Cyber-Spy Shares Her Know-How Tracking Terrorists Online
 Shannen Rossmiller
Shannen RossmillerErika Hayasaki
writes in
The Los Angeles Times:
The nervous woman in a gray suit clicked on a photo lineup on an overhead screen labeled, "Jihadi Martyrs." It flashed to mug shots of men with names like Abu Issa, an Al Qaeda recruiter, and Abu Jabber, a trainer.
A man in one photograph was pointing a machine gun.
"They are all me," said the blond mother from Montana, speaking before an audience of computer experts, law enforcement agents and investigators at the first International Conference on Cyber Security, which was held last week in New York. "These are all individuals I acted as on the Internet."
Shannen Rossmiller, 39, is a cyber-spy and former judge who taught herself Arabic after the Sept. 11, 2001, terrorist attacks and began infiltrating websites and chat rooms to hunt for terrorists. "I learned to act like them," she said. "I learned to be them."
As her children slept, she spent nights and mornings posing as more than two dozen Muslim militants from her home computer to gain information about planned attacks and terrorist cells across the world. Her investigations have led to two terrorism-related convictions in the U.S., and she has provided intelligence in more than dozens of other international cases.
More
here.
Image source: David Howells / The Telegraph
A Gaza War Full of Traps and Trickery
Steven Erlanger writes in The New York Times:
Israeli intelligence officers are telephoning Gazans and, in good Arabic, pretending to be sympathetic Egyptians, Saudis, Jordanians or Libyans, Gazans say and Israel has confirmed. After expressing horror at the Israeli war and asking about the family, the callers ask about local conditions, whether the family supports Hamas and if there are fighters in the building or the neighborhood.
Karim Abu Shaban, 21, of Gaza City said he and his neighbors all had gotten such calls. His first caller had an Egyptian accent. “Oh, God help you, God be with you,” the caller began.
“It started very supportive,” Mr. Shaban said, then the questions started. The next call came in five minutes later. That caller had an Algerian accent and asked if he had reached Gaza. Mr. Shaban said he answered, “No, Tel Aviv,” and hung up.
More
here.
Hat-tip: Danger Room
U.S. Toll in Iraq, Afghanistan

Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Friday, Jan. 9, 2009, at least 4,223 members of the U.S. military had died in the Iraq war since it began in March 2003, according to an Associated Press count.
The figure includes eight military civilians killed in action. At least 3,403 military personnel died as a result of hostile action, according to the military's numbers.
The AP count is two fewer than the Defense Department's tally, last updated Friday at 10 a.m. EST.
As of Friday, Jan. 9, 2009, at least 561 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Friday at 10 a.m. EST.
Of those, the military reports 408 were killed by hostile action.
More
here and
here.
And as always, the
Iraq Coalition Casualty Count keeps the grim watch on their website
here.
Honor the Fallen.
Army Assembles 'Mad Scientist' Conference. Seriously.

Noah Shachtman writes on Danger Room:
Last August, the U.S. Army held a three-day conference in Portsmouth, Virginia, to look at new developments in military science and hardware. The confab was called the "2008 Mad Scientist Future Technology Seminar." Really. It was.
"The objective of the seminar was to investigate proliferating technologies with the potential to empower individuals and groups in the next 10-25 years," according to an unclassified summary [.doc] of the Mad Scientist gathering, obtained by Danger Room.
As you'd expect from such a colorfully-titled gathering, the collected brains predicted a world in which individuals would have easy access to everything from ray guns to nano-bots to bioengineered weapons to arms for creating international chaos online.
More
here.
Too Many U.S. Agencies Tackle Cyber Security Threats
Loren B. Thompson writes for UPI:
Within the U.S. federal government, most of the funding allocated to information security and offensive cyber operations is spent by agencies of the Department of Defense.
The biggest player is the National Security Agency at Fort Meade, Md., which since the early days of the Cold War has been engaged in collecting and analyzing signals intelligence.
The NSA appears to have lead responsibility for securing all intelligence networks, and it shares expertise with the Defense Information Systems Agency that oversees military networks.
U.S. Strategic Command is the lead combatant command responsible for information operations and cybersecurity. In addition, each of the military departments of the Department of Defense -- the U.S. Army, U.S. Navy and U.S. Air Force -- has a dedicated command for managing information networks and assuring their security.
Although it receives much less money for network operations and security than the Department of Defense, the U.S. Department of Homeland Security is the lead federal agency for coordinating national cyberdefense initiatives.
More
here.
Cyber Espionage: Peeking Into Private Data
Kevin Coleman writes on DefenseTech.org:
Cyber espionage is a relatively new type of intelligence gathering capability with various strategies, tactics and tools.Cyber espionage is defined as the intentional use of computers or digital communications activities in an effort to gain access to sensitive information about an adversary or competitor for the purpose of gaining an advantage or selling the sensitive information for monetary reward. This widely accepted definition was originally crafted by Spy-Ops in their cyber warfare analysis program back in 2004.
Cyber espionage blasted on the scene in the mid 90s and has grown at a steady pace along side the adoption and use of the internet by business, government and industry. Even though cyber espionage is relatively new, countries like China have already invested a lot into building large and well trained cyber-espionage forces. By the first of 2009, Spy-Ops estimates about 140 countries and over 50 terrorist and criminal/extremist groups will be developing cyber weapons and espionage capabilities.
In conventional espionage you rely on deep cover covert operatives to conduct espionage and gain intelligence. In cyber espionage you use computer systems and data coupled with conventional techniques to gain intelligence and sensitive information. Events like the ones at ClearanceJobs and the Oakridge National Labs seem to indicate that the U.S. science and engineering community is being targeted. Let's look at these two incidents a bit closer.
More
here.
Friday Monkey Blogging: Africa's Oldest Chimpanzee Dead at 66
 Gregoire
Gregoire
As I
mentioned a couple of months ago, I have started a regularly recurring blog entry meme every Friday afternoon, inspired by Bruce Schneier's regular series of
"Friday Squid Blogging" posts, and my very own maddening
Monkey Theory.
Here is this week's installment.
Via The L.A. Unleashed Blog:
Gregoire, Congo legend and oldest known living chimpanzee, died peacefully in his bed (a pile of eucalyptus leaves) at Jane Goodall’s Tchimpounga Chimpanzee Rehabilitation Center on Dec. 17. He was 66 years old.
Gregoire was the poster child and ambassador for Goodall’s efforts to protect chimpanzees and end the illegal commercial bush-meat trade.
After surviving more than 40 years in a barren cage, Gregoire spent his last 11 years in peace at a sanctuary for orphaned chimpanzees. When Jane met Gregoire in 1990, he was barely recognizable.
More
here.
Image source: L.A. Unleashed / Jane Goodall Institute
Terrorist Organisations Hiring Pakistani Computer Professionals to Target Indian Websites
Via Midday News.
It is not just the big IT companies who are looking for tech-savvy youth in Pakistan. The terrorist organisations are equally interested.
Advertisements are regularly put up to attract young professionals for making a career in Jihad. Once recruited, the young minds undergo rigorous training to specifically target Indian websites both government and corporate to steal critical data, said a senior intelligence official.
"All terror groups have hired IT professionals, who are highly qualified to launch e-attacks and sabotage websites. It can not be denied that they are nurturing a new breed of cyber experts for targeting the Indian virtual space," the official added.
Attacks on Indian cyberspace from Pakistani hacker communities have increased in intensity and frequency.
More
here.
Hat-tip: Cyber Crime Updates
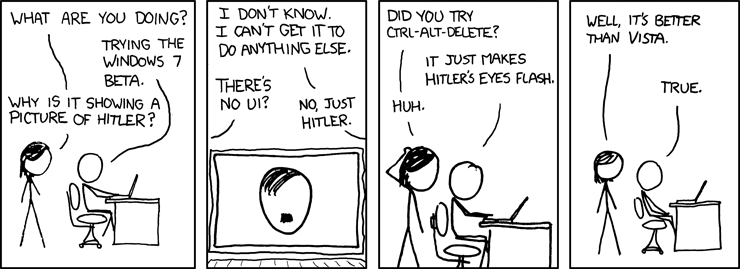
Classic xkcd: Windows 7
Click for larger image.
We
love xkcd.
Really.
- ferg
Fired Fry's Executive Charged With Fraud, Money-Laundering
Lisa Fernandez writes on SiliconValley.com:
A now-fired executive at Fry's Electronics was charged Thursday with nine counts of wire fraud and money laundering for allegedly squeezing millions of dollars in kickbacks from suppliers to pay off massive gambling debts, according to documents filed in San Jose federal court.
Ausaf Umar Siddiqui, who goes by "Omar," now faces formal arraignment on those charges Jan. 15 before U.S. Northern District Court Magistrate Judge Patricia V. Trumbull.
The nine felonies carry a maximum penalty of a 30-year prison sentence. But federal sentencing guidelines also treat first-time offenders much more leniently.
The indictment is similar — but smaller in scope — to the arrest complaint filed Dec. 18, which alleged Siddiqui cheated Fry's out of $65 million over three years. The indictment charges only nine transactions totaling less than $6 million from June 2005 to November 2008. And instead of naming five vendors by name, as was listed in the arrest complaint, the indictment limits the illegal transactions to only two unnamed vendors.
"How does it go from $65 million when he was arrested to less than $6 million now?'' asked Eric Sidebotham, Siddiqui's civil attorney helping him fend off casinos across the country who are suing him for millions they say he owes them. "I find that number really interesting. It's not nearly as bad as they originally charged.''
More
here.
Toon of The Day: Chinese Netizens on 'Netizens' Day'
 Click for larger image.
Click for larger image.
Translation:
(1) “September 14 is now Netizens’ Day. We netizens finally have our own celebratory day, Yeah!”
(2) “How should we netizens celebrate this day?”
(3) “Take a day off! I guarantee everyone will be happy.”
“But netizens are from all different walks of life, how can they take the same day off?”
(4) “I mean, let the comrades who are policing the Internet to take that day off…”
Via China Digital Times.
Report: Pentagon Drifting From Nuclear Deterrence
David Wood writes in The Los Angeles Times:
After firing the two top Air Force leaders last year for a series of embarrassing nuclear weapons mishaps, Defense Secretary Robert M. Gates was told Thursday that the same problems of inexperience, poor training and splintered authority over nuclear arms affect the entire Pentagon, including its top leadership.
A task force headed by former Defense Secretary James R. Schlesinger painted a dismal picture of a Pentagon that has drifted from the mission of nuclear deterrence during the nearly two decades since the Cold War ended. Among the Pentagon's senior military and civilian leaders, the panel found "a distressing degree of inattention" to the role of nuclear weapons in deterring attacks on the United States.
Education in nuclear deterrence theory and practice at the nation's top military schools has largely ended, senior-level exercises have stopped and the number of senior officials familiar with deterrence is rapidly dwindling and will soon become an "acute" problem, Schlesinger reported.
Many senior leaders "lack the foundation for understanding nuclear deterrence, its psychological content, its political nature and its military role -- which is to avoid the use of nuclear weapons," the report concluded.
More
here.
Widespread Vulnerabilities Found in Programs Which Use OpenSSL
Via Netcraft.
New vulnerabilities were discovered yesterday in multiple programs using OpenSSL, one of the standard cryptography libraries on Linux and Unix systems. Due to a common mistake in checking return values from functions checking digital signatures, several programs may be vulnerable to spoofing of digital signatures.
The most important affected program is ISC Bind, which is the most widely used DNS server on the internet. A flaw in its validation of signatures on DNSSEC replies means that the server may be vulnerable to DNS spoofing attacks even where DNSSEC is in use. Bind have released BIND 9.6.0-P1 this morning to fix this bug.
The common mistake is in the checking of return values from functions in OpenSSL that check digital signatures. Programmers have failed to allow for all the possible return values of the EVP_VerifyFinal function, and as a result some cases where the signature has not been successfully checked can be mistakenly treated as successfully verified.
More
here.
MI5: Internet Phone Services a Risk to National Security
Leo King writes on Computerworld UK:
Internet telephone services pose a serious threat to Britain’s security, the head of MI5 has said.
The danger with online calls, said spy chief Jonathan Evans, was that they do not result in telephone bills, which are key evidence documents in prosecutions. This meant it would be much easier for terrorists to make the calls and eventually escape prosecution if they are tried for criminal offences.
In an interview with the media yesterday, Evans, director general at MI5 since 2007, said online phone calls posed a “significant detriment to national security” by enabling terrorists to communicate with less risk.
Evans lent his support to the government’s planned database of every phone call, internet use and email in the UK, saying that it was important the security agencies could access this information.
"If we are to maintain our capability we are going to have to make decisions [on powers to intercept communications] in the next few years," he was reported as saying, in the Daily Telegraph. "Because traditional ways are unlikely to work."
More
here.
E-Mail SNAFU Exposes Names of Confidential Witnesses in Federal Probe
Jaikumar Vijayan writes on ComputerWorld:
From the how-not-to-keep-a-secret department comes the tale of an official at U.S Attorney Patrick Fitzgerald's office in Chicago who inadvertently e-mailed a document containing the names of more than 20 confidential witnesses in a federal probe to the media.
According to reports published by the Chicago Tribune and The Smoking Gun Web site, the snafu happened yesterday, when a spokesman for Fitzgerald attached the document to an e-mail message announcing felony charges against individuals named John Walsh and Charles Martin. The two men were partners in a foreign-exchange futures dealer called One World Capital Group, located in the Chicago area but now defunct, that is accused of defrauding customers of $15 million.
Included along with the 62-page complaint filed against Walsh and Martin was a one-page chart that identified 24 sources who were mentioned only in an anonymous fashion in the complaint itself. The sources included former One World employees, customers and "other" individuals, according to a copy of the document that was posted by The Smoking Gun with the names blurred out. The document also apparently identified two investment groups that hadn't been publicly named.
More
here.
A Shift in Terrorist Tactics Towards 'Softer' Targets?
Jonah Czerwinski writes on Homeland Security Watch:
President Bush’s outgoing Homeland Security Adviser, Ken Wainstein, told an audience this week that Mumbai-style attacks could happen “in any American city.” A well written piece in the UK Reuters explains the growing concern amid the counter-terrorism community that the brazen assault on civilians in tourist centers attractive to Westerners could be a sign of what’s to come.
Since 9/11, most analysis of the terrorist threat has been focused on al Qaeda’s apparent focus on catastrophic and high-casualty attacks on the unarmed. As a result, analysts have suggested that low-intensity assaults with automatic weapons or car bombs are less likely than attacks on the scale of 9/11, or worse.
However, attacks like those on the rail systems in Madrid, the nightclub in Bali, the mass transit system in London, and now the hotels and urban centers of Mumbai, among others, suggest a shift that has been underway from targeting military and government entities toward more vulnerable “soft targets” populated by civilians.
More
here.
Clock Ticking for Gas Stations to Pump Up Data Security
Jaikumar Vijayan writes on ComputerWorld:
Starting Jan. 1, Visa Inc. is requiring all new fuel-dispensing machines being installed at gas stations around the U.S. to support the Triple Data Encryption Standard, a mandate that is designed to make it harder for identity thieves to steal debit card data from gas pumps by shielding the personal identification numbers (PIN) of customers.
So-called card-skimming devices placed on gas pumps have been used to compromise payment card data in the past. For example, in 2005, data at gas stations operated by Wal-Mart Stores Inc.'s Sam's Club division was compromised.
Visa's new requirement calls on gas retailers to ensure that all new pumps capable of processing debit card purchases are equipped with an encrypting PIN pad, or EPP, that supports Triple DES. Although Visa is the only credit card company mandating the use of the encryption technology now, the requirement is expected to become part of a broader specification for unattended point-of-sale (POS) systems that is being developed by the PCI Security Standards Council, which is responsible for the Payment Card Industry Data Security Standard and other data-protection measures.
Gas station owners have until July 1, 2010, to ensure that all of their existing pumps are upgraded to support Triple DES. Robert Renke, executive vice president of the Petroleum Equipment Institute in Tulsa, Okla., estimated that about 1.4 million gas pumps would need to be retrofitted with new software — for an average of more than 2,500 per day in order for retailers to meet Visa's deadline.
More
here.
Carder Linked to TJX Hack Jailed for 30 Years by Turkish Court
John Leyden writes on The Register:
A Ukrainian fraudster linked to the infamous TJX hack was sentenced to a 30 year prison sentence in Turkey on unrelated charges this week.
Maksym Yastremskiy (AKA Maksik) was found guilty of hacking into the computer systems of 12 Turkish banks, as well as committing computer fraud against them, according to local reports. The court also reportedly fined Yastremskiy $23,200.
Yastremskiy was arrested by police in Turkey in July 2007, after visiting a nightclub in the beach resort of Kemer, in an operation US law enforcement agencies soon realised was key to unraveling the TJX hacking case.
It emerged within weeks that Yastremskiy was fencing hundreds of hundreds of thousands of credit card numbers linked to hacking attacks at US retail outlets, including TJX, through various underground carders forums. Yastremskiy was charged last August with trafficking in stolen credit card information harvested from a string of retail firms including TJX, OfficeMax, Barnes & Noble, Forever 21, DSW, and Marshall's, among others.
Alleged ringleader Albert "Segvec" Gonzalez of Miami allegedly conspired with ten other suspects (including Yastremskiy) to hack into the insecure networks maintained by the US retailers and lift 40 million credit and debit card numbers. Since the heist against TJX alone affected 45.6 million customers alone these colossal figures are, if anything, a possible underestimate of the possible extent of the crime.
More
here.
NYPD Eyes Disrupting Cell Phones in Event of Terrorist Attack
Judith Miller writes on FOXNews.com:
The New York Police Department is looking for ways to disrupt cell phone calls and other forms of electronic communication among terrorists in the event of another terror attack in New York, Police Commissioner Raymond Kelly says.
The need to disrupt communications is one of several conclusions that the NYPD has drawn from studying the November attack in Mumbai, India, a three-day rampage by machine gun and grenade-wielding Islamic militants in which at least 165 people were killed and 304 were wounded.
Kelly is scheduled to discuss this and other "lessons learned" in testimony Thursday before the Senate Committee on Homeland Security and Governmental Affairs. A draft copy of his statement was shared with FOX News in advance of his appearance.
Kelly stressed the need for law enforcement to be able to disrupt cell phone calls and other communications during an attack, pointing to threats posed by the media when they disclose law enforcement tactics during live coverage that can get passed back to the attackers.
More
here.
U.S. Army and NATO Parliament Websites Defaced by Turkish Hackers

Via Zone-H News.
The Turkish defacer going by the handle of Agd_Scorp hacked and defaced the US Army Mil website mdw.army.mil and NATO Parliament www.nato-pa.int protesting for the Israeli attacks on the Palestinian territory.
The defacements (viewable by clicking here and here) reports messages in Turkish in support of the Intifada as well as an English message stating:
"Stop attacks u israel and usa ! you cursed nations ! one day muslims will clean the world from you"
More
here.
Unemployment Claims Crash State Web Sites
Rich Miller writes on Data Center Knowledge:
A sign of the times: a surge in filings for unemployment benefits has apparently crashed online application systems in four states this week. Phone systems appear to be faring even worse in handling the logjams in jobless claims. Here’s a summary:
- North Carolina’s web site for filing unemployment claims was offline Sunday and Monday, when the system experienced three times its usual volume. The site returned to service Monday after state officials added another server to accommodate demand.
- Ohio’s online system for jobless claims was down Monday and Tuesday, with state officials citing unusual volume as the cause.
- New York’s Internet claims system failed Monday afternoon and was out of service completely for the first half of Tuesday. A state official attributed the downtime to technical problems with authentication systems.
- Kentucky’s system has also cratered under load, according to the Courier-Journal. Thanks to commenter BOFE for the tip.
Phone systems for filing unemployment claims were overwhelmed in multiple states, creating a silver lining: states are now hiring extra call center workers to field the extra call volume.
More
here.
Hat-tip: /.
Mark Fiore: Rocket Science

More Mark Fiore brilliance.
Via The San Francisco Chronicle.
Enjoy.
- ferg
DataPath to Support U.S. Battlefield SATCOM
Via UPI.
The U.S. Army has contracted DataPath Inc. for the company to provide satellite communication technologies to support battlefield communications.
Under the $100 million deal, Georgia-based DataPath will upgrade its DataPath Satellite Transportable Terminals used by the Army to operate on the Wideband Global Satellite communication system. In order for the Army's terminals to operate on the WGS system, DataPath will integrate them with Ka band conversion kits.
Officials say the satellite communication terminals are being converted to support the Army's Joint Network Node/Warfighter Information Network-Tactical program and enable mission-critical battlefield communications.
More
here.
South African Commission Seeking Legal Action Against 'Hacker' Who Leaked Documents to Wikileaks
Linda Ensor writes on Business Day:
The Competition Commission has laid criminal charges against the unknown hackers who lifted the lid on highly confidential information about the South African banking system that the four big banks wanted to keep under wraps.
The charges had been laid in terms of the Electronic Communications and Transactions Act, the commission’s manager for strategy and stakeholder relations, Nandisile Mokoena, said yesterday.
The confidential information is contained in the technical report of the inquiry into the banking system undertaken by the commission.
An uncensored version of the report was posted on the Wikileaks.org website after hackers — believed to be based in SA — broke through the security measures put in place by the commission.
More
here.
Vietnam Vets Sue CIA for Secret Drug Experiments on GIs
Jeff Stein writes on SpyTalk:
A Vietnam veterans group is suing the CIA for "thousands of secret experiments to test toxic chemical and biological substances under code names such as MKULTRA," its attorneys said today.
The suit was filed in federal court in northern California on behalf of the Washington-based Vietnam Veterans of America, Inc., and six aging veterans with multiple diseases and ailments "tied to a diabolical and secret testing program, whereby U.S. military personnel were deliberately exposed, by government and military agencies, to chemical and biological weapons and other toxins without informed consent," the Morrison & Foerster law firm said in a press release.
The firm said the alleged CIA research program was launched in the early 1950s and continued through at least 1976 at the Edgewood Arsenal and Fort Detrick, Md., as well as universities and hospitals across the country contracted by the CIA.
Defendants include the CIA, the Department of the Army, the Department of Defense and various government officials responsible for these agencies.
More
here.
Caveat Emptor: Watch Out for Phantom Stores
Brian Krebs writes on Security Fix:
Most people are proud to say they would never fall for a phishing scam, that they would never give their personal and financial information away at fake banking sites, just because someone asked them to in an e-mail. But how many people will use that same common sense when a too-good-to-be-true bargain presents itself at a no-name online electronics shop?
A slew of fake electronics sites, some of them apparently being promoted by major online search engines and comparison-shopping sites, have been swindling consumers out of cash and credit card numbers for several weeks. The Web sites are confusingly named after legitimate electronics and clothing shops in the United States. All say they accept major credit cards and PayPal, and some carry seals boasting that they are "hacker safe."
But customers who order something from these sites soon find their accounts charged increasing amounts for unauthorized transactions.
More
here.
Note: For what it's worth, Paradius has
long been known to be a source of various forms of cyber crime, and has also been known to host activities of Eastern European cyber criminals formerly affiliated with the notorious
Russian Business Network.
- ferg
Blurred Out: 51 Things You Aren't Allowed to See on Google Maps
Via Curious? Read.
Depending on which feature you use, Google Maps offers a satellite view or a street-level view of tons of locations around the world. You can look up landmarks like the Pyramids of Egypt or the Great Wall of China, as well as more personal places, like your ex’s house. But for all of the places that Google Maps allows you to see, there are plenty of places that are off-limits.
Whether it’s due to government restrictions, personal-privacy lawsuits or mistakes, Google Maps has slapped a "Prohibited" sign on the following 51 places.
More
here.
Hat-tip: Bruce Schneier
Hacked Lawmaker Calls For Cyber Briefings
Via The National Journal.
Rep. Frank Wolf, R-Va., told House leaders Tuesday that few members of Congress have availed themselves of secret briefings meant to educate them about outsiders trying to penetrate lawmakers' computers and steal sensitive information. Despite "repeated assurances" that the House leadership would inform members of Congress about threats to their computer systems and personal electronic devices, members are still at risk of being hacked by foreign and domestic sources, Wolf wrote in a letter [.pdf] sent to House Speaker Nancy Pelosi and other leaders, which was obtained by National Journal.
In September of last year, the Republican and Democratic caucuses held classified briefings for lawmakers about cyber risks, but "the meetings were sparsely attended," Wolf wrote. "I fear that Members are no better informed today than they were before."
Because so few members showed up, Wolf wants to require mandatory briefings. He has proposed including language to that effect in the rules package set to be adopted Tuesday during the first meeting of the new Congress. Wolf suggested that the meetings address "threats to House information security, threats to information security when members travel abroad, and measure being taken [to] secure House computer networks and electronic devices."
More
here.
Hat-tip: Pogo Was Right
Cisco Global Site Selector Appliances DNS Vulnerability
Via Cisco.com.
The Cisco GSS platform allows customers to leverage global content deployment across multiple distributed and mirrored data locations, optimizing site selection, improving Domain Name System (DNS) responsiveness, and ensuring data center availability.
The GSS is inserted into the traditional DNS hierarchy and is closely integrated with the Cisco CSS, Cisco Content Switching Module (CSM), or third-party server load balancers (SLBs) to monitor the health and load of the SLBs in customers data centers. The GSS uses this information and user-specified routing algorithms to select the best-suited and least-loaded data center in real time.
A vulnerability exists in the GSS when processing a specific sequence of DNS requests. An exploit of the vulnerability may result in a crash of the DNS service on the GSS.
More
here.
Google Trends Falls Victim to Disturbing 'Stunt'
Miguel Helft writes on the New York Times "Bits" Blog:
Google Trends, a service shows the relative popularity of search terms, fell victim to what appeared to be an ugly stunt on Tuesday: a sketch of an airplane flying into two towers appeared as its second most popular item under Hot Trends, its list of the fastest rising searches at any given moment. TechCrunch and a swastika appeared on Hot Trends. A week later, the list was attacked again.
Search experts said the repeated incidents are something of embarrassment for the world’s No. 1 search engine. “It’s not a good thing for Google,” said Danny Sullivan, the editor of Search Engine Land. After last summer’s incidents, Google should have done more to detect this type of stunt, he said. “They should have been able to see that the query was not made up of words,” he added.
More
here.
Homeland Security's New Rules on Electronic Data Collection Rile Businesses
Thomas Frank writes on USA Today:
The Department of Homeland Security will collect millions of new electronic records about private planes, imported cargo, foreign visitors and federal contractors as part of an array of controversial last-minute security policies imposed by the Bush administration.
Businesses say the policies are costly, and worry that sensitive information could be released if a database is lost or stolen. Some charge the Homeland Security Department with rushing to impose policies and ignoring business concerns.
"Industry keeps reaching out to (them), but our comments are continually dismissed," said Catherine Robinson, director of high-tech trade policy for the National Association of Manufacturers trade group, which represents 14,000 companies.
Homeland Security spokeswoman Amy Kudwa said that by collecting information electronically, the department can run security checks more quickly than with paper forms, and could flag people or cargo that should be barred from the USA. Some changes have been in the works for more than a year.
More
here.
CheckFree Warns 5 Million Customers After Hack
Robert McMillan writes on ComputerWorld:
CheckFree and some of the banks that use its electronic bill payment service are notifying more than 5 million customers after criminals took control of several of the company's Internet domains and redirected customer traffic to a malicious Web site hosted in the Ukraine.
The Dec. 2 attack was widely publicized shortly after it occurred, but in a notice [.pdf] filed with the New Hampshire Attorney General, CheckFree disclosed that it was warning many more customers than previously thought.
That's because CheckFree is not only notifying users of its own CheckFree.com Web site of the breach, it is also working with banks to contact people who tried to pay bills from banks that use the CheckFree bill payment service.
"The 5 million people who were notified about the CheckFree redirection were a combination of two groups," said Melanie Tolley, vice president of communications with CheckFree's parent company, Fiserv, in an prepared statement. "1.) those who we were able to identify who had attempted to pay bills from our client's bill pay sites and minus those who actually completed sessions on our site; and 2.) anyone enrolled in mycheckfree.com."
Tolley wouldn't say what banks were affected by the hack, but the majority of these five million customers were CheckFree's own users, she said. In total, about 42 million customers access CheckFree's bill payment site, she said.
More
here.
FBI Stoking Fears of 'Cyber Armageddon'
An AFP newswire article, via PhysOrg.com, reports that:
Cyber attacks pose the greatest threat to the United States after nuclear war and weapons of mass destruction -- and they are increasingly hard to prevent, FBI experts said Tuesday.
Shawn Henry, assistant director of the FBI's cyber division, told a conference in New York that computer attacks pose the biggest risk "from a national security perspective, other than a weapon of mass destruction or a bomb in one of our major cities."
"Other than a nuclear device or some other type of destructive weapon, the threat to our infrastructure, the threat to our intelligence, the threat to our computer network is the most critical threat we face," he added.
US experts talk of "cybergeddon," in which an advanced economy -- where almost everything of importance is linked to or even controlled by computers -- is sabotaged by hackers.
Michael Balboni, deputy secretary for public safety in New York state, described "a huge threat out there" against everything from banking institutions to municipal water systems and dams.
Henry said that terrorist groups are working to create a virtual 9/11, "inflicting the same kind of damage on our country, on all our countries, on all our networks, as they did in 2001 by flying planes into buildings."
More
here.
AT&T Building $23M IPv6 Network for U.S. Army Europe
Carolyn Duffy Marsan writes on NetworkWorld:
AT&T is building a production-quality IPv6 data network for the U.S. Army in Germany that will cost approximately $23 million when it is completed next year.
The Army is ahead of the curve with its new state-of-the-art data network, which will support its operations in Grafenwoehr, Germany – the home of the 7th Army Joint Multinational Training Center (JMTC).
AT&T is installing and testing a new campus data network, which will support Army personnel at 600 JMTC buildings. AT&T says the installation will be complete in January 2010.
More
here.
Twitter Hacker Says Admin Password Was 'Happiness'
Kim Zetter writes on Threat Level:
An 18-year-old hacker with a history of celebrity pranks has admitted to Monday's hijacking of multiple high-profile Twitter accounts, including President-Elect Barack Obama's, and the official feed for Fox News.
The hacker, who goes by the handle GMZ, told Threat Level on Tuesday he gained entry to Twitter's administrative control panel by pointing an automated password-guesser at a popular user's account. The user turned out to be a member of Twitter's support staff, who'd chosen the weak password "happiness."
Cracking the site was easy, because Twitter allowed an unlimited number of rapid-fire log-in attempts.
"I feel it's another case of administrators not putting forth effort toward one of the most obvious and overused security flaws," he wrote in an IM interview. "I'm sure they find it difficult to admit it."
The hacker identified himself only as an 18-year-old student on the East Coast. He agreed to an interview with Threat Level on Tuesday after other hackers implicated him in the attack.
More
here.
Data Breaches Up Almost 50 Percent, Affecting Records of 35.7 Million People
Brian Krebs writes in The Washington Post:
Businesses, governments and educational institutions reported nearly 50 percent more data breaches last year than in 2007, exposing the personal records of at least 35.7 million Americans, according to a nonprofit group that works to prevent identity fraud.
Identity Theft Resource Center of San Diego is set to announce today that some 656 breaches were reported in 2008, up from 446 in the previous year. Nearly 37 percent of the breaches occurred at businesses, while schools accounted for roughly 20 percent of the reported incidents.
The center also found that the percentage of breaches attributed to data theft from current and former employees more than doubled from 7 percent in 2007 to nearly 16 percent in 2008.
"This may be reflective of the economy, or the fact that there are more organized crime rings going after company information using insiders," said Linda Foley, the center's co-founder. "As companies become more stringent with protecting against hackers, insider theft is becoming more prevalent."
More
here.
So Why Did Obama Pick Panetta as CIA Chief?
 Leon Panetta
Leon PanettaMatthew B. Stannard
writes in
The San Francisco Chronicle:
There is no question the agency is emerging from a troubled period, criticized by many for failing to stop the Sept. 11 attacks, for mistakenly concluding that Iraq under Saddam Hussein had an arsenal of weapons of mass destruction and for shipping terror suspects to secret overseas sites to be tortured or worse.
At the same time, there is broad consensus on the need for a robust and effective intelligence service to meet modern national security and foreign policy challenges.
Under changes established after the Sept. 11 terrorist attacks, the job of briefing the president each morning no longer falls to the CIA director. That job now belongs to the director of National Intelligence, who oversees the CIA and other clandestine services. That job reportedly will go to retired Adm. Dennis Blair under President Barack Obama.
Under that structure, Panetta's lack of intelligence and overseas experience might matter less than his managerial and political experience - and his bipartisan reputation for integrity, several analysts said Monday.
More
here.
Intelligence: Pakistani Hackers Plan Attack on Indian Cyber Networks
A Press Trust of India (PTI) article, via The Hindustan Times, reports that:
After the Mumbai terror strikes, anti-India elements in Pakistan are now planning an attack on Indian computer networks, intelligence agencies have warned.
Already Pakistani hackers are trying out a dry run against Indian networks through popular websites registered there after the Mumbai terror strikes, Home Ministry sources told PTI on Tuesday.
"Every time the relations between the two countries dampen, Pakistanis start attacking Indian computer networks and this has increased after the Mumbai terror attacks," a Home Ministry source said.
Pakistani hackers have created websites such as the www.songs.pk, which are infested with software to hack data from the targeted computers, it said.
"The website www.songs.pk has over 12 lakh [equivalent to 1.2 Million - ferg] Indian users who are downloading stuff from these websites daily," said a cyber expert in the Ministry.
With these websites being highly popular, it will take only a few minutes for the hackers to take command of over 12 lakh computers in few minutes and the number of such computers can multiply in every minute, sources said.
More
here.
Internet Security Faces Chronic Problems
Loren B. Thompson writes for UPI:
U.S. network software and procedures must be continually updated to eliminate weaknesses, and tested to assure gaps have been successfully closed.
Also, there must be a mechanism among network administrators across the United States for sharing information about threats that provides timely and useful warnings of danger.
Finally, defensive measures carried out by the U.S. government and its relevant agencies must be sensitive to the missions of users, so that they do not impair network functionality in the process of providing protections.
The respected SANS Institute uses a six-step framework for explaining how cyber incidents should be addressed that begins with being prepared, and then proceeds through identification of danger, containment of the threat, eradication of the threat, system recovery and follow-up.
More
here.
U.S. Judge Revives Lawsuit Over Bush Wiretap Program
Henry K. Lee writes in The San Francisco Chronicle:
A defunct Islamic charity in Oregon that says it was illegally wiretapped by federal authorities can pursue its lawsuit challenging President Bush's clandestine eavesdropping program, a federal judge in San Francisco ruled Monday.
In reviving a suit filed by Al-Haramain Islamic Foundation, Chief U.S. District Judge Vaughn Walker said the group had enough publicly available evidence to show that it could reasonably believe it had been wiretapped.
The ruling is "a big win for us," said Jon Eisenberg, an Oakland attorney for the plaintiffs.
Walker had dismissed the suit in July, saying the group could not use a classified document that the government had accidentally turned over to the foundation.
But later that month, the group produced non-secret information - an October 2007 speech in which a deputy FBI director said that the agency "used ... surveillance" in an investigation into whether the organization was linked to terrorism. The speech was given at a conference of the American Bankers Association and American Bar Association on money laundering.
More
here.
Video: Inside a Credit Card Fraud Factory
Kevin Poulsen writes on Threat Level:
Detective Bob Watts of the Newport Beach Police Department takes us on a guided tour of the sophisticated credit card forgery operation run by Chris Aragon, an associate of Max Butler, the uber hacker I profiled for this month's Wired. Aragon made a living turning Butler's stolen credit card data into near-perfect forgeries, complete with holograms. Here's how.
More
here.
Spamhaus: Google Now 4th Most Spam-Friendly Provider
Brian Krebs writes on Security Fix:
Google's free services are being heavily exploited by spammers to redirect visitors to sites touting knockoff designer drugs and scams, according to the latest rankings from Spamhaus.org, a group that tracks unsolicited commercial e-mail.
Last month, Security Fix called attention to Microsoft's persistent ranking on Spamhaus's running list of the "Top 10 Worst Spam Service ISPs". Now that Microsoft has cleaned up its act, it appears the bad guys are moving on to Google, which is now ranked #4 on the list (#1 being the worst).
"Microsoft got rid of the bad guys, and off they went to Google, which is now hosting a lot of the stuff that was on Microsoft's domains," said Richard Cox, Spamhaus's chief information officer.
Other Internet providers, including Sprint and Verizon, currently round out the #8 and #10 slots on the Top 10 list, respectively.
More
here.
Wanted By The FBI: Job Seekers
Via FBI.gov.
Attention job seekers: the FBI is looking for a few good men and women to fill a variety of mission-critical roles within our organization.
Well actually, we’re looking for a few thousand—just over 2,100 professional staff employees and 850 special agents, to be precise—in one of the largest hiring blitzes in our 100-year history.
According to Assistant Director John Raucci of our Human Resources Division, it’s to bring more people on board with skills in critical areas, especially language fluency and computer science. “But,” explains Raucci, “we’re also looking for professionals in a wide variety of fields who have a deep desire to help protect our nation from terrorists, spies, and others who wish us harm.”
More
here.
Hat-tip: FedBlog
Constitutionality of FISA to be Reviewed
Steven Aftergood writes on Secrecy News:
A federal appeals court in Oregon will hold a hearing next month on a government appeal of a 2007 judicial ruling that said the Foreign Intelligence Surveillance Act (FISA) is unconstitutional.
The FISA is a statute that regulates domestic intelligence, and generally requires judicial authorization for intelligence search and surveillance within the United States. Critics of Bush Administration electronic surveillance activities such as the “Terrorist Surveillance Program” have argued that they unlawfully circumvented the provisions of the FISA.
But the FISA itself, as modified by the USA PATRIOT Act, is unconstitutional, a federal court ruled [.pdf] on September 26, 2007.
That ruling came in response to a challenge by Brandon Mayfield, who was erroneously arrested in connection with the Madrid bombings in 2004 based on a false fingerprint match and subsequent surveillance under the Foreign Intelligence Surveillance Act. The FBI later apologized for his mistaken arrest and provided a financial settlement. But Mayfield continued to challenge the legal foundation of the arrest.
More
here.
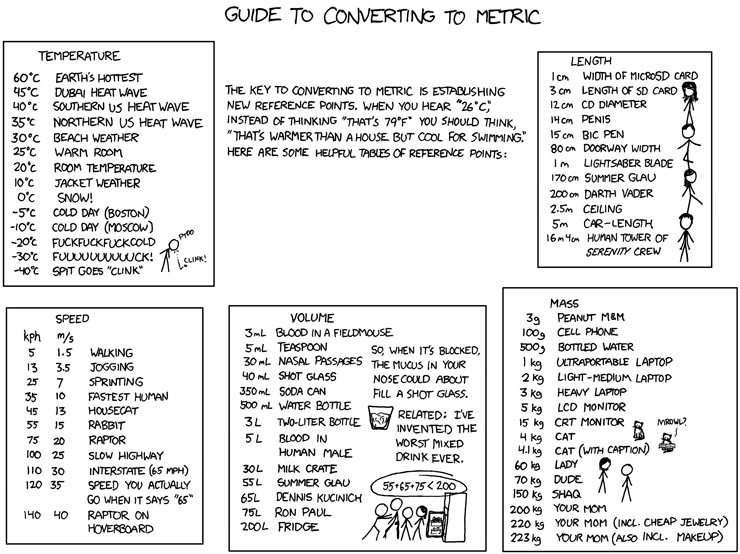
Classic xkcd: Converting to Metric
Click for larger image.
We
love xkcd. Really.
Enjoy!
- ferg
60 Minutes: Reading Your Mind
Via CBS News/60 Minutes.
How often have you wondered what your spouse is really thinking? Or your boss? Or the guy sitting across from you on the bus? We all take as a given that we'll never really know for sure. The content of our thoughts is our own - private, secret, and unknowable by anyone else. Until now, that is.
As correspondent Lesley Stahl reports, neuroscience research into how we think and what we're thinking is advancing at a stunning rate, making it possible for the first time in human history to peer directly into the brain to read out the physical make-up of our thoughts, some would say to read our minds.
More
here.
Bush Legacy in California Called 'Negative,' 'Zilch'

Carla Marinucci writes in The San Francisco Chronicle:
President Bush once remarked at a White House party that in the famously liberal enclave of San Francisco, his supporters were so rare that "you could probably fit them all in one room."
He wasn't exaggerating, and he would do little to alter his standing. He never once set foot in San Francisco during his two terms, and he was hardly much chummier with California as a whole, the nation's most populous state and the world's eighth-largest economy.
The 43rd president's legacy in the Golden State, according to the unsparing assessment of Democratic consultant Phil Trounstine, is "zilch."
"He regarded California sort of like France - as a foreign entity for which he had nothing but scorn," said Trounstine. "Except for this: He did more damage to California than he ever did to France."
More
here.
CIA Tracking 4000 UK Terror Suspects
Tim Shipman writes in The Age:
The CIA has begun an unprecedented intelligence-gathering operation in Britain to help MI5 monitor 4000 terrorist suspects.
More than four out of 10 CIA operations to prevent attacks on US soil are now conducted against targets in Britain.
This has led to friction between British and American spies, with some US intelligence officers irritated that resources are being diverted to gather intelligence on suspects in their closest ally's backyard. British intelligence officers do not know the identity of all the CIA informers and are uneasy about some of the uses to which the intelligence has been put.
More
here.
More Groups Than Thought Monitored in Maryland Police Spying
Lisa Rein and Josh White write in The Washington Post:
The Maryland State Police surveillance of advocacy groups was far more extensive than previously acknowledged, with records showing that troopers monitored -- and labeled as terrorists -- activists devoted to such wide-ranging causes as promoting human rights and establishing bike lanes.
Intelligence officers created a voluminous file on Norfolk-based People for the Ethical Treatment of Animals, calling the group a "security threat" because of concerns that members would disrupt the circus. Angry consumers fighting a 72 percent electricity rate increase in 2006 were targeted. The DC Anti-War Network, which opposes the Iraq war, was designated a white supremacist group, without explanation.
One of the possible "crimes" in the file police opened on Amnesty International, a world-renowned human rights group: "civil rights."
According to hundreds of pages of newly obtained police documents, the groups were swept into a broad surveillance operation that started in 2005 with routine preparations for the scheduled executions of two men on death row.
The operation has been called a "waste of resources" by the current police superintendent and "undemocratic" by the governor.
More
here.
Hat-tip: Pogo Was Right
Opinion: Be Wary of Using Military as Domestic Police

Gene Healy and Benjamin Friedman write in The OC Register:
The mainstream media has finally gotten around to reporting that the Pentagon has assigned active-duty troops to a homeland defense mission, a historical first. On Oct. 1, the 3rd Infantry Division's 1st Brigade Combat Team, freshly redeployed from Iraq, began a year-long assignment as a domestic "chemical, biological, radiological, nuclear or high-yield explosive Consequence Management Response Force," or CCMRF ("Sea-Smurf"). The 1st BCT is the first of three CCMRF teams, who will comprise 15,000-20,000 soldiers, according to the Army. The other two will come from the Army National Guard or reserves.
Neither the terrorist threat nor the hazards of bad weather require rethinking our traditional reluctance to use standing armies at home. We need not fear a coup, but we should worry about misusing our busy military for civilian tasks and developing an tendency to rely on the troops to answer every scare.
Initial reports were that the 1st BCT might be used to deal with civil unrest and crowd control, missions that would be in severe tension with the Posse Comitatus Act, the longstanding federal statute that restricts the president's ability to use the U.S. military as a domestic police force. In September, the Army Times described the unit's training as "the first ever nonlethal package that the Army has fielded," including beanbag bullets, Tasers and traffic roadblocks.
That report, along with the Bush administration's claim that the Constitution allows that president to use forces as he sees fit, no matter what Congress forbids, created well-founded fears that the CCMRFs first attack would be on Posse Comitatus. Yet Pentagon spokespeople deny that forces will be used for law enforcement purposes. And one suspects that the Bush administration's monarchial view of executive power will be out of fashion come January.
More
here.
Hat-tip: Radley Balko
Image source: PrisonPlanet.com
India: Infosys, Wipro Receive Threatening Terror e-Mails
Via The Hindustan Times.
Six prominent IT companies in the city, including Infosys and Wipro, have received e-mails threatening to blow up their buildings, a top police officer said in Bangalore on Sunday.
Joint Commissioner of Police B Gopal Hosur told PTI here that the companies received e-mails threatening to blow up their establishments two days ago and immediately informed the police.
The police have already begun investigations, he said, but did not divulge further details.
Link.
Image of The Day: Contents of The Toilet

Via GraphJam.
UK: Police Set to Step Up Hacking of Home PCs
David Leppard writes on The Times Online:
The Home Office has quietly adopted a new plan to allow police across Britain routinely to hack into people’s personal computers without a warrant.
The move, which follows a decision by the European Union’s council of ministers in Brussels, has angered civil liberties groups and opposition MPs. They described it as a sinister extension of the surveillance state which drives “a coach and horses” through privacy laws.
The hacking is known as “remote searching”. It allows police or MI5 officers who may be hundreds of miles away to examine covertly the hard drive of someone’s PC at his home, office or hotel room.
Material gathered in this way includes the content of all e-mails, web-browsing habits and instant messaging.
Under the Brussels edict, police across the EU have been given the green light to expand the implementation of a rarely used power involving warrantless intrusive surveillance of private property. The strategy will allow French, German and other EU forces to ask British officers to hack into someone’s UK computer and pass over any material gleaned.
More
here.
Idiocy in America: Amtrak Photo Contestant Arrested for Snapping Pictures of Amtrak Trains

Carlos Miller:
Armed with his Canon 5D and his new Lensbaby lens, photographer Duane Kerzic set out to win Amtrak’s annual photo contest this week, hoping to win $1,000 in travel vouchers and have his photo published in Amtrak’s annual calendar.
He ended up getting arrested by Amtrak police; handcuffed to a wall in a holding cell inside New York City’s Penn Station, accused of criminal trespass.
Kerzic says he was hardly trespassing because he was taking photos from the train platform; the same one used by thousands of commuters everyday to step on and off the train.
“The only reason they arrested me was because I refused to delete my images,” Kerzic said in a phone interview with Photography is Not a Crime on Friday.
“They never asked me to leave, they never mentioned anything about trespassing until after I was handcuffed in the holding cell.”
In fact, he said, the only thing they told him before handcuffing him was that “it was illegal to take photos of the trains.”
Obviously, there is a lack of communication between Amtrak’s marketing department, which promotes the annual contest, called Picture Our Trains, and its police department, which has a history of harassing photographers for photographing these same trains.
Much more
here.
Note: This is what Bruce Schneier calls the
"War on the Unexpected" -- people in positions of authority in this country have clearly lost their freekin' minds.
-ferg