Fergie's Tech Blog
Saturday, August 18, 2007
Cracker Group Arrested in Brazil
Marcelo Almeida writes on Zone-H News:
According to informations provided by the authorities, the Public prosecution service and the Civil Police had yesterday fulfilled 29 arrest warrants in three states at the south of Brazil.More here.
The group had 3 members in the state of Paraná, 1 in Santa Catarina and 25 in Rio Grande do Sul.
The Operation Nerd II, as it was nicknamed by the prosecutor of Porto Alegre, was divided in simultaneous actions carried out by four teams, with members of the Public prosecution service and the Civil Police.
The Public prosecution service calculated that the group has stolen more than R$ 10 million from bank accounts (over US$ 5 millions), they also seized all the goods belonging to the group.
Huge 'Cyber Probe' Into Glasgow Airport Attack
Richard Elias writes on News.Scotsman.com:
The investigation into the Glasgow Airport attack has become the biggest "cyber inquiry" conducted in Scotland.More here.
Hundreds of computers are being examined by experts trying to find clues to the origins of the plot.
Mobile and landline telephone traffic is also being examined.
The bungled airport raid on Saturday, June 30, came just over a day after two huge unexploded car bombs were discovered in London's West End.
It is believed the two incidents are linked, and the police were given a massive boost when they discovered mobile phones in both vehicles.
U.S. Toll in Iraq
As of Saturday, Aug. 18, 2007, at least 3,706 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,046 died as a result of hostile action, according to the military's numbers.More here.
The AP count is 8 higher than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
And as always, cryptome.org keeps a very, very extensive list here, as does the Iraq Coalition Casualty Count website here.
Lifting Corporate Fingerprints From the Editing of Wikipedia
Katie Hafner writes in The New York Times:
Last year a Wikipedia visitor edited the entry for the SeaWorld theme parks to change all mentions of “orcas” to “killer whales,” insisting that this was a more accurate name for the species.More here.
There was another, unexplained edit: a paragraph about criticism of SeaWorld’s “lack of respect toward its orcas” disappeared. Both changes, it turns out, originated at a computer at Anheuser-Busch, SeaWorld’s owner.
Dozens of similar examples of insider editing came to light last week through WikiScanner, a new Web site that traces the source of millions of changes to Wikipedia, the popular online encyclopedia that anyone can edit.
Concern Over Wider Spying Under New Law
James Risen and Eric Lichtblau write in The New York Times:
Broad new surveillance powers approved by Congress this month could allow the Bush administration to conduct spy operations that go well beyond wiretapping to include — without court approval — certain types of physical searches of American citizens and the collection of their business records, Democratic Congressional officials and other experts said.More here.
Administration officials acknowledged that they had heard such concerns from Democrats in Congress recently, and that there was a continuing debate over the meaning of the legislative language. But they said the Democrats were simply raising theoretical questions based on a harsh interpretation of the legislation.
They also emphasized that there would be strict rules in place to minimize the extent to which Americans would be caught up in the surveillance.
The dispute illustrates how lawmakers, in a frenetic, end-of-session scramble, passed legislation they may not have fully understood and may have given the administration more surveillance powers than it sought.
Terror Goes Digital. With Canadian Help.
Omar El Akkad writes in The Globe and Mail:
Welcome to Yarmouth, Nova Scotia – pivotal battleground in the global jihad.More here.
The town of 7,000 doesn't look the part. Its quietly beautiful downtown lives and dies by tourists. The coastline puts postcards to shame. The New York Islanders have held their training camp here for the past two years. But unwittingly, Yarmouth has become an example of the sort of unassuming places that are serving as relay stations in a virtual war.
The town is home to a branch of Register.com, one of its largest employers and one of the most popular Internet domain-name registration services in the world. For a fee, the company allows users to register website names – the .com, .net or .org addresses you type into your web browser to surf the Internet.
But for a few extra dollars, Register.com also offers an anonymous registration service: Try to find out who registered any one of these websites, and you'll be handed the same address and phone number in Yarmouth.
This service is hugely popular: Civil-liberties advocates and anyone else who values their privacy flock to it. But it's also very useful to another group of people, halfway around the globe: On one of the world's largest pro-Hamas websites, viewers can download martyrdom videos that feature the diatribes of masked men shortly before they launch deadly attacks. Look up the registration info for that site, and you'll get that Yarmouth address and phone number.
Image of the Day: Hurricane Dean

...from the International Space Station.
Image source: NASA / Space.com
Friday, August 17, 2007
FISA Court: U.S. Must Release Surveillance Records
An AP newswire article, via MSNBC, reports that:
The government must answer a watchdog group's demands to release records about the nation's classified terrorist spying program, the chief judge of a secretive national security court has ruled.More here.
The American Civil Liberties Union, which announced the order Friday, said it was the first time the Foreign Intelligence Surveillance Court had responded to a request filed by the public.
In her 2-page order, dated Aug. 16, Presiding Judge Colleen Kollar-Kotelly called the ACLU's demand "an unprecedented request that warrants further briefing."
San Francisco Court Allows AT&T Cell Phone Suit To Continue
An AP newswire article, via CBS5.com, reports that:
A lawsuit alleging that AT&T Inc.'s cell phone customers received deteriorated service after the company's wireless division was sold to Cingular Wireless can proceed as a class action, a federal appeals court ruled Friday.More here.
At issue was a clause in old Cingular contracts that forced customers to litigate their grievances independently, instead of grouping together for a class action lawsuit.
A three-judge panel in the 9th U.S. Circuit Court of Appeals ruled Friday that the contract was a violation of California law.
The ruling is further condemnation of so-called "class action waivers," which other courts have ruled illegally shield companies engaged in potentially harmful conduct.
U.S. Toll in Iraq, Afghanistan
Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Friday, Aug. 17, 2007, at least 3,705 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,046 died as a result of hostile action, according to the military's numbers.More here and here.
The AP count is 7 higher than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
As of Friday, Aug. 17, 2007, at least 357 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Aug. 11, 2007.
Of those, the military reports 236 were killed by hostile action.
And as always, cryptome.org keeps a very, very extensive list here, as does the Iraq Coalition Casualty Count website here.
Google Gadgets Can be Abused by Phishers
Robert McMillan writes on InfoWorld:
The domain used to host small Google Gadget applications written by Web developers could be misused by phishers, a Web security researcher said Friday.More here.
Google Gadgets are little programs that gather information on the Web and then display them on multiple Web pages. They are used to give Webmasters an easy way to display everything from sports scores to astronomical data on their sites.
Unfortunately, they can also be misused by phishers to get around antiphishing filters. Attackers could create a phishing site on the gmodules.com domain and then send that URL to victims. Because Google's gmodules.com domain is trusted by antiphishing filters, victims might then go to the phishing site without being warned by their browser's filtering software.
Security researcher Robert Hansen, a frequent critic of Google, reported the issue to the company's security team, but he was not satisfied with their response. He says Google told him that what he sees as a flaw is simply part of the site's expected behavior. Google couldn't be reached immediately for comment.
Quote of the Day: Tim Lee
"...not only is that false, but it’s so obviously false that the guy who wrote it is either an idiot or a liar. Before the bill passed, the Bush administration was required to get a warrant that named the specific individuals or facilities that would be monitored. Now, the administration only needs to submit an after-the-fact report describing the general contours of its monitoring program, but not naming specific targets. If that’s not a complete abandonment of the principles behind FISA, it’s hard to imagine what would be."
- Tim Lee, writing on The Technology Liberation Front.
Privacy Breaches Force Online Bill-Payment Company Out of Business
Ellen Messmer writes on NetworkWorld:
Small mistakes can have big consequences.More here.
Last April when a network technician working for Bellevue, Wash.-based Web content-management company Verus failed to set up a firewall properly as part of an online bill-payment service for hospitals, the mistake exposed patient data from at least a half-dozen hospitals across the country.
Until the mistake was discovered over a month later, patient information that had been stored by Verus on behalf of Concord Hospital in New Hampshire; St. Vincent Indianapolis Hospital in Indiana; Stevens Hospital in Edmonds, Wash.; and Sky Lakes Medical Center in Klamath Falls, Ore., among others, could be openly accessed on the Web. And it was, at least by Google bots that indexed it for search.
Civil Liberties Advocates Fear Abuse of Satellite Images
Eric Schmitt writes in The New York Times:
For years, a handful of civilian agencies have used limited images from the nation’s constellation of spy satellites to track hurricane damage, monitor climate change and create topographical maps.More here.
But a new plan to allow emergency response, border control and, eventually, law enforcement agencies greater access to sophisticated satellites and other sensors that monitor American territory has drawn sharp criticism from civil liberties advocates who say the government is overstepping the use of military technology for domestic surveillance.
“It potentially marks a transformation of American political culture toward a surveillance state in which the entire public domain is subject to official monitoring,” said Steven Aftergood, director of the Project on Government Secrecy for the Federation of American Scientists.
Russia: $1B Government Internet Program Launched
The Russian government has approved an electronic governance program developed by the Ministry of IT and Communications and the Ministry of Economic Development and Trade. The $1.3-billion program will allow the ten government services most frequently used by the public, such a ordering a passport, obtaining a driver's license and registering real estate, to be carried out online by 2010.More here.
Within the program, every federal and regional agency is to have a telephone service center, where the public will be able to receive information by phone, and a modernized website with detailed descriptions of the services available. A Russian federal portal will be formed in 2008. By the second stage of the program, in 2009, people will be able to file forms over the Internet using electronic signatures.
Feds Bust Identity Theft Ring That Targeted Forbes 400 Richest
Sharon Gaudin writes on InformationWeek:
Government authorities arrested and indicted five members of an alleged identity theft ring that was targeting billionaires from Forbes magazine's ranking of the 400 richest Americans.More here.
Manhattan District Attorney Robert M. Morgenthau announced on Thursday that the defendants -- four of whom were arrested Thursday and are in custody in Michigan, Texas, Florida and Kentucky -- have been charged with stealing $1.5 million and attempting to steal another $10.7 million from their victims' financial accounts. Another defendant, Igor Klopov, was arrested in May and is in custody in New York.
Klopov, a 24-year-old Russian, was the alleged ring leader who mined the Internet to obtain victims' personal identifying information. The DA's office in Manhattan reported that he was arrested in May after he came to New York to claim $7 million in gold that he thought had been purchased with money stolen from one of his victims.
Infected Job Search Sites Lead to Info Theft for 46,000
Jaikumar Vijayan writes on ComputerWorld:
A security researcher at SecureWorks Inc. has uncovered a cache of financial and personal data that was stolen from about 46,000 individuals by a variant of Prg, a Trojan program gaining notoriety for its quick-change behaviors.More here.
The stolen data includes bank and credit card account information and Social Security numbers as well as usernames and passwords for online accounts. Many of the victims were infected and reinfected as they visited several leading online job search sites, including the popular Monster.com.
Don Jackson, the SecureWorks researcher who found the collection, said it was the largest single cache of data he discovered from the Prg Trojan, a piece of malware first seen in the wild in June. According to Jackson, the server he examined is still collecting stolen data, with up to 10,000 victims feeding it information at any particular time.
Websense: Indian Syndicate Bank Website Compromised
Websense® Security Labs™ has discovered that the official site for Indian Syndicate Bank (www.syndicatebank.in) was compromised with a malicious script that attempts to exploit multiple vulnerabilities. When customers visit the Web site, a malicious JavaScript file is executed and creates two additional iframes in the page.More here.
The JavaScript [...] creates two new IFRAME elements within the page. One IFRAME attempts to load exploit code and the other creates several additional IFRAMEs that contain advertisement-related content. The exploit will try to load a Trojan Downloader which will contact a remote server to download the following Trojan Downloader and Backdoor.
The site appears to have been cleaned a few hours ago.
Image source: Websense Security Labs
DoS Vulnerability in Cisco IOS Compromises the Routers of ISPs
A denial of service vulnerability in Cisco's IOS network operating system can be exploited to reboot ISP routers. The problem arises when processing the "show ip bgp regexp" command if certain regular expressions are used as arguments. As a result, the router reboots and has to rebuild its BGP routing table. If this occurs several times in succession, resulting in a route becoming unavailable repeatedly, the router may be ignored by other providers for a certain amount of time as a result. This would cause a provider's network to become unavailable.More here.
Usually, every ISP provides public route servers or route monitors which are accessible to anyone via Telnet and can be used to execute the command in question. Route servers are used for retrieving the routing information between ISPs. Apart from Telnet access, some providers also allow access via the Looking Glass web interface, which is basically a Telnet wrapper and can also be exploited to transfer crafted parameters to a router.
Although this vulnerability is very easily exploited, its scope is difficult to assess. Large ISPs use dedicated route server systems which only return information but are not used for routing. Things may be different for smaller providers who process everything on the same system in order to be cost-efficient. In addition, a Looking Glass server can access a large ISP's core router, which creates an indirect vulnerability.
According to reports, no updated IOS version has so far become available and Cisco has not yet released any information about this problem through official channels. As a workaround solution, some ISPs have started to filter out specific regular expressions on the Looking Glass servers. With Telnet access it is allegedly sufficient to disable the "show ip bgp regexp" command.
Administrators should implement the workaround solutions as soon as possible since detailed information about this vulnerability is already being circulated on various IRC channels.
NOTE: Anyone with additional information on this please leave a comment. Likewise, if I discover additional information, I will update this blog entry. I do not see any mention of this yet on the Cisco Systems Security Advisories page. - ferg
U.S. Army Reports Brass, Not Bloggers, Breach Security
Noah Shachtman writes on Wired News:
For years, the military has been warning that soldiers' blogs could pose a security threat by leaking sensitive wartime information. But a series of online audits, conducted by the Army, suggests that official Defense Department websites post material far more potentially harmful than anything found on a individual's blog.More here.
The audits, performed by the Army Web Risk Assessment Cell between January 2006 and January 2007, found at least 1,813 violations of operational security policy on 878 official military websites. In contrast, the 10-man, Manassas, Virginia, unit discovered 28 breaches, at most, on 594 individual blogs during the same period.
The results were obtained by the Electronic Frontier Foundation, after the digital rights group filed a lawsuit under the Freedom of Information Act.
Thursday, August 16, 2007
Yeah, That'll Help: Diebold to Change Its Name
Kin Zetter writes on Threat Level:
Is it possible that John Borland's story this week about Diebold employees scrubbing the company's Wikipedia page was the final straw?More here.
Not likely. But today Diebold, a company once known primarily for making safes and ATMs, announced that it has decided to put some distance between it and its beleaguered voting machine division -- Diebold Election Systems Inc, (aka DESI), which the company purchased from Global Election Systems in 2002.
U.S. Toll in Iraq
As of Thursday, Aug. 16, 2007, at least 3,703 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,036 died as a result of hostile action, according to the military's numbers.More here.
The AP count is 15 higher than the Defense Department's tally, last updated Thursday at 10 a.m. EDT.
And as always, cryptome.org keeps a very, very extensive list here, as does the Iraq Coalition Casualty Count website here.
71% Increase in Slammer Activity Since Yesterday?
Oh, it's just China. :-)
I just had to point this out.
The folks over at Arbor do a great job, by the way.
- ferg
Image source: Arbor Networks
San Francisco Surveillance Cameras Fail To Curb Crime
An AP newswire article, via CBS5.com, reports that:
An arsenal of surveillance cameras posted at San Francisco housing projects have failed to lead to a single homicide arrest even though about one-quarter of the city's murders happen on public housing property, according to city officials.More here.
The San Francisco Housing Authority has installed 178 cameras on its properties over the past two years, but they are not regularly monitored, officials said at a hearing held this week by the Board of Supervisors' public safety committee. Instead, video shot by the cameras is only viewed if requested by police.
The city of San Francisco has 70 other cameras installed at high crime areas around the city that are similarly unmonitored.
Even when the cameras do catch crimes being committed, the footage can be so grainy that the videos don't always yield usable details, especially at night when most crimes occur, police homicide Lt. John Murphy said.
North Korea to Connect Itself to the Rest of the World - UPDATE
There is reporting in the Korean press, mostly in Korean, that North Korea is set to connect its internal internet to the global internet. In November, the Korea Times reports (in English) that ICANN is expected to approve North Korea’s ccTLD of “kp”.More here.
According to a professor at Dongguk University, Koh Yoo-hwan, “Kim Jong-il has great interest in the information technology sector.” Further, Pyongyang “has kept its network closed from the outside because it was concerned about the Web’s possible influence on its regime. But if it wants to come out to the international society, it is inevitable to utilize the Internet, first of all.”
UPDATE: 19:50 PDT, 17 August 2007: ICANN has release a formal statement in this issue, basically saying that it has indeed recieved a request for this ccTLD delegation, but has not made a decision yet. More here.
Human Error Limits Schwab Website Capacity
Clients of Charles Schwab Corp. using the discount brokerage's Web site and phone systems to trade on Thursday may have had trouble accessing their accounts due to an error that restricted system capacity.More here.
The error was fixed at 12:10 p.m, PDT (1900 GMT), and customers can now access their accounts normally, Schwab spokesman Greg Gable said.
Gable said it was human error that caused the San Francisco-based brokerage's Web site to slow down, beginning at 9:45 a.m., Pacific time.
He declined to provide details on the nature of the error or the number of clients affected.
Quote of the Day: Patti Davis
"It was bound to happen. Now even a frown or grimace can get you into trouble with The Man."
- Patti Davis, in an commentary over on Newsweek.
Automated Solutions From IBM/Lenovo Creates Vulnerability
The Automated Solutions software package from IBM/Lenovo, which supports web-interactive system diagnostics and optimisation, introduces a security vulnerability. The software installs an ActiveX module containing vulnerabilities that may allow attackers to inject and execute remote code via specially crafted websites. An update to eliminate the problem is available.More here.
US-CERT has reported multiple security vulnerabilities in the acpRunner ActiveX component, which is contained in the AcpController.dll library. Its function is to download, extract and run software. acpRunner incorrectly verifies digital signatures in downloaded software, possibly allowing attackers to download arbitrary program code onto the computer. The module also contains a format string vulnerability that can be exploited to execute remote code using specially crafted request parameters in websites. Since the module does not verify the domain from which the software originates, attackers can exploit the vulnerabilities from arbitrary websites.
Off Beat: Coming To A Checkpoint Near You... New TSA Uniforms
The Transportation Security Administration thinks it has found the answer to some of the agency's biggest problems... including its failure to retain personnel, persistent equipment troubles, missing hard drives containing personal data, and security breaches.More here.
Why, new uniforms, of course.
Image source: Aero-Net News
UK: ISPs Panicked by MS Patch Tuesday
Chris Williams writes on The Register:
ISP group 186K has blamed potential congestion on its network this week on bandwidth being swallowed by Microsoft's monthly security patch update.More here.
Redmond unleashed six critical fixes on Tuesday.
186K's engineers first suspected a new virus, according to the firm's status page, but later on Wednesday morning said it was because its network had struggled with the larger than normal update.
Visa Relaxes Retail Credit Card Security Threats
A Ziff Davis Internet article by Evan Schuman, via eWeek, reports that:
For more than a year, Visa has ominously warned large retailers that it would enforce a strict Sept. 30 deadline for many of the nation's largest retailers to either be certified that they comply with industry credit card security requirements or face fines and expulsion from discounted credit card fee programs.More here.
But as the deadline has gotten closer—and the percentage of retailers certified as compliant is still quite low—Visa has been forced to back off, albeit slightly.
In an attempt to boost the number of Level 1 retailers certified compliant with the PCI DSS (Payment Card Industry Data Security Standard, often referred to simply as PCI), Visa in December unveiled a series of incentives to convince retailers into cooperating, given the lack of success that the threat of fines was having.
A big part of those incentives was offering compliant retailers sharply discounted credit card transaction fees in a program called the Visa PCI CAP (Compliance Acceleration Program).
This month, Visa has been quietly floating memos that will soften the pain for non-compliant retailers, as it's become clear that non-compliants will have strength in numbers come early October.
Wednesday, August 15, 2007
U.S Toll In Iraq
As of Wednesday, Aug. 15, 2007, at least 3,700 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,036 died as a result of hostile action, according to the military's numbers.More here.
The AP count is 12 higher than the Defense Department's tally, last updated Wednesday at 10 a.m. EDT.
And as always, cryptome.org keeps a very, very extensive list here, as does the Iraq Coalition Casualty Count website here.
Is The Bush Administration Still Spying?
Probably yes.
David Kravets writes on Threat Level:
Is the Bush administration secretly siphoning millions of calls and e-mail communications from AT&T's network?More here.
That fundamental question was left unanswered after 2.5 hours of oral arguments before a three-judge panel of the 9th U.S. Circuit Court of Appeals, which the government asked Wednesday to dismiss lawsuits making those and other allegations.
Maybe the San Francisco-based court will take the government's side or maybe it won't. But one thing is certain: if there was or is wholesale electronic spying on Americans without warrants, the courts aren't about to step in and stop it any time soon. That's because the 9th U.S. Circuit Court of Appeals, the nation's largest federal appellate court, isn't likely to rule for months or more. And the outcome isn't likely to be settled for perhaps years.
FISA Redux in the Works?
Rebecca Carr writes on Window on Washington:
Senate Majority Leader Harry Reid, D-Nev., all but admits today that it was a mistake to give the Bush White House expanded surveillance powers before lawmakers raced out of town earlier this month.More here.
In a letter to Senate Intelligence Committee Chairman John Rockefeller, D-West Va., and Senate Judiciary Committee Chairman Patrick Leahy, D-Vt., Reid urges the chairmen to quickly pass new legislation this fall that “better serves American national security interests and comports with the Constitution and proper judicial and congressional oversight.”
Cutting to the chase of his letter: the rush to revamp the 1978 Foreign Intelligence Surveillance Act was too hurried and overlooked important constitutional considerations. Congressional oversight needed pronto.
Appeals Court May Let NSA Lawsuits Proceed
Declan McCullagh writes on C|Net News:
A federal appeals court on Wednesday appeared unwilling to end a pair of lawsuits that claim the Bush administration engaged in widespread illegal surveillance of Americans.More here.
The 9th U.S. Circuit Court of Appeals repeatedly pressed Gregory Garre, the Bush administration's deputy solicitor general, to justify his repeated requests to toss out the suits on grounds they could endanger national security by possibly revealing "state secrets."
Judge Harry Pregerson wondered: "We just have to take the word of members of the executive branch that it's a state secret. That's what you're saying, isn't it?"
A moment later Judge Michael Hawkins suggested that granting the request could "mean abdication" of our duties.
NOTE: Also, the good folks over at THREAT LEVEL has also been live-blogging the court proceedings highlights today here.
News of the Weird: Chinese Online Anti-Corruption Computer Game Overloaded
The official website of "Incorruptible Warrior", an online game which was jointly launched by Ningbo Haishu District Discipline Inspection Commission and Haishu District Ximen Street Party Working Committee earlier this month, has announced its shutdown.More here.
According to a Donews.com report, the content of the website will be moved to other websites that have not yet been specified in accordance with a notice from relevant government departments.
The Chinese media report that attracted by the theme of the game, more users registered to play it than expected, which brought a heavy burden to the server that hosts the game. However, from the very beginning, some players criticized the game saying it was produced unprofessionally and the story was sparse.
It is still unclear if and when the game will open up again.
The Internet is 'The New Afghanistan': NYC Police Commissioner
The Internet is the new battleground against Islamist extremism because it provides ideology that could radicalize Westerners who might then initiate home-grown attacks, New York police commissioner Raymond Kelly said on Wednesday.More here.
"The Internet is the new Afghanistan," Kelly said, as he released a New York Police Department (NYPD) report on the home-grown threat of attacks by Islamist extremists. "It is the de facto training ground. It's an area of concern."
C|Net Reporters Sue HP for Invasion of Privacy
Greg Sandoval writes on C|Net News:
The fallout from Hewlett-Packard's boardroom leak scandal continued Wednesday as three CNET News.com reporters sued the computer maker, alleging that its investigation tactics amounted to an invasion of privacy and a violation of state rules on business practices.More here.
Complaints were filed on behalf of reporters Dawn Kawamoto, Stephen Shankland and Tom Krazit in California Superior Court for the County of San Francisco. Kawamoto's husband, plus Shankland's wife and parents, also filed their own suits Wednesday, according to court documents. All seek unspecified damages.
An HP representative did not immediately comment on the suits.
ACLU: Patriot Act, NSL Gag Power is Unconstitutional
The American Civil Liberties Union appeared before a federal district court today to argue that the reauthorized Patriot Act's National Security Letter (NSL) provision is unconstitutional. The law permits the FBI to gag those who receive NSLs from disclosing that the FBI has sought or obtained information from them.More here.
The case before the court today, Doe v. Gonzales, was originally filed in April 2004 on behalf of an anonymous Internet access company that had received an NSL. Although the FBI has since dropped its NSL demand, the John Doe remains under a gag order. In September 2004, Judge Victor Marrero of the U.S. District Court for the Southern District of New York struck down the Patriot Act NSL provision as unconstitutional, writing that "democracy abhors undue secrecy." The landmark ruling held that permanent gag orders imposed under the NSL law violated free speech rights protected by the First Amendment.
Ubuntu Servers Hijacked, Used to Launch Attack
Lisa Vaas writes on eWeek:
The Ubuntu community had to yank five of the eight Ubuntu-hosted community servers sponsored by Canonical offline Aug. 6 after discovering that the servers had been hijacked and were attacking other machines.More here.
It was suggested during an IRC (Internet relay chat) meeting of the Ubuntu colocation team Aug. 14 that the source of the troubles might have been a Chinese IP address trying to log onto the servers by brute force "for a long time now it seems," said a participant.
On Aug. 14, the community began to bring the machines back up in a safe state so that they could recover data from them. Unfortunately, according to Ubuntu Community Manager Jono Bacon, the servers were all found to be out of date, stuffed with Web software, and missing security patches—at least in the instances where it was easy to determine what version they're running.
LAX Outage is Blamed on a Single Computer
Tami Abdollah writes in The Los Angeles Times:
U.S. Customs officials said Tuesday that they had traced the source of last weekend's system outage that left 17,000 international passengers stranded in airplanes to a malfunctioning network interface card on a single desktop computer in the Tom Bradley International Terminal at LAX.More here.
The card, which allows computers to connect to a local area network, experienced a partial failure that started about 12:50 p.m. Saturday, slowing down the system, said Jennifer Connors, a chief in the office of field operations for the Customs and Border Protection agency.
As data overloaded the system, a domino effect occurred with other computer network cards, eventually causing a total system failure a little after 2 p.m., Connors said.
"All indications are there was no hacking, no tampering, no terrorist link, nothing like that," she said. "It was an internal problem" contained to the Los Angeles International Airport system.
The system was restored about nine hours later, only to give out again late Sunday for about 80 minutes, until about 1:15 a.m. Monday. The second outage was caused by a power supply failure, Connors said. But customs officials are investigating whether the Saturday incident may have played a role in Sunday's outage.
U.S. to Expand Domestic Use Of Spy Satellites
Robert Block writes on WSJ.com:
The U.S.'s top intelligence official has greatly expanded the range of federal and local authorities who can get access to information from the nation's vast network of spy satellites in the U.S.More here.
The decision, made three months ago by Director of National Intelligence Michael McConnell, places for the first time some of the U.S.'s most powerful intelligence-gathering tools at the disposal of domestic security officials. The move was authorized in a May 25 memo sent to Homeland Security Secretary Michael Chertoff asking his department to facilitate access to the spy network on behalf of civilian agencies and law enforcement.
Until now, only a handful of federal civilian agencies, such as the National Aeronautics and Space Administration and the U.S. Geological Survey, have had access to the most basic spy-satellite imagery, and only for the purpose of scientific and environmental study.
According to officials, one of the department's first objectives will be to use the network to enhance border security, determine how best to secure critical infrastructure and help emergency responders after natural disasters. Sometime next year, officials will examine how the satellites can aid federal and local law-enforcement agencies, covering both criminal and civil law. The department is still working on determining how it will engage law enforcement officials and what kind of support it will give them.
(Hat-tip, rms.)
Tuesday, August 14, 2007
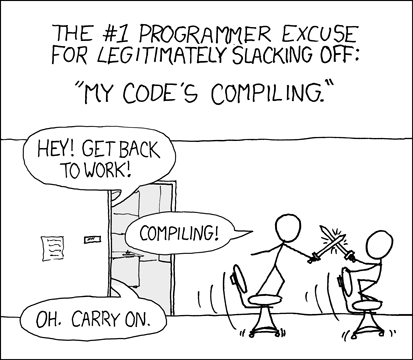
xkcd: Compiling
We love xkcd.
(This one immediately made me think of Valdis. :-)
Is InfoWorld After My Privacy? Or Worse?

Tom Sanders writes on Silicon Valley Sleuth:Infoworld seems to be breaking new ground, but not in any good way.
More here.
Looking at the main page at InfoWorld, it's chock (and I mean chock) full of JavaScript:
This is bad -- and I'll tell you why in one sentence (or maybe two).
By forcing users to allow JavaScript to "experience" the "feature-rich content" hosted on websites like this, it forces the ordinary Internet user to allow themselves to be victimized by nefarious websites containing malicious JavaScript.
Sure, there are great tools -- like NoScript for Firefox -- which allow users to selectively determine which sites to allow JavaScript functionality, but the average Internet user is most likely going to get burned because of this "Tragedy of the Commons".
- ferg
Company Sells Cell Phone Numbers and Other Personal Information
Home phone numbers have been available to the public for a long time, so many Americans treasure the fact that their cell numbers can be kept private -- or so they think. Now, all it takes is a few bucks and Internet access to find tens of millions of personal cell phone numbers.More here.
A Web site named Intelius has created a clearinghouse of cell phone numbers that can be purchased online for $15 each. Its source -- every business and company you've ever provided with your personal information.
"We do pay for the data, everything from government agencies to third party companies, where we compile a lot of this information together," said Ed Peterson, vice president of sales and marketing at Intelius.
Intelius already has 90 million cell phone numbers, and it's adding 70 million more in the coming days, along with the addresses that go with them.
TJX Profit Down Sharply on Breach Costs
An AP newswire article by Mark Jewell, via The Seattle-Post Intelligencer, reports that:
TJX Cos. on Tuesday said its second-quarter profit was cut by more than a half as the discount store operator recorded a $118 million charge because of costs from a massive breach of customer data, mostly to build up a reserve to cover estimated future expenses.More here.
The owner of about 2,500 stores including T.J. Maxx and Marshalls also expects to record future breach-related charges of an additional $21 million - costs that analysts said are easily manageable for a firm posting strong sales despite the data theft and tough times for retailers.
Off Beat: Coders Crack Secret of 'San Jose Semaphore' on Adobe Building - UPDATE

Sal Pizarro writes on The Mercury News:
San Jose scientists Bob Mayo and Mark Snesrud have been revealed as the two best cyber-sleuths in Silicon Valley. The pair each cracked the code of the San Jose Semaphore, which has been perplexing commuters and downtown visitors since its bright yellow wheels started spinning atop the Adobe building last August.More here.
Mayo and Snesrud are being honored at a news conference this afternoon at San Jose City Hall. At the event, Mayor Chuck Reed and City Councilman Sam Liccardo will reveal what the code says.
Perhaps another secret will be revealed, too: Just how much time did Mayo and Snesrud spend obsessing over the art project's spinning disks and just what do they do that gives them that much free time?
Note: Watch this space. When I find out what it means, I'll post a link. - ferg
UPDATE: 18:13 PDT: "The four, 10-foot-wide illuminated amber circles were revealing text from the 1960's book, "The Crying of Lot 49" by Thomas Pynchon." Details here.
Know Your Enemy: Malicious Web Servers
Very nice paper from the good folks over at the Honeynet Project.
The Honeynet Project & Research Alliance are excited to announce the release of a new paper in our Know Your Enemy series, "KYE: Malicious Web Servers" [.pdf]. In this paper, we take an in-depth look at malicious web servers that attack web browsers, and we evaluate several defensive strategies that can be employed to counter this threat of client-side attacks.More here.
All the malicious web servers identified in this study were found with our client honeypot Capture-HPC.
Patch Tuesday: Microsoft Fixes 14 Software Security Flaws
Brian Krebs writes on Security Fix:
Microsoft today released software updates to plug at least 14 security holes in computers powered by its different versions of Windows operating system and other software. The updates are available from the Microsoft Update Web site or via Automatic Updates.More here.
Windows XP users can expect to install at least six updates from today's patch batch, and more if they have any version of Microsoft Office installed. Office 2000 users will need to make a separate trip over to the Office Update site to scan for and download additional fixes not offered via Microsoft Updates.
Included in this month's Patch Tuesday lineup are several fixes for bugs in Internet Explorer. Specifically, Microsoft plugged at least three vulnerabilities in IE that could allow nasty Web sites to install software just by convincing users to come by for a visit.
Monday, August 13, 2007
Who's Editing Wikipedia? Diebold, the CIA, Political Campaigns, etc.
John Borland writes on Wired News:
On November 17th, 2005, an anonymous Wikipedia user deleted 15 paragraphs from an article on e-voting machine-vendor Diebold, excising an entire section critical of the company's machines. While anonymous, such changes typically leave behind digital fingerprints offering hints about the contributor, such as the location of the computer used to make the edits.More here.
In this case, the changes came from an IP address reserved for the corporate offices of Diebold itself. And it is far from an isolated case. A new data-mining service launched Monday traces millions of Wikipedia entries to their corporate sources, and for the first time puts comprehensive data behind longstanding suspicions of manipulation, which until now have surfaced only piecemeal in investigations of specific allegations.
Australia: Web Porn Blocking Sparks War of Words
Jo Best writes on ZDNet Australia:
The government and its Labor rivals have been indulging in a slanging match over the Coalition's plans to introduce Internet porn blocking software.More here.
Communications Minister Helen Coonan has slammed the Labor party's plans for mandatory ISP-level filtering which would see service providers forced to block pornographic content over Internet connections to households, schools and libraries.
Russian Cyber Attack Imminent!
Just kidding.
Well, kind of.
As some security folks like to dismiss the fact that Russian crimeware activity is indeed on the rise, I will stand by my ongoing assessment that the problem is bad, getting worse, and is worse yet that it is made more insidious by the fact that it is silent (and again, that other security folks dismiss it off-hand).
Make no mistake: There is an active and ongoing attempt by Russian malware suspects to separate you from your money -- and it is getting worse every day.
These people operate with virtual impunity -- this is an underground criminal financial operation that is thriving.
Pretending it isn't a problem flies in the face of reality.
And yes -- it's getting worse.
$.02,
- ferg
Off Beat: New Surprises About ES&S Touch-Screens
Kim Zetter writes on Threat Level:
Who would have thought that Manila sweatshops would figure prominently in the manufacture of U.S. voting machines?More here.
It turns out that Election Systems & Software, one of the top voting machine companies in the country, has its machines assembled in a Philippines sweatshop.
Lawsuits May Illuminate Methods of Spy Program
Dan Eggen writes in The Washington Post:
In 2003, Room 641A of a large telecommunications building in downtown San Francisco was filled with powerful data-mining equipment for a "special job" by the National Security Agency, according to a former AT&T technician. It was fed by fiber-optic cables that siphoned copies of e-mails and other online traffic from one of the largest Internet hubs in the United States, the former employee says in court filings.More here.
What occurred in the room is now at the center of a pivotal legal battle in a federal appeals court over the Bush administration's controversial spying program, including the monitoring that came to be publicly known as the Terrorist Surveillance Program.
Where is Security Going?
Richard Stiennon writes on the ZDNet "Threat Chaos" Blog:
Or more specifically, where is the security industry going?More here.
Change in the security space is, as always, driven by threats. The threats are growing on the criminal as well as state sponsored fronts. What does that mean for the industry?
Note: I have a tendency to agree with much of what Richard outlines here... - ferg
U.S. Toll in Iraq, Afghanistan
Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Monday, Aug. 13, 2007, at least 3,691 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,030 died as a result of hostile action, according to the military's numbers.More here and here.
The AP count is 13 more than the Defense Department's tally, last updated Monday at 10 a.m. EDT.
As of Monday, Aug. 13, 2007, at least 356 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Aug. 4, 2007.
Of those, the military reports 235 were killed by hostile action.
And as always, cryptome.org keeps a very, very extensive list here, as does the Iraq Coalition Casualty Count website here.
AT&T Admits It Censored Other Bands
Marguerite Reardon writes on the C|Net News Blog:
It looks like Pearl Jam isn't the only band that has had its politically charged comments bleeped from concerts streamed from AT&T's Blue Room Web site.More here.
AT&T issued a statement on Friday admitting that this kind of thing has happened before. And the company once again apologized.
"It's not our intent to edit political comments in Webcasts on attblueroom.com," the company said in a statement. "Unfortunately, it has happened in the past in a handful of cases. We have taken steps to ensure that it won't happen again."
Exactly how many performances have been edited is unknown. AT&T hasn't specified. Nor has it said what exactly it's doing to ensure that this won't happen again.
Quote of the Day: Christopher Bolin
"Although I would agree there is a lot of malware out there that is reusing code and techniques, I do not agree that anti-virus vendors are gaining the upper hand."
- Christopher Bolin, Executive Vice President and Chief Technology Officer at McAfee, writing on their Security Insights blog.
UK: ISPs Warn BBC Over iPlayer Plans
Andrew Murray-Watson writes in The Independent:
Some of the largest broadband providers in the UK are threatening to "pull the plug" from the BBC's new iPlayer unless the corporation contributes to the cost of streaming its videos over the internet.More here.
The likes of Tiscali, BT and Carphone Warehouse are all growing concerned that the impact of hundreds of thousands of consumers watching BBC programmes on its iPlayer – which allows viewers to watch shows over the internet – will place an intolerable strain on their networks.
Some of the companies involved have told the BBC that they will consider limiting the bandwidth available to iPlayer – a process known as traffic shaping. The measure would limit the number of consumers who could access the iPlayer at any one time.
Editorial: ICANN's WHOIS Policy Shift Would Be Criminal Negligence
Mark Hall writes on ComputerWorld:
There’s a move afoot to help criminals obscure their illegal online activities. The Internet Corporation for Assigned Names and Numbers (ICANN) is considering making it possible for anyone to avoid putting Web site ownership and contact information into the Internet’s WHOIS database.More here.
This seemingly minor change to the already loose requirements for Web site registration is being advocated by an unholy alliance of privacy ideologues, primarily in the European Union, and greedy Internet service providers. The former group argues that the less that is known about a Web site owner, the better that person’s rights are protected. The ISPs supporting the change see it as a way to generate more business, though most of it is likely to be from crooks who, ironically, rip off Internet users by violating their privacy.
German Anti-Hacking Law Arrives
Robert Lemos writes on SecurityFocus:
Security researchers in Germany continued to pull down exploit code from their sites last week, scrambling to comply with a German law that makes illegal the distribution of software that could be used to break into computers.More here.
The German law -- referred to as 202(c) -- went into effect on Sunday. Many experts have complained that the language of the law is very unclear, but a strict reading appears to make illegal the distribution, sale and possession of security tools which could be used to commit a crime.
In the latest move, PHP security professional Stefan Esser removed on Friday all exploit code from his Web site dedicated to the Month of PHP Bugs. While reasonable prosecutors would not likely pursue security researchers, the risk is too great, Esser stated.
Upkeep Of Security Devices A Burden for U.S. Gov
Mary Beth Sheridan writes in The Washington Post:
In 2003, the FBI used a $25 million grant to give bomb squads across the nation state-of-the-art computer kits, enabling them to instantly share information about suspected explosives, including weapons of mass destruction.More here.
Four years later, half of the Washington area's squads can't communicate via the $12,000 kits, meant to be taken to the scene of potential catastrophes, because they didn't pick up the monthly wireless bills and maintenance costs initially paid by the FBI. Other squads across the country also have given up using them.
Sunday, August 12, 2007
Microsoft Disputes FCC's Rejection of Web Devices That Use TV Airwaves
Kim Hart writes in The Washington Post:
Today Microsoft plans to try to convince regulators that it can connect consumers to high-speed Internet over unused television airwaves without interfering with existing broadcasts.More here.
In a document that it plans to file today with the Federal Communications Commission, Microsoft disputes the agency's recent findings that prototype devices either interfered with TV signals or could not detect them to avoid interference. Microsoft's first prototype was defective, but the firm said another model worked successfully in a demonstration it gave to the FCC last week.
The filing is Microsoft's latest attempt to get FCC commissioners to approve a plan that would let a new generation of portable wireless devices connect to the Internet without relying on existing wireless carriers. The devices in question, which were designed and made by Microsoft, would use vacant TV airwaves, known as white space, to carry Internet service to homes and offices, including those in rural areas. The airwaves will be available when TV broadcasters move to digital signals in early 2009.
U.S. Toll in Iraq, Afghanistan
Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Sunday, Aug. 12, 2007, at least 3,690 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,030 died as a result of hostile action, according to the military's numbers.More here and here.
The AP count is 12 more than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
As of Sunday, Aug. 12, 2007, at least 356 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures August 4, 2007.
Of those, the military reports 235 were killed by hostile action.
And as always, cryptome.org keeps a very, very extensive list here, as does the Iraq Coalition Casualty Count website here.
14 Hours Later, LAX Clears Last Stranded Passengers
Ari Bloomekatz, Rong-Gong Lin II, and Deborah Schoch write in The Los Angeles Times:
Thousands of international passengers stranded for hours on planes and in packed holding areas at Los Angeles International Airport on Saturday have now cleared customs. But officials have not explained what caused a computer malfunction that left them unable to process the travelers' entry into the country.This article goes on to say that "The computer system maintains a list of people who should be subject to secondary searches upon entering the country..."
The U.S. Customs and Border Protection system went down around 2 p.m., forcing some planes to sit on the tarmac for so long that workers had to refuel them to keep their power units and air conditioning running. Maintenance workers ran trucks around the airport hooking up tubes to service lavatories.
Just after midnight Saturday, Tom Winfrey, a spokesman for Los Angeles World Airports, said the computer system was up and running. Processing passengers through customs took several hours after that.
More here.
Biggest. Domain. Tasting. Day. Ever.
Jay Westerdal writes on The DomainTools Blog:
More here.
Today was the largest Domain Tasting day ever. We recorded over 8 Million Transactions today. This is a new high. We have never seen 8 Million transactions on one day before. That would be either an add or delete. Over 99 percent of these transactions are completely free and use the 5 day grace period to test domain names for traffic before they are purchase for a long term buy. Sometimes organizations will taste a domain name for multiple 5 day windows. They can tie up a domain for a long time and test it longer.
Domain Tasting seems to be getting worse, the number of transactions continues to grow.