Report: Airlines Hit Hard by Online Fraud
Sindya Bhanoo writes on The Industry Standard:
The airline industry experiences significant online fraud, according to findings released by CyberSource Corporation, a company that offers a hosted fraud management solution for online retailers.
According to the survey, airlines worldwide lost more than $1.4 billion to fraudsters in 2008. The figure amounts to about 1.3% of worldwide airline revenue.
Online fraud can occur in several ways, Bruce Frymire, a spokesperson for CyberSource told The Industry Standard. Generally, fraudsters use stolen credit card information to buy a ticket for themselves, or act as a travel agent, and buy a ticket for someone else. By the time the true card owner reports the theft, the flight has usually been taken and the airlines loses 100% of the revenue, Frymire said.
More
here.
SCADA Watch: Power Grid is Found Susceptible to Cyber Attack
Robert McMillan writes on ComputerWorld:
An emerging network of intelligent power switches, called the Smart Grid, could be taken down by a cyberattack, according to researchers with IOActive, a Seattle security consultancy.
IOActive researchers have spent the past year testing Smart Grid devices for security vulnerabilities and have discovered a number of flaws that could allow hackers to access the network and cut power, according to Joshua Pennell, IOActive's CEO. Smart Grid devices are small computers that are connected to the power grid, giving customers and power companies better control over the electricity they use. There are about 2 million of these devices currently deployed, but many more are expected to be added in coming years.
The researchers created a computer worm that could quickly spread among Smart Grid devices, many of which use wireless technology to communicate, according to Travis Goodspeed, an independent security consultant who worked with the team. "It spread from one meter to another and then it changed the text in the LCD screen to say 'pwned'," he said. Pwned is hacker-speak meaning "taken over."
In the hands of a malicious hacker, this code could be used to cut power to Smart Grid devices that use a feature called "remote disconnect," which allows power companies to cut a customer's power via the network.
IOActive briefed the U.S. Department of Homeland Security on its findings Monday and is advising the utilities industry to better test the systems before deploying them in the real world.
More
here.
U.S. Toll in Iraq, Afghanistan

Iraq and
Afghanistan statistics via
The Boston Globe (AP).
As of Friday, March 20, 2009, at least 4,260 members of the U.S. military had died in the Iraq war since it began in March 2003, according to an Associated Press count.
The figure includes eight military civilians killed in action. At least 3,425 military personnel died as a result of hostile action, according to the military's numbers.
The AP count is one fewer than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
As of Friday, March 20, 2009, at least 595 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Friday at 10 a.m. EDT.
Of those, the military reports 439 were killed by hostile action.
More
here and
here.
And as always, the
Iraq Coalition Casualty Count keeps the grim watch on their website
here.
Honor the Fallen.
Connecticut Man Sentenced for e-Card Scam
Nancy Gohring writes on PC World:
A Connecticut man was sentenced to four years of probation for his role in a phishing scam that tricked America Online subscribers into giving up their credit card numbers.
Thomas Taylor Jr., of West Haven, Connecticut, and his colleagues spammed thousands of AOL subscribers with e-mails that purported to include electronic greeting cards from sites including Hallmark.com and Bluemountain.com. When people tried to view the cards, their computers became infected with a Trojan that prevented them from accessing AOL unless they entered information including their names, addresses, Social Security numbers, credit card numbers and bank account numbers.
Taylor and his co-conspirators used the data to make fake ATM cards, which they used to withdraw cash and buy goods including gaming consoles, laptops and gift cards.
A judge in the U.S. District Court for the District of Connecticut has ordered Taylor to pay US$33,714 to the victims of his scheme. He also must spend the first seven months of his probation in home confinement and perform 200 hours of community service during his probation time.
More
here.
The Dilemma of 'CODIS Creep' - Genetic Surveillance for All?
Jeffrey Rosen writes on Slate.com:
In March 2003, a drunk in southern England threw a brick off a bridge late at night, striking and killing a truck driver traveling along the freeway below. Armed with DNA from the blood on the brick, the British police searched the United Kingdom's national DNA database, which includes convicted felons and people who have been arrested, but failed to get a direct match. They then conducted a DNA dragnet, asking hundreds of young men in the area to donate a sample voluntarily, but still came up short. Without any other leads, the police decided to conduct what's called a "familial search" of the national DNA database. They were looking not for perfect matches to convicted offenders but for near matches, in the hope of using them to identify a relative who might have committed the crime.
Ordinarily, when searching for actual offenders, the British police look for a perfect match to a DNA profile that contains 10 pairs of peaks, or "alleles," with one number in each pair provided by the father and the other by the mother. Only identical twins share genetic profiles on all 20 alleles, so if you get a perfect match between the DNA you find at the scene and the DNA database profile, you have very strong evidence that the person in the database committed the crime. But the police can also program the search to look for partial matches, identifying profiles that are similar but not identical to those in the database. A partial match can suggest that the person in the database didn't commit the crime, but a close relative whose DNA pattern varies slightly on some of the 20 alleles may have done so. Accordingly, the British authorities programmed the search to pull up any offender in the database who matched at least 11 alleles out of 20 from the blood on the brick.
Initially, this familial search produced more matches than the police could follow up. But then the authorities limited the search to young men from two counties near the crime scene. This narrowed the number of partial matches to around 25. After interviewing the person whose profile represented the closest match—16 out of 20 alleles—the police found he had a brother who lived in one of the nearby counties. They went to the brother, Craig Harman, who agreed to give a DNA sample. It turned out to match the DNA on the brick. Harmon confessed after being confronted with the match, and in 2004, he was convicted of manslaughter.
Much more
here.
Hat-tip: Personal Health Information Privacy
Friday Monkey Blogging: Orangutan Tosses Rope To Save Child

As I mentioned a few months ago, I started a regularly recurring blog entry meme every Friday afternoon, inspired by Bruce Schneier's regular series of "Friday Squid Blogging" posts, and my very own maddening Monkey Theory.
Here is this week's installment.
Richard Sheers writes on the Daily Mail:
All mothers know there is no limit to what they will do to protect their children.
But this mother orang-utan proved that the selfless sentiment extends to the animal kingdom also.
These astonishing pictures from the World Wildlife Fund capture the moment the terrified mother caught a rope thrown to her by humans and swam across a flooded river to bring her baby to safety.
It is a long-held belief that the giant apes are petrified of water. But the mother did not appear to give her leap into the swollen river a second thought.
The amazing pictures were taken by local officials of the WWF on the Malaysian island of Borneo.
More
here.
Image source: Daily Mail
Report Links Russian Intelligence to Cyber Attacks
Robert McMillan writes on PC World:
A follow-up report authored by a group of cyber-security experts claims that Russian intelligence agencies were probably involved in the 2008 cyber attacks on Georgia.
The report, released Friday, concludes that there is a "strong likelihood" that the Foreign Military Intelligence agency (the GRU) and Federal Security Service (the FSB) directed cyber attacks on Georgian government servers in July and August of 2008, attacks which coincided with a Russian military invasion of Georgia. Called Grey Goose 2, the report is a follow-up to the group's October 2008 report about the Georgian cyber war. It includes sections on the recent conflict in Gaza and politically motivated attacks against the Eastern India Railway Web site.
Grey Goose was written by a volunteer group of security experts who have used their technical skills to investigate the cyber incidents. A more detailed version of the report is being made available to government agencies and security researchers.
More
here.
Security Fix: Rogue Antivirus Distribution Network Dismantled (For Now)
Brian Krebs writes on Security Fix:
A major distribution network for rogue anti-virus products has been shut down following reports by Security Fix about massive profits that the network's affiliates were making for disseminating the worthless software.
On Monday, Security Fix profiled TrafficConverter2.biz, a program that pays affiliates handsome commissions for spreading "scareware" products like Antivirus2009 and Antivirus360. Scareware tries to frighten consumers into purchasing fake security software by pestering them with misleading and incessant warnings about threats resident on their systems.
According to a message posted at TrafficConverter2.biz and its sister sites, the programs credit card payment processor pulled the plug on them shortly after our story ran.
More
here.
Romanian Pentagon Hacker Arrested
Lucian Constantin writes on Softpedia News:
A 23-year-old man suspected of having hacked into Department of Defense systems during 2006 has been arrested in Iaşi, Romania, by the local police and the Direction for Investigating Organized Crime and Terrorism (D.I.I.C.O.T.). If found guilty, the hacker risks a maximum sentence of 12 years behind bars.
The organized crime police descended in force on the apartment of Eduard Lucian Mandru, on 18 March, at 7 AM in the morning. Realizing that he had been tracked down, the hacker attempted to destroy the data on his hard drive, but the process was stopped in time by the authorities.
In his daily life, Eduard Lucian Mandru is studying for a masters degree in Banks and Financial Markets at the local Faculty of Economy and Business Management. However, the student is also very passionate about computers and the Linux operating system.
According to the U.S. investigators, Mr. Mandru is the hacker calling himself Wolfenstein, who broke into a secure computer network belonging to the Department of Defense in 2006 and infected several systems with an information-stealing trojan.
The authorities had a very hard time locating him, as the hacker was accessing the network through compromised servers in Japan. In addition, he was covering his tracks by deleting all access logs. One solid lead that the investigators had was a yahoo e-mail address associated with the perpetrator, which eventually led to his identification.
More
here.
Hat-tip: The Register
A Search is Launched for Conficker's First Victim
Robert McMillan writes on ComputerWorld:
Where did the Conficker worm come from? Researchers at the University of Michigan are trying to find out, using a vast network of Internet sensors to track down the so-called "patient zero" of an outbreak that has infected more than 10 million computers to date.
The university uses so-called Darknet sensors that were set up about six years ago to keep track of malicious activity. With funding from the U.S. Department of Homeland Security, computer scientists have banded together to share data collected from sensors around the world.
"The goal is to get close enough so you can actually start mapping out how the spread started," said Jon Oberheide, a University of Michigan graduate student who is working on the project.
But that's not an easy job. To find the minuscule clues that will identify the victim, researchers must sift through more than 50 terabytes of data to find the telltale signatures of a Conficker scan.
More
here.
ISOC Survey: No Business Case for IPv6
Carolyn Duffy Marsan writes on NetworkWorld:
Business incentives are completely lacking today for upgrading to IPv6, the next generation Internet protocol, according to a survey of network operators conducted by the Internet Society (ISOC).
In a new report [.pdf], ISOC says that ISPs, enterprises and network equipment vendors report that there are "no concrete business drivers for IPv6."
However, survey respondents said customer demand for IPv6 is on the rise and that they are planning or deploying IPv6 because they feel it is the next major development in the evolution of the Internet.
More
here.
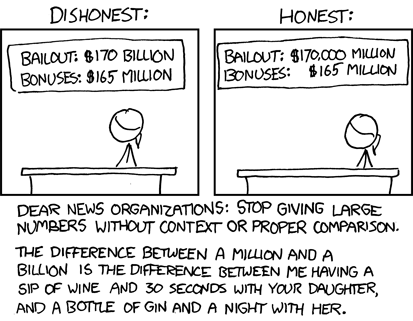
Quote of The Day: David Sirota
"United Steelworkers President Leo Gerard likes to say that Washington policymakers 'treat the people who take a shower after work much differently than they treat the people who shower before they go to work.' In the 21st century Gilded Age, the blue-collar shower-after-work crowd is given the tough, while the white-collar shower-before-work gang gets the love, and never before this week was that doctrine made so clear."
- David Sirota, writing in "A Government of Men, Not Laws".
Researchers Warn on Security Flaw in x86 Chips
Andy Patrizio write on internetnews.com:
Security researchers are sounding the alarm about what they say is a serious and long-known flaw in x86 processors that could prove embarrassing not just for its existence -- but for the lack of action taken to address it so far.
Joanna Rutkowska and Rafal Wojtczuk today published a research paper [.pdf] describing a proof-of-concept rootkit that a hacker can install on a system through a vulnerability in Intel CPUs' caching memory.
The rootkit specifically attacks System Management Mode (SMM) memory, called SMRAM -- an area of memory not accessible by software because it has a specific use: It's where the processor stores information when a system enters sleep mode.
The memory operates at a higher level of privilege than the operating system, which means the OS can't manage or control it. Even the kernel or a hardware hypervisor can't override it, making attacks that penetrate SMM potentially difficult to thwart. Because SMM memory is protected from applications accessing it, any code that runs in it is trusted to be valid and safe.
As a result, malware could take over a PC with little or no way to remove it.
More
here.
Aussie Stumbles on 19,000 Exposed Credit Card Numbers
Ry Crozier writes on ITnews.com.au:
A defunct payment gateway has exposed as many as 19,000 credit card numbers, including up to 60 Australian numbers.
The discovery by a local IT industry worker was made by mistake and appears to be caused by a known issue with the Google search engine, in which the pages of defunct web sites containing sensitive directories remain cached and available to anyone.
The cached data, viewed by iTnews, includes 22,000 credit card numbers, including CVVs, expiry dates, names and addresses.
Up to 19,000 of these numbers could be active. Most are customers in the US and Britain although some are Australian.
The credit card numbers are for accounts held with Visa, Mastercard, American Express, Solo, Switch, Delta and Maestro/Cirrus.
More
here.
Small Business: The New Black In Cyber Crime Targets
Tim Wilson writes on Dark Reading:
Hackers and computer criminals this year are taking a new aim -- directly at small and midsize businesses, according to experts who spoke here today at Visa's annual security event. The consensus: Smaller businesses offer a much more attractive target than larger enterprises that have steeled themselves with years of security spending and compliance efforts.
"As the security becomes better at large companies, the small business begins to look more and more enticing to computer criminals," said Charles Matthews, president of the International Council for Small Business, in a panel presentation here. "It's the path of least resistance."
Matthews quoted industry research that states small businesses are far less prepared to defend themselves against cyberattack. "Nearly one-fifth of small businesses don't even use antivirus software," he said. "Sixty percent don't use any encryption on their wireless links. Two-thirds of small businesses don't have a security plan in place. These numbers are both surprising and disturbing."
And many small businesses still don't know they are targets, according to Chris Gray, director of innovation policy at the Canadian Chamber of Commerce and another member of the panel. "According to a brief survey we conducted, about two-thirds of small and medium-sized businesses believe that large companies are the main target for cybercrime," he reported. "Yet 85 percent of the fraud we see in business occurs in small and medium-sized businesses."
More
here.
Mark Fiore: Clean Coal

More Mark Fiore brilliance.
Via The San Francisco Chronicle.
Enjoy.
- ferg
Classic xkcd: 1000 Times
Click for larger image.
We
love xkcd.
- ferg
SCADA Watch: Hackers Penetrating Industrial Control Systems
Grant Gross writes on ComputerWorld:
The networks powering industrial control systems have been breached more than 125 times in the past decade, with one resulting in U.S. deaths, a control systems expert said Thursday.
Joseph Weiss, managing partner of control systems security consultancy Applied Control Solutions, didn't detail the breach that caused deaths during his testimony before a U.S. Senate committee, but he did say he's been able to find evidence of more than 125 control systems breaches involving systems in nuclear power plants, hydroelectric plants, water utilities, the oil industry and agribusiness.
"The impacts have ranged from trivial to significant environmental damage to significant equipment damage to deaths," he told the Senate Commerce, Science and Transportation Committee. "We've already had a cyber incident in the United States that has killed people."
At other times, Weiss has talked about a June 1999 gasoline pipeline rupture near Bellingham, Wash. That rupture spilled more than 200,000 gallons of gasoline into two creeks, which ignited and killed three people. Investigators found several problems that contributed to the rupture, but Weiss has identified a computer failure in the pipeline's central control room as part of the problem.
More
here.
Feds: Hacker Disabled Offshore Oil Platforms' Leak-Detection System
David Kravets writes on Threat Level:
A Los Angeles federal grand jury indicted a disgruntled tech employee Tuesday on allegations of temporarily disabling a computer system detecting pipeline leaks for three oil derricks off the Southern California coast.
Mario Azar, 28, faces a maximum 10-year term after being accused of purposely impairing a computer system that monitored for leaks on three Pacific Energy Resources platforms offshore of Huntington Beach.
"It was offline. The leak-detection system was rendered inoperable for a period of time," said Thom Mrozek, a spokesman for Los Angeles federal prosecutors.
More
here.
In Passing: Natasha Richardson

Combating Cyber Attacks Needs Cooperation
Via UPI.
Estonia's defense minister said Tuesday that countering the evolving security threat from cyberattacks will require strengthening international cooperation.
Jaak Aaviksoo, the Estonian defense minister, called on the international community to work together and share techniques and intelligence to counter the global cyber-terrorism threat.
Aaviksoo, speaking Tuesday at an Organization for Security and Cooperation in Europe cybersecurity workshop in Vienna, said that countries must be proactive about collaboration and efficient cooperation.
"All OSCE states would, in my opinion, benefit from a more clear-cut arrangement where countries could discuss and share know-how and expertise to improve their own and other states' capabilities to withstand cyber attacks," Aaviksoo said in a statement.
"This could come in the form of workshops or other forms of multilateral cooperation and would be especially beneficial for countries where cybersecurity is still evolving."
Link.
Note: It seems like I've heard this
before.
-ferg
True That: In Cyber Security, There Are No Silver Bullets
William Jackson writes on GCN.com:
Members of a panel of security experts today painted a gloomy picture of the cybersecurity landscape, in which rapidly evolving threats and conditions ensure that even the best solutions are likely to remain piecemeal and temporary.
Security efforts should focus on assessing and managing risk to information, members of the panel of industry and government officials said, and baseline security requirements mandated by government cannot be expected provide adequate security across the board.
“We should go in with our eyes open to the reality that if somebody wants the information, no matter what the baseline, they will get it,” said Wayne Fullerton, solutions and operations director for Cisco Systems Inc.’s U.S. federal organization.
Levels of security need to be assigned to a given piece of information based on its value to the owner and to those who could steal it. After the cost of stealing information drops below its perceived value, “if people really want it, they will get it,” Fullerton said.
More
here.
Toon of The Week: Failure Retention Program

By Mike Lukovich, via TruthDig.com.
- ferg
Criminals Sneak Card-Sniffing Software on Diebold ATMs
Robert McMillan writes on PC World:
Diebold has released a security fix for its Opteva automated teller machines after cyber criminals apparently broke into the systems at one or more businesses in Russia and installed malicious software.
Diebold learned of the incident in January and sent out a global security update to its ATM customers using the Windows operating system. It is not releasing full details of what happened, including which businesses were affected, but said criminals had gained physical access to the machines to install their malicious program.
"Criminals gained physical access to the inside of the affected ATMs," Diebold said in its security update. "This criminal activity resulted in the operation of unauthorized software and devices on the ATMs, which was used to intercept sensitive information."
The break-in occurred in Russia and affected "a number" of machines, said DeAnn Zackeroff, a company spokeswoman. "The incident was a low-tech break-in to the ATM, but they had a high-tech knowledge of how to install the virus," she said.
Diebold did not say exactly how the criminals were able to install the software on the systems, but its security update advises customers that there are several factors that can increase the risk of such a hack. They include using administrative passwords that have been compromised; not using the locked-down version of Windows that Diebold provides; or misconfiguring the Symantec firewall software that comes with the ATMs.
More
here.
IGP: Cyber-Safety, or Global Censorship?
Milt Mueller writes on the IGP Blog:
ICANN has encouraged new constituencies to get involved in the GNSO. Now it has got what it asked for. This month, Cheryl Preston filed a petition with ICANN to form a new “Cyber-safety Constituency.”
It turns out that this constituency is nothing more than an extension of the CP80 Foundation. CP80 is devoted to systematic, global censorship of internet content in order to eradicate pornography. Backed by Mormon religious activists based on Utah, the group frames its attempt to regulate internet content with talk of “protecting children online.” But it’s not just children’s Internet access they are targeting; it’s all of us.
More
here.
Hysterically Real Story of The Day: FAS as a 'Front Company'
Steven Aftergood writes on Secrecy News:
The Federation of American Scientists (FAS) is a “front company” that seeks “to expose national security information,” according to a new briefing on classification policy prepared by a U.S. Marine Corps official.
The 13 page briefing [.pdf], which pedantically explains the proper marking of derivatively classified records, suddenly veers off at page 10 into a factually mistaken claim that “all classified material is being challenged with a view to declassification.”
Out of nowhere, the anonymous briefer asserts that “The Federation of American Scientists is a good example of a front company trying to expose National Security Information under the pretense [probably should be: pretext] of ‘World Peace’.”
“‘No secrets in government’ is their mantra,” the briefing states.
That’s close, but the correct mantra is “No stupidity in government.”
More
here.
U.S. Cyber Security: Blurred Vision

I've been asked by some of my esteemed colleagues to start voicing my own opinions a bit more on the blog, "create some original content", and pour some of my own thoughts onto the Interwebs, so to speak.
This is probably not a great idea, but we'll see.
In any event, let's look at the topic at hand.
It has been beaten, butted, and batted around quite a bit in the past few weeks -- let's look at a rough timeline of political issues which bring me to this point.
Let's look at the power struggle (I prefer to call it confusion) in the U.S. Government with regards to "Cyber Security" -- in a nutshell.
In the latter part of 2008, the U.S. House of Representatives Homeland Security Committee determined that DHS was not capable of providing proper critical infrastructure protection (and other Cyber protection capabilities) due to a number of issues.
This may well be a political maneuver, or it may well actually have merit.
A number of other issues ensued, including the inauguration of a new U.S. executive administration, which gave this entire issue another direction entirely.
This is also probably due to a group of excellent InfoSec Professionals which were commissioned to produce a set of Cyber Security initiatives for the 44th Presidency. And they did an excellent job.
What becomes of that advice, however, is anyone's guess right now.
Which is what compels me to write this, at this late hour (both figuratively and literally).
The most recent "conflict" to appear on the the U.S. Cyber Security scene is being fought in the back rooms of the intelligence community, the political stage, and the operational community.
And it's not pretty.
What this penny-ante pissing contest is doing -- right now -- is pitting people against one another who would normally be helping each other, from a political and technical vantage point.
And that is not a good thing.
The major problem right now with regards to understanding, defending against, and both tactically & strategically winning the battle in Cyberspace is division of resources.
This fight cannot be won by a single U.S. Government agency, or any U.S. Government agency for that matter. Anyone who believes that is not only disconnected from reality, but also delusional, in denial, and probably doesn't properly understand the problem.
They simply don't have the same perspective, both technically and philosophically.
The problems are multi-fold -- cyber crime takes all shapes, forms, means, and methods. Governments, in my opinion, are woefully unprepared to even begin to understand this, much less prepared to handle these problems on their own.
Budgets are being slashed, there is no proper security training, and most infrastructure is hobbled together with only the slightest of security in mind.
And I'm not talking about SCADA systems, either. I'm talking about the basics.
This is a multi-stakeholder problem, and must become a "public-private relationship".
What does that mean?
Well, it means that we all need each other more than we realize.
There is already a lot of collaboration on a day-to-day basis between security researchers, incident response organizations, government entities (both foreign and domestic), law enforcement, etc.
But it is not working so well.
Why?
I'm not sure, but this entire discussion of "...who will be responsible for U.S. Cyber Security.." is the wrong discussion altogether.
We are all responsible.
And we are all failing.
$.02,
- ferg
Australia: Darwin Hacker Jailed for Three Years
Renai LeMay and Alex Serpo write on ZDNet.com.au:
A Northern Territory IT worker who caused millions of dollars of damage to government systems has reportedly been jailed for three years.
Computer engineer David Anthony McIntosh, 28, is a former CSG employee who crashed several government services at Berrimah Prison, Royal Darwin Hospital and the Supreme Court on 5 May last year. McIntosh also deleted over 10 thousand public servants from the system. CSG holds major contracts with the NT Government.
Ninemsn late yesterday reported McIntosh had been jailed for three years as a result of the system crashes, with Justice Stephen Southwood reportedly telling McIntosh he "didn't cause significant permanent harm (but) nonetheless it was malicious".
The Northern Territory News reported last year that McIntosh said he felt "isolated" and "stressed" due to his physical segregation from the rest of his team. McIntosh used his colleague's log-in and IP address to breach the systems.
More
here.
IRS Improves Cyber Security, But Still Vulnerable to Malware
Jill R. Aitoro writes on NextGov.com:
The Internal Revenue Service has improved its protection of computer networks from malicious software attacks, but it has failed to scan computers for viruses and to enforce security policies, which put taxpayer data at risk, according to a report the IRS inspector general released on Monday.
The IRS' Computer Security Incident Response Center identified and eliminated the increasing number of cyber threats that targeted agency networks, according to a review that the IG performed from October 2007 through September 2008. Based on incident data obtained from the center, the IRS responded to 661 malware incidents during calendar year 2007 and to 961 malware incidents in 2008.
More
here.
One-Year-Old (Unpatched) Windows 'Token Kidnapping' Under Attack
Ryan Naraine writes on the ZDNet "Zero Day" Blog:
Exactly one year after a security researcher notified Microsoft of a serious security vulnerability affecting all supporting version of Windows (including Vista and Windows Server 2008), the issue remains unpatched and now comes word that there are in-the-wild exploits circulating.
The vulnerability, called token kidnapping [.pdf], was originally discussed last March by researcher Cesar Cerrudo and led to Microsoft issuing an advisory with workarounds. Five months later (October 2008), Cerrudo released a proof-of-concept in an apparent effort to nudge Microsoft into patching but the company has not yet released a fix.
Now comes word from the SANS ISC (Internet Storm Center) that the flaw is being used in a blended attack against an unknown target. Incident handler Bojan Zdrnja discovered the token kidnapping component of the the attack while doing post-infection forensics...
More
here.
Pentagon Readies its Cyber War Defenses
Paul Marks writes on NewScientist:
Cyber-attacks on a nation's military and commercial computers have grown a lot more sophisticated since the days of the lone hacker targeting a system's defences just for the thrill of it.
Nowadays, electronic attacks are increasingly seen as a cheap and easy way for one nation to attack another. "It's the ultimate bargain hunter's way of destroying everyone's way of life," says Glenn Zimmerman, a cyberspace specialist at the Pentagon. "It may even be free."
So worried are governments by the prospect of an all-out cyber-attack that last month UN secretary-general Ban Ki-moon revealed that cyber-weapons are to be added to the list of arms falling under the remit of the UN's Advisory Board on Disarmament Matters, which develops policy on weapons of mass destruction. Ban said recent breaches of critical systems represent "a clear and present threat to international security", since the public and private sectors have grown increasingly dependent on electronic information.
But despite the threat, current NATO war games tend to treat cyber-attack simulations as an afterthought, according to military sources. Now the Pentagon is hoping to change that by developing a centre at which the military can play realistic electronic war games.
More
here.
Security Fix: Massive Profits Fueling Rogue Antivirus Market
Brian Krebs writes on Security Fix:
In the cyber underworld, more and more individuals are generating six-figure paychecks each month by tricking unknowing computer users into installing rogue anti-virus and security products, new data suggests.
One service, that exemplifies a very easy way these bad guys can make this kind of money is TrafficConverter.biz, one of the leading "affiliate programs" that pays people to distribute relatively worthless security software. Affiliates are given a range of links and Javascript snippets they can use to embed the software in hacked and malicious Web sites, or tainted banner advertisements online.
Unsuspecting users who view one of these hacked sites or ads see a series misleading warnings saying their computers are infected with malware, and offering a free scan. Those who agree are prompted to download a program that conducts a bogus scan and warns of non-existent threats on the user's system. The software also blocks the user from visiting legitimate security Web sites. The user is then pestered with increasingly deceptive and incessant prompts to purchase the software.
The user's system remains in this state until he or she figures out how to remove the software or relents and pays for a license. At that point, the affiliate responsible for generating that installation is paid by TrafficConverter.biz about $30. The software is sold for between $50 and $75 per license.
More
here.
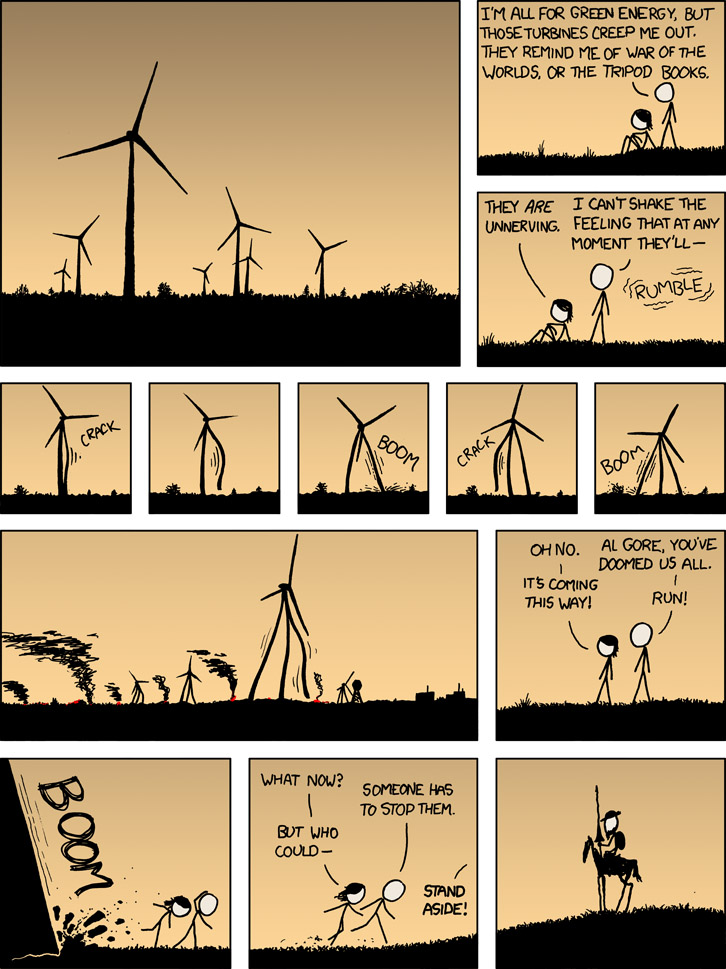
Classic xkcd: Tilting at Windmills
Click for larger image.
We
love xkcd.
Enjoy.
- ferg
In Passing: Ron Silver

Tweet This: I Don't Care
I can't help but tell you -- I hate Twitter.
It's just... useless. For me.
I already have a blog, which allows me to publish content in more than 140 characters.
What is the allure? Please, tell me.
If you want to "follow" me, good luck. Or rather, try my RSS feed.
Are people so absorbed in themselves that they really want to let everyone in the world know what they are doing at any given moment? Isn't that disturbing, in and of itself?
If you already have a blog, and Twitter, please don't tell me in your blog's RSS feed what you're Twittering about. It smacks of self-absorption and self-promotion.
Yikes. Scary.
Please. Stop it.
- ferg