Analysis: Secrets and 'Need to Know'
Lyle Denniston writes on the SCOTUS Blog:
The Justice Department, facing an impatient federal judge’s threat to rule summarily that the federal government has engaged in illegal electronic wiretrapping on a Muslim organization within the U.S., asked the judge Friday night to issue a direct order to disclose secret data over the government’s objections that would then set the stage for an appeal on issues “of extraordinary constitutional significance.”
Among those issues is whether a court has any authority to order disclosure of “state secrets” for use by a private party in a damages lawsuit, whether a law allowing such damages lawsuits overrides the government’s claim of a “state secrets” privilege against disclosing classified information, and whether a judge, not the government, can decide what a private party “needs to know” from secret government data for use in a lawsuit.
More
here.
Contractors Vie for Plum Work, Hacking for the United States
Christopher Drew and John Markoff write in The New York Times:
The government’s urgent push into cyberwarfare has set off a rush among the biggest military companies for billions of dollars in new defense contracts.
The exotic nature of the work, coupled with the deep recession, is enabling the companies to attract top young talent that once would have gone to Silicon Valley. And the race to develop weapons that defend against, or initiate, computer attacks has given rise to thousands of “hacker soldiers” within the Pentagon who can blend the new capabilities into the nation’s war planning.
Nearly all of the largest military companies — including Northrop Grumman, General Dynamics, Lockheed Martin and Raytheon — have major cyber contracts with the military and intelligence agencies.
The companies have been moving quickly to lock up the relatively small number of experts with the training and creativity to block the attacks and design countermeasures. They have been buying smaller firms, financing academic research and running advertisements for “cyberninjas” at a time when other industries are shedding workers.
The changes are manifesting themselves in highly classified laboratories, where computer geeks in their 20s like to joke that they are hackers with security clearances.
More
here.
Obama Says Government Sanctions Unwarranted in Spy Case
David Kravets writes on Threat Level:
The Obama administration refused to budge late Friday and agree to reveal state secrets in a lawsuit weighing whether a sitting president may lawfully bypass Congress and spy on Americans without warrants as President George W. Bush did following the 2001 terror attacks.
In court briefs filed at nearly midnight White House time, the Justice Department was responding to a federal judge’s week-old inquiry on whether the administration should be sanctioned for “failing to obey the court’s orders” in a key National Security Administration lawsuit. The government, as it has repeatedly, urged U.S. District Judge Vaughn Walker to allow the government to appeal his January 5 order requiring the government to develop a plan – a so-called “protective order” – that would pave the way to the release of state secrets to plaintiffs’ attorneys.
“The United States again respectfully urges the court to consider that the best way out of the present dispute, in which the position of all sides is preserved, would be to permit appellate review over the fundamental and significant separation of powers questions presented before any disclosure or risk of disclosure in further proceedings,” Anthony Coppolino, special litigation counsel for the justice department, wrote (.pdf) Walker.
Coppolino said sanctions were unwarranted because only the government can decide whether to disclose documents it believes are state secrets.
More
here.
'The Cyber Cop in Chief'
Ken Adelman writes on the Foreign Policy "The Argument" Blog:
There's an old adage about horsemeat: The more you chew, the bigger it gets. There's a new adage about cyberthreats: The more you know, the scarier they get.
Cybersecurity is vital to everything we do nowadays, from finance to romance. Just walk around any office -- whether medical, legal, public relations, manufacturing, service, whatever. Nearly everyone there is doing the same thing: sitting before a screen using a computer, mostly online. While cybersecurity is assumed, cyberinsecurity looms. It has morphed into a type of terrorism.
This morning President Obama told how today's terrorism comes "not only from a few extremists in suicide vests, but from a few key strokes of a computer." He dubbed the ability to cyberattack "a weapon of mass disruption." That's clever, but it shortchanges the danger.
Just last year were some 44,000 incidents causing the Pentagon alarm, no doubt many by Chinese authorities but some by geeky high-school hackers. Attacks across the U.S. federal government rose by some 40 percent last year, and bad guys in Iran got a hold of highly-sensitive blueprints for Marine One, and financial data on U.S. military helicopters. Other hackers apparently got their hands on data galore on the design and electronics of the new Joint Strike Fighter. One could go on.
More
here.
'The Zombies That Ran Wild in Washington'
Anne Davies writes in The Age:
A few weeks ago, in the offices of a Washington company that has close links to the Obama Administration, a server crashed, setting off an alarm.
The chief technology officer was puzzled. This sort of computer should not crash, so he printed out a log of the incident and then rebooted it.
Over the next few days, staff reported that their computers were sluggish and the technology officer started to suspect that the earlier alarm might have been the harbinger of a cyber attack.
Because of the sensitive nature of the work it was doing, the company called in the FBI. The log revealed that the server had been talking to a computer that runs the switchboard in a large hotel, even though it was not supposed to talk to anyone outside the company.
Records of the hotel's internet service provider showed that its system had been regularly talking to a computer in Shanghai, which was using the hotel computer as a command-and-control centre to relay instructions to compromised computers - the "zombies" - in the Washington office of the firm.
The zombies were coming alive each night and disgorging emails, directories, personal financial information and documents to a hacker in Shanghai, who investigators believe is part of a team sponsored by the Chinese Government to probe computers in the US.
The FBI knows who the hacker is. He left his initials in the virus - undetectable by more than 40 commercial antivirus programs. After visiting hacking chat rooms, the FBI identified a man with the initials in question and has even seen his photo on Facebook, but it is no closer to catching him.
More
here.
FAIL Blog: Risk Management FAIL

Via The FAIL Blog.
Enjoy!
- ferg
FBI e-Mail Clobbered After Virus
Robert McMillan writes on ComputerWorld:
A virus has reportedly disrupted Web-based e-mail services at the FBI.
The FBI confirmed today that it had been forced to shut down its Internet-facing unclassified network, but disputed a report that the incident had left the agency unable to e-mail counterparts in other intelligence and law enforcement agencies.
"The external, unclassified network was shut down by the FBI as a precautionary measure," the FBI said in a statement. "Within 48 hours of identifying the issue and mitigating risks, e-mail traffic was largely restored to the external, unclassified network."
FBI agents can send e-mail on the agency's more secure internal network or via BlackBerry, but many use this unclassified network to send messages via a Web-based e-mail system, said a source familiar with the situation. That webmail service was down throughout the week and continued to be unavailable for some users, the source said.
More
here.
A U.S. Cyber Warfare Command: Better Late Than Never
Ira Winkler writes on ComputerWorld:
In a class at the National Security Agency, I learned that prior to one World War II battle in the Pacific, key U.S. commanders knew an attack was coming but didn't warn anyone. The result was a major loss of life and equipment. But the decision not to warn anyone was a strategic consideration. Preparing people for an imminent attack would have given the Japanese an indication that their command communications had been compromised and that U.S. commanders were aware of all Japanese troop movements throughout the Pacific. Strategically, this single loss was preferable to losing the war.
This type of quandary becomes extremely more problematic when we are talking about cyberwarfare, where multiple units are doing the same type of work. For example, the Air Force Information Warfare Command (AFIWC) might want to break into foreign air defense facilities and blind them immediately before an air attack. That would provide a tactical advantage, at the price of showing that the AFIWC had compromised the facility. That much is comparable to the World War II scenario. But then add in the fact that the NSA might have separately compromised the same air defense facility and was using it to monitor deployments or to dig into the adversary's entire military network.
In a different scenario, the NSA could be working on a long-term project to enter false information into an adversary's database, unaware that the Army had hacked into the same database to try to track military movements. In that case, the Army intelligence efforts would be misled by the NSA's independent efforts to confound the adversary.
More
here.
Obama: Cyber Security is a National Security Priority
Brian Krebs writes on Security Fix:
President Barack Obama today pledged to make securing the nation's most vital computer networks a top economic and national security priority, broadly detailing the results of 60-day cyber security review that calls for a range of responses to help improve the security of information networks that power the government and the U.S. economy.
Speaking at the White House this morning, the president said he would work to make sure the nation's core digital infrastructure is treated as a national asset.
"Protecting this infrastructure will be a national security priority. We will ensure that these networks are secure, trustworthy and resilient." Obama said. "We will deter, prevent, detect, and defend against attacks and recover quickly from any disruptions or damage."
As expected, Obama said he plans to create a new office at the White House to be led by a cyber security coordinator "responsible for orchestrating and integrating all cyber security policies for the government; working closely with the Office of Management and Budget to ensure agency budgets reflect those priorities; and, in the event of major cyber incident or attack, coordinating our response."
More
here.
Hackers Infiltrate U.S. Army Servers
Paul McDougall writes on InformationWeek:
A known computer hacking clan with anti-American leanings has successfully broken into at least two sensitive Web servers maintained by the U.S. Army, InformationWeek has learned exclusively.
Department of Defense and other investigators are currently probing the breaches, which have not been publicly disclosed.
The hackers, who collectively go by the name "m0sted" and are based in Turkey, penetrated servers at the Army's McAlester Ammunition Plant in McAlester, Okla., and at the U.S. Army Corps of Engineers' Transatlantic Center in Winchester, Va.
The breach at the McAlester munitions plant occurred on Jan. 26, according to records of the investigation obtained by InformationWeek. On that date, Web users attempting to access the plant's site were redirected to a Web page that featured a protest against climate change.
More
here.
Police Can Forcibly Take DNA Samples During Arrests, Judge Rules
Declan McCullagh writes on C|Net News:
In the first case of its type, a federal judge in California has ruled that police can forcibly take DNA samples, including drawing blood with a needle, from Americans who have been arrested but not convicted of a crime.
U.S. Magistrate Judge Gregory Hollows ruled on Thursday that a federal law allowing DNA samples upon arrest for a felony was constitutional and did not violate the Fourth Amendment's prohibition of "unreasonable searches and seizures."
Hollows, who was appointed by President George H.W. Bush, said the procedure was no more invasive or worrisome than fingerprinting or a photograph. "The court agrees that DNA sampling is analogous to taking fingerprints as part of the routine booking process upon arrest," he wrote, calling it "a law enforcement tool that is a technological progression from photographs and fingerprints."
"The invasiveness of DNA testing is minimal," Hollows wrote (PDF). "The DNA can be taken by an oral swab, and even blood tests have been held to be a minimal intrusion."
More
here.
U.S. Toll in Iraq, Afghanistan

Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Thursday, May 28, 2009, at least 4,302 members of the U.S. military had died in the Iraq war since it began in March 2003, according to an Associated Press count.
The figure includes eight military civilians killed in action. At least 3,447 military personnel died as a result of hostile action, according to the military's numbers.
The AP count is two fewer than the Defense Department's tally, last updated Thursday at 10 a.m. EDT.
As of Thursday, May 28, 2009, at least 617 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Thursday at 10 a.m. EDT.
Of those, the military reports 455 were killed by hostile action.
More
here and
here.
And as always, the
Iraq Coalition Casualty Count keeps the grim watch on their website
here.
Honor the Fallen.
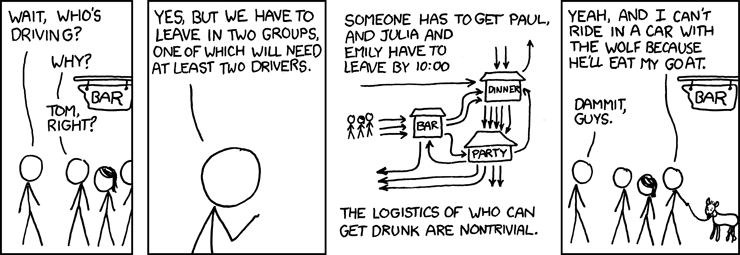
Classic xkcd: Designated Drivers (Been There)
Click for larger image.
We
love xkcd.
- ferg
Mark Fiore: Terrorist Lockup

More Mark Fiore brilliance.
Via The San Francisco Chronicle.
Enjoy!
- ferg
International Politics: Ukraine on The Brink
David J. Kramer and Damon Wilson write on Foreign Policy:
Russia has always had a knack for overshadowing its neighbors - and this time the West, focused on Moscow, is distracted from a crisis in Ukraine. As U.S. President Barack Obama gears up to "reset" Russia relations, Ukraine is in disarray. The country is teetering between economic collapse, Russian influence, and vague promises of Western support. It will take decisive moves from Washington to help pull Ukraine back from the edge. At the least, Obama should visit ailing Ukraine and prove that good relations with Russia don't meant forgetting the rest of the region.
Economic decline is largely to blame for Ukraine's perilous predicament. The country paid heavily for of its massive corporate foreign debt, failure to push through serious economic reform, and unwillingness to clean up a terribly corrupt energy sector. The International Monetary Fund and World Bank forecast an 8 to 9 percent drop in GDP this year, and that might be a conservative estimate; the economy has contracted some 30 percent in the first quarter alone. Ukraine's currency, the hryvnya, has fallen 40 percent against the dollar. Unemployment may reach 10 percent and mass protests are not out of the question -- especially in the troubled east.
More
here.
Note: Actually, U.S. engagement in The Ukraine is more important than ever -- and given the fact that U.S. Cyber Security Policy is on everyone's lips these days, engagement with The Ukraine is more important than anyone actually realizes. Most of the egregious organized cyber crime is being conducted from The Ukraine, as well as their "business associates" in Russia, Estonia, Latvia, and several other former Soviet satelite states.
-ferg
Botnet C&C Participation is a Corporate Data Breach
Gunter Ollmann writes on the Damballa "The Day Before Zero" Blog:
There are a lot of misconceptions within the IT industry when it comes to botnets and their criminal operators, but perhaps the most significant is the assumption that bot agents and their participation within a botnet is just a permutation of the malware threat.
Looking purely at the bot agent from a malware perspective really misses the point. Sure, from a feature/functionality perspective their evolutionary trails are clear to all who bother to look. However, membership within a botnet isn’t a linear scalar in a risk calculation – it fundamentally changes the risk to an enterprise and, even more importantly, has a regulatory impact.
While malware can be treated as an inconvenience, a host infected with a bot agent is technically a compromised asset. If the bot agent has successfully registered itself as a member of a botnet and its C&C is functioning, the enterprise network has been breached.
Let me restate that more succinctly – host membership within a botnet is a corporate data breach.
More
here.
DHS to Scan Fingerprints of Travelers Exiting the U.S.
Brett Winterford writes on ITNews.com.au:
The US Department of Homeland Security is set to kickstart a controversial new pilot to scan the fingerprints of travellers departing the United States.
From June, US Customs and Border Patrol will take a fingerprint scan of international travellers exiting the United States from Detroit, while the US Transport Security Administration will take fingerprint scans of international travellers exiting the United States from Atlanta.
Biometric technology such as fingerprint scans has been used by US Customs and Border Patrol for several years to gain a biometric record of non-US citizens entering the United States.
But under the Bush Administration, a plan was formulated to also scan outgoing passengers.
Michael Hardin, a senior policy analyst with the US-Visit Program at the United States Department of Homeland Security told a Biometrics Institute conference today that the DHS will use the data from the trial to "inform us as to where to take [exit screening] next."
More
here.
Hat-tip: /.
DHS Wants Budget to Back Cyber Security Efforts
William Jackson writes on GCN.com:
Just how the Obama administration manages cybersecurity has yet to be laid out in detail, but the Homeland Security Department is expected to maintain an important role, and the department’s budget request for the coming fiscal year includes additional money for the job.
DHS Secretary Janet Napolitano told the House Homeland Security Committee last month that the department is seeking an additional $75.1 million to help it develop and deploy cybersecurity technologies to counter “ongoing, real-world national cyber threats.” Defensive tactics would include deploying “effective analysis and risk-mitigation strategies to detect and deter threats” across government.
More
here.
Australia: Stolen Credit Data Published in Blog
Blair Speedy writes on Australian IT:
Victorian police are investigating a massive identity fraud involving the personal details of thousands of Australians that have been available on a blog site for more than a month.
The data, discovered by The Australian, includes thousands of Visa, Mastercard and American Express numbers, including expiry dates, together with home addresses, phone numbers and email addresses.
The list was posted on a free blogging site, where it was copied by search engine Google as part of its routine cataloguing of internet sites on April 21.
Victoria Police Sergeant Dave Spencer said the list appeared to have been collected from a number of sources before being sold to criminals.
"Lists like this come up for sale on the internet, and this is basically the end product of skimming and hacking of ATMs and other point-of-sale systems," Sergeant Spencer said.
More
here.
White House Expects Cyber Security Report Friday
Ben Bain writes on Washington Technology:
The Obama administration will release its long-awaited report on its 60-day review of federal government’s cybersecurity policy on May 29, according to White House Press Secretary Robert Gibbs.
“The administration recognizes the very serious threats public and private sector networks face from cybercrime and cyberattack,” Gibbs said during Tuesday’s press briefing. “Recognizing these threats the President has elevated cybersecurity to a major administration priority, undertaking the early comprehensive interagency review.”
The much-anticipated report is expected to include recommendations for a White House organizational structure to deal with cyber threats and an action plan to guide future efforts. In specific, the report is expected to put to answer the ongoing question of whether the White House will appoint a so-called cyber czar to coordinate efforts.
More
here.
Judge Rules LifeLock’s Fraud Alert Service Illegal
Kim Zetter writes on Threat Level:
In a decision that has privacy advocates and others scratching their heads, a federal judge has ruled that LifeLock has been breaking California law for years by placing fraud alerts on its customer’s credit profiles.
The decision is a blow to the burgeoning identify-theft protection industry, and means that companies that experience data breaches may no longer be able to offer victims free subscriptions to such services — a standard damage-control tactic in recent years. Consumers can still place fraud alerts by contacting one of the three U.S. credit reporting agencies directly.
Bo Holland, founder and CEO of Debix, a competitor of LifeLock, called the ruling “dramatic and unexpected.”
“It causes a real shift in the industry,” he told Threat Level.
More
here.
Bank Sues Savvis Over 2005 CardSystems Breach
Angela Moscaritolo writes on SC Magazine US:
Utah-based Merrick Bank claims to have lost $16 million as a result of a 2005 breach of payment card processor CardSystems Solutions and is now seeking legal restitution from an IT company it hired to audit the processor.
Merrick Bank is suing an information technology firm, Savvis, for negligence in its audit, which deemed the now defunct CardSystems compliant with Visa and MasterCard's card transaction security standards. According to a complaint filed on May 12, 2009 in U.S. District Court, Eastern District of Missouri, before doing business with CardSystems in 2004, Merrick Bank hired Savvis to assess whether the payment processor met Visa and MasterCard's security requirements.
In its audit, Savvis concluded that CardSystems had sufficient security solutions and operated in line with industry best practices. Savvis recommended that CardSystems be recognized as compliant with Visa's Cardholder Information Security Program (CISP), which ensured that payment card processors have a secure network infrastructure in place, and certain security policies and operational procedures are being followed.
More
here.
Cyber Criminals Already Gaming SCADA
Matt Hines writes on the eWeek "Security Watch" Blog:
Researchers at McAfee have stumbled onto something related to the problem that seems pretty innocent in terms of its overall impact, but which highlights the true gravity of the IT security challenges facing the infrastructure industries moving forward.
Last week, McAfee researcher Francois Paget discovered a video posted to YouTube in November 2008 in which two hackers gain access to the controls for a municipal central light system and then start playing a takeoff on the video game Space Invaders by manipulating it and turning building lights off and on.
Even though Paget openly questions the veracity of the videos, which he describes as "light-show attacks on unprepared buildings," the expert concedes that the video "confirms that hackers and cybercriminals have got their eyes on SCADA networks."
And while this simple gaming of a set of lights clearly carried out merely to prove hacking expertise is pretty benign in terms of its effect, Paget observes that no matter how harmless it may be, the tactics involved show off just the level of access that can be achieved in these environments - and by far less advanced groups than those who are suspected of doing so, such a those backed by foreign governments.
More
here.
Romanian Phisher Sentenced to 8 1/2 Years
Paul Walsh writes in the Star Tribune:
A Romanian immigrant has been sentenced to 8 1/2 years in prison for running a lucrative computerized "phishing" scheme that collected financial records and personal identification from thousands of individuals, including nearly 100 from Minnesota.
Sergiu D. Popa, 23, of Shelby Township, Mich., was sentenced Tuesday in federal court in Minneapolis for a plot that cost his 7,000 or so victims about $700,000, by his own admission.
"Because there were so many victims who were hurt badly, the court believes the sentence is appropriate in order to protect the public," said Judge John Tunheim. "There needs to be a deterrent to others who are trying similar crimes over the Internet."
More
here.
Verizon: Incompetent Training or Corporate Indifference?
Scott Bradner writes on NetworkWorld:
The news story sounded awful. A Verizon operator had refused to help police find a subscriber who was missing and likely in need of medical assistance because he was behind on his bill. One of many headlines said it all: "Verizon willing to let 62-year-old man die unless cops pay $20 of his overdue bill." I have no idea what actually happened, but what interests me is that it is entirely believable that someone working for Verizon would do something like this.
It has to be hard to be a PR person for a phone company because phone companies are awfully hard to like in the best of times. The 1967 movie "President's Analyst" portrayed The Phone Company as the common enemy of all mankind. It was not much of a stretch to accept that AT&T (The Phone Company at the time in the United States) was after world domination. To many of us concerned with the future of the Internet, the picture today is not all that much different than it was in 1967.
More
here.
NSA-Funded 'Cauldron' Tool Goes Commercial
Kelly Jackson Higgins writes on Dark Reading:
A vulnerability analysis tool used by the National Security Agency (NSA) and U.S. Department of Homeland Security is now commercially available for enterprises that want to either make sense of their reams of vulnerability data or trace an actual data breach.
The Cauldron tool, which was developed by George Mason University's Center for Secure Information Systems (CSIS) under a research grant by the NSA and Air Force Research Labs, automates the analysis of all of a network's potential attack paths, from the network to the application level. It takes in vulnerability data from scanners, aggregating and correlating that data with vulnerability databases.
The so-called Topological Vulnerability Analysis (TVA) technology also provides graphical representations of exploit sequences and paths that attackers can use to break into a network or application. "The [GMU] project looked at ways to improve on the efficiency of reviewing vulnerabilities and trying to focus on what vulnerabilities should be resolved first -- with tons of network scans and data," says Oscar Fuster, vice president of marketing for Epok, a software and integration firm that is offering Cauldron to its clients as well as for direct sale. "That's what the product does: It aggregates these globs of data and different scans, and correlates and maps it so you can visually see what an attack pattern might look like -- and not just an attack from the outside."
More
here.
Memorial Day Remembrances: You Are Not Forgotten

You Are Not Forgotten.
ITU Calls for Global Cyber Security Measures
Via The H Security.
The International Telecommunication Union ITU has published its proposals for harmonising global cybersecurity legislation on the periphery of a conference on the information society in Geneva. At a discussion session, ITU General Secretary Hamadoun Touré stated that the document, advertised as a "Cybersecurity Toolkit" is "no Bible and no Koran", instead offering a list of best practices from existing legislation.
Drafting of the document was entrusted to an expert group commissioned by the ITU and led by the American Bar Association's Privacy and Computer Crime Committee (PACC). In Geneva, PACC boss Jody Westby emphasised that legislation from many different countries was considered in producing the document, which is intended as a model for national legislation. In addition to the Council of Europe's 'Convention on Cybercrime', their search for model regulations also took in legislation from Australia, Canada, China and many other countries.
Certain stipulations, such as requirements on intellectual property, mean that the Council of Europe's convention is not suitable as a universal model, explained a representative from Brazil, which recently decided against acceding to the convention. Westby made clear that she does not care a jot whether or not countries sign the Convention on Cybercrime and that the aim of the ITU toolkit is the harmonisation of legislation targeted at cyber-criminality and not support for a single instrument. Touré admitted that a binding agreement on cyber-security under international law had encountered some resistance from member states. Rather than produce such an instrument, the ITU had instead chosen to put forward a toolkit of sample legislation.
More
here.
Gulags, Nukes and a Water Slide: Citizen Spies Lift North Korea's Veil
Evan Ramstad writes on The Wall Street Journal:
In the propaganda blitz that followed North Korea's missile launch last month, the country's state media released photos of leader Kim Jong Il visiting a hydroelectric dam and power station.
Images from the report showed two large pipes descending a hillside. That was enough to allow Curtis Melvin, a doctoral candidate at George Mason University in suburban Virginia, to pinpoint the installation on his online map of North Korea.
Mr. Melvin is at the center of a dozen or so citizen snoops who have spent the past two years filling in the blanks on the map of one of the world's most secretive countries. Seeking clues in photos, news reports and eyewitness accounts, they affix labels to North Korean structures and landscapes captured by Google Earth, an online service that stitches satellite pictures into a virtual globe. The result is an annotated North Korea of rocket-launch sites, prison camps and elite palaces on white-sand beaches.
"It's democratized intelligence," says Mr. Melvin.
More
here.
Props: /.