Zambia's Leading ISP Hacked
 Screenshot of the defaced website, www.zamnet.zm.
Screenshot of the defaced website, www.zamnet.zm.
Via The Laska Times.
ZAMNET, Zambia’s leading Internet Service Provider has been Hacked. The site was hacked Saturday afternoon and at the time of writing the site had not been fixed. The Hackers who are calling themselves 3RqU (Turkish) have changed ZAMNETs landing page. 3RqU Turkish are a known notorious group of hackers.
The hackers have gained unauthorised access to ZAMNET servers. According to the new landing page that has been put on ZAMNET, the hackers claim to have root access. Root access grants someone the ability to control all the resources on a server.With this access hackers can for example delete the whole server, read all confidential information on the server or make alterations to site.
Most of the websites hosted by ZAMNET have been affected by this security breach and these include sites like Times of Zambia, Daily mail, ZNBC.
More
here.
Props: Pogo Was Right
Middle East Submarine Cable SMW-4 Cut Again After Being Restored
Via The Jordan Times.
Internet users in the Kingdom and elsewhere in the region are expected to continue experiencing slower services as repair teams continue their attempts to fix cut cables in the Mediterranean.
Raslan Diranieh, chief financial officer of the Jordan Telecom Group (JTG), said that a few hours after SMW-4 Internet cable which links the Kingdom to the International Internet Network was fixed, it experienced another cut on Saturday.
“The mother company was supposed to complete repairing SMW-3 and SMW-4 on Saturday… but SMW-4, which is one of the Jordan’s main providers, was broken again,” Diranieh told The Jordan Times, adding that JTG has received no further information on when the line would be refixed.
Internet users in the country have experienced slower connection to the World Wide Web over the past eight days due to breaks in three submarine cables linking Europe and the Middle East.
The cut occurred in the SMW-3, SMW-4 and FLAG lines, the latter two of which link the Kingdom to the global network.
More
here.
Hat-tip: Marty
U.S. Toll in Iraq, Afghannistan

Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Friday, Dec. 26, 2008, at least 4,217 members of the U.S. military had died in the Iraq war since it began in March 2003, according to an Associated Press count.
The figure includes eight military civilians killed in action. At least 3,398 military personnel died as a result of hostile action, according to the military's numbers.
The AP count is three higher than the Defense Department's tally, last updated Wednesday at 10 a.m. EST.
As of Friday, Dec. 26, 2008, at least 558 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Wednesday at 10 a.m. EST.
Of those, the military reports 405 were killed by hostile action.
More
here and
here.
And as always, the
Iraq Coalition Casualty Count keeps the grim watch on their website
here.
Honor the Fallen.
Bush Administration Data Treatens To Overload Archives
A New York Times article by Robert Pear and Scott Shane, via The Mercury News, reports that:
The National Archives has put into effect an emergency plan to handle electronic records from the Bush White House amid growing doubts about whether the agency's new $144 million computer system can cope with the vast quantities of digital data it will receive when President Bush leaves office Jan. 20.
The technical challenge was an inevitable result of the explosion in cybercommunications, which will make the electronic record of the Bush years about 50 times as large as that left by the Clinton White House in 2001, archives officials estimate. The collection will include top secret e-mail messages tracing plans for the Iraq war as well as footage from the likes of Barney Cam 2008, a White House video featuring the First Pet.
Under federal law, the government has "complete ownership, possession and control" of presidential and vice-presidential records. The moment Bush leaves office, the National Archives becomes legally responsible for "the custody, control and preservation" of the records.
But archives officials who disclosed the emergency plan said it would mean that the agency would initially take over parts of the White House storage system, freezing the contents Jan. 20. Only later, after further study, will archivists attempt to move the records into the futuristic computer system they have devised as a repository for digital data.
More
here.
Friday Monkey Blogging: Orangutan's Spontaneous Whistling Opens New Chapter In Study Of Evolution Of Speech

As I mentioned a couple of months ago, I have started a regularly recurring blog entry meme every Friday afternoon, inspired by Bruce Schneier's regular series of "Friday Squid Blogging" posts, and my very own maddening Monkey Theory.
Here is this week's installment.
Via Science Daily.
Throughout history, human beings have used the whistle for everything from hailing a cab to carrying a tune. Now, an orangutan’s spontaneous whistling is providing scientists at Great Ape Trust of Iowa new insights into the evolution of speech and learning.
In a paper published in December in Primates, an international journal of primatology that provides a forum on all aspects of primates in relation to humans and other animals, Great Ape Trust scientist Dr. Serge Wich and his colleagues provide the first-ever documentation of a primate mimicking a sound from another species without being specifically trained to do so. Bonnie, a 30-year-old female orangutan living at the Smithsonian National Zoological Park in Washington, D.C., began whistling – a sound that is in a human’s, but not an orangutan’s, repertoire – after hearing an animal caretaker make the sound.
“This is important because it provides a mechanism to explain documented between-population variation in sounds for wild orangutans,” Wich said. “In addition, it counters a long-held assumption that non-human primates have fairly fixed sound repertoires that are not under voluntary control. Being able to learn new sounds and use these voluntarily are also two important aspects of human speech and these findings open up new avenues to study certain aspects of human speech evolution in our closest relatives.”
More
here.
Image source: ScienceDaily.com / Smithsonian National Zoological Park
Hacking U.S. is Big Business in Russia
A Chicago Tribune article, via Military.com, reports that:
Not long ago, the simple, anonymous thrill of exposing chinks in American software was enough of a payoff for a Russian hacker.
Today it's cash. And almost all the targets are in the United States and Europe, where Russia's notorious hackers pilfer online bank accounts, swipe social security numbers, steal credit card data and peek at e-mail log-ins and passwords as part of what some estimate to be a $100 billion-a-year global cyber-crime business.
And when it's not money that drives Russian hackers, it's politics -- with the aim of accessing or disabling the computers, Web sites and security systems of governments opposed to Russian interests. That may have been the motive behind a recent attack on Pentagon computers.
A new generation of Russian hacker is behind America's latest criminal scourge. Young, intelligent and wealthy enough to zip down Moscow's boulevards in shiny BMWs, they make their money in cyber-cubbyholes that police have found impossible to ferret out.
More
here.
Happy Boxing Day!

Boxing Day is a public holiday celebrated in the United Kingdom, Canada, New Zealand, Australia, and many other members of the Commonwealth of Nations on December 26, the day after Christmas Day.
Cheers!
- ferg
U.S. Government Vulnerable to Internet Predators
Loren B. Thompson writes for UPI:
Most Internet users have some awareness of the problem of threats to the entire system from criminals, terrorists and potentially hostile nations, since they encounter it in the form of spyware, viruses and other online nuisances.
However, the most disturbing "cyber" threats are largely invisible to the general public, because they involve attacks on specialized networks used by the armed forces, healthcare professionals, air traffic controllers, financial institutions, public utilities and heavy industry.
Each of these vital components of modern society now relies on Internet Protocol communications to run efficiently, and in most cases the new technology was assimilated without a careful assessment of its vulnerability to attack by outsiders.
A report [.pdf] from the Lexington Institute titled "Hidden Danger: The Threat to America's Networks" provides an overview of the threat to U.S. information networks, especially the networks operated by the federal government.
More
here.
Russian Police Bracing For Demonstrations
Via The Other Russia.
Police in Russia are worried that the economic crisis may lead to widespread public disturbances and crime. As the Nezavisimaya Gazeta reports [Russian language reference. -ferg], national guard forces are being sent to reinforce local militsiya in towns hit hard by sweeping layoffs. Towns with a single major employer, like Magnitogorsk and its metallurgical complex, are the primary focus of the relocation. The Magnitogorsk smelter has laid off some 3800 employees in the past three months, and 1000 more workers may lose their jobs in the near future.
Gennady Gudkov, the deputy chair of the State Duma Security Committee, told the newspaper that the effects of the crisis were constantly growing. “It could happen,” he said, “that no amount of Internal Forces will be enough.”
The main office of the Internal Forces, Russia’s equivalent of a national guard, denied that troops were being moved. Interior Ministry press-secretary Vasily Panchenkov said enough units were already in place, but added that OMON special forces could be sent in if public meetings and demonstrations turned violent.
More
here.
Note: Russia is not the only country that may be anticipating civil unrest due to economic turmoil -- the U.S. Army War College's Strategic Studies Institute recently released a
report entitled
"Known Unknowns: Unconventional 'Strategic Shocks' in Defense Strategy Development" in which advises the DoD that military strategies might have to be considered within the U.S. if widespread civil unrest becomes a problem because of violent protests, etc.
- ferg
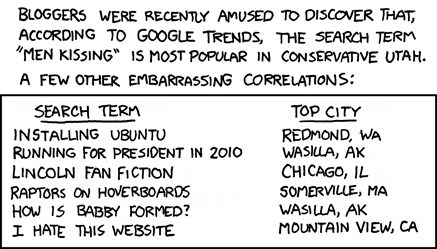
Classic xkcd: Google Trends
Click for larger image.
We
love xkcd.
Ho, ho, ho.
- ferg
'...And On Earth Peace, Good Will Toward Men'

Image source: Gary Markstein / Slate.com
Little Blue Pills Among the Ways CIA Wins Friends in Afghanistan
Joby Warrick writes in The Washington Post:
The Afghan chieftain looked older than his 60-odd years, and his bearded face bore the creases of a man burdened with duties as tribal patriarch and husband to four younger women. His visitor, a CIA officer, saw an opportunity, and reached into his bag for a small gift.
Four blue pills. Viagra.
"Take one of these. You'll love it," the officer said. Compliments of Uncle Sam.
The enticement worked. The officer, who described the encounter, returned four days later to an enthusiastic reception. The grinning chief offered up a bonanza of information about Taliban movements and supply routes -- followed by a request for more pills.
For U.S. intelligence officials, this is how some crucial battles in Afghanistan are fought and won. While the CIA has a long history of buying information with cash, the growing Taliban insurgency has prompted the use of novel incentives and creative bargaining to gain support in some of the country's roughest neighborhoods, according to officials directly involved in such operations.
More
here.
U.S. Army Officials Say Many More Active-Duty Troops Are Needed
Ann Scott Tyson writes in The Washington Post:
The Army needs to add at least 30,000 active-duty soldiers to its ranks to fulfill its responsibilities around the world without becoming stretched dangerously thin, senior Army officials warn.
"You can't do what we've been tasked to do with the number of people we have," Undersecretary of the Army Nelson Ford said in an interview last week. "You can see a point where it's going to be very difficult to cope."
Already, the Army lacks a strategic reserve of brigades trained and ready for major combat, officials said, and units being deployed to Iraq and Afghanistan are receiving new soldiers at the last minute, meaning they have insufficient time to train together before crossing into the war zone.
But the demand for soldiers extends beyond those countries, with the Pentagon creating new missions that require troops trained in cyber-warfare, homeland defense, intelligence-gathering and other areas, Ford said. "We have five to 10 new missions, and we are already stretched now."
More
here.
At Least 50,000 UAE Computers 'Infected'
Via Arabian Business.
More than 50,000 computers in the UAE are infected with “spyware” programmes that can be used to steal personal details and other personal data, a US-based internet security firm has revealed.
The figure represents an increase of almost 150 per cent in the past year but could be much bigger, according to Trend Micro.
The UAE is particularly at risk from cybercriminals because it has a tradition of ethical and trust-based business dealings, said Ian Cochrane, the company’s director of marketing in Dubai in comments published by UAE daily The National on Friday.
The wealthy Gulf region also has the world’s fastest-growing rate of internet penetration, making it additionally attractive to criminals, he added.
Gulf countries are a huge challenge for internet security firms because of the region’s tradition of honour in business, Mr Cochrane told the paper.
More
here.
Hat-tip: Pogo Was Right
Another Holiday Favorite: Bad Santa

Nothing lifts your spirits on Christmas like a down-on-your-luck, thieving, hard-drinking, Billy Bob Thornton as Santa.
Great movie.
- ferg
In Passing: Eartha Kitt

Pakistani Hackers Hit Indian Rail System Website
Via The Financial Express.
In the first instance of cyber attack on Indian government websites, the attack on Eastern Railways site on Wednesday popped open vulnerability of government websites in the country.
While Eastern Railway took almost two and half hours to restore the site to normalcy, visitors to the site continued to be attacked by Trojan virus. ER officials could only primarily trace the roots to Toronto in Canada after repeated top-brass meetings all through the day.
As spotted by FE in the morning, the official site of the Eastern Railway-www.eastern railway.gov.in—was hacked on Wednesday. When opened, the scroll on the site— which normally consists of official announcements—had unusual notes. The first note read: “Cyber war has been declared on Indian cyberspace by Whackerz- Pakistan (24 Dec-2008).” This was followed by two other notes: “Indians hit hard by Zaid Hamid” and “We are f**ked up Indians. You are hacked.”
More
here.
Hat-tip: IntelFusion
Estonia Spy Case Rattles Nerves at NATO
Ellen Barry writes in The New York Times:
As an independent state emerged here after 47 years of Soviet rule, a jovial, meticulous police official named Herman Simm was promoted again and again. By 2001, he occupied a post that satisfied his fascination with secrets: As chief of the National Security Authority, his job was to secure all classified communication between Estonia and its allies.
And prosecutors say they have established why he was so interested in secrets: They believe he was passing information to an undercover agent for the Russian Foreign Intelligence Service. The contact is identified in documents as “Jesus” and is likely to be a citizen of Portugal, said Mr. Simm’s defense lawyer, Owe Ladva.
Though the authorities have not said when they believe the spying began, Mr. Simm was in place during a critical period, from 2001 to 2006, as Estonia became a member of NATO and Moscow’s frustration at the Western military alliance grew into a hostile standoff. He was arrested in September on suspicion of treason.
More
here.
Opinion: Bush's Final F.U.

Tim Dickinson writes in The Rolling Stone:
With president-elect Barack Obama already taking command of the financial crisis, it's tempting to think that regime change in America is a done deal. But if George Bush has his way, the country will be ruled by his slash-and-burn ideology for a long time to come.
In its final days, the administration is rushing to implement a sweeping array of "midnight regulations" — de facto laws issued by the executive branch — designed to lock in Bush's legacy. Under the last- minute rules, which can be extremely difficult to overturn, loaded firearms would be allowed in national parks, uranium mining would be permitted near the Grand Canyon and many injured consumers would no longer be able to sue negligent manufacturers in state courts. Other rules would gut the Endangered Species Act, open millions of acres of wild lands to mining, restrict access to birth control and put local cops to work spying for the federal government.
"It's what we've seen for Bush's whole tenure, only accelerated," says Gary Bass, executive director of the nonpartisan group OMB Watch. "They're using regulation to cement their deregulatory mind-set, which puts corporate interests above public interests."
More
here.
A Christmas Story: All Day Long on TBS

"You'll shoot your eye out, kid."
A Christmas Story. All day long today, on TBS.
An enduring classic.
Enjoy!
- ferg
Halley's Comet - The Christmas Connection

Via Stardate.org.
Edmund Halley's resume is one of the most impressive in the history of science. He compiled the first atlas of the stars of the southern hemisphere. He measured Earth's magnetic field, and even invented the basis for life insurance.
Yet Halley's enduring claim to fame was solidified well after his death. In fact, it happened 250 years ago today.
Halley was a friend of Isaac Newton, who had devised laws of motion and gravity. The planets and moons all followed these laws just fine, but no one was sure if comets would do the same thing.
Comets are mountain-sized balls of rock and frozen gases that grow long tails as they approach the Sun. In Halley's time, though, their nature was poorly understood. In fact, no one was sure if they continuously orbited the Sun, as planets do, or if they disappeared into space after a single appearance.
Halley plotted the motions of about two dozen comets that had appeared in recent centuries. He found that the comets of 1531, 1607, and 1682 all followed the same path -- suggesting that they were a single body. Since the appearances were about 75 years apart, Halley predicted that the comet would return in 1758.
Halley died in 1742. But on Christmas Day of 1758, a German amateur astronomer, Johann Palitzsch, first saw the comet on its return to the inner solar system. Astronomers named the comet in Halley's honor -- adding one final listing to his impressive resume.
More
here.
Image source: National Geographic
Merry Christmas to All of Our Men and Women in Uniform

We Salute All of Our American Fighting Men and Women in the U.S. Military, especially those who are separated from friends, family, and loved ones & away from home this holiday season.
You are not forgotten.
Merry Christmas and Happy Holidays.
Mark Fiore's Political Cartoonist's Christmas List

Mark Fiore's Christmas Wish List.
Via The San Francisco Chronicle.
- ferg
RBS WorldPay Data Breach Hits 1.5 Million
Richard Adhikari writes on internetnews.com:
A hacker got into the computer systems of electronic payment processing services provider RBS WorldPay, compromising more than a million customers' records.
Formerly known as RBS Lynk, RBS WorldPay, which claims it has more than 20 years in the business, is the U.S. payment processing arm of The Royal Bank of Scotland Group.
Personal and financial account information of about 1.5 million cardholders and other individuals, and the social security numbers (SSNs) of 1.1 million people, may have been accessed by the hacker, RBS WorldPay said in a statement announcing the break-in on Wednesday.
RBS WorldPay describes the break-in as a highly sophisticated cyber intrusion on its Website. It notified law enforcement agencies and federal regulators after the break-in was discovered on November 10.
More
here.
Current Crisis Boosts Russian Internet and Kremlin Efforts to Control It
A Window on Eurasia article by Paul Gobel, via Georgia Daily, reports that:
One of the consequences of the current economic crisis in Russia is that the Internet is becoming a more important player in the media there, but precisely because of that, the web is attracting greater attention from Russian officials who view it as a threat to their ability to shape public attitudes through their control of television.
As their incomes stagnate or fall, Russians increasingly are turning to media outlets that do not cost them as much as newspapers and magazines do. Until recently and for many still, that has meant television; but now, especially as more and more Russians recognize the growing gaps in TV coverage, it includes the Internet as well.
The growth in the number of Russians going online entails two significant consequences. On the one hand, more and more companies are spending their advertising budgets on websites rather than traditional outlets, something that further erodes the already precarious situation of many of the latter.
On the other, Moscow has been forced to recognize that the Internet now represents an increasingly serious challenger to its control of the media space and hence of the public agenda in that country. And that recognition has led the government to seek to control a media that many Russian officials had thought that they could ignore.
More
here.
Russian Opposition Websites Shut Down By Attacks
Via The Other Russia.
A set of Russian opposition news sites are back online after a series of distributed-denial of service (DDoS) attacks overwhelmed their servers.
Kasparov.ru, the internet portal of the United Civil Front party, was forced offline Monday evening, the editorial office said. As many as 1,500 requests per second were sent to the site, which could not handle the load, and the attacks continued well into the following day. Nazbol.ru, the website of the banned National Bolshevik Party, was concurrently taken down.
On Wednesday morning, another opposition online newspaper was targeted. Grani.ru, which publishes news and opinion content, was accessible to readers only intermittently by Wednesday evening, editors said. Ikd.ru, which publishes news about demonstrations going on around Russia, also reported an attack.
More
here.
Quote of the Day: Will Chen

"I love It's a Wonderful Life because it teaches us that family, friendship, and virtue are the true definitions of wealth."
- Will Chen, writing on his blog Wise Bread (props, Boing Boing). He continues that "...in 1947, however, the FBI considered this anti-consumerist message as subversive Communist propaganda."
This has become a Christmas tradition with me now -- Merry Christmas.
- ferg
Toon of The Day: One Wise Man

Image source: Tab (Thomas Boldt) via Cagle Cartoons.
An Annual Labor of Love: Children's Xmas Letters to Christopher Walken

Something I blogged about for the last few years -- the gift that keeps on giving.
Enjoy! And Seasons Greetings.
- ferg
Earth: Population To Be 6.75B on New Year's Day

Via The Times of India.
The world's population on New Year's Day is set to reach 6.75bn, a German group that encourages birth control said on Tuesday.
The World Population Foundation of Germany said the planet's human population rose by 82m this year and according to its estimates, the world population on Jan 1 would reach 6,751,643,600.
The Hanover-based group said almost all the growth in numbers was in developing nations, where women faced multiple pregnancies whether they wanted them or not because contraception was not available.
Resources, education and health care were in short supply in those nations because of rising population, the foundation said.
A child born today in Germany can expect to live 79 years on average, but an African can only expect 54 years.
"If we want to tackle poverty at the source, we have to help women avoid unwanted pregnancy," said Renate Baehr, the secretary of the foundation. "We have to spend more on sex education and contraception."
More
here.
'Scareware' Purveyors, Innovative Marketing, Held in Contempt of Court
Tricia Bishop notes in The Baltimore Sun:
A Baltimore federal court judge yesterday held Innovative Marketing Inc., a Belize-based Internet company, in contempt of court for ignoring previous orders commanding it to shut down and hand over financial records. This month, the Federal Trade Commission sued the company, claiming it ran an illegal "scareware" operation that tricked more than a million people into spending $100 million on bogus security software by making them believe their computers were under siege from various viruses and spy programs.
In an order signed yesterday, U.S. District Court Judge Richard D. Bennett ordered the business to pay $8,000 for each day it fails to comply with the earlier orders. The company's chief executive and four other defendants, all of whom have had their assets frozen, did not show up for a hearing last week, prompting Bennett to promise he would have them arrested if they didn't respond.
More
here.
Hat-tip: techdirt.com
One Thing I Love About The Holidays: Fruitcake

That's right, you read that correctly.
I love the stuff.
With a little brandy. Or beer.
Happy Holidays, and Merry Christmas.
- ferg
Toon of The Day: 'Tis The Season...

Image source: Pat Bagley / Cagle Cartoons
Fake Antivirus Peddlers Helped by Microsoft, IRS Web Glitches
Robert McMillan writes on ComputerWorld:
Just weeks after the U.S. Federal Trade Commission shut down two companies accused of selling fake antivirus software, a new player has moved into the market, aided by glitches in the Microsoft and U.S. Internal Revenue Service Web sites.
Over the past four days the scammers have used so-called redirector links on Web sites belonging to magazines, universities and, most remarkably, the Microsoft.com and IRS.gov domains, said Gary Warner, director of research in computer forensics with the University of Alabama at Birmingham, who first reported the activity on his blog Tuesday.
More
here.
Researchers Seek Advanced Network Prioritization, Security Technology
Via The NetworkWorld "Layer 8" Blog.
Researchers are looking to build self-configuring network technology that would identifying traffic, let the network infrastructure prioritize it down to the end user, reallocate bandwidth between users or classes of users, and automatically make quality of service decisions. The system will have a minimum of 32 levels of prioritization. These prioritization levels will be configurable and changeable at the system level in an authenticated method. Data with a higher priority will be handled more expeditiously than traffic with a lower priority.
If that sounds like a major undertaking, it is, but consider who wants to develop such a beast: the Defense Advanced Research Projects Agency (DARPA).
This advanced prioritization system is part of DARPA's Military Networking Protocol (MNP) program which is looking to develop an authenticated and attributable identification system for packet based, military and government data networks, the agency said. Military or government data sent with the MNP will be compatible with normal Internet equipment to allow MNP traffic to pass through legacy network or encryption equipment, DARPA said.
Not only should the prioritization scheme be radically advanced, the system should be extremely difficult to spoof or inject false traffic into, DARPA said.
More
here.
Happy Festivus!
 Happy Festivus!
Happy Festivus!
U.S. Navy Lab Thief Gets 18 Months in Prison
Del Quentin Wilber writes in The Washington Post:
Victor Papagno had two loves, federal prosecutor say: computers and stealing.
For the Navy, it was a devastating combination.
Over 10 years, authorities said, the computer technician with obsessive-compulsive disorder ran one of the biggest computer theft scams in local history. He stole more than 19,000 pieces of computer equipment from the offices of the Naval Research Laboratory in Southwest Washington.
The loot took up so much space that Papagno built a 2,775-square-foot garage to store it all. It cost the Navy more than $150,000 to inventory the stash of keyboards, monitors, floppy disks, hard drives, cables, batteries and a device to make security badges. When investigators came to haul the equipment away from Papagno's Charles County home, they needed an 18-wheeler.
He got away with stealing computer components from a secure Navy facility by walking out the front door with the booty in boxes -- an average of five items a day over a decade. The Navy never caught on. The tip that brought him down last year came from his estranged wife, authorities said.
More
here.
U.S. Pact Nullifies $6 Billion Award in '89 Bombing Over Africa
Kimberly Kindy writes in The Washington Post:
As the State Department reviews hundreds of claims from people who lost family members in Libyan-sponsored terrorist attacks, controversy is building over a case that is so low-profile it is sometimes called "the forgotten flight."
The case stems from the Sept. 19, 1989, bombing of the French-operated UTA Flight 772, which crashed in the Niger desert after a suitcase bomb exploded in the cargo hold, killing 170 passengers and crew, including seven Americans.
Family members of the American victims made history in January by becoming the first and only group to successfully sue Libya in federal court. After hearing the Pugh case -- named for the family of one of the victims -- U.S. District Judge Henry H. Kennedy found Libya responsible for the attack and awarded 44 relatives a collective $6 billion.
Plaintiffs in the case became incensed in August when the United States reached an agreement with Libyan leader Moammar Gaddafi to dismiss all lawsuits for victims of state-sponsored terrorism. Gaddafi agreed to turn over $1.5 billion, and the U.S. government started setting up a process for reviewing survivor claims and distributing the money.
More
here.
Christmas Toon of The Day: A Bigger Grinch

Image source: David Fitzsimmons / Cagle cartoons
Fry's Exec Arrested in Alleged $65 Million Fraud Scheme

Lisa Fernandez writes in The Mercury News:
A one-time computer salesman who rose through the ranks to help build Fry's Electronics into a robust retailer is facing allegations that he defrauded the San Jose-based company out of $65 million, much of which he used to pay off enormous gambling debts in Las Vegas.
Ausaf Umar Siddiqui, 42,who goes by "Omar" and has been Fry's vice president of merchandising and operations, appeared in federal court Monday, where prosecutors filed a complaint alleging he masterminded a "secret kickback scheme to defraud Fry's Electronics of millions of dollars.''
Fry's executives didn't know about the illegal kickbacks, the federal complaint states. After 10 years with the company, he was fired Monday.
Siddiqui was known around the office for driving fast cars, carrying wads of $100 bills in his pocket and boisterously rooting on sports events from the four TV screens in his office. He spent $162 million in three years at just two of his favorites, the MGM Grand Casino and Las Vegas Sands Casino, according to his bank statements detailed in the complaint written by IRS Agent Andres Gonzalez.
The alleged scheme occurred from 2005 until mid-October when a Fry's high-level employee walked into Siddiqui's office at 600 E. Brokaw Road and saw confidential spreadsheets, letters and extraordinarily high commission amounts on Siddiqui's desk.
Siddiqui is expected to be formally charged in U.S. District Court on Jan. 15, on counts of money-laundering and wire fraud.
More
here.
Hat-tip: techdirt.com
Microsoft Warns of SQL Vulnerability
Robert McMillan writes on ComputerWorld:
Just days after patching a critical flaw in its Internet Explorer browser, Microsoft is now warning users of a serious bug in its SQL Server database software.
Microsoft issued a security advisory late Monday, saying that the bug could be exploited to run unauthorized software on systems running versions of Microsoft SQL Server 2000 and SQL Server 2005.
Attack code that exploits the bug has been published, but Microsoft said that it has not yet seen this code used in online attacks. Database servers could be attacked using this flaw if the criminals somehow found a way to log onto the system, and Web applications that suffered from relatively common SQL injection bugs could be used as stepping stones to attack the back-end database, Microsoft said.
More
here.
One Hacker's Audacious Plan to Rule the Black Market in Stolen Credit Cards
Kevin Poulsen writes on Wired:
The heat in Max Butler's safe house was nearly unbearable. It was the equipment's fault. Butler had crammed several servers and laptops into the studio apartment high above San Francisco's Tenderloin neighborhood, and the mass of processors and displays produced a swelter that pulsed through the room. Butler brought in some fans, but they didn't provide much relief. The electric bill was so high that the apartment manager suspected Butler of operating a hydroponic dope farm.
But if Butler was going to control the online underworld, he was going to have to take the heat. For nearly two decades, he had honed his skills as a hacker. He had swiped free calls from local telephone companies and sneaked onto the machines of the US Air Force. Now, in August 2006, he was about to pull off his most audacious gambit yet, taking over the online black markets where cybercriminals bought and sold everything from stolen identities to counterfeiting equipment. Together, these sites accounted for millions of dollars in commerce every year, and Butler had a plan to take control of it all.
More
here.
Eyeing the Spying to Guard Americans' Privacy
Greg Gordon writes on Nukes & Spooks:
To carry out a recommendation from the Sept. 11 Commission aimed at preventing terrorists from ever again capitalizing on the lack of U.S. intelligence sharing, the Department of Homeland Security has since 2004 quietly facilitated the creation of 58 to 60 "fusion centers" that blend local, regional, state and federal agents.
One pregnant question has been how closely these agencies have been observing state and federal privacy laws as information, sucked up from eavesdropping, informants, surveillance and government records, flows among the feds, state and local agencies down to cops on the beat.
In a Privacy Impact Assessment released today, Homeland Security officials ticked off no fewer than seven ways in which each center, with its own organizational structure, poses risks to Americans’ privacy.
More
here.
Speed Camera 'Pimping' Attack Highlights Public Identity Weaknesses
Adam O'Donnell writes on the ZDNet "Zero Day" Blog:
In a brilliant physical-world example of what happens when too much value is placed upon open identification systems for determining reputation, a group of high school students are setting off speeding enforcement cameras using fake license plates belonging to their enemies.
According to an article in the D.C. area Montgomery County Sentinel, high school students are generating photorealistic replicas of their enemies license plates, placing them on their vehicles, and blowing through speeding cameras. Obviously people who have been victimized by this attack are upset, but at least one anonymous individual hits the nail on the head:
"The practice of sending speeding tickets to faceless recipients without any type of verification is unwarranted and an exploitation of our rights."
More
here.
ICANN Releases Upgraded Invalid WHOIS Reporting System
Via Domain Name Wire.
ICANN has updated its WHOIS Data Problem Report System (WDPRS), which anyone can use to submit reports of inaccurate whois information on a domain name.
According to ICANN, the new system offers many improvements:
- More detailed information is captured from complainants to assist registrars in investigating WHOIS inaccuracies
- Duplicate reports regarding the same domain name are not accepted by the system
- Reports concerning domains already on hold are removed
- Greater capacity has been introduced to allow for bulk submissions of reports
- Processes have been put in place to assess registrar compliance with RAA Whois inaccuracy investigation requirements
The system is available on the Internic web site.
More
here.
Kiwis Nail Major Spammer
Via The Sydney Morning Herald.
A New Zealand man living in Australia has agreed to pay fines totalling $92,715 after admitting his role in an international spam email operation said to be responsible for sending out billions of unsolicited emails in recent years.
Lance Atkinson, 26, of Pelican Waters in Queensland, is also facing charges in the US where a court has frozen his assets at the request of the US Federal Trade Commission (FTC), which also succeeded in having the spam network shut down.
New Zealand's Internal Affairs' Anti-Spam Compliance Unit found Lance Atkinson's operation responsible for more than 2 million unsolicited electronic messages that were sent to New Zealand computers between 5 September 2007 and 31 December 2007.
These emails marketed Herbal King, Elite Herbal and Express Herbal branded pharmaceutical products, manufactured and shipped by Tulip Lab of India.
More
here.
In Remembrance: 20 Years After Pan Am 103 Air Disaster

On Wednesday, 21 December 1988, Pan Am 103 (a Boeing 747 named "Clipper Maid of the Seas") was destroyed by a bomb, killing all 243 passengers and 16 crew members. Eleven people on the ground, in Lockerbie, Scotland, were also killed as large sections of the plane fell in and around the town, bringing total fatalities to 270.
The echoes of this tragedy still ring loud & clear, and there are still unresolved questions surrounding the real reasons & perpetrators of this horrible crime.
- ferg
U.S. Must Update Laws To Defend Against Foreign Hackers
Jim Langevin and Michael McCaul write in The Houston Chronicle:
If on any given day, foreign nationals pulled moving vans up to the loading docks of government agency buildings, filled them with computers and drove away with sensitive information, Americans would be outraged. The fact is it is happening, but with no trucks and no finger prints. The United States is under attack in cyberspace.
Today's hackers are no longer thrill-seeking teenagers; they are organized crime syndicates and national militaries that commit espionage. From thousands of miles away, increasingly sophisticated foreign adversaries are electronically infiltrating sensitive U.S. computer networks to obtain military technologies. Foreign competitors and criminals unabashedly steal trade secrets from American companies through similar methods. Critical systems that run our financial, energy, and transportation infrastructures have also become victims of cyber attack and exploitation. One operation discovered a vulnerability in which generators could be destroyed by the mere click of a mouse.
Our national leaders have been far too slow to understand the scope and significance of this threat. America's laws for cyberspace are decades old, written for primitive technologies in a less-connected era. Our bureaucracy is organized for an industrial age. We are not prepared to meet the threats of the 21st century.
More
here.
Bush E-Mails May Be Secret a Bit Longer
R. Jeffrey Smith writes in The Washington Post:
The required transfer in four weeks of all of the Bush White House's electronic mail messages and documents to the National Archives has been imperiled by a combination of technical glitches, lawsuits and lagging computer forensic work, according to government officials, historians and lawyers.
Federal law requires outgoing White House officials to provide the Archives copies of their records, a cache estimated at more than 300 million messages and 25,000 boxes of documents depicting some of the most sensitive policymaking of the past eight years.
But archivists are uncertain whether the transfer will include all the electronic messages sent and received by the officials, because the administration began trying only in recent months to recover from White House backup tapes hundreds of thousands of e-mails that were reported missing from readily accessible files in 2005.
More
here.
Have a Cool Yule - Winter Solstice Today
 The precise moment of the 2008 solstice will be December 21, 2008 at 7:04 AM EST and 12:04 UT (Universal Time).
The precise moment of the 2008 solstice will be December 21, 2008 at 7:04 AM EST and 12:04 UT (Universal Time).Today is the beginning of
Yule, the winter solstice celebration of the Germanic pagans still celebrated by some new (old?) age movements around the world. It is also one of the eight solar holidays, or sabbats, of Paganism.
In modern Paganism, Yule is celebrated on the winter solstice, which is this morning, at precisely 04:04 Pacific Standard Time (-08:00 UTC).
All pagans celebrate!
- ferg