U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Saturday, Feb. 17, 2007, at least 3,135 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,514 died as a result of hostile action, according to the military's numbers.
The AP count is eight higher than the Defense Department's tally, last updated Friday at 10 a.m. EST.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Toon of the Day: Riding Roughshod
Click for larger image.
At MIT, A War on Pranks?
Elizabeth Weiss Green writes on U.S. News & World Report:
Last October, police discovered three Massachusetts Institute of Technology students in the kitchen of the school's faculty club, just in front of a crawl space, in possession of metal tools. "None of them could give me a legitimate reason for being in the Faculty Club Kitchen," an officer wrote in the subsequent police report, according to the Boston Globe. Students say the reason was obvious: They were "hacking," the MIT tradition responsible for pranks like putting a fire truck on the roof of a building and transforming a regular lobby into a cathedral.
In the past, the university turned a blind eye, handing out minimal punishments like fines or community service, but now the students caught trespassing in the faculty club face criminal charges and up to 20 years in prison, according to the Globe. Students worry it's a "war on hacking," but police say hacking has nothing to do with it. Their response, according to the Tech : "How do we know a hacker from a thief?"
More
here.
AOL CFO To Leave As Layoffs Continue
Sara Kehaulani Goo writes in The Washington Post:
AOL said yesterday that its chief financial officer, Stephen Swad, plans to leave the firm for a position at a private-equity firm.
In an e-mail memo to employees, AOL chief executive Randy Falco said Swad was "ready for new and different challenges" after four years at the Dulles company. AOL declined to name Swad's new employer. Falco said in the memo that AOL planned to name a replacement for Swad soon.
More
here.
Judge Nixes RIAA-Kazaa Details
Via p2pnet News.
Last year Ray Beckerman, the New York lawyer representing a number of RIAA sue 'em all victims, made it known Warner Music, EMI, Vivendi Universal and Sony BMG were using Kazaa, the former bête noire of the corporate music industry, to get songs they wanted to promote to radio stations.
But the Big 4's RIAA (Recording Industry Association of America) doesn't have to go into detail about how that was, or still is, achieved, judge Robert M. Levy has ruled, says Beckerman on Recording Industry vs The People.
Kazaa, owned by Australia's Sharmnan Networks, shows up in the majority of the Big 4 file sharing cases and has consequently become the defendant in a class action brought by Catherine Lewan, an ex-user sued by the Big Four's RIAA.
More
here.
Microsoft Patents Telling You If A Website Is On A List Of Phishing Sites?
Mike Masnick writes on techdirt.com:
It seems that every few days when new patents are announced there are a few gems awarded to Microsoft. Take, for example, Microsoft's latest patent on Phishing Detection, Prevention, and Notification.
If they truly came up with an innovative way to stop phishing attacks, that would be interesting. Instead, it appears that the patent is for looking at the URLs found in an email or visited by a website, comparing them to a known list of phishing sites -- and then alerting you that the link might be fraudulent.
More
here.
Imperfect Storm Aids Spammers
Robert Lemos writes on SecurityFocus:
For 24 hours in mid-January, stock-fraud investigation site StockPatrol disappeared from the Internet, overwhelmed by a massive flood of Web requests coming from thousands of sources.
The attack came after the site wrote a handful of reports investigating and condemning the practice of pump-and-dump stock spam campaigns. No fewer than three bot nets targeted StockPatrol as well as another anti-spam site and at least five command-and-control servers associated with a different virus, Warezov, according to an analysis released last week.
"StockPatrol.com was the victim of a cyberspace assault that evidently was calculated to disable our site and make our reports inaccessible," read a statement posted on January 17. "In this instance the attack was massive."
At the heart of the attack was a single program designed specifically to co-opt victims' computers to aid in sending stock-touting e-mail messages and to participate in denial-of-service attacks--Storm Worm.
More
here.
VA Ends Projects After Data Breach
An AP newswire article by Ben Evans, via The Boston Globe, reports that:
Veterans Affairs Secretary Jim Nicholson has stopped activities at seven specialized research centers across the country after an unprotected computer hard drive disappeared from one of the facilities in Alabama last month.
In an internal memo obtained by The Associated Press, Nicholson called the department's latest data breach "tragic" and ordered the VA's Research Enhancement Award Programs to shut down until they are certified as meeting security standards.
The research centers focus on studies involving large amounts of data. The center in Birmingham, called the Deep South Center on Effectiveness, collects data for improving quality of care.
Writing to VA's top management on Thursday, Nicholson also said the department would begin unannounced inspections at VA sites nationwide.
More
here.
U.S. Warns About Dangerous Internet Drug Mistake
A Reuters newswire article, via USA Today, reports that:
A drug used to treat schizophrenia was mailed to some consumers who had ordered other medications via the Internet, and several users had to seek emergency treatment because they could not breathe, U.S. health officials said Friday.
The Food and Drug Administration said that instead of receiving the products they ordered, some consumers were sent the prescription drug haloperidol. Several patients had to seek emergency care after taking the pills, the agency said without citing a specific number.
More
here.
Some PayPal Users Plagued by Security Warnings, Log-In Woes
Jaikumar Vijayan writes on ComputerWorld:
Some visitors to PayPal's Web site may be getting unexpected security warnings and log-in problems when they attempt to access the site or their accounts, a spokesman confirmed today.
The problems appear to be connected to an SSL security certificate used by Omniture Inc., a company PayPal is using to collect aggregate data about people using its Web site, the PayPal spokesman said. SSL certificates are used by Web browsers, such as Internet Explorer and Firefox, to check the authenticity of a site and to let users know whether a site is spoofed or not. The spokesman said the problem affects a "small portion" of PayPal users.
More
here.
Follow-Up: TSA Removes Online Traveler Redress System
Ryan Singel writes on 27B Stroke 6:
The Transportation Security Agency has removed from its website an online system designed for travelers who have been told they are on a watchlist and inserted a statement that the agency takes information security seriously, following reporting by 27B (and others) that the site could put travelers at risk of identity theft and looked like online fraud.
A link on the TSA's "Our Travelers" page earlier this week directed people who wanted to get help from the Traveler Identity Verification program to a page that looked like the TSA website but was actually a subdomain hosted by a web design company with a P.O. Box for an address (see previous link for screenshot). The site, which was full of misspellings and nonsensical directions, asked travelers to provide sensitive personal information via an unencrypted page.
More
here.
Who's The Boss of $1B DHS Interoperability Fund?
Alice Lipowicz writes on GCN.com:
The Homeland Security Department has no clear authority at this time over a $1 billion fund for public safety agency interoperable communications equipment that it has been publicizing as a first responder grant program, according to a Congressional Research Service memorandum.
The Feb. 12 memo was addressed to Rep. Carolyn Maloney, D-N.Y., in response to her request for further information about the fund. DHS said in a Feb. 5 fact sheet released with its fiscal 2008 budget request that it will be co-administering the interoperability grants program with the Commerce Department.
However, according to the CRS memorandum, the department’s authority over the $1 billion fund is not yet established. The funding is to be administered by the National Telecommunications and Information Administration, and no memorandum of understanding exists at this time between DHS and the NTIA on administration of the program, CRS said.
More
here.
Judge Limits New York Police Surveillance Taping
Jim Dwyer writes in The New York Times:
In a rebuke of a surveillance practice greatly expanded by the New York Police Department after the Sept. 11 attacks, a federal judge ruled yesterday that the police must stop the routine videotaping of people at public gatherings unless there is an indication that unlawful activity may occur.
Four years ago, at the request of the city, the same judge, Charles S. Haight Jr., gave the police greater authority to investigate political, social and religious groups.
In yesterday’s ruling, Judge Haight, of United States District Court in Manhattan, found that by videotaping people who were exercising their right to free speech and breaking no laws, the Police Department had ignored the milder limits he had imposed on it in 2003.
More
here.
DirectRevenue to Pay Back 'Spyware' Gains
Roy Mark writes on internetnews.com:
Adware distributor DirectRevenue today settled Federal Trade Commission (FTC) charges of unfair and deceptive trade practices of installing unwanted and unsolicited spyware unto consumers' computers.
DirectRevenue, which is also entangled in a spyware lawsuit filed by New York State, agreed to not download its adware without consumers' consent and to provide effective means for removing DirectRevenue's software from their computers. It also requires that DirectRevenue monitor its affiliates to ensure that they and their sub-affiliates comply with the FTC order.
In addition, the New York-based company agreed to pay $1.5 million for "ill-gotten gains," a financial settlement that prompted FTC Commissioner Jon Leibowitz to vote against the deal.
More
here.
U.S. 'Threatened' Alleged NASA Hacker, McKinnon Defense Says
Colin Barker writes on C|Net News:
The fate of Gary McKinnon, the alleged NASA hacker, is hanging in balance after his appeal against extradition to the U.S. was adjourned at the Court of Appeal in London on Wednesday evening.
Over two days in court, McKinnon's defense team presented new evidence that it said meant the judges should reject his extradition to face charges of breaking into and damaging U.S. government computers.
The Court of Appeal is the court of last resort under U.K. law, and usually it will only find for or against the appellant. But the defense argued on Tuesday and Wednesday that evidence brought to light by the McKinnon case raised serious questions about the U.S. government's case.
More
here.
Alleged School Bomb Plot Foiled by YouTube Video
An AP newswire article by Dave Collins, via ABC News, reports that:
A 16-year-old high school junior has been charged with making bombs in a plan to target classmates in his school, a plot uncovered after a video was discovered on the Internet, police said.
Frank Fechteler, who attended Newington High School, was charged late Wednesday and ordered held in lieu of $500,000 bail, state prosecutors said. He was arraigned Thursday in juvenile court.
Police said they seized weapons from Fechteler's home in Newington after receiving a tip from a parent about the attack plan.
The plot was foiled when a teen who knows the suspect sent a link to an Internet video on YouTube.com to a person who did not know Fechteler, police said. The video showed area high school students firing weapons and igniting explosives, but it was unclear Thursday who had made the video.
More
here.
Gang Arrested on Suspicion of $300k Internet Bank Theft
Fiona Raisbeck writes on SC Magazine Online:
Police in the Turkish city of Izmir have arrested 17 members of a gang who allegedly hacked into internet banking accounts and stole $300,000 (£154,000) from online users.
The men are accused of collaborating with three Russian cyber criminals, who are believed to have provided them with the banking usernames and passwords stolen from the computers they infected with spyware, Turkish authorities claim.
The Russian hackers allegedly sold the banking login details of thousands of Turkish online customers for ten per cent of the money stolen by the gang, according to police.
The authorities closed in on the group after hundreds of people started to complain about suspicious withdrawals from their online bank accounts in January.
More
here.
Quote of the Day: Bruce Schneier
"It's almost too absurd to even write about seriously..."
- Bruce Schneier, writing that the plan a proposed airplane Onboard Threat Detection System, which describes "..cameras fitted to seat-backs will record every twitch, blink, facial expression or suspicious movement before sending the data to onboard software which will check it against individual passenger profiles."
Picture of the Day: My Grandson
 My grandson, Preston Ferguson
My grandson, Preston Ferguson
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Thursday, Feb. 15, 2007, at least 3,133 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,513 died as a result of hostile action, according to the military's numbers.
The AP count is seven higher than the Defense Department's tally, last updated Thursday at 10 a.m. EST.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Picture of the Day: Alabama Special
 Image source: Boing Boing
Image source: Boing BoingThis is astoundingly retarded. Congratulations, Alabama.
Via Boing Boing (
Props, Violet Blue).
In a unanimous opinion, a three-judge panel for the 11th U.S. Circuit Court of Appeals upheld an Alabama statute banning the commercial distribution of sex toys, saying that there is no fundamental right to privacy raised by the plaintiff's case against the law.
According to the statute, it is 'unlawful for any person to knowingly distribute any obscene material or any device designed or marketed as useful primarily for the stimulation of human genital organs.'
More
here.
TSA Wants 2,000 More ID Checkers
Michael Hampton writes on Homeland Stupidity:
The Transportation Security Administration wants to hire 1,300 people, and divert 700 more from actual airport screening duties, to look for fake IDs.
Pitching the idea before Congress on Tuesday, TSA head Kip Hawley asked for $60 million in new funding for fiscal 2008, to pay these screeners to do nothing but check identification against boarding passes and detect fake IDs.
And you’ll never guess who’s been trying to get through airport security with fake IDs. I’ll give you a hint: it isn’t the terrorists.
More
here.
FTC Asks Court to Stop Pretexters
Robert McMillan writes on InfoWorld:
The U.S. Federal Trade Commission has asked a federal court to make two Florida companies stop telephone pretexting and to pay back victims of the practice.
One of the companies, Action Research Group, has been linked in press reports to last year's Hewlett-Packard pretexting scandal, which led to the resignation of HP Chairman Patricia Dunn last September. The second company, Eye in the Sky Investigations, has "performed services" for Action Research Group, the complaint said. Eye in the Sky also was called to testify before a congressional investigation into the matter.
In a complaint filed Wednesday in U.S. District Court in Orlando, the FTC claims that the practice of pretexting violates the U.S. Telecommunications Act of 1996.
More
here.
Older Version of Skype Tracked Computer Data of Subscribers
An AP newswire article by Rachel Konrad, via The Mercury News, reports that:
A program used by eBay Inc.'s Skype Internet phone service collected identifying information from users' computers running an advanced version of Microsoft's Windows operating system, the software's developer said.
Although executives said the data were never used for nefarious purposes and the program has been updated, some critics said the problem could have been serious.
It stemmed from a program developed by Norway-based EasyBits Software for Skype, which allows more than 170 million subscribers to place free long-distance calls to other users over the Internet.
An older version of EasyBits - when running a Windows PC with the 64-bit version of Windows - collected the serial number of the PC's main circuit board and settings stored in the PC's BIOS, which contains code for controlling keyboard, display, disk drives and other important functions.
More
here.
City College of San Francisco: ID Theft Alert for 11,000 Students
Via CCSF.edu.
On Tuesday, February 6, 2007 City College of San Francisco’s (CCSF) Information Technology Department learned that a computer file created in May 2000, containing the names, addresses and social security numbers of approximately eleven thousand students was potentially viewable via the Internet. The file did not include any driver’s license numbers, credit card or banking information. The College took immediate steps to remove the file and ensure that it could no longer be viewed.
The file in question was used in 2000 for providing students that attended in Summer 1999 their grades. You should know that since June 2002, the College stopped using social security numbers as unique identifiers for students and switched to student identification numbers. All grades issued since 2002 are connected to student identification numbers and do not involve the use of social security numbers.
More
here.
(
Props, Pogo Was Right.)
UK: Hackers Target Banking Executives Home Computers
Via The Guardian.co.uk.
One of the UK's leading banks has been forced to admit that organised hacking gangs have been targeting its executives. For the past year, Royal Bank of Scotland has been fighting systematic attempts to break into its computer systems from hackers who have sent personalised emails containing keyloggers to its senior management. This has included executives up to board level and is now the subject of a separate investigation by the Serious and Organised Crime Agency.
The hackers are homing in on the trend for people to work from home. The hackers make the assumption that the computers being used outside the work environment are more vulnerable than those protected by a corporate IT department.
More
here.
Massive Insider 'Industrial Espionage' Breach At DuPont
Larry Greenemeier writes on InformationWeek:
The Delaware U.S. Attorney on Thursday revealed a massive insider data breach at chemicals company DuPont where a former scientist late last year pled guilty to trying to steal $400 million worth of company trade secrets and now faces up to a decade in prison, a fine of $250,000, and restitution when sentenced in March.
Gary Min worked as a research chemist for DuPont for 10 years before accepting a job with DuPont competitor Victrex PLC in Asia in October, 2005. Between August and December of that year, Min downloaded 22,000 sensitive documents and viewed 16,706 more in the company's electronic library, making him the most active user of that database in the company, according to prosecutors.
It's unclear whether Min's frequent access to that database tipped off an automatic alert to DuPont officials or whether his behavior was discovered by studying database access logs. Regardless, Min left DuPont on Feb. 3, 2006, and transferred 180 DuPont documents to a Victrex-owned laptop computer.
More
here.
'Save Our Selves' - Al Gore Plans to Rock Against Global Warming

Via MSNBC.
Al Gore, the former vice president and now hit documentary maker, on Thursday added rock promoter to his resume, announcing plans for a 24-hour concert series on all seven continents to highlight, you guessed it, the dangers of global warming.
With a powerhouse lineup of acts from the Red Hot Chili Peppers to Snoop Dogg to Bon Jovi, what's being called "Live Earth" aims to gather more than 100 of the world's top musicians on July 7 — and attract 2 billion viewers, most of them via television, radio and the Web.
More
here.
The Three Principle Types of Phishers
A good summation of the types of phishers by RSnake over at ha.ckers.org.
Romanians/Eastern Europeans: They tend to be the most skilled of the bunch. They think about scalability and they run their activities like a business. They use modern exploits, and tend to come up with most of the cutting edge scams. They tend to be on the bleeding edge of new issues, and tend to tie in things like malware, pharming, and server exploits. They tend to be the ones creating the phishing kits. Like the others they have strong ties to organized crime, and have actually resorted to kidnapping and (presumed) killing of at least one government official. Due to their technical nature they are highly scalable even though there are probably fewer in numbers. They require the most hardware, and are assumed to have ties with lots of botnets.
Chinese/Asians: They tend to be copy-cats. They watch what the other groups do and mimic the same tactics, only months or years later. What they lack in innovation of exploits they make up for in volume and brute force attacks. They are relative newcomers to the world of phishing in comparison but they are growing rapidly.
Nigerians/North West Africans: They tend to have the lowest sophistication of the three groups, and primarily focus on ways of coming up with new variants of 419 scams. They tend to use people instead of automation and focus only on high dollar scams. They are most likely to make contact with the victim and actually will resort to strong arm tactics if they find out where you live.
More
here.
Quebec Health Officials Fighting Computer Virus
Charlie Fidelman writes in The Montreal Gazette:
Quebec health officials are battling a fast-spreading virus that struck its entire computer network system late Tuesday.
The virus ripped through computers at most health-care institutions, affecting hospitals, CLSCs and nursing homes’ administrative activities So far, it’s caused a province-wide slowdown and some fear that patients’ files may have been damaged, too.
But government officials say patients’ privacy has not been compromised and confidential information remains confidential.
The extent of the damage is not yet known, Isabelle Merizzi, press attache to Health Minister Philippe Couillard said Wednesday.
More
here.
(
Props, Flying Hamster.)
Offering Data Breach Victims A Solution They Can’t Have
Via The McAfee Security Insights Blog.
Sometimes trying to comply with all of the various laws out there gets a bit ridiculous. Emergent Chaos has a blog post about how Sprint had to send a disclosure letter to a bunch of customers in New York after a laptop containing personal info of customers was stolen.
They were doing so to comply with New York’s data breach law. The letter noted that Sprint was offering these customers a free year of credit monitoring — which has become pretty standard these days for companies that lose customer date. There’s just one problem.
The letter also notes that, due to a New York law forbidding it... the free credit monitoring isn’t available to customers in New York.
More
here.
Citibank Korea Customer Data Hacked, Purchases Made
Via Maeil Business.
Personal data on the Citibank e-payment system, used for e-commerce, has been hacked, allowing illegal transactions on bank users' credit cards.
According to the banking industry, 20 credit cards issued by Citibank of Korea have been illegally settled from Feb. 1 to 6, worth 50 million won [USD $53,504].
Citibank Korea has requested an investigation from the National Policy Agency's Cyber Terror Center after finding the company's e-payment system was hacked to garner dates on the customers' credit card information and passwords in order to make charges.
Hackers targeted under-300,000 won [USD $321] financial transactions of companies with weak e-payment security.
That method was used, as below-300,000 won financial transactions can be made by inserting basic personal information, such as credit card numbers and passwords without official certificates.
"Unlike other banks, Citibank has omitted the process of inserting the Card Validation Code (CVC) when executing e-payments, allowing the culprits to take illegal actions," said an official from the Financial Supervisory Service (FSS).
More
here.
(
Props, Pogo Was Right.)
Report: Kaiser Computer Glitches May Harm Patients
Via CBS5.com.
Repeated technical problems have hampered Kaiser Permanente's $4-billion effort to computerize medical records and has lead to potentially dangerous incidents involving patients, according to a published report citing hospital documents and current and former employees.
Kaiser officials acknowledge the digital effort, called Health Connect, has had technical challenges, but say those have been resolved and patients should feel safe getting care at any Kaiser facility, the Los Angeles Times reported Thursday.
Kaiser's effort, one of the largest and most ambitious electronic medical records projects in the country, is seen as a possible national model. President Bush is pushing for every American to have an electronic medical record by 2014.
The documents obtained by the newspaper show that at times, doctors and medical staff haven't had access to crucial patient information and system outages have led to delays in emergency room care.
More
here.
Microsoft Piracy Case Against Teacher Collapses in Russia
Via The BBC.
A Russian court has thrown out a criminal case against a rural headteacher accused of using pirated Microsoft software in his school.
The court in Perm, some 1000km (620 miles) east of Moscow, dismissed the case of Alexander Ponosov as "trivial".
The trial was seen as a response by the authorities to international pressure to crack down on piracy in Russia.
More
here.
Iowa Department of Education Records Hacked
Darwin Danielson writes on Radio Iowa:
The Department of Education is warning Iowans that someone gained access to personal information in records that were in what was supposed to be a protected area on the department's website. Department spokesperson, Elaine Watkins-Miller, says the records contained names, addresses, dates of birth and social security numbers of individuals who obtained a G.E.D. from Iowa between 1965 and 2002.
Watkins-Miller says they want people to be aware of this and have information on their website at: www.iowa.gov/educate so they can take action and check their credit report. Watkins says the credit report can help you determine if your information is being used illegally.
Watkins-Miller says you should keep an eye on the credit report, and call local law officers if you see any unusual activity. Watkins says they believe someone hacked into the records on Sunday. Watkins-Miller says they can't say how the records were access and that's being investigated by the DCI and the FBI. There were some 160-thousand records in the file, but she says it's believe only about 600 may have been viewed.
More
here.
(
Props, Pogo Was Right.)
California Muslim Organization's Website Hacked, Defaced
An AP newswire article, via North County Times, reports that:
The FBI said Wednesday it was investigating hate speech posted by a hacker on the Web site of a prominent Southern California Muslim organization.
A hacker accessed the Web site of the Islamic Shura Council of Southern California sometime Tuesday and posted an expletive-laced message against Muslims, said Shakeel Syed, the council's executive director. The site remained down Wednesday but could be back up within 24 hours, he said.
Syed said the posting was one of a number of hate messages the council and its affiliated mosques have received in recent months. He said he has received 11 anti-Muslim e-mails or phone calls since last year, including a phone message three weeks ago.
Laura Eimiller, a spokeswoman for the FBI, confirmed that the agency was investigating the Web site incident, but declined to comment further.
More
here.
Cisco, Apple Still in iPhone Talks - Deadline Thursday
Sarah Jane Tribble writes in The Mercury News:
Will it be an iPhone romance or an ugly corporate trademark battle between Silicon Valley heavyweights?
San Jose's Cisco Systems has given Apple until Thursday to respond to a trademark lawsuit filed last month over the "iPhone" moniker, according to a federal court documents.
More
here.
Off Topic: Stephen Colbert's Americone Dream
 Image source: Associated Press
Image source: Associated PressAn AP newswire
article, via
Yahoo! News, reports that:
Stephen Colbert may have no taste for the truth, but he does have a sweet tooth. Ben & Jerry's has named a new ice cream in honor of the comedian: "Stephen Colbert's Americone Dream."
It's vanilla ice cream with fudge-covered waffle cone pieces and caramel.
Announcing the new flavor Wednesday, Ben & Jerry's called it: "The sweet taste of liberty in your mouth."
More
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Wednesday, Feb. 14, 2007, at least 3,132 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,512 died as a result of hostile action, according to the military's numbers.
The AP count is seven higher than the Defense Department's tally, last updated Wednesday at 10 a.m. EST.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
MySpace Teen Suit Dismissed by Texas Court
Via Reuters.
News Corp.'s MySpace said on Wednesday a federal court dismissed a negligence lawsuit filed by the family of a teenage girl who was a victim of an adult sex predator she met on the popular Internet social network.
Judge Sam Sparks of the U.S. District Court for the Western district of Texas granted MySpace's motion to dismiss charges for negligence and fraud and negligent misrepresentation.
MySpace separately faces several other lawsuits filed by families of teenage girl victims of predators on the service.
More
here.
Local: Laptop Stolen With 22,000 Kaiser Patients' Data
Via CBS5.com.
In yet another instance of laptop theft potentially endangering personal data, Kaiser Permanente is in the process of notifying as many as 22,000 patients of a possible breach of their private medical information.
The personal information was located on a doctor's laptop computer stolen from the Medical Center in Oakland at the end of last November.
There were no details provided about where or how the laptop was taken, but a Kaiser spokesman said it was likely a random and isolated crime of opportunity.
Kaiser said the majority of patients had only limited information listed on the laptop, but 500 of them included social security numbers.
More
here.
The Mystery of the Missing 'L'

Ryan Blitstein writes in The Mercury News:
Would a Google by any other name search as sweet? That's what visitors to Google.com might have asked themselves Wednesday morning, after the Mountain View search giant posted a puzzling holiday "Google Doodle" logo on its home page.
The doodle, which substituted a mouthwatering chocolate-covered strawberry for the second 'G' in the company moniker, was meant to celebrate Valentine's Day. Instead, the logo touched off a firestorm of blogger commentary that the $10 billion company had forgotten how to spell its own name. What appeared on the page seemed to read: "Googe."
More
here.
For what its worth, my girlfriend Lori has her own theory. She says "'L' is for 'Love' and there's no love at Google." Go, girl. :-)
Toon of the Day: Be Mine, Valentine
Click for larger image.
Dutch Botnet Hacker Appeals Jail Sentence
A WebWereld Netherlands article by Edwin Feldmannm, via PC World, reports that:
The leader of a gang that committed what has been described as the Netherland's biggest cybercrime is appealing his sentence.
The man, a 20 year old from Loon op Zand who has not been named, was sentenced on Jan. 30 to two years in prison and a €9,000 (US$11,691) fine. Prosecutors had been seeking three years imprisonment and a €30,000 fine.
The second hacker, a 28-year-old man from Rijswijk, was given 18 months in prison and fined €4,000. He did not appeal his sentence.
Because one of the men is appealing, the prosecutor also appealed the sentence on Tuesday. "The penalty they were given is a little less then we had asked for. That's why we want to try and raise the jail term," said Desiree Leppens, spokeswoman for the National Public Prosecution Service in Rotterdam.
The two men were found guilty of writing the Toxbot and Wayphisher viruses. They used the Toxbot virus to infect millions of computers in 2005. The virus included a key logger that provided the hackers with user names and passwords of eBay and PayPal accounts, as well as some personal credit-card information. The card information was used to buy equipment including PlayStations consoles, iPods and digital cameras, as well as luxury goods such as Prada shoes.
More
here.
Europe: Proposed Legislation Called a Threat to Internet Users Privacy
Victoria Shannon writes in The International Herald Tribune:
European governments are preparing legislation to force companies to keep detailed data about people's Internet and phone use that goes beyond what the countries will be required to do under a European Union directive.
In Germany, a proposal from the Ministry of Justice would essentially prohibit using fake information to create an e-mail account, making the standard Internet practice of creating pseudonymous accounts illegal.
A draft law in the Netherlands would likewise go further than the EU requires, in this case by mandating phone companies to save records of exactly where someone is during an entire mobile phone conversation.
Even now, Internet service providers in Europe divulge customer information — which they normally keep on hand for about three months, for billing purposes — to police officials with legally valid orders on a "routine" basis, a privacy expert said. The data concern how the communication was sent and by whom but not its content.
More
here.
FBI Taps Raytheon for Info-Sharing System
Wilson P. Dizard III writes on GCN.com:
The FBI has awarded a contract to the Raytheon Co. of Waltham, Mass., to build out the National Data Exchange (N-Dex) law enforcement information-sharing system, sources said.
According to a bureau official, FBI systems specialists expect to meet with their Raytheon counterparts within the next two weeks to plan the IT work leading up to the N-Dex system rollout.
N-Dex uses advanced information sharing that harmonizes data entered into various types of law enforcement systems for common search, acquisition and analysis. N-Dex acts as a counterpart to R-Dex, a regional data exchange system that provides a "pointer" to the location of specific information held by other law enforcement agencies.
Technical descriptions of the N-Dex project emphasize its use of standards such as the Global Justice XML Data Model and the National Information Exchange Model to foster information sharing.
More
here.
Turkish Hacker 'Destroys' 100 New Zealand Websites
Via TVNZ.co.nz.
An overseas computer hacker has managed to wipe out nearly 100 New Zealand websites.
Some of the customers, who are mostly with the service provider ihug, are having to re-build their websites at a cost of thousands of dollars.
Kathryn Fisher, who sells her sunbeds on the internet, is one of an estimated 200,000 website owners who have suffered the same fate around the world thanks to a notorious Turkish hacker called Iskorpitz.
"On Monday morning I had been informed by clients that my website had been hacked," Fisher says.
The demolition tally on New Zealand websites is growing.
More
here.
Satire of the Day: 'Love, Democratic Style'
 Image source: The Raw Story
Image source: The Raw StoryHilarious.
But as also noted,
The Raw Story "...could not locate a 'Love Republican style' greeting card at the company's website."Enjoy.
- ferg
Australia: Secret New U.S. Spy Base to Get Green Light
Brendan Nicholson writes in The Sydney Morning Herald:
Australia close military alliance with the United States is to be further entrenched with the building of a high-tech communications base in Western Australia.
The Federal Government is about to approve the base after three years of secret negotiations with Washington.
The Age has been told the base, which will be built on defence land at Geraldton, will provide a crucial link for a new network of military satellites that will help the US's ability to fight wars in the Middle East and Asia. It will be the first big US military installation to be built in Australia in decades, and follows controversies over other big bases such as Pine Gap and North West Cape.
The deal has come to light amid heightened political debate over the alliance with the US and in the same week that the US finally told Australia it would not allow it to buy its best fighter aircraft, the F-22 Raptor.
More
here.
Chinese Police Plan to Allow Hacker to Release 'Fix' for Worm?
Bizarre.
And beware anything that purports to be a "fix" for a worm. :-)
Gregg Keizer writes on ComputerWorld:
A hacker arrested only days ago will be allowed to release a fix for the worm that he helped write, China's state media reported today.
Li Jun, one of six people recently arrested by provincial police for creating, then selling, the worm known as Panda Burning Joss Stick and Fujacks, has written a seek-and-destroy program that will eradicate the worm, said the government's official Xinhua News Agency.
Xinhua also reported that Li confessed yesterday to writing the worm "for fun" and selling it to several people for nearly $13,000. The Panda worm, which has spread widely throughout China, steals online game usernames and passwords.
Police in central China's Hubei Province said that after additional testing, the unnamed killer program will be posted to the Internet. According to Ye Tieguan, vice director of the Xiantao police bureau, Li's program eliminates the Panda worm.
More
here.
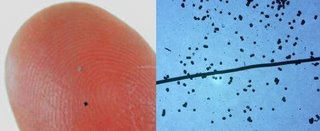
Mark of the Beast Watch: Hitachi's 'Weaponized' RFID Powder
Liz McIntyre
writes on the
Spychips RFID Blog:
The picture on the left shows Hitachi's infamous mu chip, once heralded as the world's smallest RFID tag. Back in 2003, it was touted as the perfect size for embedding into currency, slipping into bullets, and even tagging humans. The siren song of this dot-sized tracker even lured the Malaysian government into buying rights to it.
One can only wonder how Hitachi's new "weaponized" RFID powder will be used and abused. It is 64 times smaller than the mu chip, measures in at just .05 X.05 mm, but can still hold a unique 38-digit number. Specks of this RFID powder are pictured next to a human hair in the picture on the right.
More
here.
FBI: Sex Predator Hacked Into Computer To Threaten Girls
Via WFTV.com.
The FBI says it has caught an online sex predator who is more menacing than Central Floridians have ever seen before. He goes beyond trolling chat rooms for young girls and actually hacks into their computers and uses their personal information to threaten them.
The accused hacker got into the computers of four teenage girls, all friends, three from Rockledge. There was one attempt to threaten the hacker back, but it backfired. Investigators said a child should not communicate at all with a suspected hacker.
It all started on MySpace.com, according to federal documents. Records show that was where suspected hacker and child predator Ivory Dickerson, of North Carolina, first saw a 15-year-old girl from Rockledge and then asked her for nude photos.
Investigators said the accused hacker instant messaged her that "he knew where she lived, then provided the address."
More
here.
(
Props, Flying Hamster.)
California: Josh Wolf Case Assigned to Mediator
Michelle Meyers writes on the C|Net Media Blog:
Video blogger Josh Wolf, who last week became the longest-imprisoned journalist for contempt of court, got some good news yesterday in the form of a court order assigning his case to a mediating judge for settlement negotiations.
On August 1, Wolf, 24, was sent to a federal correctional facility in Dublin, Calif., for refusing to cooperate with a federal grand jury seeking unpublished footage he shot during a 2005 anarchist protest in San Francisco that turned violent. With exception of a short release on bail, he's been there ever since--for almost six months.
But on Tuesday, U.S. District Judge William Alsop, who has thus far presided over the case, referred it to U.S. Magistrate Joseph Spero for mediation, Wolf's Oakland, Calif.-based attorney Dan Siegel said Wednesday.
More
here.
Background
here.
Insurer Reports Personal Information Stolen
Via The (Louisville, Kentucky) Courier-Journal.
Computer tapes containing personal information on about 196,000 members of health insurer WellPoint — including many Anthem Blue Cross and Blue Shield customers in Kentucky and Indiana — have been stolen from the office of a WellPoint vendor.
Social Security numbers, often the key to committing identity theft, were among the information on the tapes.
Indianapolis-based WellPoint — the parent company of Anthem Blue Cross and Blue Shield, Kentucky’s largest health insurer — has received no reports of the information being misused, spokesman Jim Kappel said.
People whose information was stolen were notified in a recent letter from the company. The theft occurred in early November, but it took a long time to determine which members’ data was on the tapes, Kappel said.
More
here.
(
Props, Pogo Was Right.)
Man Who Hacked Physicians Organization Website Sentenced
Via The Philadelphia Business Journal.
A man who pleaded guilty last year to hacking into membership information on the American College of Physicians' Web site has been sentenced to three months in prison, three years of supervised release and a $10,000 fine, the U.S. Attorney's Office in Philadelphia said Tuesday.
William Bailey Jr. of Charlotte, N.C., had admitted to illegally downloading information on 80,000 members of the Philadelphia-based professional society from its Web site between January and May 2005.
Bailey ran a company that sold contact information for doctors called dr-411.com, the U.S Attorney's Office said. The stolen information did not include Social Security numbers or credit-card information.
More
here.
(
Props, Pogo Was Right.)
Valentine's Day
Via xkcd.com.
Hong Kong: Internet Links Normalized 50 Days After Quake
A dpa German Press Agency article, via The Raw Story, reports that:
Internet connections were restored to normal in Hong Kong Wednesday, 50 days after an undersea earthquake off Taiwan severely damaged cables to the former British colony. Six out of seven submarine cables coming in and out of Hong Kong were snapped by the December 26 earthquake, causing severe disruption to e-mail and internet connections.
Services were gradually improved but it took until Wednesday [14 February 2007] for Hong Kong's Telecommunications Authority to announce that the repairs to the cables were complete.
More
here.
Gang Warfare Spills Onto YouTube
A Reuters newswire article, via Red Herring, reports that:
A vicious Mexican drug gang war has moved onto Internet video site YouTube, where rivals taunt each other with blood-soaked slideshows and film of their murder victims.
One popular video on the site shows a man being shot in the head. A stomach-churning series of photos shows another execution victim, his missing face a mangled mess of flesh.
More
here.
Better Business Bureau Tangled in E-Mail Trojan Scheme
Annys Shin writes in The Washington Post:
The Better Business Bureau network was the target of a "spoofing" scam yesterday in which thousands of businesses in the United States and Canada received e-mails encouraging them to download what is thought to be a computer virus.
The e-mails, using the name of the 95-year-old network of nonprofit groups that looks into consumer complaints, told businesses that they were the subject of a complaint and included a link to view related documents. Clicking on the link, however, accessed the address book of an infected computer and distributed the counterfeit e-mail to more recipients, said Steve Cox, spokesman for the Council of Better Business Bureaus.
More
here.
Toon of the Day: Shifting Targets
Click for larger image.
Has the TSA Outsourced the TSA Traveler Identity Verification Program? - UPDATE
Christopher Soghoian writes on Slight Paranoia:
Browsing TSA's website this evening, I came across a link to the new TSA Traveler Identity Verification Program.
"The TSA Traveler Identity Verification Program is designed to assist those airline passengers who have been delayed or prevented from traveling as a result of TSA's security measures."
Unlike the rest of the TSA website, this is served from a different domain: http://rms.desyne.com/
Which means that a private company is running this site...
The whois database shows as follows:
Administrative Contact, Technical Contact:
Desyne, Inc. dns@DESYNE.COM
Desyne Web Services, Inc.
PO Box 143
Boston, VA 22713
US
(703) 391-2400 fax: (703) 391-2550
Record expires on 21-Mar-2015.
Record created on 20-Mar-1996.
Database last updated on 13-Feb-2007 21:32:10 EST.
This begs the question: Who are these guys, why don't they know how to use SSL and how were they awarded this sweet contract?
More
here.
UPDATE: 09:47 PST 02/14/2007: Brian Krebs
picked up this story this morning.
UPDATE: 09:54 PST 02/14/2007: So has Ryan Singel over on
27B Stroke 6.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Tuesday, Feb. 13, 2007, at least 3,126 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,509 died as a result of hostile action, according to the military's numbers.
The AP count is four higher than the Defense Department's tally, last updated Tuesday at 10 a.m. EST.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Australia: Police Porn e-Mail Investigation Under Way
Jano Gibson writes in The Sydney Morning Herald:
An investigation is under way after sexually explicit material was distributed on the NSW Police Force's internal email system.
Hundreds of officers and civilians have been caught up in the scandal, which involves "sexually inappropriate" material, a newspaper reported today.
A police spokeswoman today confirmed to smh.com.au that the Professional Standards Command was treating the matter seriously.
She said the emails were of an "inappropriate nature" but she would not be drawn on whether they contained pornographic images.
More
here.
FTC Urged to Step Up Oversight of Telecom Companies Offering Net Access
An AP newswire article, via SiliconValley.com, reports that:
Consumer advocates on Tuesday said federal regulators need to increase oversight of telephone and cable companies that offer Internet access to ensure they aren't discriminating against certain providers of video and other Web content.
Gigi B. Sohn, president of Public Knowledge, a nonprofit group that focuses on communications law, said the Federal Trade Commission should also require more disclosure from telephone and cable companies about the Internet access speeds they promise to deliver to consumers.
Sohn spoke on the first of a two-day workshop convened by the FTC to discuss "network neutrality" issues. The phrase is shorthand for the concept that all online traffic should be treated equally by Internet service providers.
More
here.
Sandia 'Back-Hacker' Wins $4.3M Judgment Against Sandia Labs - UPDATE
Bob Brewin writes on FCW.com:
Shawn Carpenter, who was fired by Sandia National Laboratories in January 2005 for conducting backhacking operations against intruders he discovered on Sandia networks, won a $4.3 million wrongful discharge suit against the labs today. Backhacking occurs when networks are attacked and someone on the hacked network responds with a counterhack or attack.
Carpenter, who worked in Sandia’s computer security operations organization, started detecting attacks against Sandia networks in 2002, according to court records in the 2nd District Court of New Mexico. Carpenter brought the attacks to the attention of Sandia and other government agencies, including the Army Research Laboratory and the FBI.
More
here.
Background: "
Titan Rain: The Invasion Of The Chinese"
UPDATE: 11:24 PST 02/15/2007: Time.com also has an update on this story
here.
Joshua Eveloff Pleads Guilty to Federal Spam Charges
Via Technology News Daily.
United States Attorney Carol C. Lam announced that Joshua Eveloff pled guilty in federal court in San Diego to fraud in connection with the generation of commercial electronic mail (e-mail) messages over the Internet for profit.
In connection with his plea, Eveloff admitted that he caused commercial e-mail messages, more commonly known as “spam,” to be sent out to millions of people during a three-month period in 2004.
More
here.
Iraqis Use the Internet to Survive War
Andrew North writes for The BBC:
Google is playing an unlikely role in the Iraq war. Its online satellite map of the world, Google Earth, is being used to help people survive sectarian violence in Baghdad.
As the communal bloodshed has worsened, some Iraqis have set up advice websites to help others avoid the death squads.
One tip - on the Iraq League site, one of the best known - is for people to draw up maps of their local area using Google Earth's detailed imagery of Baghdad so they can work out escape routes and routes to block.
It's another example of the central role technology plays in the conflict - with the widespread use of mobile phones, satellite television as well as the internet - by all sides and for many purposes.
More
here.
U.S. Cyber Officials: Chinese Hackers Attack 'Anything and Everything'
Josh Rogin writes on FCW.com:
At the Naval Network Warfare Command here, U.S. cyber defenders track and investigate hundreds of suspicious events each day. But the predominant threat comes from Chinese hackers, who are constantly waging all-out warfare against Defense Department networks, Netwarcom officials said.
Attacks coming from China, probably with government support, far outstrip other attackers in terms of volume, proficiency and sophistication, said a senior Netwarcom official, who spoke to reporters on background Feb 12. The conflict has reached the level of a campaign-style, force-on-force engagement, he said.
More
here.
Google Flags Pages that Install Malicious Software
Via the Google Operating System Blog.
I mentioned in August last year that Google started to show malware warnings if you click on a search result from a harmful site. Now Google shows a message below the title of a search result: "This site may harm your computer." Even if you click on the title, you won't be able to visit the site: Google explains you once again that the site could be dangerous and recommends you to visit another search results or to change your query. The only way to visit the site is to copy the URL and paste it in the address bar, which is not an obvious or a trivial task for an ordinary computer user.
Google explains: "this warning message appears with search results that we've identified as sites that may install malicious software on your computer. We want our users to feel safer when they search the web, and we're continuously working to identify such dangerous sites and increase protection for our users."
More
here.
Eli Lilly Loses Effort to Censor Zyprexa Documents Off the Internet
Via The EFF.
A U.S. District Court judge today refused Eli Lilly's request to ban a number of websites from publishing leaked documents relating to Zyprexa, Eli Lilly's top-selling drug. Although the judge rejected the First Amendment arguments made by a variety of individuals eager to publish the documents, the court concluded that "it is unlikely that the court can now effectively enforce an injunction against the Internet in its various manifestations, and it would constitute a dubious manifestation of public policy were it to attempt to do so."
The order is a victory for the Electronic Frontier Foundation (EFF), which represents an anonymous individual who was previously barred by the court's earlier orders from posting links to the Zyprexa documents on the zyprexa.pbwiki.com wiki.
The Zyprexa documents were leaked from an ongoing product liability lawsuit against Eli Lilly. The internal documents allegedly show that Eli Lilly intentionally downplayed the drug's side effects, including weight gain, high blood sugar, and diabetes, and marketed the drug for "off-label" uses not approved by the Food and Drug Administration (FDA).
More
here.
Quote of the Day: The Chinese Alliance Against Google
 Image source: Websense Security Labs
Image source: Websense Security Labs"Our league is an organization which against www.google.com treat large-scale net friends and the heads of station unfair. The purpose of our league is to collect the unfair proof and supervise google company go to fair."
- J. Random Chinese hacker, quoted on a Google "copycat" website (reported by the fine folks at Websense Security Labs), which attempts to exploit unpatched Internet Explorer users who have the Chinese language pack installed. Assuming users are not running the latest version of IE, they will be exploited with code that utilized the MS06-14 "MDAC" vulnerability.
Bank of America to Launch Mobile Banking
My opinion: Bad, bad idea.
Linda Rosencrance writes on ComputerWorld:
Bank of America's online customers will soon be able to use their cell phones and smart phones to check account balances, pay bills and transfer funds.
The bank said today it's launching secure mobile banking for its 21 million online banking customers. The service will be launched in Tennessee beginning in March and will be rolled out to other cities across the country through mid-year.
Customers who have mobile Internet access through Verizon Wireless, Sprint-Nextel, Cingular and T-Mobile will be able to access the new service. Customers will also be able to use a wide variety of mobile phones and devices, including Motorola, Nokia and LG handsets or smartphones, such as the Palm Treo, RIM BlackBerry or Motorola Q.
More
here.
Microsoft Releases Patches to Fix 20 Security Holes
Brian Krebs writes on Security Fix:
Microsoft Corp. today issued a dozen software updates to plug at least 20 security holes in its Windows operating system and other software, including fixes for a number of vulnerabilities in Office that hackers are currently exploiting to hijack vulnerable PCs. Windows users can download the free updates by visiting Microsoft Update or by enabling automatic updates.
The company labeled half of the vulnerabilities "critical," its most severe rating. Critical security holes are those that bad guys could exploit to seize control over vulnerable machines without any action on the part of the user, or those that could be exploited just by convincing a user to click on a link in an e-mail, or visit a particular Web page.
More
here.
Advice: Patch Now!
Leaked Letter Shows RIAA Pressuring ISPs - UPDATE
Eric Bangeman writes on ARS Technica:
The RIAA is asking for additional cooperation from ISPs in getting customers targeted by the RIAA's file-sharing sting to cooperate, according to a letter recently leaked to P2P attorney Ray Beckerman.
In it, the RIAA lays out its vision for how it would like ISPs to cooperate with its efforts to identify and sue those accused of sharing music over P2P networks. This includes communicating a standing offer of a $1,000 settlement discount should the subscriber settle before a lawsuit is filed against him or her. The letter also discloses plans for a settlement web site that will launch later this year.
More
here.
UPDATE: 21:23 PST: Or as the EFF puts it, "
RIAA to ISPs: Help Us Sue Your Customers Better."
Study: 70% Of Web Sites Are Hackable
Of course, this story sounds like a bit of self-promotion for the company that conducted the study, but it does highlight a problem that seems to be growing.
In fact, only recently, malicious code which was planted on the Miami Dolphins website just prior to the Super Bowl (as well as the CDC) illustrated this trend.
Sharon Gaudin writes on InformationWeek:
About 70% of Web sites contain vulnerabilities that put them at risk of being hacked, according to a new study issued on Tuesday.
A year ago, Acunetix, a Web site security company, began scanning sites, both business and nonbusiness, looking for vulnerabilities. Out of 3,200 sites scanned, 70% had vulnerabilities with either a medium- or high-risk rating, according to an Acunetix announcement. Company analysts say there is an "extremely high probability" of hackers finding and using the vulnerabilities to steal information.
More
here.
Gary McKinnon Update: UK Hacker Extradition Appeal Hearing Begins
 Gary McKinnon, appearing at court in London in 2005.
Gary McKinnon, appearing at court in London in 2005.
Jeremy Kirk
writes on
InfoWorld:
Lawyers for a British computer hacker started an appeal in London High Court Tuesday to block their client's extradition to the U.S.
Gary McKinnon, of London, is accused of deleting data and illegally accessing information on 97 U.S. military and NASA computers between February 2001 and March 2002. He's been charged in U.S. District Court for the Eastern District of Virginia.
McKinnon, who did not show up in court, could face up to 60 years in prison, said his attorney, Edmund Lawson.
British authorities declined to prosecute McKinnon and the U.S. sought to extradite him. He challenged the extradition order in Bow Street Magistrates Court in May 2006. His attorney contended that since U.S. authorities allege McKinnon disrupted critical military networks after the Sept. 11 terrorist attacks, he could be held as an enemy combatant and subjected to inhuman treatment.
The judge rejected the argument, and the U.K. Home Secretary John Reid subsequently approved an extradition order.
The appeal hearing will continue Wednesday in London High Court.
More
here.
Background
here.