Cyber Crime Online: Card PINs Traded at Two for a Dollar
Leo Lewis writes on The Times Online:
The buyers and sellers converse cheerfully in the international language of commerce: negotiating prices, swapping samples, issuing quality assurances and loyalty discounts. One vendor, a Russian, offers a Chinese customer free translations of the product’s instruction manual; another promises “friendly technical support”.
It is here, in this polite, super-exclusive online marketplace, that the world’s most dangerous cybervillains plot to make your life a misery and get fabulously rich in the process. This is where your debit card PIN is bought and sold, your e-mail inbox engorged with spam, your identity touted to the highest bidder and the company you work for blackmailed or incapacitated.
From here, a rogue IT engineer can sell access to the tills of 50 high street stores or a Taiwanese factory worker can be bribed to install spy software in a dozen credit card readers. Botnets, trojans, worms — and worse — are fomented here.
Forums such as this, say analysts of cybercrime, have become the hubs of a £30 billion-a-year global industry that in 2008 alone spirited nearly 300 million items of supposedly secure information from the internet.
More
here.
DefCon Air Traffic Control Hacker: Excuse Me While I Change Your Aircraft's Flight Plan
Dean Takahashi writes on VentureBeat:
In a scary presentation at the Defcon hacker conference, a security researcher showed how easy it is to compromise the Federal Aviation Administration’s air traffic control system.
Righter Kunkel was careful not to show exactly how to bring aircraft out of the sky. But he showed how its easy to shut down information going into an air traffic control tower, jam radar, submit a fake aircraft flight plan, get recognized as a pilot even if you aren’t a pilot, and stop planes from taking off at an airport.
Kunkel laid out the process. You could get a fake identification (which is illegal). Go to the doctor and get an aviation medical certificate which shows you are fit to fly. With that, you can get a student pilot’s certificate number. Then you can log into the FAA’s pilot registration site. Then you can submit yor own flight plans.
You would think this stuff would be impossible in the age after 9/11. But then, it’s easy to believe, considering the plodding place at which the government is embracing new technologies, such as those that make government computer systems more secure. And the FAA’s priority has been keeping planes safe in the sky, not necessarily shoring up its network security.
More
here.
U.S. Defense Deparment Eyes DefCon for New Recruits
Robert McMillan writes on ComputerWorld:
The U.S. Air Force has found an unlikely source of new recruits: The yearly Defcon hacking conference, which runs Thursday through Sunday in Las Vegas.
Col. Michael Convertino came to Defcon for the first time last year, and after finding about 60 good candidates for both enlisted and civilian positions decided to come back again.
"The principal reason that I'm here is to recruit," said Convertino, commander of the U.S. Air Force's 318th Information Operations Group, speaking Thursday during a panel discussion at Defcon's sister conference, Black Hat. "We have many empty jobs, empty slots that we can't fill."
Federal agencies have only recently begun embracing the hacker crowd. When U.S. Department of Defense (DoD) director of futures exploration Jim Christy hosted his first Defcon "Meet the Fed" panel on 1999, he was one of two people onstage. At this week's Defcon, there may be several thousand federal employees in attendance, he said.
More
here.
U.S. Weighs Risks of Civilian Harm in Cyber Warfare
John Markoff and Thom Shanker write in The New York Times:
It would have been the most far-reaching case of computer sabotage in history. In 2003, the Pentagon and American intelligence agencies made plans for a cyberattack to freeze billions of dollars in the bank accounts of Saddam Hussein and cripple his government’s financial system before the United States invaded Iraq. He would have no money for war supplies. No money to pay troops.
“We knew we could pull it off — we had the tools,” said one senior official who worked at the Pentagon when the highly classified plan was developed.
But the attack never got the green light. Bush administration officials worried that the effects would not be limited to Iraq but instead create worldwide financial havoc, spreading across the Middle East to Europe and perhaps to the United States.
Fears of such collateral damage are at the heart of the debate as the Obama administration and its Pentagon leadership struggle to develop rules and tactics for carrying out attacks in cyberspace.
More
here.
SCADA Watch: Open Sesame! Network Attack Literally Unlocks Doors
Kim Zetter writes on Threat Level:
Security researchers have spent a lot of time the last couple of years cracking building access systems from the level of the user device — RFID and smartcards, for example.
But a researcher in Texas found that he could crack one electronic access system at the network control level and simply open a door with a spoofed command sent over the network, eliminating the need for an access card. He could do it while bypassing the audit log, so the system wouldn’t see that someone opened the door.
The hack is possible because the system uses predictable TCP sequence numbering.
Ricky Lawshae, a network technician for Texas State University, presented his findings on Friday at the DefCon hacker conference.
More
here.
In Passing: Corazon Aquino

Gary McKinnon Loses Extradition Appeals
 Gary McKinnon
Gary McKinnonKevin Poulsen
writes on
Threat Level:
Britain’s High Court on Friday rejected two extradition appeals by Pentagon hacker and 9/11 truther Gary “Solo” McKinnon, who’s trying to avoid a U.S. trial for cracking nearly 100 Pentagon and NASA computers in 2001 and 2002.
If convicted, McKinnon, 43, faces anywhere from six months to six-and-a-half years in prison under federal sentencing guidelines, depending on how much damage he caused, and other factors.
Lawyers for McKinnon argued that Home Secretary Jacqui Smith failed to consider McKinnon’s recent diagnosis of Asperger’s Syndrome when ordering his extradition, and that British prosecutors should charge the hacker in Britain, where he lives. But Judge Stanley Burnton said in a 41-page opinion Friday that extradition was “a lawful and proportionate response to his offending,” according to the AP.
More
here.
Adobe Releases Security Updates for Reader and Acrobat
Via U.S. CERT.
Adobe has released Reader 9.1.3 and Acrobat 9.1.3 to address a vulnerability. By convincing a user to open a PDF document embedded with a specially crafted SWF file, an attacker may be able to execute arbitrary code.
US-CERT encourages users and administrators to review Adobe security bulletin APSB09-10 and apply any necessary updates to help mitigate the risks. Additional information regarding this vulnerability can be found in US-CERT Technical Cyber Security Alert TA09-204A.
Link.
Following the Money: Rogue Anti-virus Software
Brian Krebs writes on Security Fix:
By its very nature, the architecture and limited rules governing the Web make it difficult to track individuals who might be involved in improper activity. Cyber-sleuths often must navigate through a maze of dead-end records, pseudonyms or anonymous corporations, usually based overseas. The success rate is fairly low.
Even if you manage to trace one link in the chain -- such as a payment processor or Web host -- the business or person involved claims that he or she was merely providing a legal service to an unknown client who turns out to be a scammer.
But every so often, subtle links between the various layers suggest a more visible role by various parties involved. This was what I found recently, when I began investigating a Web site name called innovagest2000.com.
This Innovagest2000 domain has for at least four years now been associated with spyware and so-called "scareware," surreptitiously installed software that bombards the victim with incessant and misleading warnings that their PC is infested with malicious software. The warnings usually mimic Microsoft software or the operating system itself, and persist until the victim figures out how to remove it or pays for a license to the software.
More
here.
Mark Fiore: Beer

More Mark Fiore brilliance.
Via The San Francisco Chronicle.
Enjoy.
- ferg
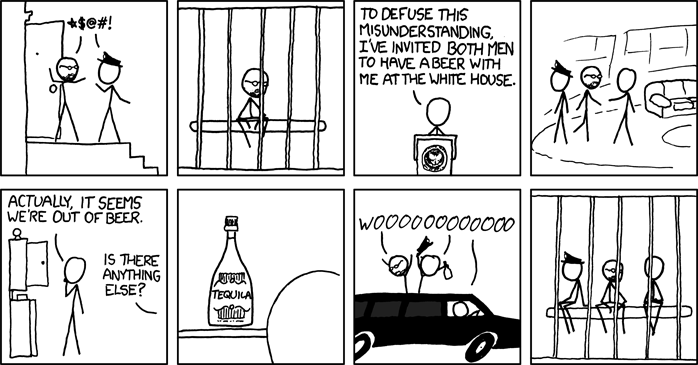
Classic xkcd: Tequila
Click for larger image.
Being a big fan of Tequila, we love
xkcd even more now.
Enjoy.
- ferg
PBS NOVA: Astro Spies

Great show, worth watching.
- ferg
Adobe Updates Flash Player for 10 Vulnerabilities
Angela Moscaritolo writes on SC Magazine:
Adobe on Thursday issued a security update for Flash Player and AIR to address a number of critical vulnerabilities which could potentially allow an attacker to take control of the affected system.
The flaws affect the current versions of Adobe Flash Player 9 and 10 for Windows, Macintosh and Linux operating systems and Adobe AIR 1.5.1 and earlier versions, Adobe said in its security bulletin.
The update addresses 10 vulnerabilities in total. Specifically, it addresses a bug caused by a flaw in Microsoft's Active Template Library (ATL) that Microsoft patched in Internet Explorer and Visual Studio on Tuesday. This vulnerability could allow an attacker to take control of an affected system, Adobe said.
In addition, the update addresses a memory corruption vulnerability that Adobe said last week was being exploited in the wild in targeted attacks. The critical bug, which affects not only Flash Player and AIR, but also Adobe Reader and Acrobat, could cause a computer to crash or enable an attacker to take control of an affected system. Adobe said it plans to update Adobe Reader and Acrobat to address this vulnerability on Friday.
More
here.
Future of Cyber Security: Hackers Have Grown Up
Kevin Poulsen writes on Wired's Dual Perspectives:
Late last year, the software engineers developing a new Windows-based networking client confronted an all-too-common problem in today's hostile internet environment: How would they make their software resistant to the legions of enemies waiting to attack it? Particularly worrisome was a key feature of their code, a mechanism to accept updates online. If it were subverted, an attacker could slip his own program into an installed base of millions of machines.
The coders decided to fortify their software with MIT's brand-new, high-security cryptographic hashing algorithm called MD-6. It was an ambitious choice: MD-6 had been released just two months before, and hadn't yet faced the rigors of real-life deployment. Sure enough, the move seemed to backfire when a security hole was found in MD-6's reference implementation not long after the launch. But the coders rallied, and pushed out a corrected version in a new release of their software just weeks later.
It would be a model for secure software development, except for one detail: The "Windows-based networking client" in the example above is the B-variant of the spam-spewing Conficker worm; the corrected version is Conficker C, and the hard-working security-minded coders and software engineers? A criminal gang of anonymous malware writers, likely based in Ukraine. The very first real-world use of MD-6, an important new security algorithm, was by the bad guys.
More
here.
Hackers Crack MI5 Website
Via the Daily Express:
Computer hackers have invaded MI5’s official website, it emerged last night.
The gang rigged the site so the identity of visitors could be stolen and viruses downloaded on to their machines.
The hackers, who called themselves Team Elite, would also have been able to discover the identity of anyone using Britain’s intelligence services website and find out every other website they had visited years earlier. The lapse is a major embarrassment for MI5, which is responsible for monitoring threats inside the UK.
One computer expert said it was “a schoolboy error”.
Tory MP Patrick Mercer said last night: “Having potentially highly-classified information available to hackers is deeply concerning. The identity of agents and informers in terror groups such as Al Qaeda are held by MI5.
More
here.
Researcher Pressured to Pull 'Conficker' Talk
Jim Finkle writes for Reuters:
Investigators searching for the criminals who infected millions of computers with the notorious Conficker virus are trying to limit access to information about its creators.
The investigators pressured one of the world's leading experts in cybercrime to pull a talk on Conficker's origins and motives of the gang behind the attack. He was due to discuss the topic on Thursday at the Black Hat security conference in Las Vegas, one of the world's top forums for exchanging information on Internet threats
"I was asked not to go into that because of an ongoing investigation," Mikko Hypponen, chief research officer for Internet security firm F-Secure, said in an interview on Wednesday.
He declined to say which agency requested him to pull the talk or explain why they asked him to do so.
More
here.
Black Hat: Less Gov't Involvement Would Be A Good Thing
Dan Kaplan writes on SC Magazine:
While all eyes seem fixated on who will be named to the federal cybersecurity coordinator post, some may be overlooking the expansiveness of the private sector to defend against attacks, according to a panel of government and public policy experts speaking Wednesday at the Black Hat conference in Las Vegas.
“If our nation came under attack tonight, we don't have a way to respond,” said Marcus Sachs, executive director of government affairs for national security policy at Verizon.
“We've got to, as a nation, step up to the plate and be leaders as we've always been,” added Sachs, who also is director of the all-volunteer SANS Internet Storm Center. “Do we need a cyberczar? Are we that hopeless that we can't figure out, as community, how to do this?”
The private sector owns about 85 percent of the nation's critical infrastructure.
Amit Yoran, CEO of security intelligence firm NetWitness and the former director of US-CERT, agreed.
“To think that the government is the center of defense in the cyber realm, I think is a fallacy,” he said.
More
here.
Clampi Trojan Revealed as Financial-Plundering Botnet Monster
Ellen Messmer writes on NetworkWorld:
A close look at the Clampi Trojan, an elusive piece of malware that uses encryption to help hide its nefarious data-stealing deeds, reveals it to be a botnet-controlled monster that can swipe a victim's sensitive data associated with more than 4,500 different sites, according to one researcher.
"We've been able to get through the layers of encryption in Clampi," says Joe Stewart, director of malware research at SecureWorks. "Clampi is collecting data associated with about 4,600 sites, such as banks and other financial institutions targeted by criminal networks."
But it doesn't stop there.
Clampi "is going after utilities, market research firms, online casinos and career sites," Stewart says, in a broad sweep to grab personally identifiable information, such as credentials and account information, that might be of use to criminals for financial gain. Clampi, also known as Ligats, Ilomo or Rscan, is using psexec tools to spread to spread across Microsoft-based networks in a worm-like fashion.
More
here.
Black Hat: Fighting Russian Cyber Crime Mobsters
Adam Ely writes on InformationWeek:
McAfee and the FBI teamed up at Black Hat to discuss Russian online organized crime. The standing room only presentation was part fact and part hype. With a mission to publicize the FBI’s work, Russians were made to be some of the most organized and threatening of all cybercriminals. While this could be true, the connections to American and other hackers around the world were drawn and cannot be ignored.
Composed of money laundering, botnets, hacking, and other activities, organized crime racks up $256 Million USD a year in losses for US organizations alone. This figure is based on losses reported to the FBI’s Internet Crime Compliant Center (IC3) in 2008.
Tracking down Russian online cybercriminals is a difficult task and one where the FBI often fails. With crimes occurring in the US linked to Eastern Europe, such as the TJX breach, global cybercrime is hitting home. It is important for US law enforcement to be aware of and attempt to shut down these global rings.
Punishment for cybercriminals in Russia is so disproportionate with the rewards for committing such crimes that the criminals are not deterred and will continue to perform the crimes once released. One such criminal, whose testimony was presented during the Black Hat talk, received only 6 months in jail and commented that he will commit the same crimes once he is released.
More
here.
Security Breaches Cost Businesses Customers
Jeremy Kirk writes on PC Advisor:
Companies that have lost sensitive data are being shunned by consumers, according to a new study.
The Ponemon Institute, which studies privacy procedures in companies and government organisations, studied 43 US companies that lost sensitive data last year. The research revealed that on average, it cost the companies $202 (£141) for every data record lost in 2008. That's compared with $197 (£138) in 2007, $182 (£127) in 2006 and $138 (£96) in 2005, the first year the study was conducted.
Factored into those figures are how much companies spend on detecting data losses, costs incurred notifying victims and hiring forensic experts and paying for free credit checks for affected consumers, among others.
The most costly factor, however, was loss of business. Of the $202 (£141), $139 (£97) represented the cost of lost business, up 69 percent over 2007.
"The growth in lost business costs demonstrates consumers do not take a breach of their trust and privacy lightly and have not become desensitised to the issue," the study said.
More
here.
Napolitano to Unveil New Antiterror Plans
Cam Simpson writes in The Wall Street Journal:
Homeland Security Secretary Janet Napolitano is expected to outline Wednesday the Obama administration's domestic approach to preventing terrorist attacks -- a strategy that will rely in large measure on refining and expanding initiatives launched under President George W. Bush.
How to keep the U.S. safe and foil terrorists are charged issues that took a central role in last year's presidential campaign, when then-Sen. Barack Obama criticized the Bush administration's tactics. But Ms. Napolitano, in an interview this week, signaled that the Obama administration isn't contemplating a wholesale revision of the agencies or programs created under Mr. Bush to further antiterrorism efforts.
One element of Ms. Napolitano's approach, for example, will be the expansion of a pilot program started during the Bush administration to train police to report such suspicious behavior as the theft of keys from a facility that keeps radiological waste.
It is part of a much broader effort to significantly increase cooperation between her agency and state and local governments across the nation. Her aides say this is one area where her efforts will significantly exceed those of her predecessors in the Bush administration.
More
here.
NOVA: The Spy Factory

If you haven't seen "Spy Factory" on NOVA, you really should.
Link.
- ferg
U.S. Supercomputing Lead Rings Sputnik-Like Alarm for Russia
Patrick Thibodeau writes on ComputerWorld:
Russia's launch of Sputnik in 1957 triggered a crisis of confidence in the U.S. that helped drive the creation of a space program. Now, Russia is comparing the U.S.'s achievements in supercomputing with theirs, and they don't like what they see.
In a speech on Tuesday, Russia's President, Dmitry Medvedev, criticized his country's IT industry almost to the point of sarcasm for failing to develop supercomputing technology, and urged a dramatic change in Russia's use of high-performance computing.
Medvedev, at the opening address of a Security Council Meeting on Supercomputers in Moscow, told attendees that 476 out of the 500 supercomputers on the Top500 list were manufactured in the United States. "Therefore, in general, our situation is very difficult," he said.
Medvedev was clear about his blame for this gap.
"If we are talking seriously, a huge number of entrepreneurs, not to mention officials, do not know what supercomputers are: For them it is an exotic type of those machines that were created in the 1920s to catch up and overtake America," Medvedev said in remarks published on a government Web site.
More
here.
SCADA Watch: 'Smart Grid' Raises Security Concerns
Brian Krebs writes in The Washington Post:
Electric utilities vying for $3.9 billion in new federal "smart grid" grants will need to prove that they are taking steps to prevent cyberattacks as they move to link nearly all elements of the U.S. power grid to the public Internet.
The requirements from the Energy Department come amid mounting concern from security experts that many existing smart-grid efforts do not have sufficient built-in protections against computer hacking, such as new "smart meters" that put information about consumers' power use onto the Internet, grid-management software and other equipment.
The smart-grid spending in the federal stimulus package is intended to create jobs and improve the efficiency and reliability of the electricity grid by lowering peak demand, reducing energy consumption, integrating more renewable energy sources and easing the pressure to build new coal-fired power plants.
Many of those efficiency gains will be made possible by new technology being built on top of the existing power grid, such as smart meters, which provide real-time feedback on power consumption patterns and levels. An estimated 8 million smart meters are used in the United States today, and more than 50 million more could be installed in at least two dozen states over the next five years, according to the Edison Foundation's Institute for Electric Efficiency.
Yet security researchers have found that these devices often are the weakest link in the smart-grid chain. Smart meters give consumers direct access to information about their power usage and the ability to manage that usage over the Web, but that two-way communication also opens up the possibility that the grid could be attacked from the outside. Many such systems require little authentication to carry out key functions, such as disconnecting customers from the power grid.
More
here.
Holy Twister, Batman: Infectious Diseases Study Site - In Tornado Alley - Questioned
Carol D. Leonnig writes in The Washington Post:
The Department of Homeland Security relied on a rushed, flawed study to justify its decision to locate a $700 million research facility for highly infectious pathogens in a tornado-prone section of Kansas, according to a government report.
The department's analysis was not "scientifically defensible" in concluding that it could safely handle dangerous animal diseases in Kansas -- or any other location on the U.S. mainland, according to a Government Accountability Office draft report obtained by The Washington Post. The GAO said DHS greatly underestimated the chance of accidental release and major contamination from such research, which has been conducted only on a remote island off the United States.
DHS staff members tried quietly last week to fend off a public airing of the facility's risks, agency correspondence shows. Department officials met privately with staff members of a congressional oversight subcommittee to try to convince them that the GAO report was unfair, and to urge them to forgo or postpone a hearing. But the House Energy and Commerce Committee's oversight and investigations subcommittee, chaired by Rep. Bart Stupak (D-Mich.), decided otherwise. It plans to hold a hearing Thursday on the risk analysis, according to two sources briefed on the plans.
The criticism of DHS's site selection comes as the proposed research lab, the National Bio and Agro-Defense Facility (NBAF), was expected to win construction funding in the congressional appropriations process.
More
here.
U.S. Citizens Wrongly Detained, Deported by ICE
Tyche Hendricks writes in The San Francisco Chronicle:
The son of a decorated Vietnam veteran, Hector Veloz is a U.S. citizen, but in 2007 immigration officials mistook him for an illegal immigrant and locked him in an Arizona prison for 13 months.
Veloz had to prove his citizenship from behind bars. An aunt helped him track down his father's birth certificate and his own, his parents' marriage certificate, his father's school, military and Social Security records.
After nine months, a judge determined that he was a citizen, but immigration authorities appealed the decision. He was detained for five more months before he found legal help and a judge ordered his case dropped.
"It was a nightmare," said Veloz, 37, a Los Angeles air conditioning installer.
Veloz is one of hundreds of U.S. citizens who have landed in the custody of U.S. Immigration and Customs Enforcement and struggled to prove they don't belong there, according to advocacy groups and legal scholars, who have tracked such cases around the country. Some citizens have been deported.
More
here.
This shit has got to stop.
-ferg
'Virtual' Credit Cards Are Worth Looking Into
George Gombossy writes in The Chicago Tribune:
In the battle against less than honorable businesses, consumers have a weapon that many of us have overlooked — the one-time use, or "virtual" credit cards.
John O'Leary of West Hartford brought these cards to my attention last month after reading my column about Dazzle White, the teeth-whitening company that has sucked in thousands of people by offering dirt-cheap samples on the Internet, but then charging $59 a month until customers figure out how to cancel the charges.
O'Leary said he has used his Citi virtual credit card for years for all Internet purchases, even from legitimate companies like Amazon.
With these cards, offered through at least Citi, Discover, Bank of America and Pay Pal, consumers can generate a new credit card number for each purchase or set specific spending limits, blocking companies like Dazzle White from putting additional charges on their credit cards.
More
here.
Hat-tip: The Consumerist
Chinese Hack Australian Film Festival Website
Via The BBC.
Chinese hackers have attacked the website of Australia's biggest film festival over a documentary about Uighur leader Rebiya Kadeer.
Content on the Melbourne International Film Festival site was briefly replaced with the Chinese flag and anti-Kadeer slogans on Saturday, reports said.
In an earlier protest on Friday, Beijing withdrew four Chinese films.
Melbourne's The Age newspaper says private security guards have been hired to protect Kadeer and other film-goers.
She is due to attend the screening of Ten Conditions of Love, by Australian documentary-maker Jeff Daniels, on 8 August.
More
here.