U.S. Spy Chief Scraps Stealth Satellite Program
An AP newswire article by Katherine Shrader, via MSNBC, reports that:
Spy chief Mike McConnell has junked a multibillion-dollar spy satellite program that engineers hoped would someday pass undetected through the space above other nations.
The move from the director of national intelligence comes after several years of congressional efforts to kill the program, known publicly as the next generation of “Misty” satellites. The new satellite was to be a stealthy intelligence spacecraft designed to take pictures of adversaries and avoid detection.
Little is known about the nation’s classified network of satellites, which represent some of the most expensive government programs and receive almost no public oversight. Because of their multibillion-dollar price tags, sensitive missions and lengthy development schedules, spy agencies go to great pains to keep details from becoming public.
More
here.
MPack: Nasty Malware Toolkit Making the Rounds
Matt Hines writes on InfoWorld's "Zero Day" Blog:
Security researchers at VeriSign are tracking the emergence of a dangerous malware development kit being sold on the Russian underground that is being used to level many different types of threats at unprotected computers.
Dubbed MPack, the kit -- which is trading hands for roughly $1,000 -- is empowering stealthy malware attacks on Web browser vulnerabilities, and claiming roughly a 50 percent success rate, according to Ken Dunham, senior engineer and director of the Rapid Response Team in VeriSign's iDefense security unit.
Dunham said in an e-mail that MPack is using multiple exploits "in a very controlled manner" to infect vulnerable computers.
More
here.
Also, Symantec has put up a nice video of MPack in action
here.
Europeans Widen Investigation Into Search Data
An AP newswire article, via The New York Times, reports that:
A European Union investigation set off by concerns over how long Google stores user information has widened to include all Internet search engines.
The European Union’s panel of national data protection officers said it was now concerned over the retention of data that the companies use to deliver more-relevant search results and advertising. Some fear the data could be sought by hackers and governments.
The panel “will deal with search engines in general and scrutinize their activities from a data-protection point of view, because this issue affects an ever-growing number of users,” it said in a statement on Thursday.
More
here.
Attorneys Lock Horns in NSA Wiretapping Case
Henry Weinstein writes in The Los Angeles Times:
A Justice Department attorney sparred with lawyers for five states in federal court here [San Francisco] Thursday over the Bush administration's attempt to block states from investigating whether phone companies illegally shared customer information with the National Security Agency.
The case stems from a newspaper report published last year alleging that AT&T and Verizon had cooperated with the government on its Terrorist Surveillance Program. That program has spawned several major court cases because of allegations that the U.S. engaged in secret wiretapping of individuals without seeking warrants.
Last year, five states — Connecticut, Maine, Missouri, New Jersey and Vermont — asked the telephone companies whether they had turned over customer records to the NSA, contending that doing so might have violated state privacy laws.
Although the requests were not identical, they all generated concern in the government, which has taken the position that any revelations about the wiretapping program could endanger national security.
More
here.
Silly Picture of the Day: Drone On

Via LOL Bots.
Internet Terrorism Trial Highlights Web Open Info Access Dilemma
Larry Greenemeier writes on InformationWeek:
A husband and wife charged with running Web sites that supported terrorists by providing them information on how to make bombs went on trial in Switzerland Wednesday.
Moez Garsallaoui, a 39-year-old Tunisian based near Fribourg, in western Switzerland, and first detained in February 2005, is accused of running Internet discussion forums used by terror groups to share information and to publicize claims of responsibility for attacks and threats against Westerners. Swiss prosecutors demanded two years of prison for Garsallaoui, six months of which would be suspended.
Malika El Aroud, a 48-year-old Belgian-born widow of an al-Qaeda suicide bomber and Garsallaoui's wife, stands accused of operating an Islamist Web site. The widow of one of the suicide attackers who killed the anti-Taliban Afghan warlord Ahmed Shah Massoud two days before the Sept. 11, 2001, attacks, El Aroud is facing a 12-month suspended prison sentence.
Both Garsallaoui and El Aroud this week pleaded innocent to the charges against them.
More
here.
Feds' Own Hacker Cracks Homeland Security Network
Sharon Gaudin writes on InformationWeek:
Within the past year, a hacker secretly broke into the Department of Homeland Security network and deleted, updated, and captured information -- all without anyone knowing he was even in there.
Luckily, the hacker was Keith A. Rhodes, chief technologist at the U.S. Government Accountability Office. Rhodes, considered to be the federal government's top hacker, has a congressional mandate to test the network security at 24 government agencies and departments. He performs 10 penetration tests a year on agencies such as the IRS and the Department of Agriculture. And for the past year, he's been testing the network at DHS.
"I would label them [DHS] as being at high risk," Rhodes told InformationWeek the day after a congressional hearing into the security of the government agency tasked with being the leader of the nation's cybersecurity. "There was no system we tested that didn't have problems. There was nothing we touched that didn't have weaknesses, ranging from WAN to desktops. ... If we had continued the audit we would have found more. We curtailed the audit because we just kept finding problems. At a certain point, we just ran out of room in our basket."
More
here.
Meet Verizon, King of ISP Spammers
Larry Seltzer writes on eWeek:
The biggest spammer in the world is a huge, imposing presence in the Internet, known for mercilessly wiping out opposition. China? Russia? No, you guessed it: It's Verizon.
The numbers come from Trend Micro, one of the biggest security companies in the world. I've known Dave Rand, chief technology officer of Trend Micro Internet Content Security, for years. He is a pioneer of much basic software for e-mail and other computing essentials, and a founder of MAPS (Mail Abuse Prevention System) with Paul Vixie, another computing pioneer. The MAPS RBL, the blacklist with perhaps the most clout on the Internet, is now also with Trend Micro. I sat down to lunch with Dave on June 20.
More
here.
Russians Say Quicken Backdoor Could Give Feds Access to Finance Data
Gregg Keizer writes on ComputerWorld:
A Moscow-based password-recovery vendor today accused Intuit Inc. of hiding a backdoor in its popular Quicken personal finance program that gives it -- and perhaps government agencies -- access to users' data files.
Intuit called the charges baseless, and said that although there is a way to unlock Quicken's encrypted data, it's only used by the company's support team to help customers who have forgotten their passwords.
In a statement released today, Elcomsoft Co. Ltd., a Russian maker of password-recovery tools, said Quicken versions since 2003 have used strong encryption designed to foil hackers. But those editions also have a backdoor that unlocks the encryption with the 512-bit RSA key that Intuit controls.
More
here.
Committee Approves Subpoena Authority on NSA Snooping
Via CDT.org.
The Senate Judiciary Committee today voted 13-3 to give Chairman Patrick Leahy (D-VT) the authority to issue subpoenas for information and documents relating to the administration's warrantless wiretapping of Americans.
CDT [Center for Democracy & Technology] supports the committee's effort to conduct rigorous oversight on warrantless surveillance activities to determine the extent to which they have impacted Americans' privacy rights. The administration is seeking to rewrite the Foreign Intelligence Surveillance Act to legalize warrantless wiretapping of Americans who communicate with people abroad or with foreign embassies and related entities in the U.S.
CDT renewed its call for Congress to convene a joint inquiry to take a serious, in-depth look at domestic surveillance in the U.S. and whether current law is adequate to protect privacy in the digital age.
More
here.
Zone-H DDoS'd, AOL and Intel Defaced
Marcelo dos Santos de Almeida writes on Zone-H News:
Three different dDoS attacks temporarily took Zone-H offline for some days, preventing Zone-H team to publish news and to update our Attacks Archive. Now that all Zone-H activities have been restored we point out some important digital events that affected both companies and governmental websites during last weeks.
One of the most worth noticing attack was carried out by a Turkish defacer against Intel and AOL’s website, based in Puerto Rico.
There is still no documented clue about how the attacker managed in penetrating the web server, but he is likely to have used a recent flaw in Solaris where a correct exploitation results in a remote code execution.
More
here.
Malware Knocks Defense Department e-Mail Offline - UPDATE
Robert Vamosi writes on the C|Net News Blog:
According to the Associated Press, the US Defense Department took 1,500 computers offline as the result of a cyber attack. No additional information about the event was provided. Defense Secretary Robert Gates said the attack happened sometime yesterday and that e-mail systems were expected to be back online later today.
Gate said during a press conference on the matter: "We obviously have redundant systems in place. ... There will be some administrative disruptions and personal inconveniences." When asked if he, personally, had been inconvenienced, Gates replied that he's a very low tech person. "I don't do e-mail."
More
here.
UPDATE: 05:00 PDT, 22 June 2007: More details available
here.
LexisNexis Warns of Consumer Database Breaches
Brian Krebs writes on Security Fix:
Last month, Security Fix wrote that scam artists were trying to steal the login credentials that law enforcement officers use to access their accounts at Accurint, a database operated by LexisNexis owner ReedElsevier that contains highly detailed and personal files on millions of Americans.
It would seem as though those efforts have been successful.
The company recently sent out an undetermined number of letters to consumers across the country, stating that "...a law enforcement customer's user ID may have been used in an unauthorized manner that allowed some personal information about you to be viewed..." The letter, dated May 25, said thieves had accessed the recipient's personal data, which may have included the victim's name, address, Social Security and/or drivers license number. It also offered free Equifax monitoring through a promotional code.
Sources familiar with the incident said the letters were sent after it was discovered that a number of accounts were compromised at a federal law enforcement agency, though the source declined to say which agency was targeted.
More
here.
Programming Note: Vacation

Yes, headed back east to see family.
Blogging will be spotty starting today (Thursday) , for about a week.
I might sneak a few posts in here & there. :-)
Cheers,
- ferg
Dark Web: 'The Bad Side of Town'
This is a quote I often use to explain to people that it's just not an issue of "...surfing only trusted websites..." anymore to avoid malware-laden, exploits, and other "hostile" content -- it's all suspect territory these days.
Roger Thompson, over at Exploit Prevention Labs, is doing a great job by posting a daily summary of "Dangerous Searches" -- showing that, as I have been saying for some time now, it's a wild, wild web world out there.
Even doing a web search can get you infected if you are not properly protected.
Great job, Roger.
Let's be careful out there!
- ferg
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Wednesday, June 20, 2007, at least 3,531 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,897 died as a result of hostile action, according to the military's numbers.
The AP count is two higher than the Defense Department's tally, last updated Wednesday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Toon of the Day: Global Warming - A Slam Dunk
Click for larger image.
TSA Tosses Sensitive Docs in Airport Dumpster
Audrey Hudson writes in The Washington Times:
Homeland Security officials are being warned not to toss secret documents that could compromise transportation security into the ordinary trash after hundreds of such papers marked "sensitive" reportedly were found in a city trash container near the Orlando International Airport in Florida.
The Transportation Security Administration (TSA) used its most recent newsletter to tell employees not to throw away outdated materials stamped as "Sensitive Security Information" (SSI).
"There have been recent news stories about a young person who went Dumpster diving near a major airport and found an airport binder that contained documents marked as [SSI]", the newsletter said.
Employees are told to shred SSI documents in cross-cutting shredders, cut them manually into squares that measure no less than a half-inch or place them in trash bins specifically designated for SSI disposal.
More
here.
Off Topic: State Farm Accused of Katrina Racketeering

An AP newswire article, via MSNBC, reports that:
State Farm Fire & Casualty Co. engaged in a "pattern of racketeering" by manipulating engineering reports on Hurricane Katrina damage so the company could deny policyholder claims, lawyers for a group of Mississippi homeowners allege in a lawsuit filed Wednesday.
The federal suit against State Farm represents a new legal strategy for attorney Richard "Dickie" Scruggs, who has played a prominent role in challenging the insurance industry for its handling of Katrina claims.
Hundreds of homeowners in Mississippi and Louisiana have sued their insurers for denying their claims after the Aug. 29, 2005, storm. The suits typically accuse insurers of bad faith and breach of contract for refusing to pay for damage from Katrina's storm surge.
More
here.
Image source: Steve Helber / AP file / MSNBC
How Easy is it to Cross the U.S.-Mexico Border? Very.
 An NBC News hidden camera investigation shows just how easy it is to get fake documents to enter the U.S. from Mexico.Image source: NBC News
An NBC News hidden camera investigation shows just how easy it is to get fake documents to enter the U.S. from Mexico.Image source: NBC NewsLisa Myers & the NBC News Investigative Unit
report on
MSNBC.com:
We're on the streets of Juarez, a few feet from the bridge leading across the U.S. border. NBC News producers with hidden cameras came here this week to see how easy it is to get fraudulent documents to enter the U.S.
The first offer came within 15 minutes. A man offered U.S. residency and Social Security cards for $1,000.
For about $500, we could rent what is known as a lookalike document — a real "green card" — with a photo of someone resembling our undercover producer. Because the document is authentic, it will pass inspection unless a customs officer notices the photo doesn't match the person.
More
here.
EU, U.S. Reach Preliminary Deal on SWIFT Data
Ingrid Melander writes for Reuters:
The EU and the United States have reached a preliminary deal on how U.S. authorities can consult data from the international banking network SWIFT in anti-terror investigations, an EU spokesman said on Wednesday.
"We have a draft agreement," Friso Roscam Abbing, spokesman for EU Justice and Security Commissioner Franco Frattini said of an accord aimed at allaying European data privacy concerns.
Roscam Abbing did not give details but said the deal included provisions on data protection. "Then it is for SWIFT and for the banks to do their share in informing in advance their customers about providing the data," he said.
U.S. officials could not confirm if a preliminary deal had been reached. One said: "The process for reaching a final deal is still ongoing."
More
here.
nic.at Domains Blacklisted by Spamhaus for Phishing
David Goldstein writes on DomainNews.com:
nic.at is currently advising registrars of a problem with the nic.at mailserver currently listed on a spam blacklist of Spamhaus.
Previously Spamhaus.org complained about 15 .at domains to nic.at noting they have been used for phishing. nic.at informed spamhaus.org of the legal and technical issues involved, however Spamhaus still insists on the immediate deletion of the domains based on the indication of phishing.
nic.at cannot - according to the registry terms and conditions and Austrian jurisdiction - comply with this demand. Subsequently Spamhaus has listed nic.at without further ado on their email spam blacklist.
In their notice to registrars, nic.at makes it clear they in no way support spamming or phishing. Due to the legal situation they note their options are very limited, mainly because the contract is with the domain owner themselves.
More
here.
U.S. Faces Growing Pressure Over Online Gambling
An AP newswire article, via The International Herald Tribune, reports that:
The United States should face commercial sanctions worth more than $3.4 billion each year for its failure to comply with a World Trade Organization ruling that its Internet gambling restrictions are illegal, the Caribbean nation of Antigua and Barbuda said Wednesday.
Japan and India, meanwhile, added extra pressure on the United States by filing WTO compensation requests as a result of Washington's attempt to change the details of its obligations under the 1994 General Agreement on Trade in Services.
The two Asian countries and the European Union, which filed a similar request Tuesday, complain that the unprecedented legal move by the United States of deleting part of an agreed-upon treaty has to be accompanied by a commitment to open up other trade sectors.
More
here.
Science, Censored
Sharon Begley writes on Newsweek.com:
Of course the press whines when government scientists won’t talk to reporters. Now the government itself—well, at least the congressional branch—has noticed the same problem. The U.S. Government Accountability Office (GAO) has released a report [.pdf] concluding that three federal agencies that conduct scientific research, including NASA and the National Oceanic and Atmospheric Administration, the latter of which is the home of much of the nation’s climate research, do a darn good job of preventing government scientists from telling the public what they’ve discovered.
The GAO, the investigative arm of Congress, surveyed 1,811 randomly-selected researchers at three agencies. It found that 102 at NASA and 76 at NOAA have been barred from publicizing their research results. (This did not include those who were shut down for valid reasons, such as that the study did not pass technical muster.)
More
here.
U.S. Spy Agencies IT Spending Up to $16B
Via UPI.
Overall federal spending on information technology is flat or falling, but U.S. intelligence agencies' purchases will rise more than 8 percent a year to 2012.
INPUT, a research group that analyzes government contract markets, issued its annual forecast of federal IT spending over the next five years on Wednesday.
INPUT said spending by U.S. intelligence agencies is expected to increase from $11.1 billion in 2007 to $16.6 billion by 2012 -- a compound annual growth rate of 8.4 percent.
The growing numbers of intelligence professionals in the IT field and the agencies' expanding role in the U.S.-led war on terrorism are driving "substantial" IT spending, the group said in a statement.
More
here.
YouTube 'Riddled with 40+ Security Vulnerabilities'
Web 2.0 turns into "Web Uh-Oh".
Dan Goodin writes on The Register:
Google researchers have at last responded to a hacker who says he's uncovered more than 40 YouTube flaws that put users at risk.
Christian Matthies, says he's been trying to get the attention of Google bug squashers for the past several months, but was unsuccessful in getting a single reply to his emails warning of the vulnerabilities. That changed this week, a few days after he posted an ultimatum effectively vowing to disclose the bugs publicly if Google didn't give him some acknowledgment of the problems.
The vast majority of the vulnerabilities are of the cross site scripting (XSS) variety, in which hackers are able to inject unauthorized code by making it appear as if it's hosted by the website being targeted. Many of the flaws make it possible for an attacker to infect a user's profile with a quick-spreading worm that could also steal login credentials. In recent weeks, both Google and Yahoo! have been tripped up by serious XSS errors that put the privacy of millions of their users at risk.
More
here.
Hackers Hit London Stock Exchange Website Alert Service
Richard Fletcher writes on The Telegraph.co.uk:
The London Stock Exchange is investigating a suspected attack on its website by hackers that has disrupted an alerts service used by more than 14,000 private investors.
The attackers set up hundreds of thousands of erroneous alerts, overloading the LSE website and disrupting the service for legitimate users.
The attack has left the service - which alerts investors when a company in its portfolio makes a stock exchange announcement or when a share price moves outside set parameters - paralysed for almost 48 hours.
More
here.
(
Props, DJ Technocrat.)
Trojans Lurking In Fake Video Postings On YouTube
Sharon Gaudin writes on InformationWeek:
Malware authors have a new trick up their sleeves that targets the YouTube nation.
Within the past week, cybercriminals have hidden Trojan horses in fake video postings on the wildly popular YouTube site, according to Paul Henry, vice president of technologies with Secure Computing. While YouTube techies were quick to pull down both postings, Henry said in an interview Wednesday that the two incidents could sound the bell for a new means of attack.
More
here.
Romanian Immigrant Indicted for Phishing in Minneapolis
Dan Browning writes on The StarTribune.com:
A Romanian immigrant has been indicted in federal court in Minneapolis on charges that he operated a computerized "phishing" scheme for several years that raked in financial records and personal identification from thousands of individuals, including many from Minnesota.
Sergiu Daniel Popa, 20, of Shelby Township, Michigan, was indicted Tuesday on three counts of possessing 15 or more devices designed to access data on the Internet without authorization, and three counts of aggravated identity theft.
Popa had email addresses for more than 10,000 individuals, and investigators found evidence that he planned to solicit them to visit fraudulent web sites, where they might be tricked into leaving personal information, according to a sworn statement by Theodore Theisen, a special agent with the Federal Bureau of Investigations who works on the Minnesota Cybercrimes Task Force in Minneapolis.
More
here.
Forget Porn And Gambling, Everyday Searches Can Be Dangerous
Sharon Gaudin writes on InformationWeek:
Users may be wary about malware embedded in gambling and porn sites, but one researcher is warning that simple, benign searches could land them in heaps of trouble.
Roger Thompson, a security researcher at Exploit Prevention Labs, reported that users doing online searches can easily stumble upon malicious Web sites -- normally legitimate sites that hackers have broken into to embed malicious code. Thompson is posting the problematic search terms on his blog.
"Mostly we do it because we find it fascinating to see what innocent things can get you into trouble," said Thompson in an e-mail to InformationWeek. "However, it is important for everyone to understand that you can get into trouble without visiting obviously dangerous Web sites. Lots of people think that because they don't surf to places like adult Web sites, they are perfectly safe, and that is not the case."
More
here.
New Hampshire Identifies 153 MySpace Users as Sex Offenders
Via KEYETV.com.
New Hampshire Attorney General Kelly Ayotte says 153 registered sex offenders in the state have been identified as establishing profiles on the Internet site MySpace.
Nationally, MySpace has indicated that more than 7,000 registered sex offenders have been identified as having had established profiles on the site. Each of the identified profiles has been removed by MySpace.
Ayotte's office had subpoenaed the subscriber registration information from MySpace. It's one of six states that pursed the information. It has provided the New Hampshire names to the Department of Corrections.
More
here.
(
Props, Flying Hamster.)
National Security Risks Prompt French BlackBerry Ban
Peter Sayer writes on InfoWorld:
French government members and their advisors have been told not to use BlackBerry smartphones, for national security reasons. The ban on BlackBerry devices is just one of the IT challenges facing new National Assembly members as they take their seats following Sunday's elections.
The smartphones, developed by Canadian company Research in Motion, send and receive e-mail through just a handful of servers in the United Kingdom and in North America -- a reality brought home when a failed software upgrade to the North American servers in April abruptly halted service to BlackBerry users there.
This concentration of data poses a threat to national security, according to Alain Juillet, senior economic intelligence advisor to the French Prime Minister, because of the risk of data interception.
More
here.
Thieves Steal Herman Munster's Identity
 Fred Gwynne, in character as Herman Munster, in the 1960's TV sitcom "The Munsters."
Fred Gwynne, in character as Herman Munster, in the 1960's TV sitcom "The Munsters."An AP newswire
article by Ted Bridis, via
PhysOrg.com, reports that:
Did Internet thieves steal Herman Munster's MasterCard number? Crooks in an underground chat room for selling stolen credit card numbers and personal consumer information offered pilfered data purportedly about Herman Munster, the 1960s Frankenstein-like character from "The Munsters" TV sitcom.
The thieves apparently didn't realize Munster was a fictional TV character and dutifully offered to sell Munster's personal details — accurately listing his home address from the television series as 1313 Mocking Bird Lane — and what appeared to be his MasterCard number. Munster's birth date was listed as Aug. 15, 1964, suspiciously close to the TV series' original air date in September 1964.
CardCops Inc., the Malibu, Calif., Internet security company that quietly recorded details of the illicit but wayward transaction, surmised that a Munsters fan knowledgeable about the show deliberately provided the bogus data.
More
here.
DHS Acknowledges Its Own Computer Break-Ins
An AP newswire article by Ted Bridis, via The Guardian Unlimited, reports that:
The Homeland Security Department, the lead U.S. agency for fighting cyber threats, suffered more than 800 hacker break-ins, virus outbreaks and other computer security problems over two years, senior officials acknowledged to Congress.
In one instance, hacker tools for stealing passwords and other files were found on two internal Homeland Security computer systems. The agency's headquarters sought forensic help from the department's own Security Operations Center and the U.S. Computer Emergency Readiness Team it operates with Carnegie Mellon University.
In other cases, computer workstations in the Coast Guard and the Transportation Security Administration were infected with malicious software detected trying to communicate with outsiders; laptops were discovered missing; and agency Web sites suffered break-ins.
The chairman of the House Homeland Security Committee, Rep. Bennie Thompson, D-Miss., said such problems undermine the government's efforts to encourage companies and private organizations to improve cyber security.
More
here.
FBI Investigate Online 'Hitman' Scams
Dan Lothian writes on CNN.com:
Peter McGlothin didn't know what to think when he first got the e-mail with a bounty on his head.
"[It] is a pity that this is how your life is going to end," the e-mail said.
The e-mailer, describing himself as a hitman, said one of McGlothin's "friends" put out a contract on his life and that people were monitoring his movements.
But the e-mailer offered to cut him a deal: Cough up $30,000 and McGlothin would be left alone. Ignoring the e-mail's threat to "not contact police," McGlothin went to the FBI.
Authorities say McGlothin is not alone. The FBI has received more than 100 complaints about the so-called "hitman scam" from across the country. Typically, the cyber shakedown seeks anywhere from $30,000 to $80,000.
More
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Tuesday, June 19, 2007, at least 3,528 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,897 died as a result of hostile action, according to the military's numbers.
The AP count is one fewer than the Defense Department's tally, last updated Tuesday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
California: Raising Privacy Alarm Over RFID
Edwin Garcia writes in The Mercury News:
Attempting to prevent a potential clash between privacy rights and the latest technological advances, a Palo Alto lawmaker is trying to dissuade the state government, schools and private businesses from tracking people through the use of radio frequency identification devices such as electronic cards and implanted devices.
A legislative package of four measures by Sen. Joe Simitian, D-Palo Alto, will be introduced in an Assembly committee today that would prohibit an employer from implanting tiny ID chips in workers, block RFID technology from being embedded in driver's licenses, prohibit schools from issuing ID cards to track student attendance and make it a misdemeanor to skim identification cards - a method by which identity thieves secretly read the cards of unsuspecting people and clone new versions.
His measures, vociferously opposed by the tech industry, were prompted in part by the increasing availability of wireless equipment sold in stores and cyberspace that can read employee badges - even if they are in someone's pocket or purse 20 feet away - and create a new card using that individual's personal information.
More
here.
Terror Web 2.0
Jeffrey Carr writes on ThreatsWatch.org:
The latest phase of the Internet revolution, which has been widely referred to as Web 2.0, has not been overlooked by web-based terror networks.
A recent study by the Artificial Intelligence Lab of the University of Arizona details precisely how these net-savvy terrorists are using the Web for fund-raising, recruitment, propaganda, logistical support, communications, training, and even cyber warfare.
More
here.
Gapingvoid: Failure is Not an Option
Via gapingvoid.com. Enjoy!
EFF Urges Court to Protect Privacy at Border Crossings
Via The EFF.
The government should not search travelers' computers at border crossings without suspicion, said the Electronic Frontier Foundation (EFF) and the Association of Corporate Travel Executives (ACTE) in an amicus brief filed today in the 9th U.S. Circuit Court of Appeals.
Over the past several years, U.S. customs agents have been searching and even seizing travelers' laptops when they are entering or leaving the country if the traveler fits a profile, appears to be on a government watch list, or is chosen for a random inspection. The Supreme Court has ruled that customs and border agents may perform "routine" searches at the border without a warrant or even reasonable suspicion, but EFF and ACTE argue that inspections of computers are far more invasive than flipping through a briefcase.
More
here.
FTC Looks for More Victims of ChoicePoint Breach
Grant Gross writes on InfoWorld:
The U.S. Federal Trade Commission (FTC) is looking for victims of a data breach at ChoicePoint announced in early 2005.
Victims with out-of-pocket expenses due to the breach have until Aug. 18 to file claims and be eligible for payments from a $5 million fund that ChoicePoint agreed to pay in its January 2006 settlement with the FTC.
The FTC has now mailed reimbursement claim forms to 2,400 consumers who may have been victims of identity theft due to the breach, the agency said in a speech. The FTC has mailed claim forms to 1,000 consumers since December 2006, it said.
In addition, the FTC has created a Web site where consumers who do not receive a claim letter can download a claim form and get more information about the claims process.
More
here.
Google to Build $600M Data Center in Western Iowa
An AP newswire article, via The Mercury News, reports that:
Google Inc. will build a $600 million data center in western Iowa, Gov. Chet Culver announced Tuesday.
The online search leader has already begun construction on a 55-acre site in Council Bluffs, across the Missouri River from Omaha, Neb. The center is expected to create about 200 jobs with an average salary of about $50,000.
More
here.
U.S. Congress to Grill Homeland Security on Cyber Weaknesses - UPDATE
Anne Broache writes on the C|Net News Blog:
A congressional panel that has been none too pleased about various federal agencies' responses to cyber threats plans on Wednesday to put the Department of Homeland Security's chief information officer in the hot seat.
The title of the latest House of Representatives Homeland Security Committee hearing--"Hacking the Homeland: Investigating Cybersecurity Vulnerabilities at the Department of Homeland Security"--suggests another bruising may be on the horizon for CIO Scott Charbo and the oft-criticized agency chiefly responsible for overseeing the nation's cybersecurity efforts.
The event follows an April hearing that focused primarily on cyberattacks involving computers at the State and Commerce Departments.
More
here.
UPDATE: 15:59 PDT: Brian Krebs has a very good overview on this topic, as well,
here on
Security Fix.
Tech Security Companies Are Hot Targets
An AP newswire article by Brian Bergstein, via PhysOrg.com, reports that:
Companies that specialize in computer security are being snapped up at a furious rate. The latest one is SPI Dynamics Inc., a privately held company based in Atlanta that Hewlett-Packard Co. said Tuesday it had bought for an undisclosed amount.
SPI's software scans Web sites and internal corporate programs for potential security holes. SPI's customers include the federal government and financial companies.
The deal comes two weeks after HP's biggest rival, IBM Corp., acquired Watchfire Corp. for more than $100 million. Watchfire is the top player in computer application security, while SPI is No. 2, Forrester Research analyst Chenxi Wang said.
More
here.
Breach at Los Alamos Labs May Have Exposed Classified Data on Nukes
Jaikumar Vijayan writes on ComputerWorld:
Several officials at the company that manages security at the Los Alamos National Laboratory (LANL) used unprotected e-mail networks earlier this year to share highly classified information related to the characteristics of materials used in nuclear weapons.
The incident occurred on Jan. 19 and was considered so serious that a U.S. Department of Energy official was notified of it in the midst of a White House event.
Now, Rep. John Dingell (D-Mich.), chairman of the House Committee on Energy and Commerce, wants to know why a subcommittee investigating an October 2006 security breach at LANL was not told about the January compromise.
Dingell last week wrote a letter to U.S. Department of Energy Secretary Samuel Bodman expressing concern over the failure of the National Nuclear Security Administration to notify the subcommittee of the breach. The NNSA is a semiautonomous body within the DOE that's responsible for supervising the country's nuclear facilities.
More
here.
Australia: Westpac Hit by DoS Attacks
Brett Winterford writes on ZDNet Australia:
Westpac is considering additional security measures for its online banking system after a spate of security and availability dramas, including denial of service (DoS) attacks.
Just days after human error caused the bank's ATM, EFTPOS and online banking networks to fail, the bank has confirmed that its online banking system was crippled by a DoS attack.
The attack, on Thursday 7 June, caused the bank's online service to be shut down for three hours between 8pm and 11pm.
According to Westpac insiders, the problem was initially passed off as a hardware failure.
Three hours later it was discovered to be a Denial of Service attack -- caused by flooding of one of the open ports on an incoming router that carries Internet traffic.
More
here.
Westpac describes itself as
"...Australia's First Bank with a range of innovative financial packages to suit your needs."
SWIFT Must Defend Itself Against Violation of Privacy Accusations
A Bloomberg newswire article by Andrew Harris, via The International Herald Tribune, reports that:
Swift, the banking cooperative based in Belgium that has aided U.S. government efforts to trace terrorist financing, must defend a lawsuit accusing it of violating the privacy rights of U.S. citizens, a judge has ruled.
Swift, the Society for Worldwide Interbank Financial Telecommunications, is an industry-owned group that enables more than 8,000 banks and financial institutions in more than 200 countries to trade information and process transactions, according to the group's Web site.
Judge James Holderman of the U.S. District Court in Chicago said that the complaint brought by two bank customers contained sufficient allegations to support a claim that Swift had violated the U.S. Right to Financial Privacy Act, a law limiting the right of the government to view bank customers' records.
"The Swift program is another example of reckless disregard for the Constitution and values that make us who we are as a nation," Steven Schwarz, a lawyer for one of the plaintiffs, said Friday.
More
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Monday, June 18, 2007, at least 3,527 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 2,888 died as a result of hostile action, according to the military's numbers.
The AP count is 10 higher than the Defense Department's tally, last updated Monday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Appeals Court Says Feds Need Warrants to Search E-Mail
Luke O'Brien writes on Threat Level:
A federal appeals court on Monday ruled that e-mail users have privacy rights that prohibit federal agencies from conducting warrantless searches of electronic correspondence during investigations, a practice that has been allowed for 20 years.
The ruling by the Sixth U.S. Circuit Court of Appeals in Ohio upholds a lower court ruling that placed a temporary injunction on e-mail searches in a fraud investigation against Steven Warshak, who runs a supplements company best known for a male enhancement product called Enzyte. Warshak hawks Enzyte using "Smiling Bob" ads that have gained some notoriety.
The case boiled down to a Fourth Amendment argument, in which Warshak contended that the government overstepped its constitutional reach when it searched and seized e-mail records from his internet service providers. Under the federal Stored Communications Act (SCA), the government has regularly obtained e-mail from third parties without the right court orders.
More
here.
NBC Wants More ISPs to Spy on Users, Reform Safe Harbor
Ken Fisher writes on ARS Technica:
Last week NBC/Universal general counsel Rick Cotton argued that law enforcement resources are "misaligned." Cotton says it's wrong to focus on real property theft and potentially deadly crimes when cops could be out enforcing intellectual property laws.
Cotton wasn't finished. He filed a response on behalf of NBC Universal to the FCC's call for comments last week on the broadband industry and Net Neutrality which says, in effect, that Net Neutrality is a waste of time. The FCC should be focusing on... you guessed it, piracy!
More
here.
IT Managers Say Risk Of Data Loss Is Bad And Getting Worse
Sharon Gaudin writes in InformationWeek:
Nearly half of IT and compliance professionals said in a recent survey that their organizations are doing an inadequate job of lowering the rate of data loss
The survey of more than 1,000 IT and compliance practitioners also showed that 45% said that if they were hit by a data breach, they don't believe they would be able to notify users and customers, according to researchers at the Ponemon Institute LLC. The same IT managers added that their companies lack the necessary security tools or internal controls to prevent, detect, and correct data security breaches. The study was commissioned by Oracle.
The findings have "disturbing implications" for any company dealing with information stores, according to the study. "It suggests that the IT and compliance practitioners who are required to deal with IT security and privacy issues see the potential for catastrophic data loss," researchers reported. "They also believe that their organizations are grossly inadequate in curbing this potential risk."
More
here.
Computer Cookies and How They Crumble
Alex Mindlin writes in The New York Times:
Tiny files called “cookies” are the lifeblood of online advertising. When a computer visits a site or sees an ad for the first time, the site’s server slips a cookie onto the visitor’s hard drive, identifying the computer in future dealings with that site or ad network. Cookies let online hosts determine the number of unique visitors they reach, a key metric for advertisers.
But this system of measurement has a well-known flaw: users are prone to delete their cookies, either manually or by using antispyware programs. Users who delete a cookie are eventually given a new one by that cookie’s issuer, meaning that they are often counted as unique visitors, inflating the numbers at host sites.
More
here.
DARPA Watch: LANdroid WiFi Robots

Via Technovelgy.com.
LANdroid WiFi robots are the latest items from DARPA's technology wish-list. DARPA is soliciting proposals for intelligent autonomous radio relay nodes that are able to establish mesh networks in urban settings.
Ideally, a LANdroid unit would consist of a robotic platform - small, inexpensive, smart, and mobile (as shown in the photoshop artist's conception above). Warfighters would carry lots of them (they should be roughly palm-size) and then drop them as they go.
More
here.
Experts Debate Microsoft Patch Priorities
Gregg Keizer writes on ComputerWorld:
As Microsoft Corp. last week issued patches for 15 vulnerabilities in its operating systems, browser and applications, security experts debated which flaw should be fixed first.
The June updates fixed multiple bugs in Windows, Internet Explorer, Office, Outlook Express and Windows Mail. Of the 15 flaws, nine were labeled “critical,” Microsoft’s most serious ranking. The vendor characterized two as “important” and two others as “moderate.”
Security experts disagreed over which of the June flaws should be fixed first.
More
here.
Police Smash Global Web Paedophile Ring
Via The Guardian Unlimited (UK).
Police have smashed a global internet paedophile ring with more than 700 suspects worldwide, a British law enforcement agency said today.
The Child Exploitation and Online Protection (Ceop) centre said about 200 of the suspects are based in the UK, and 31 children have been rescued from abuse.
The paedophiles used an internet chatroom called Kids the Light of Our Lives to swap photos and videos of children being subjected to horrific sexual abuse.
The past 10 months of the huge police investigation has involved agencies from 35 countries around the world.
More
here.
Crippling Malware Attack Strikes in Italy
Shaun Nichols writes on vnunet.com:
Italy is suffering from a barrage of remote attacks launched from hundreds of compromised websites, security experts have warned.
Researchers at Symantec reported that attackers have injected 'iframe' tags within the HTML files on compromised sites.
The tags redirect users to a site that runs MPack, a utility that attempts multiple exploits and malware installations.
More than 65,000 users had been redirected to the malicious page since Friday afternoon, and more than 7,000 successful exploits had been carried out.
More
here.
Nuclear Explosion on Czech Morning Television - UPDATE
Via heise Security News.
The site of the Krkonose Mountains in Bohemia disappearing in a nuclear explosion yesterday (Sunday) morning, may have had some viewers of Czech public television channel CT2's breakfast show choking on their cornflakes. Happily, this turned out to be a stunt by a group of artists known as Ztohoven. They broke via the internet into a camera / camera server which provided images from the Krkonose Mountains as part of the morning panorama program. Skiers will be familiar with similar TV content - alternating images of camera pans from skiing areas accompanied by snow reports and temperatures.
According to media reports, Ztohoven fed a 30 second film which showed images of an atomic explosion and the group's web address. According to initial investigations by the Czech authorities, the CT2 network itself was not affected, the compromised camera server was operated by an outside contractor.
More
here.
UPDATE: 06:38 PDT: Cory has a snippet over on
Boing Boing, along with a link to a YouTube segment with the video. Sweet.
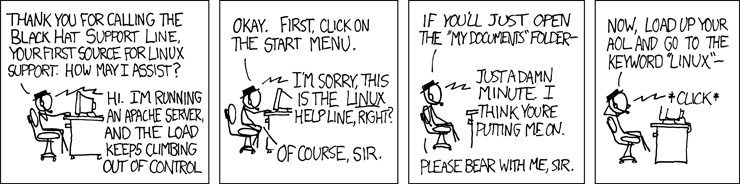
Black Hat Tech Support
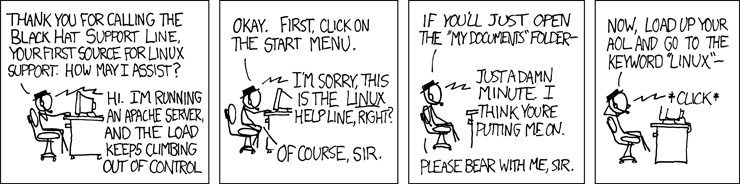 Click for larger image.
Click for larger image.
We love
xkcd.
Rocket Carrying U.S. Spy Satellites Suffers Glitch
An AP newswire article, via Space.com, reports that:
A rocket carrying an intelligence-gathering payload for the Pentagon suffered a technical problem after its launch, officials said. But they were confident Saturday that its secretive mission would be performed.
The Atlas V rocket launched Friday morning, hauling a payload from the National Reconnaissance Office, a division of the Department of Defense that builds and operates spy satellites.
The NRO said Friday night that the launch was successful, but the rocket's Centaur upper stage later had a "technical anomaly which resulted in minor performance degradation.''
Rick Oborn, an NRO spokesman, said Saturday there was a slight but manageable problem. Officials did not elaborate and have not said exactly what the rocket was carrying or how it would be used.
More
here.
The Frisbee Turns 50

An AP newswire article, via CBS5.com, reports that:
Wham-O Inc. changed the name of the Pluto Platter to Frisbee 50 years ago Sunday, flinging a new word into the cultural ether that still conjures images of carefree fun in the park and breezy days at the beach.
And to think Walter "Fred" Morrison, the inventor of the beloved disc, thought the new moniker would never fly.
"I thought Frisbee was a terrible name," Morrison, now 87, said. "I thought it was insane."
Frisbee instead became insanely popular, making the name as synonymous with flying discs as Google is with searching the Internet and Kleenex is with tissue.
More
here.