San Antonio NSA Data Center: The Panopticon Economy
Greg M. Schwartz writes on The San Antonio Current:
Surrounded by barbwire fencing, the anonymous yet massive building on West Military Drive near San Antonio’s Loop 410 freeway looms mysteriously with no identifying signs of any kind. Surveillance is tight, with security cameras surrounding the under-construction building. Readers are advised not to take any photos unless you care to be detained for at least a 45-minute interrogation by the National Security Agency, as this reporter was.
There’s a strangely blurry line during such an interrogation. After viewing the five photos I’d taken of the NSA’s new Texas Cryptology Center, the NSA officer asked if I would delete them. When I asked if he was ordering me to do so, he said no; he was asking as a personal favor. I declined and was eventually released.
America’s top spy agency has taken over the former Sony microchip plant and is transforming it into a new data-mining headquarters — oddly positioned directly across the street from a 24-hour Walmart — where billions of electronic communications will be sifted in the agency’s mission to identify terrorist threats.
“No longer able to store all the intercepted phone calls and e-mail in its secret city, the agency has now built a new data warehouse in San Antonio, Texas,” writes author James Bamford in the Shadow Factory, his third book about the NSA. “Costing, with renovations, upwards of $130 million, the 470,000-square-foot facility will be almost the size of the Alamodome. Considering how much data can now be squeezed onto a small flash drive, the new NSA building may eventually be able to hold all the information in the world.”
More
here.
Note: It is worth mentioning that
AT&T is headquartered in San Antonio, too.
-fergProps: /.
In Passing: Forrest J. Ackerman

U.S. Toll in Iraq, Afghanistan

Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Friday, Dec. 5, 2008, at least 4,209 members of the U.S. military have died in the Iraq war since it began in March 2003, according to an Associated Press count.
The figure includes eight military civilians killed in action. At least 3,395 military personnel died as a result of hostile action, according to the military's numbers.
The AP count is the same as the Defense Department's tally, last updated Friday at 10 a.m. EST.
As of Friday, Dec. 5, 2008, at least 557 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Friday at 10 a.m. EST.
Of those, the military reports 405 were killed by hostile action.
More
here and
here.
And as always, the
Iraq Coalition Casualty Count keeps the grim watch on their website
here.
Honor the Fallen.
Thieves Winning Online War, Maybe in Your PC
John Markoff writes in The New York Times:
Internet security is broken, and nobody seems to know quite how to fix it.
Despite the efforts of the computer security industry and a half-decade struggle by Microsoft to protect its Windows operating system, malicious software is spreading faster than ever. The so-called malware surreptitiously takes over a PC and then uses that computer to spread more malware to other machines exponentially. Computer scientists and security researchers acknowledge they cannot get ahead of the onslaught.
As more business and social life has moved onto the Web, criminals thriving on an underground economy of credit card thefts, bank fraud and other scams rob computer users of an estimated $100 billion a year, according to a conservative estimate by the Organization for Security and Cooperation in Europe. A Russian company that sells fake antivirus software that actually takes over a computer pays its illicit distributors as much as $5 million a year.
With vast resources from stolen credit card and other financial information, the cyberattackers are handily winning a technology arms race.
More
here.
Concerns Persist Over DHS Info-Sharing Network 'Upgrade'
Ben Bain writes on FCW.com:
The Homeland Security Department’s effort to upgrade its platform for sharing sensitive but unclassified information with its partners continues to draw concern from groups keeping an eye on the department’s plans.
On a conference call held Dec. 3, a group of outside experts advising the department on its effort to upgrade the Homeland Security Information Network (HSIN) agreed to a statement of support for the endeavor to upgrade the program.
However, the group, the HSIN Advisory Committee, still urges DHS to alter its approach to the HSIN Next Generation program, said Joe Rozek, who until last week was its chairman and remains a member of the committee.
More
here.
'Facebook Terrorists'?
Urmee Khan writes on The Telegraph:
A Bangladeshi military general has revealed that new generations of extremists are using social networks for terrorist activity.
Major General Muniruzzaman, a former military advisor and Chief of Staff to the President of Bangladesh, told MPs at a Parliamentary meeting on Tuesday evening that the young people from Asian communities in Britain are often more radicalised that their counterparts in South Asia.
He revealed that he would be writing a report next year examining ‘cross pollination’ with communities now living in the western nations and will be specifically studying the British Bangladeshi community and any possible links.
More
here.
Props: Danger Room
New Study: Board Members Not Watching Security, Business Risks
Linda McGlasson writes on BankInfoSecurity.com:
At a time when risks are high and consumer confidence is low, corporate boards of directors aren't paying nearly enough attention to information security and cyber threats.
This is the key takeaway from a new Carnegie Mellon University CyLab survey [.pdf], which shows that there is a "gaping hole as wide as the Grand Canyon" in board and senior executive oversight of these critical business issues.
The report draws on data from 703 individuals (primarily independent directors) serving on U.S-listed public company boards. Only 36 percent of the respondents indicate that their board has any direct involvement with oversight of information security. Of those respondents, 22 percent of them are from the financial services industry, where federal regulations mandate board responsibilities.
"The board members and CEO of these companies don't understand that information security governance is really the Grand Canyon and not a crevice," says survey author Jody Westby, Adjunct Distinguished Fellow at CyLab and CEO at Global Cyber Risk. "They don't understand that IT risks are corporate risks."
More
here.
Two Held Over BNP Membership Leak
Angela Balakrishnan writes on The Guardian:
Police have arrested two people in Nottinghamshire over the leak of the BNP membership list on the internet.
The arrests came as part of an investigation by the Welsh police, who are in charge of the case, and the information commissioner's office.
Police said the pair, who have not been named, were held in connection with alleged offences under the Data Protection Act.
A spokesman for Dyfed Powys police said: "We can confirm that last night Nottinghamshire police arrested two people as part of a joint investigation with Dyfed Powys police and the information commissioner's office in conjunction with alleged criminal offences under the Data Protection Act.
"The arrests followed an investigation into a complaint received about the unauthorised release of the BNP party membership list."
More
here.
FBI: Criminals Auto-Dialing With Hacked VoIP Systems
Robert McMillan writes on PC World:
Criminals are taking advantage of a bug in the Asterisk Internet telephony system that lets them pump out thousands of scam phone calls in an hour, the U.S. Federal Bureau of Investigation warned Friday.
The FBI didn't say which versions of Asterisk were vulnerable to the bug, but it advised users to upgrade to the latest version of the software. Asterisk is an open-source product that lets users turn a Linux computer into a VoIP (Voice over Internet Protocol) telephone exchange.
In so-called vishing attacks, scammers usually use a VoIP system to set up a phony call center and then use phishing e-mails to trick victims into calling the center. Once there, they are prompted to give private information. But in the scam described by the FBI, they apparently are taking over legitimate Asterisk systems in order to directly dial victims.
"Early versions of the Asterisk software are known to have a vulnerability," the FBI said in an advisory posted Friday to the Internet Crime Complaint Center. "The vulnerability can be exploited by cyber criminals to use the system as an auto dialer, generating thousands of vishing telephone calls to consumers within one hour."
More
here.
Friday Monkey Blogging: Diabetic Monkey Trained For Daily Insulin Injections

As I mentioned last month, I have started a regularly recurring blog entry meme every Friday afternoon, inspired by Bruce Schneier's regular series of "Friday Squid Blogging" posts, and my very own maddening Monkey Theory.
Here is this week's installment.
Richard Savill writes on The Telegraph.
George, a nine-year-old De Brazza monkey, knows when it is time for its insulin and is a willing volunteer when its keeper enters its enclosure each morning.
One of eight De Brazzas at Port Lympne Wild Animal Park in Ashford, Kent, the animal leaves its troop and scampers across to welcome its keeper.
"He presents himself at 9am, puts his bottom in the air, and has the insulin," said Tricia Corkhill, a spokesman for the park. "Afterwards he jumps up and wants his food."
Matt Crittenden, the monkey's keeper who is also a diabetic, said: "We have been very lucky because he has trained himself."
More
here.
Image source: The Telegraph / FERRARI
Three Charged with International Bank Trojan Scheme
Kevin Poulsen writes on Threat Level:
Two U.S. men and a Russian face conspiracy and bank fraud charges for allegedly running a successful scheme to compromise online banking and brokerage accounts and help themselves to the cash.
In a 15-month-long caper that ended in December of last year, prosecutors say Alexander Bobnev, of Volgograd, worked with others in Russia to infect U.S. consumers with Trojan horses that let the gang swipe the victims' login credentials.
Bobnev then initiated wire transfers from the hacked bank accounts -- and liquidated stocks from compromised brokerage accounts -- and channeled the money to "drop" accounts in the U.S., according to federal indictments filed last week in Manhattan.
Opening the drop accounts and pulling out the cash was allegedly the job of Aleksey Volynskiy, of Manhattan, and Alexey Mineev from Hampton, New Hampshire, who got to keep a portion of the loot for their efforts, according to the government.
More
here.
FBI Agent Accused of Trying to Help Pellicano
Scott Glover writes in the Los Angeles Times:
A veteran FBI agent has been accused of illegally accessing computers at bureau headquarters in Washington, D.C., in what prosecutors suspect was a failed bid to help Hollywood private eye Anthony Pellicano defend himself against federal racketeering and wiretapping charges, according to court documents and a source familiar with the case.
Mark T. Rossini, a charismatic and popular agent who once worked in the bureau's press office, was charged Monday with criminally accessing FBI computers on five occasions from January through July of last year, according to documents filed in U.S. District Court in Washington, D.C. Each of the charges is a misdemeanor.
Rossini allegedly was accessing the computers to find information that may have been helpful to Pellicano, who was tried and convicted of wiretapping and racketeering earlier this year in Los Angeles, said the source, who asked not to be named because he was not authorized to speak publicly about the case.
More
here.
Security at the IGF: Just Give Me the Money
Michel van Eeten writes on the IGP Blog:
Day two at the IGF.
Day two focuses on cybersecurity, meaning the main sessions are devoted to it. After the first session, I heard a participant say: “I know nothing about Internet security, but I didn’t hear anything new.” That about sums it up. It was depressing, frankly.
All presentations, from people related to different CSIRTs, ITU and Cisco, were rehashed arguments that we have been hearing for years. Their slides could have been made in 2005 and no one would have noticed. The storyline is all too familiar: cybercrime is exploding and therefore we need more collaboration, more CSRITs, more education, more international cooperation among law enforcement, more sharing of information, et cetera.
I’m sure you’ve heard it all before. This type of story marries an alarmist diagnosis to a set of answers that do nothing to remedy the alarmist diagnosis.
More
here.
UK: DNA 'Innocents' Must Be Wiped After Landmark Human Rights Ruling
Christopher Hope and Tom Whitehead write in The Telegraph:
The European Court of Human Rights ruled retaining the samples of those who were acquitted of crimes or never charged with them breached their human rights in test case brought by two Sheffield men.
It means the DNA profiles of around 850,000 innocent people could have to be removed while a similar number of individuals' prints could have to be taken off the national fingerprint database.
The ruling has grave consequences for a key weapon in police investigations and the Home Secretary, Jacqui Smith, said she was "disappointed" with the decision.
The Home Office now has until March to respond to the ruling but experts said it was likely to abide by it to avoid hundreds of thousands of challenges in the courts.
One likely option is to set a time limit after which samples are removed, similar to schemes run in other countries, including Scotland.
More
here.
Patch Tuesday: Eight Security Updates On Tap
Robert Vamosi writes on C|Net News:
The final Patch Tuesday for 2008 will be big, with six critical bulletins and two important bulletins due, according to Microsoft.
On Thursday, the company announced eight security bulletins set to go public December 9. The pre-announcement is intended as a heads-up for IT departments before Patch Tuesday. Six bulletins are considered "critical," the most serious ranking given by the software giant. Two are considered "important," the next level down.
Among the critical patches, two affect Windows, and there is one each that addresses issues in Word, Excel, Visual Basic, and Internet Explorer. All flaws could enable remote code execution if exploited.
More
here.
Berlusconi Plans to Use G8 Presidency to 'Regulate the Internet'
Chris Williams writes on The Register:
Italian president and media baron Silvio Berlusconi said today that he would use his country's imminent presidency of the G8 group to push for an international agreement to "regulate the internet".
Speaking to Italian postal workers, Reuters reports Berlusconi said: "The G8 has as its task the regulation of financial markets... I think the next G8 can bring to the table a proposal for a regulation of the internet."
Italy's G8 presidency begins on January 1. The role is taken by each of the group's members in rotation. The holder country is responsible for organising and hosting the G8's meetings and setting the agenda. Italy's last G8 presidency in 2001, also under Berlusconi, was marred by riots at the annual meeting in Genoa.
Berlusconi didn't explain what he meant by "regulate the internet", but the mere mention of it has prompted dismay among Italian commentators. Berlusconi owns swathes of the Italian mass media.
More
here.
Experts' Report Urges Changes in National Security System
Walter Pincus writes in The Washington Post:
A bipartisan panel of foreign policy experts, including some associated with the incoming Obama administration, has recommended changes in the White House national security apparatus that would provide the president and his staff with new tools to ensure interagency cooperation.
Chief among its recommendations is merging the National Security and Homeland Security councils and creating a director for national security who would manage implementation of the president's policies rather than just coordinate the views of Cabinet members and present them to the president, as the national security adviser currently does.
"The basic deficiency of the current national security system is that parochial departmental and agency interests, reinforced by Congress, paralyze interagency cooperation even as the variety, speed and complexity of emerging security issues prevents the White House from effectively controlling the system," says the report of the Project on National Security Reform, released yesterday.
As an example, the report said that "after more than seven years, the U.S. government has proved unable to integrate adequately the military and nonmilitary dimensions of the complex war on terror."
More
here.
Israeli Telephone Commandos Strike Again
Reported via the Strategy Page.
Recently, Israel hacked into the Syrian phone system, and sent thousands of messages to Syrians offering a $10 million reward for information on the whereabouts of missing Israeli soldiers. Syrian intelligence officials believe the campaign was more interested in recruiting intelligence agencies. Many Syrians thought it was all an attempt by their own government to find and identify disloyal citizens. Whatever the case, such an attack is nothing new.
For the last two years, Israel has been hacking into Lebanon based Hezbollah radio and TV broadcasts, and inserting messages that point out mistakes Hezbollah has made, or lies Hezbollah has been pushing, or simply ridiculing the Islamic radicals. Israeli Information War teams have also spammed Lebanese cell phone users with anti-Hezbollah voice mail and text messages.
More
here.
Note: There are no verifiable external resources listed to support this claim.
-ferg
Mark Fiore: Greater Georgelandia

More Mark Fiore brilliance.
Via The San Francisco Chronicle.
- ferg
Air Force CIO: Cyber Security is Federal 'Achilles' Heel'
Jill R. Aitoro writes on NextGOV:
Until best practices in information security become pervasive across all aspects of the enterprise, agencies' networks remain at risk, said a top technology chief with the Air Force at a conference Wednesday, calling cybersecurity one of the federal government's most overlooked and critical weaknesses.
"There's too much fighting about cyber -- how big [a concern] it is, who owns it," said Lt. Gen. Michael Peterson, chief information officer at the Air Force, during a keynote at Air Force IT Day, sponsored by the Armed Forces Communications and Electronics Association of Northern Virginia.
"This is our Achilles' heel," he said. "It's not about a denial-of-service attack; it's about the information on the network -- ensuring it's accurate, protected, and available. [But] we're still fighting over what patch to put on."
Despite Russia's cyberwarfare tactics against Estonia and Georgia, Peterson said an all-out cyberwar won't happen; instead, cyberattacks will become one of many combat strategies used by adversaries to bring government to its knees.
More
here.
Hat-tip: IntelFusion
FBI: Copper Thieves Threaten U.S. Infrastructure
David Kravets writes on Threat Level:
Copper thieves, sometimes acting as "organized groups," are threatening what the FBI said is "critical" U.S. infrastructure, from electrical sub-stations, cellular towers, telephone land lines to railroads and crops, the agency said in an unclassified report unveiled Wednesday.
The report, Copper Thefts Threaten US Critical Infrastructure, said bandits are taking advantage of unprecedented high prices for copper, an almost 500 percent increase since 2001 as measured earlier this year.
But perhaps market forces can stop crimes that law enforcement officials cannot.
The FBI publicized the unclassified report the same day stocks of global mining concerns were battered as operations worldwide gear up for a 50 percent reduction in copper prices. Shares of Arizona-based Freeport-McMoRan Copper & Gold, the world's largest copper supplier, plummeted nearly 20 percent Wednesday as the company suspended dividends, cut spending and scaled back copper production to adjust to weakening demand amid a global economic slump.
More
here.
Whither Cisco MARS?
Jon Oltsik writes on C|Net News:
Cisco System's Security Monitoring for Threat Identification, Mitigation, and Compliance (aka MARS) product is the company's offering for security and compliance management, competing with the likes of ArcSight, RSA Security, and Symantec. The MARS product came via Cisco's acquisition of Protego for $65 million in December 2004.
Through 2005 and 2006, Cisco pushed this product into end-user accounts through an aggressive scorched-earth effort. Cisco intended to get the product out into the market quickly, establish a base, and then continually add product enhancements over time. This seems to be where the strategy hit a speed bump.
The product languished behind competitive offerings, causing problems with the installed base. This opened the door for aggressive competitors: Enterasys, Juniper, and Nortel established partnerships with Q1 Labs in a direct attack on MARS. Log management vendors like LogLogic and LogRhythm out-flanked Cisco with incremental products. Worst of all, some Cisco sales executives and channel partners eschewed MARS in favor of more popular Cisco products. When you have a portfolio of hundreds of products, it is easy to lead with your best stuff and never mention those in the doghouse.
More
here.
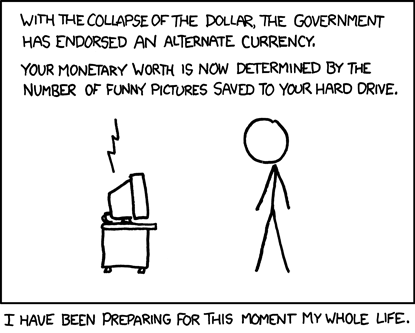
Classic xkcd: Alternate Currency
Click for larger image.
No kidding.
We
love xkcd.
- ferg
Russians Track Crippled U.S. Spy Satellite
A Space.com article by Leonard David, via MSNBC.com, reports that:
Even in the vacuum of outer space, it's hard to keep the sound of a secret quiet.
The U.S. Air Force apparently has a malfunctioning Defense Support Program satellite on its hands. DSP-23 is one piece of a constellation of such Earth-staring satellites designed to detect missile launchings and nuclear detonations, and gather other technical intelligence.
DSP-23 seems to be drifting out of its high-altitude slot — and might prove troublesome to other high-value satellites in that populated area.
One person who has flagged the problem to a U.S. satellite tracking expert is a Russian space analyst — a project partner of the International Space Observation Network, or ISON for short.
More
here.
Leaked U.S. Army Files Highlight Dangers of Peer-To-Peer
Via The Wall Street Journal.
Organizations that have suffered data breaches usually rush to plug technology or policy holes that led to the loss of information, but trying to retrieve data that has already leaked can be a difficult task.
Consider the case of an apparent data breach of Army soldiers’ names and personal information, the details of which were described in an August letter sent by then Sen. Joseph Biden to Pete Geren, secretary of the Army. The letter, which has been reviewed by The Wall Street Journal, mentions “files containing the personal identifying information of nearly 24,000 U.S. soldiers” that became publicly accessible through a so-called peer-to-peer network. “The files include full names and social security numbers” of the soldiers, the letter says.
The Army wouldn’t confirm or deny the existence of the files, and said it doesn’t comment on ongoing investigations or incidents. A spokeswoman replied in an email that the Army has taken steps in recent months to boost its security. However, there’s little it can do about information on computers the government doesn’t control; in that situation, “the Army can only ask the owner of a public site to remove the information,” she says in the email.
In this case the files—spreadsheets that appear to be lists of soldiers due for promotion—made their way to a peer-to-peer file-trading network, which lets people connect their computers directly to one another. People most commonly use these networks—examples include Limewire and BitTorrent—to swap music files or videos.
More
here.
eBay Users Say Holiday Giveaway Was Hacked
Bob Sullivan writes on the MSNBC "Red Tape Chronicles" Blog:
eBay.com users are complaining that a holiday contest offered by the auction Web site has been over-run by Scrooge-like computer hackers, and that eBay’s poor design for contest is to blame.
As part of its "Holiday Doorbusters" promotion, eBay is giving away about 1,000 items -- everything from jet skis to iPods to a Corvette -- for $1. The first buyer to find and bid $1 on the specially-marked items wins. But users say the contest has been overrun by "cheaters" who are implementing automated scripts to game the contest, winning hundreds of auctions before the items are even available to the public.
As evidence, the disgruntled point to a number of closed auctions where the visitor counter shows “0000,” meaning no Web users visited the item’s page before it was won. On Saturday, for example, a "Green Life" brand electric scooter worth $1,000 was won by a bidder before anyone visited the page, according to the counter on it. The next day, a vintage Oscar de la Renta evening gown was also won with the counter reading zero.
Forums devoted to eBay users are ablaze in complaints about the contest from disappointed would-be bidders who haven’t won.
More
here.
In Courtroom Showdown, Bush Administration Demands Amnesty for Spying Telecoms
David Kravets writes on Threat Level:
The Bush administration on Tuesday will try to convince a federal judge to let stand a law granting retroactive legal immunity to the nation's telecoms, which are accused of transmitting Americans' private communications to the National Security Agency without warrants.
At issue in the high-stakes showdown — set to begin at 10:00 a.m. PST — are the nearly four dozen lawsuits filed by civil liberties groups and class action attorneys against AT&T, Verizon, MCI, Sprint and other carriers who allegedly cooperated with the Bush administration's domestic surveillance program in the years following the Sept. 11 terror attacks. The lawsuits claim the cooperation violated federal wiretapping laws and the Constitution.
In July, as part of a wider domestic spying bill, Congress voted to kill the lawsuits and grant retroactive amnesty to any phone companies that helped with the surveillance; President-elect Barack Obama was among those who voted for the law in the Senate. On Tuesday, lawyers with the Electronic Frontier Foundation are set to urge the federal judge overseeing those lawsuits to reject immunity as unconstitutional. At stake, they say, is the very principle of the rule of law in America.
More
here.
CBS Website Bitten by iFrame Hack
John E. Dunn writes on Techworld:
TV network CBS has become the latest big name to have it website used to host malware, a security company has reported.
It appears that Russian malware distributors were able to launch another iFrame attack on a sub-domain of the cbs.com site so that it was serving remote malware to any visitors.
A user's vulnerability to the malware attack launched by the site hack would depend on a number of factors, including the type of security used on a PC, the operating system, and possibly the browser version.
More
here.
Massachussetts City Theft Highlights Prevalence of Hackers
George Brennan writes on The Cape Cod Times:
The theft of $34,000 from a town bank account is part of growing underground economy centered on cyber crime, a top law enforcement official says.
"It's massive, it's growing and it's transnational," said Scott O'Neal, chief of the FBI's Washington-based computer intrusion section. "There are cyber criminals and cyber victims in many different countries."
Sandwich police say hackers stole the password and security information for a town bank account earlier this month and made four illegal wire transfers. The town treasurer noticed the bogus transactions while attempting to pay the town's weekly bills.
Bank officials told the town the wire transfers were made using Treasurer Craig Mayen's name and password, police said. Investigators believe the hackers breached the town computers using a virus that logged Mayen's key strokes.
Sandwich police Detective Albert Robichaud was able to trace the transfers to banks in Florida and Georgia in the United States, Police Chief Michael Miller said Tuesday. At least one of those transactions was traced to St. Petersburg, Russia, an indication to law enforcement that organized crime may be involved.
More
here.
Secret Geek A-Team Hacks Back, Defends Worldwide Web
Joshua Davis writes on Wired.com:
In June 2005, a balding, slightly overweight, perpetually T-shirt-clad 26-year-old computer consultant named Dan Kaminsky decided to get in shape. He began by scanning the Internet for workout tips and read that five minutes of sprinting was the equivalent of a half-hour jog. This seemed like a great shortcut—an elegant exercise hack—so he bought some running shoes at the nearest Niketown. That same afternoon, he laced up his new kicks and burst out the front door of his Seattle apartment building for his first five-minute workout. He took a few strides, slipped on a concrete ramp and crashed to the sidewalk, shattering his left elbow.
He spent the next few weeks stuck at home in a Percocet-tinged haze. Before the injury, he'd spent his days testing the inner workings of software programs. Tech companies hired him to root out security holes before hackers could find them. Kaminsky did it well. He had a knack for breaking things—bones and software alike.
But now, laid up in bed, he couldn't think clearly. His mind drifted. Running hadn't worked out so well. Should he buy a stationary bike? Maybe one of those recumbent jobs would be best. He thought about partying in Las Vegas ... mmm, martinis ... and recalled a trick he'd figured out for getting free Wi-Fi at Starbucks.
More
here.
Military State? Pentagon Plan Would Deploy 20,000 Uniformed Troops Inside U.S. By 2011
Spencer S. Hsu and Ann Scott Tyson write in The Washington Post:
The U.S. military expects to have 20,000 uniformed troops inside the United States by 2011 trained to help state and local officials respond to a nuclear terrorist attack or other domestic catastrophe, according to Pentagon officials.
The long-planned shift in the Defense Department's role in homeland security was recently backed with funding and troop commitments after years of prodding by Congress and outside experts, defense analysts said.
There are critics of the change, in the military and among civil liberties groups and libertarians who express concern that the new homeland emphasis threatens to strain the military and possibly undermine the Posse Comitatus Act, a 130-year-old federal law restricting the military's role in domestic law enforcement.
But the Bush administration and some in Congress have pushed for a heightened homeland military role since the middle of this decade, saying the greatest domestic threat is terrorists exploiting the proliferation of weapons of mass destruction.
More
here.
Classic xkcd: Defective By Design
Click for larger image.
We
love xkcd.
Enjoy!
- ferg
60 Minutes: How Online Gamblers Unmasked Cheaters

Via CBS News/60 Minutes.
In the wild, wild west, when a poker player was caught cheating it was a capital offense, with the punishment quickly dispensed right across the card table. But today if you're caught cheating in the popular and lucrative world of Internet poker, you may get away scot-free.
At least that seems to be what is happening in the biggest scandal in the history of online gambling. A small group of people managed to cheat players out of more than $20 million.
And it would have gone undetected if it hadn't been for the players themselves, who used the Internet to root out the corruption. As a joint investigation by 60 Minutes and The Washington Post reveals, it raises new questions about the integrity and security of the shadowy and highly profitable industry that operates outside U.S. law.
Much more
here.
Image source: CBS News / 60 Minutes
Canada Backpedals on Sharing Personal Database With U.S.
Via CKWS-TV.
Ottawa has quietly dropped plans to let the United States house a database of personal information about Canadians who hold special driver's licences aimed at better securing the border.
The move follows vocal criticism from federal and provincial privacy commissioners, who warned earlier this year the scheme could open the door to abuse of the sensitive data.
However, the office of federal Privacy Commissioner Jennifer Stoddart is still wary of the plan to share information on so-called enhanced driver's licences with the United States, and stresses the passport is still the ideal travel document for Canadians.
More
here.
Hat-tip: Pogo Was Right