service agent that accompanied the criminal complaint remains under seal.
Butler is to appear Tuesday before U.S. Magistrate Patricia Trumbull in San Jose for a detention hearing.
Butler was released from federal prison in October 2002 after being sentenced to 18 months and ordered to pay more than $60,000 in restitution for computer hacking. He was indicted in 2000 on charges of hacking into computers used by UC Berkeley, national laboratories, federal departments, Air Force bases and a NASA flight center in 1998.
More
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Monday, Sept. 10, 2007, at least 3,772 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,081 died as a result of hostile action, according to the military's numbers.
The AP count is 13 higher than the Defense Department's tally, last updated Monday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Yahoo! Feeds Trojan-Laden Ads to MySpace and PhotoBucket Users
Dan Goodin writes on The Register:
A Yahoo-owned advertising network became the unwitting ally of cyber crooks after it spewed millions of Trojan-laced banner ads on MySpace, PhotoBucket and other websites.
The banner ads, which were brokered by Right Media, were served an estimated 12 million times over a three-week period starting in early August, according to ScanSafe, a managed security provider. Earlier this year, Yahoo paid $650m to acquire the 80 percent of the company it didn't already own.
The banners contained a Flash file that silently installed a Trojan back door on unpatched Windows machines that visited the popular web destinations. Using an unpatched version of Internet Explorer while visiting MySpace or PhotoBucket was all that was necessary to become infected. The ads also ran on TheSun.co.uk, Bebo.com and UltimateGuitar.com.
Security Fix reported the story earlier.
More
here.
Terrorist Screening Center Fails to Redress Errors
Wilson P. Dizard III writes on Washington Technology:
The interagency Terrorist Screening Center, which maintains the nation’s electronic records about various types of dangerous individuals, has failed to redress the technology flaws that have choked its systems with inaccurate, outdated and duplicate information as well as creating hazardous watch list gaps, Justice Department auditors said.
The scathing report from Justice’s Inspector General cited the somewhat gloomier findings in its June 2005 analysis of the technology, business processes and overall effectiveness of the watch list center.
The TSC works alongside the FBI and intelligence community’s National Counterterrorism Center, both of which nominate people for inclusion in the terrorist watch list, which resides on the Terrorist Screening Database.
More
here.
Rogue FBI Letters Hint at Phone Companies Own Data Mining Programs
Ryan Singel writes on Threat Level:
An FBI office under criminal investigation for sending emergency phone record requests to phone companies that included knowingly false statement also included requests for the phone companies to identify the "community of interest" for the targeted phone numbers, according to documents acquired through a government sunshine lawsuit.
Those mysterious requests, first revealed by Eric Lichtblau in the New York Times on Sunday, suggest that the phone companies may be doing their own data mining and profiling on behalf of the United States government.
More
here.
DoJ Clarifies FISA Warrants Required for Spying in U.S.
David Kravets writes on Threat Level:
A top Justice Department official clarified Monday that the new national security electronic eavesdropping rules under the Foreign Intelligence Surveillance Act demand warrants when the "target" of spying is inside the United States.
The announcement by Kenneth L. Wainstein, assistant attorney general for national security, came three weeks after another Justice Department official muddied up the definition of the so-called Protect America Act enacted last month -- suggesting warrants were not required to peer into the electronic communications of foreigners on U.S. soil.
More
here.
Wrongly Accused Lawyer Back in Court Over USA Patriot Act
An AP newswire article, via The International Herald Tribune, reports that:
The lawyer whom the FBI wrongly accused in the 2004 Madrid terrorist bombings was back in court Monday to argue the merits of the USA Patriot Act's provisions for surveillance of U.S. citizens.
The case is the latest legal challenge to the 2001 Patriot Act, which greatly expanded the authority of law enforcement to investigate alleged acts of terrorism, both domestically and abroad.
Last week in New York, a U.S. District judge struck down a part of the law that allowed the FBI to demand records without the level of court supervision required for other government searches. His ruling, which is likely to be appealed, said Congress had overstepped its boundaries in approving the Patriot Act, at the expense of individual liberties.
Brandon Mayfield's case builds on that decision.
Mayfield was arrested May 6, 2004, after a fingerprint found on a bag of detonators in Madrid was incorrectly matched to him.
More
here.
U.S. Senator Wants to Expand Spying Authority
An AP newswire article by Pamela Hess, via Forbes.com, reports that:
Congressional Democrats are looking for ways to curtail some of the electronic surveillence authority Congress hastily approved last month just as a key Republican senator is trying to expand those powers.
Sen. Kit Bond, R-Mo., said Monday he wants Congress to grant immunity to telecommunications companies that cooperated with the government's warrantless wiretapping program prior to January 2007.
"I strongly believe that retroactive immunity is critical to adopt in order to ensure the government can get assistance from (telecommunications) carriers," Bond, the top Republican on the Senate intelligence committee, told an audience of attorneys, intelligence officials and civil liberties groups.
Well, at least now we know where Mr. Bonds stands on this issue.
- fergMore
here.
U.S. Says Wiretapping Helped Foil Terror Plot in Germany - UPDATE
A Reuters newswire article by Randall Mikkelsen, via The Boston Globe, reports that:
Information gained through a U.S. wiretapping program much criticized by civil liberties advocates helped authorities foil attack plots last week in Germany and Denmark, top U.S. intelligence officials said on Monday.
U.S. Director of Intelligence Michael McConnell said the surveillance program had made "significant contributions" in discovering and breaking up a suspected plot in Germany to bomb American installations. He cited them as a reason that the U.S. Congress should reject attempts to restrict it.
"It allowed us to see and understand all the connections ... to al Qaeda," McConnell told a hearing of the Senate Homeland Security Committee.
The program also contributed to the arrests in Denmark of eight Muslims, with suspected links to al Qaeda, on suspicion of planning a bomb attack, National Counterterrorism Center Director John Redd told reporters later.
More
here.
UPDATE: 13:55 PDT, 11 September 2007: "...another government official said Mr. McConnell might have misspoken."
New Zealand: Foreign Spies Hacking into Government Computers
Hank Schouten writes in The (New Zealand) Dominion Post:
Government computer systems have been hacked into by foreign governments, the country's chief spymaster says.
Government departments' websites have been attacked, information has been stolen and hard-to-detect software has been installed that could be used to take control of computer systems, Security Intelligence Service director Warren Tucker said.
In his first interview since taking up the post in November, Mr Tucker said there was evidence that foreign governments were responsible for the attacks.
He would not discuss what country was responsible but referred to comments by Canada's security service about Chinese spying activities.
Russia and China have been implicated in attacks on the British parliament's computer system.
More
here.
Terrorist Web Site Taken Down
Via WHIR News.
A Web site hosted out of a server in Minnesota was taken down last week after authorities discovered it showed users how to attack US military bases.
According to reports, the Web site Ekhlass.cc was operating for months on a server in Rochester, Minnesota and was registered to an address in Van Nuys, California. A whois search Monday provided no registration information for the domain.
Yigal Carmon, president of the Middle East Media Research Institute, a group that monitors terrorist Web sites, says that the site communicated messages from one of the most active groups on the Internet trying to recruit terrorists in the US. The Web site reportedly showed diagrams and prompted discussions on how to attack US military bases on US soil and offered tips on where to put explosives and where to target on certain buildings.
More
here.
EU: Web Searches for Bomb Recipes Should be Blocked
Ingrid Melander writes for Reuters:
Internet searches for bomb-making instructions should be blocked across the European Union, the bloc's top security official said on Monday.
Internet providers should also prevent access to any site giving instructions on how to make a bomb, EU Justice and Security Commissioner Franco Frattini said in an interview.
"I do intend to carry out a clear exploring exercise with the private sector ... on how it is possible to use technology to prevent people from using or searching dangerous words like bomb, kill, genocide or terrorism," Frattini told Reuters.
The EU executive is to make this proposal to member states early in November as part of a raft of anti-terrorism proposals.
More
here.
10,000 .eu Names Suspended Amid Cybersquatter Allegation
Via OUT-LAW.com.
The organisation behind the .eu domain has suspended 10,000 domain names registered by a Chinese woman whom it accuses of being a cybersquatter. The woman has filed a lawsuit in Belgium in retaliation.
EURid, the Belgium-based registry for .eu domain names, has blocked the names and has the right to strip the woman, Zheng Qingyin, of the names. EURid legal manager Herman Sobrie told OUT-LAW, though, that the organisation wanted to have a court strip Qingyin of the addresses. He said that case would take around a year.
Qingyin has filed a separate suit objecting to the blocking of the domains in the Court of First Instance in Brussels. This is a fast-track case whose result should be known in a month, Sobrie said.
More
here.
Security Researcher Intercepts Embassy Passwords From Tor
Jeremy Kirk writes on InfoWorld:
A security researcher who collected thousands of sensitive e-mails and passwords from the embassies of countries such as Russia and India blamed systems administrators on Monday for not using encryption to shield their traffic from snooping.
Dan Egerstad, a 21-year-old security researcher, revealed on Monday he was able to capture the information by setting up his own node in a peer-to-peer network used by the embassies to make their Internet traffic anonymous.
The embassies relied on a volunteer network of servers using software called Tor (The Onion Router) to hide their Internet traffic and make it anonymous. Traffic sent through a Tor node is transmitted through a randomly selected series of other Tor nodes before exiting the network for its intended destination, so as to disguise the source and destination of the traffic.
But although traffic between nodes in a Tor network is encrypted by default, traffic entering and exiting the system is not, so anyone wanting to hide not only who are they are communicating with, but what they are saying, must apply an extra layer of encryption themselves. Embassies and companies neglected to do this, which left their information open for Egerstad to collect.
More
here.
ISPs Turn Blind Eye to Million-Machine Malware Monster
Dan Goodin writes on The Register:
Several weeks ago, security researcher Lawrence Baldwin dispatched an urgent email to abuse handlers at OptimumOnline, the broadband provider owned by Cablevision, warning that one of its customers stood to lose more than $60,000 to cyber crooks.
"He's got a keylogger on his system . . . below is a log of the miscreant viewing the info that was logged from his system while accessing his [Bank of America] accounts," Baldwin's email read. "Looks like he's got nearly $60K in there, so a lot at stake. Can you get someone to phone me that might be able to establish contact with this customer?"
The email, which was addressed to a specific handler's email address and was also copied to OptimumOnline's abuse desk, went on to provide the user's IP address and enough specifics to suggest Baldwin's claim of a keylogger was probably accurate. Yet, more than three weeks later, Baldwin still hasn't heard back from the company.
More
here.
Indian Gvernment Forcing Cybercafés to Install Keyloggers
Jacqui Cheng writes on ARS Technica:
The roughly 500 cybercafés in Mumbai, India, will soon have police-sanctioned keylogging software installed on their machines in the name of fighting terrorism. The software will track everything entered into web forms, chat rooms, e-mail, and more, and report it back to the government. Mumbai police say that cybercafé owners must agree to the installation of the software or else they will lose their licenses.
The president of India's Foundation for Information Security and Technology, Vijay Mukhi, told India-based newspaper Mid Day late last month that the decision was based on the fact that terrorists look to hide their Internet activities by using cybercafés instead of their home computers.
More
here.
Toon of the Day: The Gonzales Legacy
Click for larger image.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Sunday, Sept. 9, 2007, at least 3,762 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,071 died as a result of hostile action, according to the military's numbers.
The AP count is 14 higher than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Cyber Attacks Outstripping Defenses
Edwin Yapp writes on ZDNet Asia:
Speaking to the media in Kuala Lumpur at this week's Hack in the Box Security Conference, Lance Spitzner, president of the Honeynet Project, said malicious software writers have been producing sophisticated codes, motivated mainly by the prospect of making millions of dollars from their exploits.
"The techniques used by criminal hackers are changing so rapidly now that it's difficult to keep up with them," Spitzner said. "In the end, it's all about returns on investment [for the hackers] because, by changing their attacks, there is so much more money to make."
An organisation dedicated to improving the security of the internet, the Honeynet Project employs a network of "honeypots", internet-attached servers that behave as decoys to lure potential hackers in order to study their techniques and monitor malicious activities.
More
here.
Scary Sign of the Day: UK DNA Property Marking

(Hat-tip: Judi.)
French Reveal That They, Too, Victims of China Hackers
Via Australian IT.
French information systems fell prey to cyber attacks "involving China", similar to those reported by the US, British and German governments, a top French security official said.
"We have indications that our information systems were the object of attacks, like in the other countries," the Secretary-General of National Defence (SGDN) Francis Delon said, confirming a report published in French newspaper Le Monde.
"We have proof that there is involvement with China. But I am prudent. When I say China, this does not mean the Chinese government. We don't have any indication now that it was done by the Chinese People's Liberation Army," he added.
Asked which computer systems had been hacked, Delon said they "concerned the services of the (French) state."
A source close to the issue said the French defence ministry's public Internet site was targeted, but that it contained no confidential information. The attack was made by cyber saboteurs to "test information technology defences."
More
here.