Quote of the Day: The Declaration of Independence

"Prudence, indeed, will dictate that Governments long established should not be changed for light and transient causes; and accordingly all experience hath shewn that mankind are more disposed to suffer, while evils are sufferable than to right themselves by abolishing the forms to which they are accustomed. But when a long train of abuses and usurpations, pursuing invariably the same Object evinces a design to reduce them under absolute Despotism, it is their right, it is their duty, to throw off such Government, and to provide new Guards for their future security"
- The U.S. Declaration of Independence.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Saturday, April 14, 2007, at least 3,297 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,674 died as a result of hostile action, according to the military's numbers.
The AP count is five higher than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
In Passing: Don Ho
August 13, 1930 - April 14, 2007
Off Topic: Garry Kasparov Held in Moscow Protest March

Andrew E. Kramer and Michael Schwirtz write in The New York Times:
Garry Kasparov, the former chess champion turned opposition politician in Russia, was arrested with nearly 200 other protesters during a rally in Moscow on Saturday that ended in clashes with riot troops.
The rally, the third so-called Dissenters’ March held by a loose antigovernment coalition known as Other Russia, was noteworthy because authorities aggressively pursued the organizers, including President Vladimir V. Putin’s former prime minister, Mikhail M. Kasyanov, whom the police jostled but did not arrest.
The rally was principally supported by Mr. Kasyanov and Mr. Kasparov, who leads a group here called the United Civil Front.
Essentially barred from access to television, members of Other Russia have embraced street protests as the only platform to voice their opposition ahead of parliamentary elections in December and presidential elections next March. Early this month, Mr. Kasyanov’s and Mr. Kasparov’s Web sites were blocked, though it was unclear by whom.
More
here.
Who’s Watching the FBI?
Jeffrey Rosen writes in The New York Times:
In the latest and most serious post-9/11 civil-liberties abuse to emerge from Washington, the Bush administration’s “Trust me anyhow” defense has finally collapsed. The scandal involves “national-security letters,” which the F.B.I. has secretly used to scrutinize the financial data, travel records and telephone logs of thousands of U.S. citizens and residents.
In March, a report by the inspector general of the Justice Department described “widespread and serious misuse” of national-security letters after the U.S.A. Patriot Act of 2001 significantly expanded the F.B.I.’s authority to issue them: between 2003 and 2005, he concluded, the F.B.I. issued more than 140,000 national-security letters, many involving people with no obvious connections to terrorism.
The Bush administration was fortunate that, shortly after the F.B.I. scandal broke, the tempest over the Justice Department’s firing of prosecutors bumped it off the front page.
More
here.
Stalkers Go High Tech to Intimidate Victims
Chris L. Jenkins writes in The Washington Post:
Law enforcement officials and safety groups have focused on the Internet as an arena for such types of harassment as false impersonation and character assassination as more people voluntarily place their private lives on public display through Web sites such as Facebook.com and MySpace.com.
But a little-discussed and more threatening phenomenon is also happening to the unwitting online and in the high-tech world: cyber-stalking, the illegal monitoring of private information and communication of ex-lovers and spouses as a form of domestic violence. The spurned often use global positioning systems, invasive computer programs, cellphone monitoring chips and tiny cameras to follow the whereabouts, goings-on and personal communications of unsuspecting victims.
More
here.
Image of the Day: In El Dorado
 Image source: NASA/ESA/Hubble Heritage Team (STScI/AURA)
Image source: NASA/ESA/Hubble Heritage Team (STScI/AURA).
Bright spiral arms, dark lanes of dust, and hotbeds of star formation highlight this recent Hubble Space Telescope view of NGC 1672, a spiral galaxy in the southern constellation Dorado. The galaxy's nucleus, which contains a supermassive black hole, forms a stretched-out "bar" of stars.
The bright red blobs are stellar nurseries, where hundreds of new stars are being born. Several more-distant galaxies appear around or behind NGC 1672. The bright diamond-like objects are foreground stars in our galaxy.
Link.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Friday, April 13, 2007, at least 3,297 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,674 died as a result of hostile action, according to the military's numbers.
The AP count is five higher than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Space Tech: China Launches Navigational Satellite
Via Reuters AlertNet.
China launched a navigation satellite on Saturday to be used for everything from tracking forest fires to public security, Xinhua news agency said.
With more to be launched in coming years, the system would cover China and neighbouring countries by 2008, before being expanded into a global network, it said.
The "Compass" navigational system is designed to provide positioning services in transportation, meteorology, petroleum prospecting, forest fire monitoring, disaster forecasts, telecommunications and public security.
More
here.
Support Intelligence: BusinessWeek Wants Me to Become a Better Lover?!?
The guys over at Support Intelligence keep on exposing big companies with spam problems:
We've been collecting spam from a corporate email gateway (205.142.53.51) over at Business Week which is owned by McGrawHill which is responsible for announcing the 205.142.50.0/22 block from AS 4546.
This particular computer is one of Business Week's outbound mail gateways better known as mail03-1.mcgraw-hill.com. Its been showering our traps with titles like "Become a better lover" and "Enjoy complete and total confidence every time".
This server isn't botted it's just an IronPort [aren't they owned by cisco now?] box that's forwarding SPAM, but where is the spam coming from?
More
here.
'List of Places Blurred Out on Google Maps' Being Considered for Deletion
It is rumored that some secretive agencies are behind the request to remove this entry on Wikipedia.
Check it out before it disappears. - ferg
(Thanks, Juha-Matti.)
Google Buys DoubleClick for $3.1 Billion
Louise Story and Miguel Helft write in The New York Times:
Google reached an agreement today to acquire DoubleClick, the online advertising company, from two private equity firms for $3.1 billion in cash, the companies announced, an amount that was almost double the $1.65 billion in stock that Google paid for YouTube late last year.
The sale offers Google access to DoubleClick’s advertisement software and, more importantly, its relationships with Web publishers, advertisers and advertising agencies.
More
here.
Bush Asks Congress to Alter 1978 Eavesdropping Law
A Reuters newswire article, vis The Boston Globe, reports that:
The Bush administration asked Congress on Friday to expand the number of people it can subject to electronic surveillance in the United States.
The request was contained in a proposed bill authored by intelligence and Justice Department officials that also protects companies that cooperate with spy operations.
Legislation submitted a week ahead of a Senate hearing on government surveillance practices calls for the 1978 law that governs eavesdropping operations to be updated to combat the threat from Islamist militants who use computer and wireless technology that did not exist in the 1970s.
More
here.
Local: Credit Card Scam Costs East Bay Grocery Customers
Via CBS5.com.
Alameda County investigators say high-tech thieves may have scammed at least $100,000 from the bank accounts of shoppers at an East Bay grocery chain.
According to authorities, thieves put a credit card skimmer in one of the checkout lines at an Albertsons on Hesparian Boulevard in San Lorenzo. This device enabled the crooks to collect account information including PIN numbers from countless shoppers. The suspects are believed to have started withdrawing money from accounts this week.
Since Monday, Alameda County Sheriff's detectives received 70 reports of bank fraud, twice the usual number of complaints.
More
here.
Quote of the Day: Hance Haney
"The Internet can be used to collect, store and cross-reference potentially limitless information about each one of us — our day-to-day activities, our associations, our spending habits, even our thoughts. If for example the government wanted to control Medicare and Medicaid costs by identifying who smokes, who drinks, and who doesn’t follow the government’s dietary, exercise or safe-sex guidelines, it will increasingly become possible for the government to do that."
"Is the only criteria going to be whether the government could save money from imposing surveillance mandates on the private sector (which would operate indiscriminately against the innocent and the guilty alike) versus spending more for law enforcement (which must respect basic civil liberties) or other government programs?"
- Hance Haney, in a very thought-provoking article on The Technology Liberation Front.
Off Topic: 'Reverse Progress in Iraq,' Vetoes, and War Czars
One of the most hilarious and witty segments I've seen on
The Daily Show with Jon Stewart in a while.
Via Crooks and Liars.
Stewart and Oliver take a look back at the so-called "progress" of the Iraq War and the new position of war czar that Bush is having trouble filling.
Highly recommended viewing.
Watch it
here.
TJX Thieves Had Time to Steal, Trip Up
An AP newswire article by Mark Jewell, via PhysOrg.com, reports that:
For at least 17 months, someone had free rein inside TJX Cos.' computers. Without anyone noticing, one or more intruders installed code on the discount retailer's systems to methodically unearth, collect and transmit account data from at least 45.7 million credit and debit cards.
It's believed to be the biggest such breach of customer records ever in the United States - a theft that owes its size in part to the time the electronic heist went undetected, information security experts say.
The 17-month duration appears to be unprecedented among recent large U.S. data thefts involving hackers, according to an Associated Press review of a dozen of the biggest cases over the past four years.
Experts say the nearly year-and-a-half of undetected access could be a mixed blessing as investigators look for any incriminating evidence left behind.
More
here.
Ballistic Missile Forces Passenger Jet to Return Home

An AP newswire article, via MSNBC, reports that:
An Indonesian jet carrying hundreds of passengers was forced to turn around over Indian airspace after a nuclear-capable ballistic missile streaked across the sky, the Foreign Ministry said Friday.
Indonesia has demanded an explanation from New Delhi, which insisted that aviation authorities were informed about Thursday’s test launch well in advance.
The Garuda Indonesia Boeing 747 was en route from Jakarta to Saudi Arabia when the Indian control tower told pilots the missile had been launched, said Ari Sapari, the national carrier’s director.
More
here.
Social Security Administration Worker Charged In Identity Theft Scheme
Sharon Gaudin writes on InformationWeek:
A former Social Security Administration employee surrendered to federal authorities Wednesday to face charges of illegally disclosing personal information she took off a government computer that was then used in an identity theft scheme that racked up $2.5 million in credit card charges.
Jennifer Batiste, 45, of Leimert Park, Calif., made her initial court appearance Wednesday afternoon in U.S. District Court in Los Angeles. She was released on $5,000 bond.
Batiste is charged with conspiracy, accessing a protected computer to conduct fraud, and disclosure of a Social Security number. If she is convicted of the three counts in the indictment, Batiste faces a maximum sentence of 15 years in federal prison.
More
here.
Off Beat: Dolphin Defenders To Patrol Naval Base
 Dr. Evil
Dr. EvilNot exactly "
...Sharks with frickin' laser beams on their heads...," but interesting nonetheless.
Via NBC11.com.
You've heard of the Navy SEALS, but on Thursday, the military showed the talents of their Navy sea lions and dolphins.
The animals are part of the San Diego-based marine mammal program, Naval Special Clearance Team One. The group is housed at Naval Base Point Loma.
For the first time since the start of the war in Iraq, officials at the base opened their doors to the media.
Military officials said the mammals are used to help dive underwater and retrieve targets.
More
here.
The Forensic Felons: The Next Generation of Cyber Thieves
A Ziff Davis Internet article by Evan Schuman, via eWeek, reports that:
For years, retailers have been told that if they merely abide by common sense security procedures—don't permit obvious passwords, check audit logs regularly and patch software immediately—they'd be in good security shape.
Although there is no doubt that is still sound counsel, security consultants are describing a new breed of professional cyber thieves out there, crooks who know as much about sophisticated forensic investigations as the good guys do.
More
here.
Pakistan: Deadly 'Phone Virus' Threat Causes Panic
A Reuters newswire article, via ComputerWorld, reports that:
Mobile service providers in Pakistan have been inundated by calls from subscribers worried by a prank message that they could die of a deadly virus being transmitted via their phones.
The rumor was so effective that some mosques in the country's biggest city, Karachi, made announcements that people were being killed by a mobile virus and they should be aware of God's wrath.
In a prank reminiscent of the plot in the hit Hollywood movie "The Ring" in which people die within a week after watching a video, the prankster warned users that a deadly virus transmitted through phones had killed 20 people.
More
here.
Australia: Secret Police Computer Files Infiltrated
Andrea Petrie writes on TheAge.com.au:
The girlfriend of a Melbourne crime figure has gained access to confidential police records in a serious security breach.
The woman, who was not a police officer, was working at the force's criminal records branch.
She was suspended from the force last month, resigned 14 days ago and has been interviewed by Purana taskforce detectives for inappropriately checking the law enforcement assistance program (LEAP) and VicRoads databases.
Force command confirmed yesterday that an employee from the corporate support area had resigned because of "one occasion in which she inappropriately accessed" the database.
But senior police sources have told The Age she has been accused of wiping the records of possibly hundreds of criminals and selling information from the confidential files. The Age believes that a taskforce has been set up to check the records examined by the woman while she worked at the unit.
More
here.
Calls Mount for Wal-Mart to Disclose Surveillance Records
An AP newswire article by Marcus Kabel, via The Mercury News, reports that:
More demands for details of Wal-Mart security activities - including records of alleged corporate surveillance - were voiced Thusday.
Another shareholder group and the lawyers in a massive class-action sex-discrimination lawsuit in federal court in California called for the Bentonville, Ark.-based retailer to shed light on its intelligence gathering.
Brad Seligman, lead attorney in the Dukes v. Wal-Mart gender discrimination case pending in San Francisco, wrote Wal-Mart's lawyers that he was concerned about recent news stories claiming Wal-Mart's security apparatus conducted widespread surveillance operations.
More
here.
Homeland Security Tech: Port of Tampa Employees Victimized by ID Thief
Steve Huettel writes in The St. Petersburg Times:
A contractor's employee took personal information on thousands of people with Port of Tampa access badges and applied for credit cards in the names of about 20 of them, law enforcement officials said Thursday.
Daniel E. Glenn, 29, was arrested near his Lakeland home Thursday and charged with an offense against intellectual property to defraud/obtain property.
A computer technician for Siemens Building Technologies, Glenn was working on a computer upgrade at the Tampa Port Authority on Feb. 28.
He told port authority employees he needed access to the security badge database to fix corrupted data, according to an arrest report. The agency has issued 39,000 badges for longshoremen, truckers and workers at port businesses to enter secure areas along the waterfront.
More
here.
(
Props, Pogo Was Right.)
Australia: Telstra's Spam Solution: Block Gmail Messages
Via techdirt.com.
You might remember that some time ago, Verizon tried a novel way to cut down on the amount of spam its customers received -- by blocking most foreign email. Though it eventually dropped the policy (after a lawsuit), the company's anti-spam practices still leave a lot to be desired. Meanwhile, over in Australia, incumbent telco Telstra was blocking messages sent from Gmail, claiming Google doesn't do enough to stop spam being sent from the service.
Rather than being a fair indictment of Gmail, this simply sounds like an admission that Telstra's simply not up to the task of adequately dealing with spam -- after all, it's hard to see how simply blacklisting messages from such a large email provider could really be seen as an adequate solution. If anything, it will just drive users away from Telstra's service and to Gmail.
More
here.
Friday the 13th and The Knights Templar

Via Wikipedia.
At dawn on Friday, October 13, 1307, scores of French Templars were simultaneously arrested by agents of King Philip, later to be tortured in locations such as the tower at Chinon, into admitting heresy in the Order.
Over 100 charges were issued against them, the majority of them identical charges to what had been earlier issued against the inconvenient Pope Boniface VIII: accusations of denying Christ, spitting and urinating on the cross, and devil worship. The main interrogation of the Templars was under the control of the Inquisitors, a group of experienced interrogators and clergy who circulated around Europe at the beck and call of any European noble.
The rules of interrogation said that no blood could be drawn, but this did nothing to stop the torture. One account told of a Templar who had fire applied to the soles of his feet, such that the bones fell out of the skin. Other Templars were suspended upside-down or placed in thumbscrews.
Of the 138 Templars (many of them old men) questioned in Paris over the next few years, 105 of them "confessed" to denying Christ during the secret Templar initiations. 103 confessed to an "obscene kiss" being part of the ceremonies, and 123 said they spat on the cross. Throughout the trial, however, there was never any physical evidence of wrongdoing, and no independent witnesses - the only "proof" was obtained through confessions induced by torture.
More
here.
Local: Glitch Causes Bay Area Cingular Service Outage
Via CBS5.com.
A "software glitch" caused Cingular Wireless customers to lose cell phone service for four hours Thursday though a spokeswoman said not all customers were prevented from receiving calls.
Lauren Garner of Cingular Wireless said the first reports of service problems came at 4:30 p.m. Thursday and that the system was fully restored by 8:30 p.m.
"It was a software glitch, but it's over and we're back completely," said Garner.
More
here.
Microsoft Investigating Vulnerability in Windows DNS Server
Via Microsoft Technet.
Microsoft is investigating new public reports of a limited attack exploiting a vulnerability in the Domain Name System (DNS) Server Service in Microsoft Windows 2000 Server Service Pack 4, Windows Server 2003 Service Pack 1, and Windows Server 2003 Service Pack 2. Microsoft Windows 2000 Professional Service Pack 4, Windows XP Service Pack 2, and Windows Vista are not affected as these versions do not contain the vulnerable code.
Microsoft’s initial investigation reveals that the attempts to exploit this vulnerability could allow an attacker to run code in the security context of the Domain Name System Server Service, which by default runs as Local SYSTEM.
More
here.
And
here on the
SANS Internet Storm Center.
Secunia rates this vulnerability
HIGHLY CRITICAL.
Gapingvoid: Order & Chaos
Via gapingvoid.com. Enjoy!

Identity Thieves Tap Into Lucrative Tax Fraud
Lisa Myers, Amna Nawaz, and the NBC News Investigative Unit:
Evangelos Soukas is perhaps not the most likely of consultants for the IRS, but he may be among the most qualified. Currently serving out a seven-and-a-half year sentence in a California prison for various identity theft scams — including more than a dozen counts of false claims to the IRS — Soukas was brought Thursday before the Senate Finance Committee to testify about his fraud experience, and the simplicity with which he made off with more than $43,000 in taxpayers' money.
"This was an easy way to get money," he said. "And if I wanted to, I could hijack other people's identities and never get caught."
Soukas' scam involved using stolen, personal information to file fake online tax returns with the IRS. With the help of refund anticipation loans — which allow a taxpayer access to an anticipated refund within just a matter of days — Soukas was able to collect on the funds before the fraud could be detected.
More
here.
Note: Mr. Soukas was allowed to testify
after an attempt by the Department of Justice to mysteriously block his testimony.
China Announces New Anti-Porn Internet Campaign
Via Reuters.
China has launched its latest campaign against pornography on the Internet that will also take aim at fraud, illegal lotteries and "rumor-spreading", the official Xinhua news agency said.
"The boom of pornographic content on the Internet has contaminated cyberspace and perverted China's young minds," it quoted Zhang Xinfeng, vice-minister of public security, as saying in a late night report.
"The inflow of pornographic materials from abroad and lax domestic control are to blame for the existing problems in China's cyberspace," Zhang said.
More
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Thursday, April 12, 2007, at least 3,292 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,674 died as a result of hostile action, according to the military's numbers.
The AP count is two higher than the Defense Department's tally, last updated Thursday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Stolen Bank of America Laptop Held Employee Data
Rick Rothacker writes in The Charlotte Observer:
A stolen Bank of America Corp. laptop has resulted in lost personal information of current, former and retired employees, according to a letter sent this week to those affected.
The letter said a "limited" number of people were affected, but the Charlotte bank on Thursday would not provide a number. Employees at various levels of the company were affected, spokesman Scott Silvestri said.
The lost data included names, addresses, dates of birth and Social Security numbers, but there is no sign the information has been misused, according to an April 10 letter obtained by the Observer. The bank is offering a free credit monitoring service for two years to those affected.
The bank employs more than 203,000 worldwide, including about 15,000 in the Charlotte area. A former employee who received the letter Thursday said he appreciated the warning.
More
here.
(
Props, Pogo Was Right.)
European Fears Surface Over Possibility of U.S. Secret Services Access to European Domestic Banking Data
Via heise Online News.
The German Federal Data Protection Commissioner Peter Schaar has critically remarked that the creation of a Single Euro Payments Area (SEPA) will mean that in future the SWIFT (Society for Worldwide Interbank Financial Telecommunications) financial network will also handle all domestic transfers.
This would make it possible for secret services, including those of the United States, ostensibly out to combat the funding of terrorist organizations, to gain access to such transfer data.
"If these data, as is planned, are handled by SWIFT, it would mean that, unless the system is changed, these data too will be available to the Americans for their investigations," Mr. Schaar, talking to the regional German public broadcaster SWR, said by way of summing up his misgivings about the developments. According to the data privacy advocate such a practice would "scarcely be compatible with our notions of sovereignty."
More
here.
(
Props, Pogo Was Right.)
Federal Circuit Rejects Trademark Protection for Lawyers.com Website
Robert Loblaw writes on the Decision of the Day Blog:
Here’s an interesting intellectual property decision involving a legal website. The lawyers out there are undoubtedly familiar with Martindale-Hubbell, which operates a massive database with contact information and brief biographies of lawyers across the country.
Its parent company, Reed Elselvier, has expanded the database service in recent years and now provides various online tools for the public at the website http://www.lawyers.com/.
The company then tried to register “lawyers.com” as a trademark, but the Patent and Trademark Office rejected it as generic. The company fares no better with the Federal Circuit, which wastes little time in affirming the PTO’s decision.
More
here.
Off Beat: 'Geek Squad' Tech Accused of Taping Woman in Shower
An AP newswire article, via USA Today, reports that:
A 22-year-old woman and her mother are suing Best Buy and its "Geek Squad" computer repair team for dispatching a technician who they say videotaped the daughter taking a shower.
Sarah Vasquez and her mother Natalie Fornaciari filed a Superior Court lawsuit Wednesday claiming technician Hao Kuo Chi, 26, placed his cellular telephone in Vasquez's bathroom during a service call March 4 in the family's Walnut home and recorded her showering.
The suit also claims the phone was found in the bedroom of Vasquez's 13-year-old sister, Kelly Rocha.
More
here.
Vonage in Crisis
Cassimir Medford writes on Red Herring:
Internet telephony market leader Vonage on Thursday said chief executive Michael Snyder stepped down and announced it would slash costs in a bid to turn around its struggling business.
The Holmdel, New Jersey based company, which recently lost a critical patent dispute with Verizon Communications, said company founder and chairman Jeffery Citron would take over as interim CEO.
Vonage said it was cut its crucial marketing expenses by about 25 percent, and administrative expenses by $30 million. The moves come less than a week after a federal judge banned Vonage from signing up new customers, a major blow to a company that operates on very thin margins, an analyst said.
“This is a really bad time for Vonage because it now has to survive on less money,” said Yankee Group analyst Zeus Kerravala. “Can they survive running lean and mean? The jury is out on that.”
More
here.
Feds Grade Agencies on Security - 1/3 Get Failing Marks
Jaikumar Vijayan writes on ComputerWorld:
The federal government today got an overall grade of C-minus in an annual computer security report card that evaluates the performance of 24 individual agencies covered by the Federal Information Security Management Act (FISMA).
Eight agencies -- including the departments of Defense, Interior and State as well as the Nuclear Regulatory Commission -- received failing grades. An equal number of agencies, including the General Services Administration, the Social Security Administration and the Department of Housing and Urban Development (HUD), scored at least an A-minus.
More
here.
Microsoft Looking Into Hotmail Problems - UPDATE
Elinor Mills writes on the C|Net Microsoft Blog:
Microsoft engineers were looking into problems with Windows Live Hotmail on Thursday after users reported problems getting onto the Web site. The company was unsure of the cause or the scope of the problems, which began around 9 a.m. PDT. There was no impact on customer data, the company said.
"We are aware that a small percentage of our customers are experiencing problems signing in to some services," Adam Sohn, director of Microsoft's Online Services Group, said in a statement. "We're actively investigating the cause and are working to take the appropriate steps to remedy the situation as rapidly as possible. We sincerely apologize for any inconvenience and disruption this may be causing our customers."
More
here.
Note: For what its worth (and from personal observations), these problems also affect
MS Messenger accessibility with users that have
Hotmail accounts.
UPDATE: 12:38 PDT: It appears to have been fixed at this time.
UK: Wireless Internet Zone to Cover City of London
Via The Daily Mail.
The City of London will become Europe's biggest wireless internet hotspot next week.
The network will span the entire Square Mile, giving its estimated 350,000 workers internet access via their laptop or mobile phone.
It will use a new "mesh" technology to transfer users automatically from base station to base station as they walk by, allowing uninterrupted web use.
Some 130 base stations will be used to cover the area when the system is turned on next week.
Users will be charged about £11 a month.
More
here.
Prosecutors Reverse Course in China Spy Case
Josh Gerstein writes in The New York Sun:
After complaints from business lawyers and university administrators, prosecutors on a Chinese espionage case have reversed course, acknowledging that the defendant, Chi Mak, may attempt to defend himself by arguing that the military-related reports he sent to China were in the public domain.
Mr. Mak is on trial in Santa Ana, Calif., on charges of conspiracy to export defense-related data without a license, acting as an unregistered agent for the Chinese government, and lying to investigators.
The government contends that he sent the Chinese sensitive plans for quiet submarine drive technology, electrical systems, and a new generation of Navy warships.
More
here.
Vista DRM Could Hide Malware
Tom Espiner writes on ZDNet UK:
A security researcher has released a proof-of-concept program that hackers could use to exploit Windows Vista digital rights management processes to hide malware.
Alex Ionescu claims to have developed the program — D-Pin Purr v1.0 — that will arbitrarily enable and disable protected processes in Vista, Microsoft's latest operating system.
Screenshots on Ionescu's blog suggest the program can be run successfully. Ionescu included stack information related to one of the processes that is by default protected on Vista. Try to retrieve that information using Process Explorer and you get an error message. In Ionescu's screenshot, taken after allegedly removing the protection, the information is visible.
More
here.
'Damaging' Internal E-Mails Blast State Farm on Katrina Damage Claims
Joseph Rhee reports on ABC News' "The Blotter":
Internal company e-mails obtained by ABC News reveal that engineers complained of being pressured by State Farm Insurance to change damage reports of homes ravaged by Hurricane Katrina.
One official of the engineering firm, Forensic Analysis and Engineering Corp. (FAEC), wrote that he had "a serious concern about the ethics of the whole matter."
More
here.
Off Beat: Hundreds of UK Partygoers Trash House After MySpace Invite - UPDATE
Via The Guardian (UK).
Up to 200 teenagers from across the country trashed a family house while the parents were away after their daughter advertised a party on MySpace, police said today.
Revellers caused £20,000 of damage to the £230,000 property after the invitation for the Easter Monday celebration was posted on the popular site as a "Skins Unofficial Party" - a reference to the controversial Channel 4 series which featured scenes where a teenage get-together got out of hand.
Partygoers allegedly urinated on the mother's wedding dress and children's clothes; stole cash and jewellery; ripped light fittings from the ceiling by swinging on them; stubbed out cigarettes on the carpet; vomited throughout the house and barricaded the back door to prevent neighbours from intervening.
More
here.
UPDATE: 17:39 13 April 2007: Apparently, the girl responsible for this incident has "...emerged from hiding to blame internet hackers for the £20,000 chaos, and to apologise profusely to her parents." More
here.
Multiple Vulnerabilities in the Cisco Wireless Control System
Via Cisco Systems.
The Cisco Wireless Control System (WCS) works in conjunction with Cisco Aironet Lightweight Access Points, Cisco Wireless LAN Controllers, and the Cisco Wireless Location Appliance by providing tools for wireless LAN planning and design, system configuration, location tracking, security monitoring, and wireless LAN management.
Cisco WCS contains multiple vulnerabilities that can result in information disclosure, privilege escalation, and unauthorized access through fixed authentication credentials.
More
here.
U.S. Military to Put Internet Router in Space
John Blau writes on InfoWorld:
The U.S. military plan to test an Internet router in space, in a project that could also benefit civilian broadband satellite communications.
Cisco Systems and Intelsat General, a subsidiary of Intelsat, are among the companies selected by the U.S. Department of Defense for its Internet Routing In Space (IRIS) project, which aims to deliver military communications through a satellite-based router.
Potential nonmilitary benefits of the IRIS program include the ability to route IP (Internet Protocol) traffic between satellites in space in much the same way packets are moved on the ground, reducing delays, saving on capacity and offering greater networking flexibility, Lloyd Wood, space initiatives manager in the Global Defense, Space & Security division of Cisco, said Thursday.
More
here.
Europe: E-Mail Monitoring May Violate Laws
Tom Espiner writes on C|Net News:
Monitoring employees' Internet and telephone use at work may contravene human rights laws in Europe, according to a ruling in a landmark case in the European Court of Human Rights last week.
The case involved a public-sector employee who won $5,910 in damages and $11,820 in court costs and expenses after her communications were intercepted by her employer, Carmarthenshire College, based in South Wales. Lynette Copland successfully took the U.K. government to court after her personal Internet usage and telephone calls were monitored by one of her bosses in 1999.
More
here.
Analysts: TJX Breach Case May Cost Over $1B
Ross Kerber writes in The Boston Globe:
If the loss of millions of customer credit- and debit-card records from TJX Cos. plays out like previous data-breach cases, the final cost of the theft could add up to more than $1 billion, some technology analysts say.
The exact cost to TJX itself is unclear and may be lower. Insurance and tax credits may offset the Framingham retailer's expenses, which could be spread over several years. Banks that issue the credit cards may also have to pick up part of the costs.
Regardless, the liability would be among the highest associated with lost or stolen data, say analysts. They arrived at their estimates by comparing the cost of breaches at other companies in areas such as technology upgrades, contacting customers, reissuing cards, and lost customers.
More
here.
Winny P2P (And Stupidity) Responsible for More Sensitive Data Leaks in Japan
A Kyodo News article, via The Japan Times Online, reports that:
The layout of an arms depot and other internal information from the Ground Self-Defense Force's Matsudo garrison in Chiba Prefecture appeared on the Internet in late March via the Winny file-sharing software, sources said Monday.
The information came from the personal computer of a sergeant who used to be stationed at the base.
Although the data did not include confidential information, the ministry plans to punish the sergeant 1st class for failing to comply with its ban on storing professional data on privately owned PCs.
The ban was put in place in February 2006, after secret data leaked from the Maritime Self-Defense Force via Winny. All personnel under the Defense Ministry's jurisdiction, including Self-Defense Forces members, are subject to the ban. They have also been ordered to delete data already stored on their PCs.
More
here.
In Passing: Kurt Vonnegut

New York Times article
here.
Support Intelligence: Fortune 500 Botnet Problem
 Rick Wesson, left, is chief executive of the data-gathering company Support Intelligence; Adam Waters is chief operating officer. “We are losing this war badly,” Mr. Wesson said of the growing threat from botnets.
Rick Wesson, left, is chief executive of the data-gathering company Support Intelligence; Adam Waters is chief operating officer. “We are losing this war badly,” Mr. Wesson said of the growing threat from botnets.
Image source: Peter DaSilva for The New York Times
A couple of good friends and colleagues of mine, Rick Wesson and Adam Waters at
Support Intelligence up the street a few miles in San Francisco, have begun publicizing some highly visible botnet problems exposed via the spambot-generated e-mails that hosts within their networks have generated.
The lastest in their series of exposés on their blog features
AFLAC. In previous posts, they have featured botnet problems in
AIG,
Thomson, and
3M.
More detail can found
here.
Keep up the good work, Rick and Adam.
- ferg
Off Beat: Bill Gates Ponders Orbital Flight
Tariq Malik writes on Space.com:
American billionaire and Microsoft mogul Bill Gates is eyeing the possibility of his own orbital spaceflight, according to the next commander of the International Space Station (ISS) and Russian news reports.
Russia’s Interfax News Agency reported Wednesday that ISS Expedition 15 commander Fyodor Yurchikhin, a Russian Federal Space Agency cosmonaut, and U.S space tourist Charles Simonyi discussed Gates’ interest in orbital spaceflight from their perch aboard the space station.
More
here.
Bush Aides' Use of GOP e-Mail Probed
Via USA Today.
The White House said Wednesday it had mishandled Republican Party-sponsored e-mail accounts used by nearly two dozen presidential aides, resulting in the loss of an undetermined number of e-mails concerning official White House business.
Congressional investigators looking into the administration's firing of eight federal prosecutors already had the non-governmental e-mail accounts in their sights because some White House aides used them to help plan the U.S. attorneys' ouster. Democrats were questioning whether the use of the GOP-provided e-mail accounts was proof that the firings were political.
Democrats also have been asking if White House officials are purposely conducting sensitive official presidential business via non-governmental accounts to get around a law requiring preservation — and eventual disclosure — of presidential records. The announcement of the lost e-mails — a rare admission of error from the Bush White House at a delicate time for the administration's relations with Democratically controlled Capitol Hill — gave new fodder for inquiry on this front.
More
here.
Gapingvoid: The Network
Via gapingvoid.com. Enjoy!

U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Wednesday, April 11, 2007, at least 3,292 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,674 died as a result of hostile action, according to the military's numbers.
The AP count is five higher than the Defense Department's tally, last updated Wednesday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Australia: Telstra Accused of Misinforming About Broadband Services
Via The New Zealand Herald.
A group of telecommunications and internet companies have complained to the Government's competition watchdog that Telstra is waging a campaign of misinformation about the state of broadband services in Australia.
Eleven companies, including AAPT, Austar and Primus Telecom, have sent a letter of complaint to the Australian Competition and Consumer Commission (ACCC) calling for an investigation into a series of recent public statements by Telstra about broadband.
The move comes as the Federal Government is under increasing pressure to improve broadband infrastructure around Australia following an announcement by Labor last month that it would spend $4.7 billion to build a high-speed broadband network if it won office this year.
The letter to the ACCC is part of a wider campaign being run by the 11 companies dubbed "Tell the Truth Telstra".
More
here.
Just How Much Will That Data Breach Cost Your Company?
Jaikumar Vijayan writes on ComputerWorld:
Want to know just how much a data breach is likely to end up costing your company? Darwin Professional Underwriters Inc. may be able to help.
The Farmington, Conn.-based technology liability insurance company has released a free online calculator that it said allows businesses to estimate -- with a fair degree of accuracy -- their financial risk from data theft.
More
here.
Internet Security Aalliance Pushes for Security Incentives Instead of Regulation
Grant Gross writes on InfoWorld:
The U.S. government should explore new incentives for companies to invest in cybersecurity instead of focusing on regulation, a cybersecurity trade group said.
The ISA (Internet Security Alliance), made up of IT vendors and customers, called on the U.S. government to abandon old regulatory approaches in favor of incentives like cybersecurity insurance, awards programs, and caps on legal liability for companies that adopt cybersecurity best practices.
The alliance, in a white paper released Wednesday, said legislation that requires the U.S. government to create cybersecurity standards, including the Improving America's Security Act passed by the U.S. Senate in mid-March, takes the wrong approach. The Improving America's Security Act would authorize the U.S. Department of Homeland Security to develop standardization and certification programs for U.S. critical infrastructure, including the Internet.
More
here.
FBI Seeks Six Years to Process FOIA Request
Scott Hodes writes on The FOIA Blog:
The Washington Post is reporting that the FBI is seeking six years, until 2013, to complete its processing of a request submitted by the National Security Archive. The matter is now before a federal judge who will have to decide if the time request is permissable pursuant to FOIA caselaw.
The six years sought by the FBI is not unprecedented. In the late 1980's and early 1990's the FBI, and other agencies, routinely sought lengthy periods of time to process FOIA requests when litigation was brought on those requests due to large FOIA backlogs. However, the FBI, and other agencies, worked on reducing those backlogs, and by the early part of this decade, had eliminated the need to ask for such long periods of time. Unfortunately, agencies, such as the FBI, have now reversed the clock and find themselves unable to process large requests in what would appear to be a reasonable period of time.
It will be interesting how the National Security Archive attacks the FBI's request for six years and whether the Court will grant fully grant the time.
More
here.
The Actual Computer Crime Law (As Interpreted)
Friend and colleague Scott Bradner writes on NetworkWorld:
The United States has a lot of laws (a surfeit some might say). It's doubtful any one person can know them all, even within a particular jurisdiction and about a particular topic. But fear not, the Department of Justice is here to help at least in one area.
It has just published another manual in a series examining federal laws in the realm of computer crime. So you too can see what laws you might be breaking as you go through your average day of computer work.
More
here.
Comcast to Buy Fandango Movie Tickets Website
Via Reuters.
Top U.S. cable operator Comcast Corp. said it will buy movie tickets site Fandango as part of the launch of a new online entertainment business.
Financial terms of the deal were not furnished.
The new online entertainment site, called Fancast.com, will let consumers search and watch online entertainment.
More
here.
U.S. State Dept. Comes Up Short on Information Security
Alice Lipowicz writes on GCN.com:
Despite some improvements, the State Department still falls short in its information security efforts, according to a new report [.pdf] from Inspector General Howard J. Krongard.
Nearly half of the 34 departmental posts and bureaus audited by the inspector general from April to September 2006 displayed shortcomings in IT security, according to the report. These shortcomings were apparent in classified data being stored in unclassified systems, inadequate separation of duties among IT employees and missing or inadequate documentation on security settings used to protect data.
Despite progress in addressing privacy and in reporting computer hacking incidents, the department also shows inadequacies in its Federal Information Security Management compliance and documentation.
More
here.
DoJ Losses Bid to Block Prisoner's Testimony
Roy Mark writes on internetnews.com:
Inmate #35211-086 will, after all, testify Thursday morning before the U.S. Senate Finance Committee on his criminal career as an identity thief who used online auctions to hijack peoples' identities for financial gain.
Earlier this week, the Department of Justice (DoJ) attempted to quash a summons for notorious scam artist Evangelos Dimitrios Soukas' appearance.
Soukas, 28, is expected to testify on the various online schemes he used to defraud victims of more than a million dollars. Using stolen identities obtained in fraudulent Internet auctions, Soukas filed false income tax returns in his victims' names in an attempt to obtain tax refunds. He even applied for refund anticipation loans in his victims' names.
But Monday the DoJ asked U.S. District Judge Thomas F. Hogan to dismiss the Finance Committee's summons for Soukas since the Bureau of Prisons' policy is to not allow inmates to have an "elevated status" over other prisoners. The DoJ also cited "security concerns."
More
here.
EFF Sues DoJ for Immediate Release of NSL Abuse Records
Via The EFF.
The Electronic Frontier Foundation (EFF) has asked a judge to issue an emergency order requiring the FBI to immediately release agency records about its abuse of National Security Letters (NSLs) to collect Americans' personal information.
Congressional hearings and a storm of media coverage followed a recent Justice Department report detailing the FBI's extensive misuse of NSLs -- requests through which federal agents may collect telephone, Internet, financial, credit, and other personal records about Americans without judicial approval. The report and the ensuing uproar also sparked the introduction of a bill in the House of Representatives to curb the Bureau's NSL authority.
In a lawsuit filed under the Freedom of Information Act (FOIA), EFF demands that the FBI release all information about NSL abuse without delay, so that the records can be part of the national debate about domestic surveillance.
More
here.
Study: Data Breaches Break Consumer Trust
David Utter writes on SecurityProNews:
E-commerce sites that have not been diligent in protecting their consumer information from attacks may find their customer bases drop off as a result.
If you want to keep people visiting your site, you need to provide them with a secure environment and take steps to keep it that way. A study from Javelin Strategy showed that breached merchants will be hard-pressed to keep customers.
77 percent of Javelin's respondents said they intend to stop shopping at sites that have experienced data breaches. It is a tossup as to whether or not people will blame a site for a breach, with roughly half of consumers fixing responsibility to the site. Either way, getting them back will be a tough prospect.
More
here.
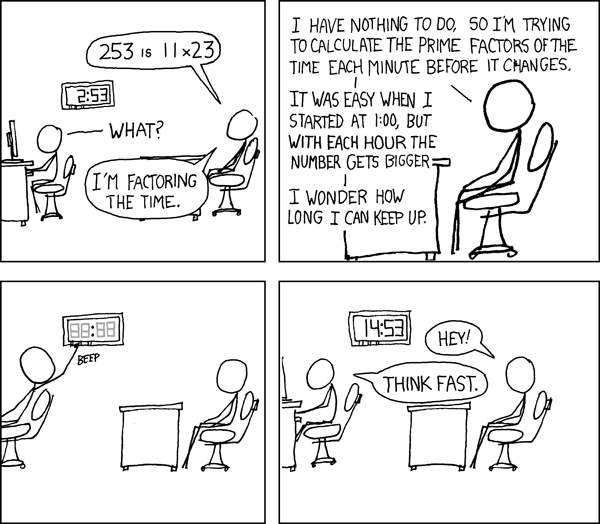
xkcd: Factoring Time
Click for larger image.
We also love
xkcd.
The FBI's Terrorism Trade-Off?
Paul Shukovsky, Tracy Johnson, and Daniel Lathrop write in The Seattle Post-Intelligencer:
Thousands of white-collar criminals across the country are no longer being prosecuted in federal court -- and, in many cases, not at all -- leaving a trail of frustrated victims and potentially billions of dollars in fraud and theft losses.
It is the untold story of the Bush administration's massive restructuring of the FBI after the terrorism attacks of 9/11.
Five-and-a-half years later, the White House and the Justice Department have failed to replace at least 2,400 agents transferred to counterterrorism squads, leaving far fewer agents on the trail of identity thieves, con artists, hatemongers and other criminals.
More
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Tuesday, April 10, 2007, at least 3,290 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,666 died as a result of hostile action, according to the military's numbers.
The AP count is 11 higher than the Defense Department's tally, last updated Tuesday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Oracle Has a Patch Tuesday, Too: Will Fix 37 Flaws
Joris Evers writes on C|Net News:
Oracle next week plans to release fixes for 37 security flaws across all its products, the company said Tuesday.
The fixes will be delivered April 17 as part of Oracle's quarterly patch cycle. Seven of the bugs are serious and could allow a system running the vulnerable Oracle software to be compromised remotely, the company said in a note on its Web site.
More
here.
WoW Players Learn Value of Windows Updates
Dan Goodin writes on The Register:
Subscribers playing World of Warcraft on Windows machines continue to find their accounts stolen more than eleven months after hackers first began targeting them using a Trojan attack, according to posts on the game's official website. The perpetrators are employing sophisticated techniques that involve hundreds of booby-trapped sites that in some cases use the ANI cursor vulnerability that Microsoft patched last week.
According to an advisory by McAfee, some ANI exploits are being carried out by the same malicious hackers who commandeered the Miami Dolphins football stadium just in time for the Superbowl. The Trojan unleashed in that attack sat dormant on compromised machines until users opened the WoW client, at which point a keylogger captured login credentials, according to the BBC.
More
here.
Quote of the Day: Joris Evers
"With Forefront, Microsoft is ramping up its efforts to convince businesses that it is the solution to, not the source of, their security woes."
- Joris Evers, writing on the C|Net Security Blog.
Bush Spy Chief Seeks to Boost U.S. Spy Powers - UPDATE
An AP newswire article by Kathrine Shrader, via SFGate.com, reports that:
President Bush's spy chief is pushing to expand the government's surveillance authority at the same time the administration is under attack for stretching its domestic eavesdropping powers.
National Intelligence Director Mike McConnell has circulated a draft bill that would expand the government's powers under the Foreign Intelligence Surveillance Act, liberalizing how that law can be used.
Known as "FISA," the 1978 law was passed to allow surveillance in espionage and other foreign intelligence investigations, but still allow federal judges on a secretive panel to ensure protections for U.S. citizens — at home or abroad — and other permanent U.S. residents.
The changes McConnell is seeking mostly affect a cloak-and-dagger category of warrants used to investigate suspected spies, terrorists and other national security threats. The surveillance could include planting listening devices and hidden cameras, searching luggage and breaking into homes to make copies of computer hard drives.
More
here.
UPDATE: 18:34 PDT: Ryan Singel has some additional commentary over on
Threat Level here.
New FOIA Office Head Appointed
Rebecca Carr writes on Window on Washington:
Attorney General Alberto Gonzales tapped a career Justice Department lawyer today to run the Office of Information and Privacy—the office in charge of deciding who gets public information requested under the Freedom of Information Act.
Melanie Ann Pustay replaces Daniel J. Metcalfe, who directed the office for 24 years with Richard Huff before he retired in January. Huff retired the year before.
Pustay arrived in the department in 1983 as an attorney advisor. However, she recently came under fire for failing to publish the FOIA Guide on time.
That criticism did not deter Gonzales.
More
here.
U.S. Navy Computer System Damaged, Former Contractor Sentenced
Via Technology News Daily.
Richard Sylvestre, 43, of Boylston, Massachusetts, was sentenced to 12 months and one day in prison, followed by three years of supervised release, and ordered to pay a $10,000 fine and $25,007 in restitution, upon his conviction for damaging protected United States Navy computers. Chuck Rosenberg, United States Attorney for the Eastern District of Virginia, made the announcement after Sylvestre was sentenced by United States District Judge Rebecca Beach Smith.
Sylvestre, a former Navy contractor, previously pled guilty on September 20, 2006 to intentionally damaging a Navy computer network used in furtherance of national security. This network was located at the United States Navy European Planning and Operations Command Center (NEPOCC) in Naples, Italy, where Sylvestre worked as one of three systemadministrators. In this role, Sylvestre helped to oversee the daily operation of a computer systemused to track and plot the locations of ships, submarines, and underwater obstructions within areas covered by the Navy’s European Command.
More
here.
Toon of the Day: The Real Cause of Global Warming
Click for larger image.
We
love Mr. Fish.
FTC Official: Imprison Spyware Distributors
Anne Broache writes on the C|Net Security Blog:
Steep fines are nice, but one of the best weapons against spyware purveyors is locking them up, a federal regulator told senators on Tuesday.
At a morning Senate Commerce Committee hearing here, Federal Trade Commissioner William Kovacic said most wrongdoers in the spyware arena "can only be described as vicious organized criminals."
"Many of most serious wrongdoers we observed in this area, I believe, are only going to be deterred if their freedom is withdrawn," so it's important for the FTC to collaborate on its cases with criminal law enforcement authorities, Kovacic said.
More
here.
Microsoft Patch Tuesday: PATCH NOW
There are a couple of really, really critical security vulnerabilities that need to be patched immediately.
You have been warned. Really -- it's
that bad.
- ferg
Bush, DoD get 'Muzzle' Awards

An AP newswire article, via Military.com, reports that:
The Bush administration and the Defense Department are among the winners of the 2007 Jefferson Muzzle awards, given Tuesday by a free-speech group to those it considers the most egregious First Amendment violators in the past year.
The Bush administration appears on the list, compiled by the Thomas Jefferson Center for the Protection of Free Expression, for its efforts to discourage, modify and sometimes censor government scientists' reports and studies to be more in line with the administration's political policies, notably on global warming, the center said.
More
here.