Computer Glitch Causes 5-Hour Delays at LAX - UPDATE
An AP newswire article, via MSNBC, reports that:
About 2,500 international passengers were stranded for as long as five hours Saturday on planes and in terminals at Los Angeles International Airport because a computer shutdown prevented them from passing through customs, authorities said.
The passengers were stranded in four airport terminals and on runways starting at about 1:30 p.m. because of a breakdown in a computer system that contains names of arriving passengers and law enforcement data about them including arrest warrants, said Mike Fleming, a Customs and Border Protection spokesman.
More
here.
UPDATE: 21:31 PDT: Los Angeles Times coverage
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Saturday, Aug. 11, 2007, at least 3,685 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,030 died as a result of hostile action, according to the military's numbers.
The AP count is seven more than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
UK: Database of Top-Secret Police Phone Taps Stolen - UPDATE
Ruth Elkins writes in The Independent:
Police chiefs have launched a major investigation after the theft of a computer database containing thousands of top-secret mobile phone records from terrorism and organised crime investigations.
Scotland Yard is concerned that crucial evidence from undercover investigations could be lost forever or has found its way into "the wrong hands" after the computer and other IT equipment disappeared from a private firm in Sevenoaks, Kent, last Monday night after a break-in.
Forensic Telecommunications Services, whose clients include Scotland Yard, The Police Service of Northern Ireland, HM Revenue and Customs and the Crown Prosecution Service, specialises in tapping mobile phone calls made by criminal suspects. The stolen security-protected server contained the minutiae of phone calls it had screened, including the identity of the person who had made the call, as well as the exact time and location of the suspect when the call was made.
In a statement released to The Mail on Sunday, Forensic Telecommunications Services confirmed that the equipment had been stolen from its offices but denied that its disappearance would impact negatively on current police cases.
Yeah. Right.
- fergMore
here.
UPDATE: 10:35 PDT, 21 August 2007: Apparently UK police has recovered the database. Details
here.
TJX Kiosk Rumors Re-Emerge
Evan Schuman writes on StorefrontBacktalk:
How did the TJX breach start? Reports that the attack began using a wireless entry point have been confirmed by multiple investigators, but reports that circulated in March that the attacks began via an in-store employment kiosk have re-emerged.
Could both be true? It’s unlikely, as both entry attempts were reprotedly successful, raising the question of why the second was attempted. Could TJX have actually been the victim of two simultaneous and unrelated attacks, one using wireless and the other a jobs kiosks that was not firewall-protected?
More
here.
(
Props, Emergent Chaos.)
Toon: Fourth and Goal
Click for larger image.
Tucson Man Sentenced to 7 Years in Prison for Stealing Money With Stolen Bank Cards
Alexis Huicochea writes in the Arizona Daily Star:
A 21-year-old Tucson man was sentenced to seven years in prison for his role in an identity theft ring that purchased stolen bank card numbers over the Internet to withdraw more than $1 million from ATMs.
Jacob Vincent Green-Bressler was sentenced Friday in federal court for conspiracy to commit offenses against the United States, aggravated identity theft and possession of stolen authentication features.
The charges stem from activity that began around September 2003 when Green-Bressler solicited and was supplied with stolen credit and debit card account information of U.S. banking customers from people in foreign countries.
He was able to get the information by going into Internet chat rooms run by the suppliers where they would advertise the sale of card information that was obtained illegally through various schemes, according to a news release from the U.S. Attorney’s Office in Arizona.
More
here.
(
Props, Flying Hamster.)
ICANN Investigating Domain Tasting
Michele Neylon writes on CircleID:
ICANN has announced that it is seeking input and feedback on the topic of domain tasting. (See their announcement for full details
Interestingly enough Michael Gilmour published an article a couple of days ago covering the same topic - “Why domain tasting is great!”, which will probably raise a few hackles!
More
here.
Reported Drop in Surveillance Spurred a Law
Eric Lichtblau, James Risen, and Mark Mazzetti write in The New York Times:
At a closed-door briefing in mid-July, senior intelligence officials startled lawmakers with some troubling news. American eavesdroppers were collecting just 25 percent of the foreign-based communications they had been receiving a few months earlier.
Congress needed to act quickly, intelligence officials said, to repair a dangerous situation.
Some lawmakers were alarmed. Others, jaded by past intelligence warnings, were skeptical.
The report helped set off a furious legislative rush last week that, improbably, broadened the administration’s authority to wiretap terrorism suspects without court oversight.
It was a surprising victory for the politically weakened White House on an issue that had plodded along in Congress for months without a clear sign of urgency or resolution. A flurry of talk in the last three weeks on intelligence gaps, heightened concern over terrorist attacks, burdensome court rulings and Congress’s recess helped turn the debate from a slow boil to a fever pitch.
More
here.
Alert: Scientist's Arrest Stirs Concern
 Marc van Roosmalen
Marc van RoosmalenAn AP newswire
article, via
PhysOrg.com, reports that:
Dutch scientist Marc van Roosmalen's success at combing the Amazon for new monkey species has earned him international acclaim and recognition as one of the world's leading biologists. Time magazine named him one of its "Heroes for the Planet."
Now his work has earned him a more troubling distinction: a nearly 16-year prison sentence. He was jailed in June for nearly two months before a panel of judges freed him on bail Tuesday while he appeals.
Van Roosmalen was convicted of holding an Internet auction for the naming rights of two monkey species he discovered. He planned to use the proceeds to help preserve their habitats. But the court ruled the auction was illegal because van Roosmalen was working at Brazil's National Institute for Amazon Research at the time of the discoveries and said the naming rights belonged to the government.
Van Roosmalen blames the state's powerful logging interests and overzealous environmental regulators for orchestrating his conviction and accuses them of trying to discourage scientific investigation.
More
here.
Image source: Michael Astor / AP
Retrospect: The TJX Effect
Larry Greenemeier writes on InformationWeek:
TJX will be glad when this year is over. The $17 billion-a-year parent company of T.J. Maxx, Marshall's, and several other discount retail chains has spent the past eight months dealing with the largest breach of customer data in U.S. history, the details of which are starting to come to light.
Last December, TJX says it alerted law enforcement that data thieves had made off with more than 45 million customer records. Since that time, at least one business, Wal-Mart, has lost millions of dollars as a result of the theft, while TJX has spent more than $20 million investigating the breach, notifying customers, and hiring lawyers to handle dozens of lawsuits from customers and financial institutions. Should TJX lose in the courts, it could be on the hook for millions more in damages.
But there's an even broader TJX Effect: The data breach, which actually took place over a period of years, has put the entire retail industry on the defensive and stirred up demands for all businesses that handle payment card information to do a better job of protecting it. Legislators are invoking TJX's name to fast-track data-security bills.
More
here.
'Unverified' Terror Threat Prompts NYPD Caution - UPDATE
Richard Esposito reports on ABC News' "The Blotter":
Despite its apparent unreliability, an Internet report of a possible terrorist attack on New York City published by a private, Israel-based counterterrorism Web site has prompted police to increase deployment of sensors around Manhattan, officials said Friday night.
New York Deputy Police Commissioner Paul J. Browne stressed that the threat was "unverified" and that its increased vigilance was "strictly precautionary."
More
here.
UPDATE: 20:06, 11 August 2007: An AP newswire article,
MSNBC, explains that "
NYC reduces security after ‘radiological threat’."
U.S. Toll in Iraq, Afghanistan
Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Friday, Aug. 10, 2007, at least 3,684 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,030 died as a result of hostile action, according to the military's numbers.
The AP count is six more than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
As of Friday, Aug. 10, 2007, at least 356 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures August 4, 2007.
Of those, the military reports 235 were killed by hostile action.
More
here and
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
VoIP Hacker: Service Provider Nets Easy Pickings
Tim Greene writes on NetworkWorld:
A combination of simple dictionary and brute-force attacks in combination with Google hacking enabled a criminal pair to break into VoIP-provider networks and steal $1 million worth of voice minutes, says one of the duo who has pleaded guilty to his crimes.
Had his victims observed security basics, most of the attacks would have been unsuccessful, says Robert Moore, the 23-year-old hacker from Spokane, Wash., who has been sentenced to two years in federal prison and fined $150,000.
More
here.
Exploit Released for Vulnerability in BIND9 Nameserver
Via heise Security News.
A program has appeared on the Milw0rm exploit portal which is able to exploit the recently reported vulnerability in the BIND9 nameserver. Transaction IDs can be predicted or guessed relatively easily, so the cache of a vulnerable nameserver can be poisoned. Phishers can use cache poisoning for pharming attacks on users by manipulating the assignment of a server name to an IP address. Even if the user enters the name of his bank in the address line of his browser manually, he will still be taken to a counterfeit web page.
However, the attacker must himself be in control of an authorative nameserver in order to manipulate the cache of a nameserver either by hacking into a server or administering a server for his own domain. In order to protect their users, operators using BIND9 should now install the version cleared of the bug as soon as possible. Amit Klein who discovered the hole estimates that around half of all the nameservers on the web are running BIND9 so the latest vulnerability could potentially affect the entire internet.
More
here.
Site of the Day: Security Problem Excuse Bingo

Props, Matt Blaze and Jutta Degener. Hat-tip, Bruce Schneier.
SCADA Watch: Knowledge is Greatest Threat to Critical Infrastructure
Liam Tung writes on ZDNet Australia:
The threat of terrorism has raised concerns over the security of essential services as SCADA systems have increasingly been opened to TCP/IP protocol corporate networks to improve process automation and visibility of data.
Cause for this concern was reaffirmed recently when a security expert from 3Com's security division, Tipping Point, at the Black Hat conference in Las Vegas, demonstrated how a SCADA system flaw could be exploited to cause the system to crash.
More
here.
UK Report Questions Role of ISPs in Online Safety
Jeremy Kirk writes on InfoWorld:
A new report on Internet safety has concluded ISPs (Internet service providers) should take more responsibility for online security since end users are often lax.
But the 121-page Personal Internet Security report [.pdf], published on Friday by the U.K. House of Lords, stopped short of suggesting that the Office of Communications (Ofcom) -- the U.K. communications regulator -- should impose new rules on ISPs.
"We do not advocate immediate legislation or heavy-handed intervention by the regulator," the report said. "But the market will need to be pushed a little if it is to deliver better security."
ISPs generally argue that security is the responsibility of end users, which Ofcom has also supported. The report called it "disappointing" that the U.K. government has accepted those arguments since the reality often exceeds the capability of end users to recognize the threats.
More
here.
TSA Unveils Planned Overhaul of Airport Screening
Ryan Singel writes on Wired News:
The federal government proposed Thursday to overhaul how airline passengers are screened against terrorist watch lists by taking over the process from airlines, and closing a long-known security hole that allows a person to evade extra screening using a fake boarding pass.
The new program, known as Secure Flight, would require airlines to forward itineraries to the government starting 72 hours before a flight. The Transportation Security Administration would then compare the names, dates of birth and gender against hundreds of thousands of names on the No-Fly and Selectee watch lists, and send the results back to the airlines.
Those who match or have details similar to a name on the Selectee list will get a boarding pass with a special code singling them out for extra screening. Individuals who don't match will be free to print a boarding pass at home, if the airline offers that option.
More
here.
Toon of the Day: Surveillance Oversight
Click for larger image.
Hackers Find Easy Target in Universities, Public Agencies
Sue Schultz writes in The Baltimore Business Journal:
If searching for porn online, a Web surfer might be directed to Johns Hopkins Department of Psychological and Brain Sciences. It's not that Hopkins is branching out into a new business. But visitors who click on the esteemed department's Internet address are being redirected to sexually explicit Web sites.
The trend has universities, colleges and government agencies scrambling to keep hackers from muddying their good name and offending potential visitors. They're also trying to figure out a way to protect information from getting into the wrong hands.
"The universities and colleges aren't hosting porn, they are just helping the bad guys," said Alex Eckelberry, CEO of Sunbelt Software, a Clearwater, Fla., company that sells security software and researches and tracks hackers. "It's the plague of the Internet."
Hackers often get through holes in inadequately managed or updated security software, Eckelberry said. And the larger universities have more difficulty keeping hackers out.
More
here.
(
Hat-tip, Alex.)
Internet Hackers Steal Confidential Data on 60,000 Norwegians
Via The Brisbane Times.
Internet hackers have stolen confidential data on 60,000 Norwegians, including the head of the agency for safeguarding them, the agency itself revealed Friday.
It said they had used a weakness on the website of the telephone operators Tele2 to procure the national personal identity numbers and addresses of subscribers, amounting to 1.3 percent of the country's population.
The information would enable the hackers to change the addresses of the people concerned so as to intercept their mail, or order goods on their account.
More
here.
(
Props, Pogo Was Right.)
Australia Backflips on ISP Filters
Chris Jenkins writes on Australian IT:
The announcement of ISP-level internet filtering as part of the federal Government's NetAlert package has seen a major reversal on the technology, which the government last year derided as having "questionable benefits".
Communications Minister Senator Helen Coonan today announced a $189 million package of measures to improve the safety of using the internet.
As well as increased funding for the federal Police to track down online predators and national security threats, the package included $84.8 million to provide households with either internet filtering software packages or pre-filtered internet connections from an internet service provider.
But the endorsement of ISP-level filtering is at odds with earlier government assessments, which blasted the method as costly and ineffective in comparison to PC-level systems.
More
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Thursday, Aug. 9, 2007, at least 3,683 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,024 died as a result of hostile action, according to the military's numbers.
The AP count is ten more than the Defense Department's tally, last updated Thursday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
UK: Lords Chides Government Over Internet Security
Tom Espiner writes on ZDNet UK:
The government must act now or risk losing public confidence in the security of the internet, an influential House of Lords committee has found.
A wide-ranging inquiry into personal internet security conducted by the House of Lords Science and Technology Committee has "highlighted the threat to the future of the internet posed by e-crime".
"The government must do more to protect individual internet users," a House of Lords statement read.
"The internet, while still a powerful force for good, has increasingly become the playground for criminals. Today's e-criminals are highly skilled, organised and motivated by financial gain. Individual internet users are increasingly victimised," said the report.
More
here.
U.S. Navy Secretary Laments Continued Loss of Private Data
Sebastian Sprenger writes on FCW.com:
The Navy continues to wrestle with maintaining control of service members’ personal information.
“Unfortunately, numerous naval messages, media attention and changes to policy have had only a limited impact on improving our handling and safeguarding of [personally identifiable information], and losses have continued,” Navy Secretary Donald Winter wrote in a July 7 message to all Navy and Marine Corps personnel.
Personally identifiable information includes names, Social Security numbers, biometric records and medical histories.
In the past 19 months, Navy officials reported more than 100 incidents of such information of being lost. Those incidents affected more than 200,000 Navy and Marine Corps personnel, including retirees, civilians and dependents, according to Winter’s message.
More
here.
(
Props, Pogo Was Right.)
Note: Clearly, I agree with the editors at
Pogo Was Right when they say that
"...I don't remember seeing 100 incidents involving breaches of information involving the Navy in the past 19 months. Once again, it is clear that we only hear about the tip of the iceberg..."
Citing Four-Day Old Surveillance Law, Bush Seeks Dismissal of Lawsuit Challenging NSA Spying
David Kravets writes on Threat Level:
Four days after President Bush signed controversial legislation legalizing some warrantless surveillance of Americans, the administration is citing the law in a surprise motion today urging a federal judge to dismiss a lawsuit challenging the NSA spy program.
The lawsuit was brought by lawyers defending Guantanamo Bay prisoners. The lawyers and others alleged the threat of surveillance is chilling their First Amendment rights of speech, and their clients' right to legal representation.
Justice Department lawyers are asking U.S. District Judge Vaughn Walker to toss the case, citing the new law -- which says warrantless surveillance can continue for up to a year so long as one person in the intercepted communications is reasonably believed to be located outside of the United States.
The motion is set to be heard in federal court in San Francisco this afternoon.
More
here.
Patch Tuesday: Microsoft to Patch 9 Security Vulnerabilities
Via The MSRC Blog.
Next Tuesday, we’re currently planning to release nine security bulletins:
- Six Microsoft Security Bulletins affecting Microsoft Windows with a Maximum Severity rating of Critical. These updates will require a restart and will be detectable using the Microsoft Baseline Security Analyzer and the Enterprise Scan Tool.
- One Microsoft Security Bulletins affecting Microsoft Office with a Maximum Severity rating of Critical. These updates will not require a restart and will be detectable using the Microsoft Baseline Security Analyzer.
- One Microsoft Security Bulletin affecting Microsoft Office and Microsoft Windows a Maximum Severity rating of Critical. This update will require a restart and will be detectable using the Microsoft Baseline Security Analyzer.
- One Microsoft Security Bulletin affecting Microsoft Virtual PC and Microsoft Virtual Server with a Maximum Severity rating of Important. This update will require a restart and will be detectable using the Microsoft Baseline Security Analyzer and the Enterprise Scan Tool.
More
here.
Images: Record-Breaking Weather Pounds Mother Earth

Above: Oxford residents hold a protest blaming climate change for Britain's worst floods in 60 years on July 25, 2007.
Via National Geographic.
Image source: National Geographic / Chris Ison/ PA / AP
Credit Card Headaches From TJX Breach Remain
Se Young Lee writes in The Boston Globe:
Almost seven months after the biggest security breach of financial data in the nation was revealed, some banks still appear to be sorting out which of their credit card customers were put at risk.
Retail giant TJX Cos., with headquarters in Framingham, revealed this spring that at least 45.7 million credit and debit card numbers were compromised by hackers who gained access to the company's computer systems in the second half of 2005 as well as from May 2006 to January of this year. But some companies, such as Citibank, are still reissuing cards for customers whose information may have been exposed.
More
here.
Appeals Court Battle Over NSA Surveillance on August 15
Via the EFF.
In the wake of Congress approving a dramatic expansion of U.S. warrantless wiretapping powers, the 9th U.S. Circuit Court of Appeals will hear arguments on the future of two critical lawsuits over illegal surveillance of Americans. The hearing is set for August 15, at 2 p.m. in San Francisco.
The government is fighting to get the cases thrown out of court, contending that the litigation jeopardizes state secrets. The Electronic Frontier Foundation (EFF) is representing the plaintiffs in Hepting v. AT&T, which accuses the telecom giant of collaborating with the National Security Agency (NSA) in illegal electronic surveillance of millions of AT&T's customers. The court will also hear the arguments on the future of Al-Haramain Islamic Foundation v. Bush, a case alleging that the government illegally wiretapped calls between the charity and its lawyers.
More
here.
DARPA's New Tools for Net Defenders, Cyber-Snoops
Noah Shachtman writes on Danger Room:
It’s getting harder and harder for the Pentagon’s cyber defenders to protect military networks – and for federal snoops to peek in on our e-mail. DARPA, the Pentagon’s way-out research arm, has an idea for how to keep up: use the laws of heat flow to monitor network traffic. It's part of a bigger push to make sure net protectors and digital surveillance type can keep up with the rising tide of e-mail, web-surfing, and other online activities.
We all know about Moore’s Law – that computer processors will double in strength and speed every 18 months. But network traffic is grows even faster, at nearly double the rate. Every decade, the amount of packets expands a thousand-fold.
That’s a major worry for the Pentagon, and its cybersecurity pros. All that increased traffic means more bits to scan for viruses and other malicious code. If today’s trends keep up, DARPA program manager Brian Hearing tells DANGER ROOM, “we’d use the majority of DOD [Department of Defense] computers to monitor network traffic. Which won’t happen, obviously. So our ability to detect will drop.”
So Hearing is launching a new program, Scalable Network Monitoring, that aims to detect 99% of the bad code in a torrent of traffic, a hundred gigabits per second (GPS) -- with only a single false alarm per day. He's leading a meeting in Virginia next week, to kickstart the effort.
More
here.
A Gateway for Hackers: The Security Threat in the New Wiretapping Law
Susan Landau writes in The Washington Post:
Current administration policy is replete with examples of quickly enacted efforts whose consequences led to the opposite effect. (Beware of what you wish for . . . .) With Congress caving last week, the National Security Agency no longer needs a Foreign Intelligence Surveillance Act (FISA) warrant to wiretap if one party is believed to be outside the United States. This change looks reasonable at first, but it could create huge long-term security risks for the United States.
The immediate problem is fiber optics. Until recently, telecommunication signals came through the air. The NSA used satellites and antennas to pick up conversations of foreigners talking to other foreigners. Modern communications, however, use fiber; since conversations don't go through the air, the NSA wants to access communications at land-based switches.
Because communications from around the world often go through the United States, the government can still get access to much of the information it seeks. But wiretapping within the United States has required a FISA search warrant, and the NSA apparently found using FISA too time-consuming, even though emergency access was permitted as long as a warrant was applied for and granted within 72 hours of surveillance.
More
here.
Off Beat: China's iClone

Dan Koeppel writes on Popular Science:
The little gadget was bootleg gold, a secret treasure I'd spent months tracking down. The miniOne looked just like Apple's iPhone, down to the slick no-button interface.
But it was more.
It ran popular mobile software that the iPhone wouldn't. It worked with nearly every worldwide cellphone carrier, not just AT&T, and not only in the U.S. It promised to cost half as much as the iPhone and be available to 10 times as many consumers. The miniOne's first news teases—a forum posting, a few spy shots, a product announcement that vanished after a day—generated a frenzy of interest online. Was it real? When would it go on sale? And most intriguing, could it really be even better than the iPhone?
More
here.
Image source: PopSci / Mat Dartford
Korea: ISPs Suspected of Massive ID Theft
Simon Burns writes on ITWeek.co.uk:
Police are investigating South Korea's two biggest ISPs on suspicion that they broke identity theft laws on more than seven million occasions. The two companies, KT and Hanaro Telecom Inc, are suspected of signing up more than seven million customers for services without their permission, according to police sources cited by local media today.
Many of the company's internet service customers were apparently illegally signed up for additional services by telephone sales agents, who did not obtain the written consent required under law, police say. Reports say the two ISPs may have illegally signed up 7.3 million of the 10 million households and businesses in the country that rely on them for internet service.
More than 60 employees and agents working for the two firms are now being questioned by police. KT has announced that it is cooperating with authorities and that it will improve internal data security procedures. Hanaro Telecom CEO Park Byung-Moo made an apparent apology at a press conference today, saying "he feels sorry to customers for causing such trouble," according to the Korea Herald.
More
here.
(
Props, Pogo Was Right.)
Security Firms Working on Devices to Spot 'Would-Be Terrorists' in Crowd
Ian Sample writes in The Guardian:
Counter-terrorism experts have drawn up plans to develop an array of advanced technologies capable of spotting would-be terrorists in a crowd before they have time to strike.
Scientists and engineers have been asked to devise ways of analysing people's behaviour and physiology from afar, in the hope they may reveal clues about their mental state and even their future intentions.
Under Project Hostile Intent, scientists will aim to build devices that can pick up tell-tale signs of hostile intent or deception from people's heart rates, perspiration and tiny shifts in facial expressions.
The project was launched by the US department of homeland security with a call to security companies and government laboratories for assistance.
More
here.
Australia: Pipe Networks Picks Tyco to Build Submarine Cable
Stuart Comer writes on iTWire.com:
Pipe Networks is yet to make a firm commitment to proceed with Project Rainbow, its planned submarine cable linking Sydney To Guam, but it has announced that, if it goes ahead, Tyco Telecommunications will build it.
Tyco Telecommunications has committed to a target ready for service date of end of Q4 2008. Pipe says this would allow it to interconnect and provision customers in Q1 2009 as previously released to market. The value of the deal was not disclosed.
More
here.
Politics as Usual: Need for Linguists Stymied by Cold War Procedures
Rowan Scarborough writes in The Examiner:
Minoo Krauser, of Gaithersburg, has two cousins living in her native Iran, a faraway family link that could be preventing her from getting a job at America’s secretive intelligence agencies.
Krauser has applied online to three agencies, figuring her Farsi fluency is her ticket to join the war on terrorism, in which language skills are highly prized.
Mike McConnell, the nation’s top intelligence officer, said last month his agencies need more linguists but are stymied by Cold War rules. Agencies, he said, still discriminate against applicants who have family abroad.
This may be the reason Krauser has been rebuffed. She has yet to hear an answer, or even get an interview, after filling out applications for the FBI, CIA and the National Security Agency.
More
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Wednesday, Aug. 8, 2007, at least 3,680 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,024 died as a result of hostile action, according to the military's numbers.
The AP count is eight more than the Defense Department's tally, last updated Wednesday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Toon: Old Dog, Bad Trick
Click for larger image.
Via TruthDig.com.
AT&T Censors Pearl Jam WebCast - UPDATE
 Pearl Jam
Pearl Jam:
Ma Bell seems to be acting like the big brother. Apparently, AT&T censored parts of Pearl Jam’s performance over the weekend. Rock band was performing as part of Lollapalooza. On their website, Pearl Jam writes:
During the performance of “Daughter” the following lyrics were sung to the tune of Pink Floyd’s “Another Brick in the Wall” but were cut from the webcast: - “George Bush, leave this world alone.” (the second time it was sung); and - “George Bush find yourself another home.”
They go on and say that this is more than just the censorship of a rock band. “What happened to us this weekend was a wake up call,” they write. AT&T blamed the censorship on an over aggressive content monitor.
Gigi B. Sohn, president and co-founder of Public Knowledge, dismissed that defense, and said it was “nothing short of appalling.”
More
here.
UPDATE: 15:02 PDT: More on this
here over at
IP & Democracy.
Cisco Publishes Quartet of Security Advisories

Link.
Banking Customers More and More Mistrustful of Financial Institutions
Nancy Feig writes on Bank Systems & Technology:
The growing ranks of banking customers are becoming more and more mistrustful of their financial institutions, according to IBM (Armonk, N.Y.). In a new twist on the issue, the trend is increasing in younger generations of consumers, IBM says, threatening banks' long-established position as trusted financial advisers.
Consumer mistrust of banks is a familiar topic. But typically the reports are from the standpoint of the so-called "unbanked" or "underbanked". Recent immigrants not familiar with their new country's established banking system or unfamiliar with the language, or much older people who can still recall the Great Depression, are recognized as often being mistrustful of established financial institutions. The trend identified by IBM, however, has less to do with language or preconceived emotions and much more to do with the performance of the banks themselves.
Concurrently, a new survey from Unisys (Blue Bell, Pa.) found that 71 percent of U.K. consumers do not trust their banks. The attributes most cited in the survey for eroding trust are disrespectful attitudes, poor privacy, weak IT (such as Web sites), poor corporate governance and a lack of investment in the local community.
More
here.
Congress Seeks Surveillance Documents
An AP newswire article by Laurie Kellman, via The Boston Globe, reports that:
Though Congress is on vacation, majority Democrats are keeping alive various fights with the White House with one common thread: Congress' access to administration documents and testimony to which President Bush has claimed executive privilege.
Smack in the middle of the August break, the White House faces a new deadline for producing subpoenaed information about the legal justification for the president's secretive eavesdropping program.
And aides in both chambers are considering a selection of ways to deal with Bush's refusal to let current and former advisers testify publicly about their roles in the firings of federal prosecutors. Contempt proceedings could begin in the House as early as September.
More
here.
Bush Prepares to Sign U.S. Tech Competitiveness Bill
George Leopold writes on EE Times:
President George Bush will sign legislation on Thursday (Aug. 9) designed to help the U.S. retain its "brainpower advantage."
Congress approved and sent to the White House last week (Aug. 2) the America Creating Opportunities to Meaningfully Promote Excellence in Technology, Education and Science (Competes) Act. The legislation is based on recommendations contained in a 2005 government report, "Rising Above the Gathering Storm."
The Competes Act also responds to industy lobbying for greater federal funding of basic research and bolstering support for science and engineering education.
Among other provisions, the legislation to be signed by the president will double research funding over the next three years for the National Science Foundation (NSF), National Institute of Standards and Technology and the U.S. Energy Department.
More
here.
ACLU Asks FISA Court to Release Orders That Led to 'Emergency' Wiretapping Legislation
Via ACLU.org.
In the first effort of its kind, the American Civil Liberties Union will today file legal papers with the Foreign Intelligence Surveillance Court (FISC) requesting that it disclose recent legal opinions discussing the scope of the government's authority to engage in secret wiretapping of Americans.
The ACLU initiated this action following Congress' passage this past weekend of the so-called "Protect America Act," a law that vastly expands the Bush administration's authority to conduct warrantless wiretapping of Americans' international phone calls and e-mails.
More
here.
U.S. Navy Chief to Geeks: Tech Doesn't Count
Noah Shachtman writes on Danger Room:
Navy Secretary Donald Winter has made a habit of telling military audiences exactly what they don’t want to hear. A few months back, he told a bunch of defense contractors that they were basically robbing the Pentagon blind. Now, he just told the 3,000 geeks gathered at the DARPATech conference in Anaheim that all their gee-whiz gadgetry may not help at all in the war on terror.
There’s a tendency to view Islamists as backwards barbarians, Winter said. This image is “misleading and very dangerous.” The terrorist enemy is more likely to be a “engineer in a lab” than an “evildoer in a cave.”
More
here.
New U.S. Military Regs on Information Assurance, COMSEC
Steven Aftergood writes on Secrecy News:
A newly updated U.S. Army regulation on information assurance defines standards and procedures for protecting classified and unclassified information in automated information systems. See "Information Assurance" [.pdf], AR 25-2, August 3, 2007.
Meanwhile, a new U.S. Navy Instruction establishes policy on monitoring of Navy communications for internal security purposes. See "Communications Security (COMSEC) Monitoring of Navy Telecommunications and Automated Information Systems (AIS)" [.pdf], OPNAV Instruction 2201.3A, August 2, 2007.
More
here.
Nearly 60% of 'gov.vn' Websites Attacked by Hackers
Via VietNamNet.
More and more computer networks of state agencies, enterprises, credit institutions have been attacked by hackers seeking profit, said a representative of the Government Commission for Code at an international workshop on information and network security held in HCM City recently.
According to surveys by this commission, nearly 60% of websites of ministries and state agencies which have the domain name gov.vn have been attacked by hackers.
Those attacks take place in many forms but the most popular form is attacking the archive system of Internet Service Providers (ISP) to delete information about service charges, steal information of enterprises, passwords of credit accounts, etc.
More
here.
(
Props, DomainNews.com.)
NSA Pushing Elliptic-Curve Cryptography
Kathleen Hickey writes on GCN.com:
The cryptographic security standards used in public-key infrastructures, RSA and Diffie-Hellman, were introduced in the 1970s. And although they haven’t been cracked, their time could be running out.
That’s one reason the National Security Agency wants to move to elliptic-curve cryptography (ECC) for cybersecurity by 2010, the year the National Institute of Standards and Technology plans to recommend all government agencies move to ECC, said Dickie George, technology director at NSA’s information assurance directorate.
Another reason is that current standards would have to continually extend their key lengths to ensure security, which increases processing time and could make it difficult to secure small devices. ECC can provide greater security with shorter keys, experts say.
The switch to ECC will be neither quick nor painless. It will require mass replacement of hardware and software to be compatible with ECC and new NSA cybersecurity standards.
More
here.
Pure Java™, Pure Evil™ Popups

Giorgio Maone writes on Hackademix.net:
Imagine you’re a web advertiser.
Imagine you can open a popup window from a web page defeating any popup blocker.
Imagine this popup can invade the whole desktop, full screen.
Imagine this popup has no title bar, no menus, no toolbar, no location bar, no border and no buttons. No mean to close it.
Imagine user can’t move or minimize this popup. It will go away only when the browser is killed or your show is done…
Now imagine you’re a phisher.
Imagine you can use this almighty popup to draw anything you want. A fake browser or — why not? — a whole fake desktop to collect user’s data.
Impossible wet dreams of clueless evildoers?
No, it’s just 100% Pure Java™ Reality.
More
here.
(
Props, /.)
You Can’t Patch an Election: Notable Quote
Avi Rubin:
Software is designed to be upgraded, and patch management systems are the norm. A certification system that requires freezing a version in stone is doomed to failure because of the inherent nature of software.
Since we cannot change the nature of software, the certification process for voting machines needs to be radically revamped. The dependence on software needs to be eliminated.
More here.
(Props, The Technology Liberation Front.)
Facebook - The CIA Conspiracy
Matt Greenop writes in The New Zealand Herald:
Facebook has 20 million users worldwide, is worth billions of dollars and, if internet sources are to be believed, was started by the CIA.
The social networking phenomenon started as a way of American college students to keep in touch. It is rapidly catching up with MySpace, and has left others like Bebo in its wake.
But there is a dark side to the success story that's been spreading across the blogosphere. A complex but riveting Big Brother-type conspiracy theory which links Facebook to the CIA and the US Department of Defence.
More
here.
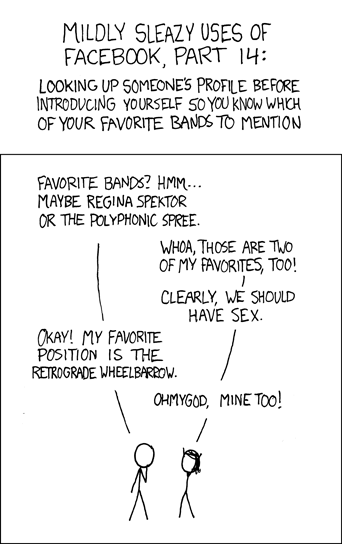
xkcd: Mildly Sleazy Uses Of FaceBook
Click for larger image.
We
love xkcd.
Off Beat: Microsoft Hires Former Miss Austrlia to 'Sex Up' IT Industry
 Former Miss Australia Erin McNaught
Former Miss Australia Erin McNaught
.
Microsoft is hiring a former Miss Australia to encourage young people to get involved in the computer industry.
Enrolments in IT courses plummetted worldwide following the crash of dot com bubble in 2001, and in New Zealand are still 30 per cent lower than they were in 2003, despite a booming local industry.
Microsoft and the Australian IT industry association hope Erin McNaught can turn this around in Australia by convincing teenagers IT careers were "chic", media reported.
More
here.
Image source: Fairfax Digital Media
Off Beat: Man Sneaks Small Monkey Onto Flight to New York
 A Pygmy Marmoset
A Pygmy Marmoset.
CBS 2 HD has learned a monkey was apparently snuck into the United States with a passenger from Peru and let loose during a Spirit Airlines flight that landed at LaGuardia Airport Tuesday afternoon.
Officials say the monkey, a pygmy marmoset, apparently belonged to a male passenger from Lima, Peru. He bought the animal off the streets in Lima.
The man then smuggled the animal, which measures only about a foot tall, through security in Peru onto a flight to Fort Lauderdale, Fla. He then got past security again when he took a connecting flight from there to New York City, and he even kept the monkey out in the open mid-flight.
Passengers of that flight say they noticed a small monkey clinging to the man's ponytail during the flight and reported it to authorities.
More
here.
Stiff Fines Prompt Amex to Bolster Money-Laundering Vigilance
Chris Preimesberger writes on eWeek:
American Express Bank International learned an expensive lesson when it agreed on Aug. 6 to pay a stiff penalty to the federal government after admitting that it failed to install and maintain anti-money-laundering software at its Miami office.
The bank, which has about $1 billion in assets, must fork over a whopping $65 million, including $55 million in restitution and $10 million in penalties to the Department of the Treasury, as a result of negligence in its banking and compliance practices.
A criminal information affidavit filed in U.S. District Court in Miami charged the bank with a single count of failing to maintain an effective anti-money-laundering program, and Amex decided not to fight the charge and to take the fine instead.
The investigation raises obvious questions about why the bank's executives failed to address the money-laundering problems earlier. The transgressions apparently had been happening for several years, according to the federal affidavit.
More
here.
Man Pleads Guilty to Stealing $1.5M in Credit from 225 People
Steve Visser writes in The Atlanta Journal-Constitution:
An Atlanta man has pled guilty to trying to become 225 people on paper so he could loot their bank account, buy on their credit and ruin their finances.
And what penalty did 27-year Sarp Yaman get for stealing documented credit lines of more than $1.5 million? Three years, six months in the federal penitentiary.
Bank robbers take note: it's often a whole lot less time if you engage in white-collar crime.
More
here.
(
Props, Pogo Was Right.)
The Pendulum Swings: Travelers From U.S. Face EU Crackdown
Tobias Buck and Demetri Sevastopulo write on FT.com:
US business travellers and tourists flying to the European Union are facing the threat of the same laborious registration requirements that Washington has demanded of Europeans in the latest US security crackdown.
In its first reaction to the new US visa law, the European Commission said it was “considering” a so-called electronic traveller authorisation scheme – similar to the American plan – that would require foreigners heading to the EU to give notice of their travel plans before departure.
More
here.
Big Brother in the Big Apple
Bob Barr writes in The Washington Times:
Even though officials in other cities are embracing and installing surveillance cameras in huge numbers — Chicago, Detroit and Washington, D.C., to name a few — the latest plan unveiled by Mr. Bloomberg and his equally surveillance-enamored police commissioner, Raymond Kelly, leaves these other American cities in the surveillance dust. Truly what we are witnessing being created here is a 21st-century Panopticon.
The Panopticon, as envisaged by British philosopher Jeremy Bentham (1748-1832), was a society (initially proposed as a prison) in which surreptitious surveillance of the citizenry was always possible and ever-known. Control was exercised not by being surveilled continuously but by each person knowing they might be under surveillance at any time, or all the time.
More
here.
(
Props, Flying Hamster.)
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Tuesday, Aug. 7, 2007, at least 3,679 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,020 died as a result of hostile action, according to the military's numbers.
The AP count is 11 more than the Defense Department's tally, last updated Tuesday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Phishers Now Targeting Domain Registrars
Edward Falk writes on CircleID:
This is an issue of some concern and should be watched carefully: phishers are now trying to get passwords of domain registrants (domain owners). Currently, correspondents inform me that GoDaddy is the target, but there’s no reason to think the phishers won’t expand to other registrars.
Normally, phishers go after bank accounts or other financial information, or sometimes the online accounts of users so that they may send spam.
More
here.
Hackers Dscover How to Download Streaming Movies From Netflix
Brad Linder writes on TV Squad:
Earlier this year Netflix announced a new service that would allow you to watch a limited number of videos online instead of waiting for the DVDs to come in the mail. The service is free with your regular subscription. If you pay $17/month for access to 3 DVDs at a time, you can watch 17 hours of video per month. If you pay $5 per month for access to 2 DVDs per month, you can watch 5 hours of video online.
There's just one problem. You have to watch on Netflix's terms. The video player is browser based, and the movies are encoded using Windows Media DRM. If you want to begin a movie now and finish it later, you're out of luck. Or if you want to copy it to a portable device for viewing during your morning commute (on the train, not while driving, of course!), no soup for you.
Well, the smart folks over at the Rorta forums seem to have cracked the code, using Internet Explorer, Windows Media Player 11, FairUse4WM, and Notepad. The solution involves finding the URL of the video file, downloading it, acquiring the license key and then stripping the DRM. It's a bit involved, and will probably take longer than just sitting down and watching the movie. But hey, it's the principle of the thing, right?
More
here.
(
Props, Consumerist.)
Global Network Security Forecast: Not So Sunny and Bright
Allan Holmes writes on GovExec Tech Insider Blog:
The United States, as well as any other nation hooked into the Internet, is losing the battle against cyberthieves and hackers looking to commit crimes and steal sensitive, and possibly classified, information from networks. And it doesn't look like we will be able to improve the situation much in the near future.
That sobering assessment comes from cybersecurity expert Seymour Goodman, who was in Washington, D.C., yesterday to give a talk on securing the Internet at the Hudson Institute. Goodman, a professor of international affairs and computing at the College of Computing at Georgia Tech, was frank about the extremely difficult path nations face in trying to secure the Internet. In fact he was downright apologetic.
More
here.
Off Beat: Airlines Sue FBI and CIA to Demand 9/11 Interviews
An AP newswire article by Larry Nuemeister, via The Detroit Free Press, reports that:
Airlines and aviation-related companies sued the CIA and the FBI on today, asking a federal court to let them interview investigators who can tell whether the aviation industry was to blame for the Sept. 11 terrorist attacks or whether it had acted reasonably.
The separate lawsuits in U.S. District Court in Manhattan asked a judge to order the government to let the aviation companies gather the information as part of their defense against lawsuits brought by victims or families of victims of the 2001 attacks.
In the CIA lawsuit, companies including American Airlines Inc., United Airlines Inc., US Airways Group Inc., Delta Air Lines Inc., Continental Airlines Inc. and The Boeing Co. asked to interview the deputy chief of the CIA’s Osama bin Laden unit in 2001 and an FBI special agent assigned to the unit at that time.
In the FBI lawsuit, the companies asked to interview a “limited number of former and current FBI employees” who had participated in investigations of Al Qaeda and Al Qaeda operatives before and after Sept. 11, 2001.
Government spokeswoman Yusill Scribner said she had no immediate comment on the lawsuits.
More
here.
The Onion: The Man of the Street on the 'Protect America Act'
 Click for larger image.
Click for larger image.Right on, there, Mr. Albaugh.
Link.
Checks? Balances? Same Agencies to Run, Oversee Surveillance Program
Walter Pincus writes in The Washington Post:
The Bush administration plans to leave oversight of its expanded foreign eavesdropping program to the same government officials who supervise the surveillance activities and to the intelligence personnel who carry them out, senior government officials said yesterday.
The law, which permits intercepting Americans' calls and e-mails without a warrant if the communications involve overseas transmission, gives Director of National Intelligence Mike McConnell and Attorney General Alberto R. Gonzales responsibility for creating the broad procedures determining whose telephone calls and e-mails are collected. It also gives McConnell and Gonzales the role of assessing compliance with those procedures.
The law, signed Sunday by President Bush after being pushed through the Senate and House over the weekend, does not contain provisions for outside oversight -- unlike an earlier House measure that called for audits every 60 days by the Justice Department's inspector general.
More
here.
Note: Also, take a moment to read
this article over at
Slate.com by Patrick R. Keefe, and
this editorial today in
The New York Times entitled "
The Fear of Fear Itself".
Merrill Lynch ID Theft May Affect 33,000 Employees
Via CNBC.com.
A "major identity-theft incident" has occurred at brokerage giant Merrill Lynch that may affect more than 30,000 employees, CNBC's Charlie Gasparino reported.
"A computer device apparently was stolen from [Merrill's] corporate offices in New Jersey," Gasparino said.
According to sources, the device contained sensitive personal information, including Social Security numbers, about some 33,000 employees of the financial firm.
The incident allegedly occurred approximately two weeks ago, but Merrill Lynch is "only today getting around to telling people," Gasparino said.
More
here.
(Props, Data Loss mailing list.)
U.S. Firm Says Outsourcer Holding Its Data Hostage Offshore
Paul McDougall writes on InformationWeek:
A provider of spend management services says one of India's largest outsourcers is holding its data hostage at an offshore location and is refusing to return the information unless legal claims against it are dropped.
New York City-based The Buying Triangle also says that Infosys, through a subsidiary, exposed its customer data online and stole its business plans.
More
here.
Quote of the Day: Eugene Robinson
"What if someone had predicted 50 years ago that someday all this once-private information would be captured and stored? Psychiatrists would have issued a quick and definitive diagnosis: paranoia."
- Eugene Robinson
ATS: DHS Reduces Traveler Data Retention Time From 40 Years to 15
Alice Lipowicz writes on Washington Technology:
In response to more than 600 public comments, the Homeland Security Department has shortened the amount of time that it will retain data and made other changes to its Automated Targeting System.
Under the ATS, information on cargo destined to arrive in the United States, and on incoming U.S. and foreign travelers, is assessed against several terrorist threat databases to determine whether additional security checks are needed.
Formerly, the incoming passenger personal information in the system was to be held for 40 years, but now that time has been reduced to 15 years, the DHS said.
More
here.
NOTE: Given the
breadth & scope of the data that is collected, I'm not really sure that a reduction in the time the data is held really means anything substantial.
- ferg
Estonian Cyber-War Highlights Civilian Vulnerabilities
Gadi Evron guest writes in eWeek:
The online attacks against Estonia are being referred to as the first Internet war. If this "war" is anything to go by, simple folk such as you and I may end up as the weak links in our country's defense.
Indeed, the attack's impact was not what we might have expected: It was the civilian infrastructure used by banks, ISPs and home users—not the military's—that was under siege.
The Estonian incident is not the first of its kind. Whenever political tensions manifest between different ethnic groups or countries, the aftermath can be seen online shortly thereafter. Often, this involves attacks by groups of hackers who are sympathetic to one side but have no official affiliation with it.
More
here.
Mozilla Foundation Releases Browser Fuzzing Tool
Via heise Security Online.
The Mozilla Foundation has released three tools that enable developers and users to test their browsers for vulnerabilities that can be exploited while browsing. They are specifically aimed at assisting those users who regularly download and test the nightly builds - the latest (possible unstable) development versions - in searching for bugs.
The Mozilla Foundation is hoping to achieve a better level of security for their browser through feedback from the Mozilla community. The tools were originally conceived for Firefox and Mozilla only. However the developer, Jesse Rudermann, also wants to make them available to other browser producers.
The jsparsefuzz.js fuzzing tool attempts to crash the browser by generating buggy JavaScript code. This should allow potential security vulnerabilities to be detected at an early stage.
More
here.