‘Nigerian scams’ keep evolving
Bob Sullivan writes for MSNBC:
The most familiar Nigerian scam is an e-mail offering lots of free money in exchange for helping someone with a name like Barrister Richard Okoya. The offer varies, but the theme is the same — help a downtrodden victim recover a large sum of money trapped in an overseas bank, and you will be rewarded handsomely.
For most, the e-mails are the butt of jokes and evoke a "Who would ever fall for that?" reaction.
You'd be surprised, says Dale Miskall, supervisory special agent in charge of an FBI cybercrime squad in Birmingham, Ala. He's been working Nigerian scams for the Internet Fraud Complaint Center for years; in January, he went to Nigeria to testify against suspects after a rare arrest.
Hackers Monkey With Korean Mozilla Site
Tim Gray writes on internetnews.com:
The Korean language Mozilla Web site was hacked and defaced this week, prompting calls from some corners of the open source community to gain control of the independent site.
The job was likely the work of the notorious Simiens Crew, a Brazil-based outfit, and while the main page was not affected, other pages were replaced by the message "Simiens Crew ownz u viva os macacos."
Not all agree on 'overhyped' security threats
Grant Gross writes for NetworkWorld:
Two Gartner analysts released their list of the five most overhyped IT security threats, with IP telephony and malware for mobile devices making the list, but not all IT security vendors agreed with the analysts' assessment.
Lawrence Orans, principal analyst at Gartner, and John Pescatore, vice president and Gartner fellow, noted that while attacks on IP telephony and mobile devices may come eventually, current warnings about security problems are ahead of actual attacks.
Not everyone agreed with Gartner's assessment, however. Companies deploying IP telephony or voice-over-IP services do need to pay attention to security, and users of IP telephony need to protect not only the end-device phones and IP servers, but also signaling and other voice equipment, said Stan Quintana, vice president of managed security services for AT&T. "It's a slightly different, more complex equation than data networks," he said.
Two computers stolen with Motorola staff data
Yet another disclosure of personal data that has been lost, stolen, or obtained by unauthorized means...
Wei Gu and Sinead Carew write for Reuters:
Two computers containing personal information on Motorola Inc. employees were stolen from the mobile phone maker's human resources services provider, Affiliated Computer Services, the latest in a series of incidents of companies losing control of employee data.
The data on the stolen computers included names and Social Security numbers but no financial information, according to Motorola. The number of employees affected was not disclosed.
Award Claim Sparks Firefox, Opera Clash
David Worthington writes in BetaNews:
The watchful eye of bloggers has once again stirred controversy. A press release issued by Opera Software claimed that Opera 8 won PC World's 2005 World Class Award for best Web browser only to be harshly refuted by the Mozilla Foundation's Asa Dotzler who is recognized as the Firefox and Thunderbird product manager.
The press release, which has since been corrected, prompted Dotzler to say with an acid pen, "Opera is simply lying. They were one of 100 products to be labeled as "World Class" but they did not win any "best Web browser" anything. They were last in the ranking of three web browsers. They got beat by both Maxthon and Firefox."
Accused UT hacker apologizes for taking personal information
Local news for us here in Austin...
Steven Kreytak writes today in the Austin American Statesman (registration required):
Christopher Phillips testified in federal court this morning that he is not an identity thief and that he was only practicing computer programming when he harvested thousands of Social Security numbers from University of Texas computers in 2002 and 2003.
Federal prosecutors say Phillips, a former UT student, is a criminal who violated both university policy and federal law by harvesting the numbers and corresponding names. They charge that he intended to use them to defraud, a crime punishable by up to 10 years in prison.
The names and Social Security numbers belonged to UT students, faculty, donors and others included in school database.
In more than an hour of testimony under direct questioning, Phillips, 22, admitted in a quiet, cracking voice that he knew it was wrong to gather the personal information but he didn't plan to profit from the information. He said he wanted only to practice writing programs to extract data and merge databases, he said.
Then Phillips, whose lawyer describes him as a harmless computer geek, told the 12-person jury that he was sorry.
RSS To Carry Spyware Before Year's Out
Gregg Keizer writes in TechWeb News:
By the end of the year, spyware programs will have tripled in number, put Firefox in their sights, and have turned to RSS to distribute its key loggers and ad spawners, a security expert said Friday.
Richard Stiennon, director of threat research at anti-spyware software vendor Webroot, first presented his six predictions at this week's Gartner IT Security Summit.
Number one on his list?
"The first spyware that targets Firefox will appear in the first half of 2005," prognosticated Stiennon. "That means either a spyware writer will take advantage of a vulnerability in Firefox, as others already have in Internet Explorer, or create a site that forces Firefox to invisibly download and install adware or spyware."
Yahoo! looking for Voice Services?
Hmmm. Today brings us several rumors of the possibility that Yahoo! is looking to expand it's service portfolio, perhaps even to the extent of acquiring Skype.
Also, Justin Hyde writes for Reuters:
Internet services company Yahoo Inc. is looking to boost its business in the Internet's next big growth area -- voice communications.
The largest U.S. provider of Web e-mail services, Yahoo already has deals with several landline and wireless telephone companies, including SBC Communications, Verizon Communications Inc., and Sprint Corp., for a variety of Web-based services.
In addition to voice services, Yahoo is also expanding the reach of its e-mail service, saying earlier this week it would allow Sprint wireless customers to manage their e-mail accounts through their cell phones. Last month, Yahoo announced an upgrade of its messenger service, boosting the ability to make free voice calls between computers.
Google backs street-imaging project
Will Knight writes for NewScientist:
Having mapped the farthest corners of the internet, search-engine giant Google appears to be turning its attention to the “real world”, funding a project to scan the streets of San Francisco.
Researchers behind Stanford University’s CityBlock Project have developed a technique for creating realistic and panoramic street-level images using a combination of vehicle-mounted laser range-finding equipment and video cameras.
"We have been building technology for digitising commercial city blocks from sideways-looking video taken from a vehicle driving down the street," writes Stanford researcher Marc Levoy on the project's homepage. "Possible applications include in-car navigation, online route visualisation, and web-based tourism."
Google declined requests to comment on the project, but some experts see it as a natural extension of the company's existing services.
Spam sign-up man convicted of harassment
John Leyden writes in The Register:
A US man who signed his boss up to various spam lists has been convicted of harassment. Scott Huffines, 41, from Essex County near Baltimore, Maryland, was sentenced to probation and 100 hours community service this week after pleading guilty to misuse of electronic mail, the Baltimore Sun reports.
The Web designer signed Alex Vitalo, his female supervisor at Maryland Public Television, up to dating services and job sites. But the revenge ploy backfired when his victim forced an investigation that traced the sign up messages back to Huffines. The case is reckoned to be the first of its kind considered by US courts.
Nortel president resigns after falling out with CEO
Wow, that didn't last very long.
Gary Daichendt and Gary Kunis both used to be at Cisco, and being a former Cisco flunky myself, I found this story especially revealing. I won't say exactly why, though. ;-)
Peter Sayer (IDG News Service) writes in NetworkWorld:
Gary Daichendt Friday resigned as president and COO of Nortel , after falling out with CEO Bill Owens.
CTO Gary Kunis was caught in the crossfire and will also leave the company. Kunis had worked with Daichendt during their time at Cisco.
Bell South Intros Super High-Speed DSL
Matthew Friedman writes in Networking Pipeline:
Bell South's 2.3 million digital subscriber line (DSL) customers will be able to surf the Internet at even higher speeds when the carrier launches its BellSouth FastAccess DSL Xtreme 6.0 service.
Announced yesterday, the FastAccess DSL Xtreme 6.0 service will provide users with 6 MB connections to support demanding next-generation network applications. Business users will be able to benefit from the same kind of big data pipe for shared access and other applications with FastAccess Business DSL 6.0.
Foundry Networks Unveils All-Fiber Metro Ethernet Switch
Matthew Friedman writes in Networking Pipeline:
Foundry Networks Inc. has unveiled a new, all-fiber optic layer 2/3 edge switch designed to allow service providers and carriers to easily deploy Ethernet to the home and Ethernet to the business services.
The FastIron Edge X424F switch features 24 hot-pluggable small form factor pluggable ports that can be configured with 100 Mbps and 1000 Mbps transceivers, and up to two 10 Gigabit Ethernet ports. The switch supports a wide ranger of metro Ethernet service deployments, including Gigabit Ethernet over 10 km of single strand single-mode fiber and Gigabit Ethernet over 2 km of dual-strand Fiber Distributed Data Interface grade multimode fiber.
Dutch hacker love-in will get permit
Jan Libbenga writes in The Register:
Dutch hacker love in What the Hack will get a permit after all for this year's bash on a campground near Boxtel in the Netherlands.
The gathering of 3,000 international hackers, between 28 and 31 July, faced the chop a couple of weeks ago, because the local mayor feared "breaches of law and order and danger to public safety". Now the organisers tell hack trekkies: "Ladies and gentlemen, grab your tissues to wipe away the tears of joy!"
Swedish anti-piracy group broke privacy data act
Jan Libbenga writes in The Register:
Swedish anti-piracy group Antipiratbyrån (APB) has been disciplined by the country's Data Inspection Board for breaking privacy data rules in its hunt for illegal file-sharers.
ABP used special software to record the IP-addresses of file swappers, the file name and the server through which the connection was made, Sweden's The Local says. The company, a private organisation, reported hundreds of people to the police recently and has sent up to 2,000 emails a day to internet service providers notifying them of abuse.
Israel espionage case points to new Net threat
This is an ongoing saga, apparently--something I've mentioned here a couple of times, most notably earlier this morning when one of the suspects in the case suffered a severe "fall" that landed him in the hospital in critical condition.
Bob Sullivan writes on MSNBC:
Executives of top telecom firms accused of spying on each other. A jealous ex-husband suspected of monitoring his former in-laws. Private investigators implicated in computer-hacking-for-hire; one now involved in a possible attempted suicide. So much bad publicity, government officials worry it might impact the entire nation’s economy.
At the center of it all--a tiny computer program that’s caused the biggest corporate scandal anyone in Israel can remember.
Skype Expands VoIP Services
A UPI newswire report on Newsfactor Technology News reveals that:
Skype, one of the world's fastest-growing telecommunications companies, has launched two new premium services that will expand its Voice over Internet Protocol capabilities into conventional telephony -- although experts doubt the service will challenge that industry sector.
"SkypeIn and Skype Voicemail enhance the basic free Skype and give friends, family and colleagues not connected to the Internet an inexpensive and convenient way to contact members of our global user base," Niklas Zennstrom, Skype's chief executive officer and cofounder, said in a statement.
Microsoft CEO Warns of Internet Dangers
An AP newswire article by Ted Bridis (via Yahoo! News) reports:
Computer users, beware. The head of the world's largest software company worries that consumers who make Internet purchases have become too complacent about the risks of financial fraud and stolen identity.
Microsoft CEO Steve Ballmer said in an interview with The Associated Press that a calm period without significant Internet attacks has lulled computer users, even older Web surfers who traditionally have been more anxious than teenagers about their online safety.
Amazon.com hit with slowdown
Parija Bhatnagar writes in CNN/Money:
A technical glitch caused online retailer Amazon.com to suffer at least two periods of extended slowdowns Thursday, one during late morning and a second during the peak lunch-time browsing period.
According to Web site monitoring firm AlertSite.com, the first slowdown occurred between 9:30 to 10 a.m. ET, during which time the Web site was available to 82 percent of users.
The situation became worse for a 40-minute period between 1:20 p.m. to 2 p.m. ET, when the site was available to just 25 percent of users, said Ken Godskind, vice president of marketing for AlertSite.com.
"What started out as a small error in the morning is turning into somewhat of a bigger matter," Godskind told CNN/Money. "When your Web site is the face of the entire company, that kind of an error is a big deal." Godskind estimates that the 40-minute slowdown in the afternoon probably affected traffic of about a million impressions to the site.
Patty Smith, spokeswoman for Amazon.com, attributed the slowdown to a "technical problem."
Fake Jacko Suicide Spam Hides Trojan Horse
Sharon Gaudin writes on eSecurityPlanet.com:
A new spam campaign is claiming that Michael Jackson has attempted suicide in an effort to trick users into downloading a Trojan horse.
The message in the spam reads: ''Last night, while in his Neverland Ranch, Michael Jackson has made a suicidal attempt... They suggest this attempt follows the last claim was made against the king of pop. 46 years old Michael has left pre-suicid note which describes and interpretes some of his sins.''
If users click on a link in the email, they are taken to a Web site that secretly downloads malicious code onto their machine, according to analysts from Sophos, Inc., an anti-virus and anti-spam company with U.S. headquarters in Lynnfield, Mass.
Microsoft Plans 10 Patches Next Tuesday
Via TechWeb News.
Next week Microsoft will roll out ten security bulletins, at least one marked "Critical," the Redmond, Wash.-based developer disclosed Thursday.
As is its custom, Microsoft gave advance notice of the number, highest severity, and target of the patches it plans to post Tuesday, June 14. Of the ten bulletins, seven affect Windows, and one each impacts Microsoft Services for UNIX, Microsoft Exchange, and Microsoft Internet Security and Acceleration (ISA) Server and the associated Small Business Server.
Cisco, Alcatel Join New Infranet Group
Craig Matsumoto writes in Light Reading:
As expected, Alcatel and Cisco last night announced they have joined the Infranet effort begun by Juniper Networks, which in turn will begin working under the auspices of an established standards body.
The reborn Infranet Initiative Council (IIC) officially got underway today with an inaugural meeting here that included the election of board members and the selection of a name, which has yet to be determined (IIC2? IICII?). Members characterized the meeting -- still going on at press time -- as the first step toward an ambitious industrywide effort to augment networks with the power to apply quality of service (QOS) and security to every application.
The new group was born yesterday with the announcement that Alcatel and Cisco were joining the Infranet effort, which was launched by Juniper last year. Cisco in particular had steadfastly refused to join the IIC, claiming the industry would be better served by doing this work in the established standards bodies.
Cybertip.ca surprised by flood of responses
A Canadian Press newswire article in the Globe and Mail reveals that:
The people who run Canada's national tipline for child pornography say they're surprised by the number of responses they've received.
Officials at Cybertip.ca said Thursday they took in 1,400 reports between late January and the end of April relating to suspected cases of child porn, or of people using the Internet to lure children.
Child Find Manitoba, the non-profit agency that set up the tipline as a pilot project in the province in 2002, called the numbers startling, and said they are probably just the tip of the iceberg.
Indonesia: $1 amnesty for pirated Microsoft software
Via The BBC.
Microsoft has reached a deal with Indonesia over the tens of thousands of pirated versions of Windows programs used in government departments.
Ministers said Microsoft had agreed an amnesty under which a token sum of one dollar will be paid for every computer found to be using illegal software.
In exchange, the government has promised to buy Microsoft merchandise legally in future.
Indonesia has one of the world's highest rates of pirated programs.
Europe to push ahead with ISP snooping law
Sylvia Carr writes in C|Net News:
Legislation that would require telephone companies and Internet service providers to save information about customers' communications is set to proceed despite being rejected by the European Parliament.
The legislation's draft proposal was introduced jointly by France, Ireland, Sweden and the United Kingdom to aid law enforcement in combating terrorist acts. It will require phone companies and ISPs to retain for 12 to 36 months customer data such as the time, date and location of sent and received e-mails and phone calls. The content of the communications, however, will not be retained.
The European Parliament on Tuesday rejected the proposal, partly on grounds it could be illegal.
Blogger Mojtaba Saminejad gets two-year prison sentence
Via Reporters sans Frontières (Reporters without Borders).
Reporters Without Borders voiced deep concern today about the fate of 25-year-old blogger Mojtaba Saminejad, who has been sentenced to two years in prison by a Tehran revolutionary court for "insulting the Supreme Guide" and who is due to be tried soon on a separate charge of insulting the prophets, which carries a possible death penalty.
The press freedom organisation urged all bloggers to mobilise on behalf of the young blogger, who was arrested on 12 February.
"All blogosphere messages of solidarity are welcome," the organisation said. "We know that these message reach the prisoners and help put pressure on the Iranian authorities, especially in the run-up to the presidential election. It is vital for people to talk about Mojtaba."
Mojtaba's lawyer, Mohammad Saifzadeh, said the two-year sentence was handed down after a hearing on 23 May in which his client was not allowed to speak freely. To intimidate him, the authorities had him accompanied in court by the police officers who interrogated him in prison.
U.S. will compromise on biometric passports
Excerpt from an FT.com article by Edward Alden and Sarah Laitner (via MSNBC):
The U.S. is poised to drop its demand that European nations and other close allies adopt biometric passports by October, a move aimed at avoiding a serious disruption in transatlantic travel, according to U.S. and European government officials.
The U.S. is poised to drop its demand that European nations and other close allies adopt biometric passports by October, a move aimed at avoiding a serious disruption in transatlantic travel, according to U.S. and European government officials.
The likely U.S. action, which comes amid travel industry concerns that overseas visitors are deterred from coming to the US, would be a significant shift in policy. For more than two years Washington has insisted for security reasons that countries whose citizens can enter the U.S. without visas begin issuing biometric documents that ensure the identity of the passport holder.
The plan is the latest in a series of twists since Congress passed legislation in 2002 that required the 27 countries in the so-called visa-waiver program to start issuing the high-tech passports by October of last year. Brussels has said that some European countries in the program will not be able to meet that requirement until August, 2006.
Neustar IPO set at 25 million shares, $18-$20 per share
An Dow Jones/AP article in The Mercury News (registration required) this morning reveals that:
Neustar Inc. on Thursday set the terms of its pending initial public offering at 25 million shares, at an estimated price of $18 to $20 a share.
The company, based in Sterling, Va., provides the North American communications industry with clearinghouse services. It operates the directories that manage virtually all telephone area codes and numbers, and enables the routing of calls among competing communications service providers in the United States and Canada.
According to an amended filing with the Securities and Exchange Commission, Neustar said all of the shares being offered will be sold by selling shareholders.
The largest selling shareholder listed in the filing was Warburg Pincus Equity Partners LP.
The selling shareholders have granted the underwriters an option to purchase up to an additional 3.75 million shares to meet demand.
ACLU to challenge Utah porn-blocking law
Declan McCullagh writes in C|Net News:
Opponents of a Utah law that requires Internet service providers to offer to block Web sites deemed pornographic will file a lawsuit Thursday to overturn the measure.
The American Civil Liberties Union of Utah is seeking an injunction in federal district court in Salt Lake City as part of its lawsuit claiming that the Utah law violates state residents' rights to free expression and unlawfully interferes with interstate commerce.
The controversial legislation requires the attorney general to create an official list of Web sites with material that is deemed "harmful to minors" and that is "not access restricted." Under the law, Internet providers in Utah must provide their customers with a way to disable access to sites on the list or face felony charges.
Astronomers don’t want the in-flight cellphone ban lifted
Peter Rojas posts over on Engadget:
It’s not just flight attendants and federales worried about terrorism who are coming out against lifting the ban on using cellphones on airplanes, now it’s the astronomers who are unhappy (and you so do not want to be on their bad side). Cellphones just happen to leak radiation at an integer that coincides with the molecular signature of newborn and dying stars, and the National Academy of Sciences’ Committee on Radio Frequencies has complained to the FCC that even a single cellphone in the air is enough to seriously interfere with a radio telescope. Except when it’s a cellphone that’s connected to one of those in-plane picocell mini base stations that relays the signal to the ground at a frequency that doesn’t interfere with their telescopes. They don’t mind that.
FCC Speeds Up Digital TV Signal Deadlines
An AP newswire article written by David Pace (via Yahoo! News) reports that:
Federal regulators on Thursday moved up the deadlines for manufacturers to make popular, mid-sized television sets capable of receiving digital signals.
The next-generation technology provides sharper images and more programming options.
The Federal Communications Commission voted 4-0 to require that all medium-sized televisions, those with screens from 25 to 36 inches in diameter, be capable of receiving both digital and traditional analog signals by March 1, four months earlier than the commission had decreed three years ago.
Regulators also retained a requirement that half of all new mid-size televisions must have digital receiving capability by July 1.
The commission also proposed moving the deadline for all small TVs to have digital tuners to the end of 2006, rather than the July 1, 2007, deadline the regulators set in 2002. That proposals will be voted on later after a period of public comment.
T-Mobile Tops Customer-Care Ranking; Sprint Is At The Bottom
Antone Gonsalves writes on TechWeb News:
T-Mobile has the most satisfied subscribers, while Sprint PCS has the worse customer-care ranking among the six major U.S. carriers, J.D. Power and Associates said Wednesday.
In its third-annual customer service study, the market research firm found that two other companies, Verizon Wireless and Nextel ranked above the industry average for customer satisfaction, while Cingular joined Sprint in falling below the mark. AllTel scored the industry average of 100.
Even Taxi Cabs Are Worried About Consumer Data Security
Steven Martin writes in InformationWeek:
Companies responsible for handling consumer financial data are moving quickly to repair the weak links in their information security infrastructure in the wake of high-profile losses and thefts of customer information.
Transaction Network Services Inc., which provides network services to payment processors, this week revealed that it's encrypting personal account and credit-card information sent across its Synapse system, which provides payment services for merchants that use wireless devices, including taxi and limousine companies, towing services, arts and crafts shows, and mobile concession and souvenir stands.
When merchants enter a request for a card authorization, it's transmitted over a wireless network such as Cingular or Verizon to Synapse, which transports the request over a landline to a payment processor. After the transaction is authorized, the approval is sent back via Synapse to the wireless network and on to the merchant.
techdirt.com: BellSouth's Not-New, Not-WiMax Trial Is Also Not-Naked DSL
Mike over at techdirt.com hits the proverbial nail on the head:
Contributed by Mike on Thursday, June 9th, 2005 @ 01:09AM
from the spin-spin-spin-spin dept.
Wow. Does BellSouth ever have a talent for taking something and making it sound like something completely different. Earlier this week, BellSouth got some press for saying they were launching new WiMax trials in Georgia and Florida. There were two problems. The technology isn't WiMax (not even close, actually) and it isn't new (again, not even close). However, the press seemed to buy both claims. So, if they got away with both of those, why not go one step further and claim that these not-WiMax, not-new trials are "naked DSL." You'll recall that "naked DSL" is when a telco offers DSL service without also requiring a phone line. At one point, BellSouth was required to offer naked DSL, but not everyone agreed, and eventually the FCC said that BellSouth was fine not offering naked DSL at all. So, why does BellSouth claim that this not-WiMax is naked DSL (despite, obviously, not being DSL at all)? It's because customers will be able to order this service without also ordering a phone line. Of course, that completely misses the point. The reason customers don't have to order a phone line is because, unlike with real DSL, this wireless broadband technology doesn't require phone wires to go into the house -- so if they actually required phone service with it, it wouldn't actually make sense. Yet, the company still has the gall to claim that this qualifies as them offering naked DSL... and, of course, the gullible News.com reporter eats it up.
New shot fired in Net drug battle
Barrie McKenna writes in the Globe and Mail:
Alberta as South Africa, Quebec as India and Manitoba as Vietnam?
That's the way drug maker GlaxoSmithKline depicts the map of Canada in an edgy new magazine ad aimed at dissuading millions of Americans from ordering cheap drugs from Internet pharmacies.
"Are you buying medicine from north of the border or east of the border?," the company asks in the ad now running in Time and Newsweek, as well as major U.S. daily newspapers.
Glaxo officials said the company is just trying "get out the facts" to U.S. consumers that they may be getting bogus and unregulated drugs when they buy from Internet websites identified as Canadian.
Cybersecurity plagues Fort Hood
Here's a double-dose of déjà vu. I served at Fort Hood in the 1st Cavalry Division for a couple of years in the mid-1980's during my 8 year Army stint, and Ft. Hood is just a few miles up the road from my current home, Austin.
Frank Tiboni writes on FCW.com:
The Army's biggest base has a cybersecurity problem to match its size.
Fort Hood, Texas, the largest Army base in the world and home of the 4th Infantry Division — the service’s first digitized force — has a huge information security problem, said Maj. Gen. Dennis Moran, the Army’s director of information operations, network and space in the Office of the Chief Information Officer. He spoke June 8 at the Army Information Technology Conference sponsored by the Army Small Computer Program.
Some Army IT leaders think the best way to solve the information security problem at Fort Hood is to operate IT as an enterprise. For example, the base has 96 domains on the military’s unclassified network. Consolidating e-mail, servers and storage systems would improve network management, operations and security, Moran said.
Israeli Spyware suspect in hospital after fall
John Leyden writes in The Register:
A key suspect in a spyware-linked industrial espionage case was severely injured after falling down a stairwell on Wednesday during a break in questioning by Israeli police. The Jerusalem Post reports that Yitzhak Rath, 54, boss of the Modi'in Ezrahi private detective agency, was taken for treatment at a Tel Aviv hospital following the incident at Yarkon District police station. He's been treated for "severe head, spinal cord and chest injuries" in Ichilov Hospital's intensive care unit where his condition is described as "stable", Israeli English language daily Haaretz reports.
Police have appointed an officer to investigate whether the incident was a suicide attempt, an accident or something more sinister. Rath's firm is one of several alleged to have helped Israeli firms to spy on rivals using customised spyware or Trojan horse packages designed to evade detection by security tools. He was called in for police questioning on Wednesday following his initial arrest and detention two weeks ago.
Ebbers Tries to Settle Shareholder Lawsuit
Carrie Johnson and Ben White write in The Washington Post:
Convicted former WorldCom Inc. chief executive Bernard J. Ebbers is negotiating to settle a class-action lawsuit filed by investors in the nation's second-biggest telecommunications firm for an undisclosed sum, according to lawyers involved in the case.
Former WorldCom finance chief Scott D. Sullivan and two other officials who pleaded guilty to participating in a widespread accounting fraud at the Ashburn company also are taking part in the settlement talks, lawyers said.
ICANN Board Designates VeriSign to Retain Control of .NET Registry
Via the ICANN website.
Marina del Rey, CA – 8 June 2005 – ICANN’s Board has named VeriSign, Inc. as the designated .NET successor registry. ICANN has also approved entering into a new agreement with VeriSign for their continued management of the .NET registry for six additional years. This announcement is the culmination of the .NET RFP and successor registry process that began on 6 March 2004 and included an independent evaluation of VeriSign and four other applicants.
In taking this action ICANN’s Board considered the entire RFP Process, an independent evaluator’s report, Internet community comments and the terms of the new agreement.
ICANN hired Telcordia Technologies, Inc. (an independent third party) to conduct the evaluation of the applications and the qualifications of the applicants. In April, Telcordia declared that all five applicants were capable of running the registry for .NET but gave the highest ranking to the incumbent registry, VeriSign. In May, Telcordia confirmed this ranking after evaluating an additional round of comments from all five applicants.
VeriSign’s current agreement for .NET is scheduled to run out on 30 June 2005. The agreed framework for ICANN and VeriSign’s new arrangement will be set out in a new .NET Registry agreement which will strike a balance between innovation and business certainty, with the need to ensure competition, security and stability in the domain name system.
Commenting on the designation, Dr. Paul Twomey, President and CEO of ICANN, stated: “We would like to thank all five qualified applicants, the entire Internet community, ICANN’s Generic Supporting Organization, and Telcordia for the work in making this a successful process.”
A detailed outline of the .NET Successor Registry Process can be found at the following link:
http://icann.org/tlds/dotnet-reassignment/net-rfp-process-summary-08jun05.pdf
Additionally, here are some of the key documents and announcement from the process:
27 May 2005 Telcordia Report .NET RFP on Evaluation
http://icann.org/tlds/dotnet-reassignment/net-rfp-finalreport-issue4-27may05.pdf
3 May 2005 ICANN Posts Telcordia Review of Findings
http://icann.org/tlds/dotnet-reassignment/review-of-findings-03may05.pdf
20 Jan 2005 ICANN Receives Five Applications to Operate .NET
http://icann.org/announcements/announcement-19jan05.htm
12 Dec 2004 ICANN .NET Reassignment RFP
http://icann.org/tlds/dotnet-reassignment/net-rfp-final-10dec04.pdf
5 Aug 2004 Final Report from the GNSO on .NET Criteria
http://www.gnso.icann.org/issues/dotnet/dotnet-reportv9.pdf
29 Jun 2004 Final Procedure for Designating Subsequent .NET Registry Operator
http://www.icann.org/announcements/announcement-29jun04.htm
6 Mar 2004 ICANN Board Resolution regarding Preparation for the Designation of a Transparent Procedure for Designating a Subsequent .NET Registry Operator
http://www.icann.org/minutes/rome-resolutions-06mar04.htm
About ICANN:
The Internet Corporation for Assigned Names and Numbers (ICANN) is an internationally organized, non-profit corporation that has responsibility for Internet Protocol (IP) address space allocation, protocol identifier assignment, generic (gTLD) and country code (ccTLD) Top-Level Domain name system management, and root server system management functions. As a private-public partnership, ICANN is dedicated to preserving the operational stability of the Internet; to promoting competition; to achieving broad representation of global Internet communities; and to developing policy appropriate to its mission through bottom-up, consensus-based processe s.
Any press enquires should be addressed to Tanzanica King at ICANN on +1 310 301 5804. Any follow-up questions or requests can be sent to press@icann.org.
FCC Chairman will stop at nothing to 'level the playing field'
Ashlee Vance, at Supercomm in Chicago, writes in The Register:
Many of you will be familiar with those Play-Doh presses that squeeze out turds of brightly colored goo in the shape of stars, circles or, these days, waffles. Well, imagine that Harvard Law School had one of these presses and replaced the colorful Play-Doh with mounds of dull, white flesh and then replaced the star or circle design with the outline of a bureaucratic suit. That's how we figure new FCC (Federal Communications Commissioner) Commissioner Kevin Martin came into being after seeing him speak yesterday at the Supercomm conference here in Chicago.
Martin wooed the Supercomm crowd with his boyish looks, southern charm and disarming approach to answering questions about the US communications agenda. If nothing else, Martin's toned provided a refreshing change from the ego-driven salesman Michael Powell who served before him. When not keeping children protected from breasts, Powell always seemed to be hawking Tivo, HDTV or PDAs. Despite saying "shop and buy" was the message he wanted to leave with the Supercomm crowd, Martin didn't go quite as far as Powell with the product placements, and we thank him for that.
Instead, Martin proved rather charming and humble. An IP-enabled, capitalist Cincinnatus came to mind.
"Establishing a regulatory environment that is conducive for . . . creating a level playing field for the various service provides out there" will be one of the "top priorities for the Commission going forward," he said during a question and answer session. And later, "I think the Commission needs to do all it can . . . to create a level playing field." And later, "I hope that people say I was fair in trying to address these issues - that we did try to make some progress in creating a level playing field."
Them Harvard boys know how to stay on message.
Read Ashlee's
entire commentary here.
AT&T'S Dorman Says IP Is Driving Telecom Growth
Phil Britt writes in Advanced IP Pipeline:
After weathering the burst of the investment bubble and the indictment of former executives, the telecom industry is transforming and growing again, AT&T chairman and CEO David Dorman said here Wednesday at Supercomm.
The growth, Dorman said, all comes from new technologies, like IP, wireless and Internet services, while traditional telephone services continue to decline.
Dorman linked the decline in part to the Telecommunications Act of 1996, which fueled investment and speculation in competitive carriers. Prior to the enactment of the law, carriers spent about 10 to 15 percent of revenues on capital expenditures, Dorman said. In the late 1990s, that figure grew to more than 40 percent for four consecutive years.
Lion's Birthday Wish Hides Trojan Horse
Sharon Gaudin writes on eSecurityPlanet.com:
Anti-virus experts are warning users about a Trojan horse that steals users' passwords and information while an animanted lion wishes them a happy birthday.
A spam campaign is tempting users to click on a link where the LDPinch-BD Trojan will be downloaded, infecting the computer. The malware is designed to steal sensitive information, including passwords, from various applications on the machine, according to analysts at Sophos, Inc., an anti-virus and anti-spam company with U.S. headquarters in Lynnfield, Mass.
The Trojan horse is accompanied by an animated GIF file of a singing lion. Although the image carries a copyright message from 123Greetings.com, the Trojan horse has no connection with the company, reports Sophos.
U.S. Wireless begins Pre-WiMax deployment
Hmmm. Yesterday it was BellSouth announcing that it will begin a "Pre-WiMax" network trial, and today it's U.S. Wireless announcing a much larger Pre-WiMax deployment.
One can only wonder if that if the WiMax specification changes significantly (or at all, for that matter) from what is deployed today, we'll simply have a bunch of incompatible WiMax technology deployments.
I certainly understand the time-to-market issues involved in deploying any product in a competitive market, but you simply can't turn a blind eye to compatibility issues that may come back to haunt you. Then again, I'm an engineer, not a business analyst. :-)
Supercomm: Securing service provider networks is a matter of national security
Tim Greene writes in NetworkWorld:
Top executives of major telecom equipment makers say beefing up security and reliability on service provider networks is necessary to protect customers and is a matter of national security.
"Wait until we see a shutdown of the telecom network...then we'll understand what a virus or intruder on your network can do," Bill Owens, president and CEO of Nortel told Supercomm 2005 attendees during a keynote panel today. "We need to get into the security of these networks for the security of our countries."
Public networks must be reliable and secure so first-responder calls go through, video meetings between patients and doctors remain private and public networks are protected from cyberterrorists, Lucent President and CEO Pat Russo says. "With innovation comes responsibility. We need to ensure that next-generation services are exciting and are reliable and secure," Russo says.
Ownes says the key to the public IP networks now being built is they must be made as reliable as traditional phone networks, Owens says.
UK: Sports body locks down critical data
Now if only their American counterparts would only follow suit....
Daniel Thomas writes on vnunet.com:
The English Institute of Sport (EIS) has tightened IT security to ensure that sensitive medical details about famous athletes and their training programmes cannot be stolen by hackers.
The organisation, which provides medical, nutritional and performance-related support to English athletes participating at Commonwealth and Olympic Games standard, has worked with IT supplier Lynx Technology to install the security systems at nine regional centres and 30 satellite offices.
Hacker cleared over NTL abuse message
Via The BBC.
An angry hacker who recorded a rude message on a cable helpline for other customers to hear has been found not guilty of causing offence.
Ashley Gibbins, 26, was so angry at being put on hold for an hour by NTL that he recorded a message littered with four-letter swear words.
But Teesside magistrates cleared him of a charge under the Communications Act ruling it was not "grossly offensive".
Mr Gibbins, a taxi driver of Redcar, told the court it had been a joke.
The court heard how Mr Gibbins had been waiting on the line to order broadband when he discovered he could change the recorded message so everyone who rang NTL customer service helpline was met with the stream of abuse.
The new message told astonished callers that NTL did not care about its customers and would not handle their complaints.
Europe broadband surpasses Americas
A Reuters newswire article appearing in CNN/Money:
More Europeans than Americans had a broadband Internet connection in the first quarter, according to a survey published Wednesday, which also showed South Korea is on the verge of losing its global pole position.
The Asia Pacific region, where most of the world's population live, remained the world's biggest broadband market with 61 million subscribers and a 39 percent share of the global broadband market, Anglo-Dutch research group TelecomPaper said. Europe was second with 47.95 million fast Internet subscribers, overtaking the Americas with 47.53 million.
"Europe has outrun the Americas for the first time in history and became the second largest broadband market in the world," TelecomPaper said in a note.
Mobile-phone outage hits Colorado, Wyoming
Bob Sullivan writes on MSNBC:
A software upgrade that went awry is being blamed for a two-hour outage this morning that left Sprint and Qwest customers in Colorado and Wyoming without mobile phone service.
The trouble began at 6:30 a.m. local time, said Sprint spokesman Dave Mellin. Service was restored by 8:30 a.m.
"It affected customers from Cheyenne to Colorado Springs," Mellin said. He said he didn't know how many consumers were affected, but the outage impacted the sizeable Denver market.
Qwest consumers who called a customer service line to complain heard a pre-recorded message indicating there was a "known outage."
New ads warn girls of online predators
John L. Levere of The New York Times writes (via The International Herald Tribune):
A new ad campaign warns teenage girls about the danger of online sexual predators.
One in five children received a sexual solicitation in 1998 and 1999, according to a survey of 1,500 regular Internet users age 10 to 17, conducted for the National Center for Missing and Exploited Children and the U.S. Justice Department. The study was done by the Crimes Against Children Research Center at the University of New Hampshire.
At Webby Awards, five words say it all
David Carr of The New York Times writes (via the International Herald Tribune):
One of the more charming idiosyncrasies of the Webby Awards, the annual awards for achievement in Web creation, requires that recipients use five words, and five words only, to make their acceptance speeches.
So after a night full of award innuendos, the 550 people in attendance were wondering how Al Gore, the loquacious former vice president, would respond to his lifetime achievement award.
He did not disappoint. "Please don't recount this vote," he said. The place went nuts.
Senate panel votes to expand Patriot Act
Declan McCullagh writes in his Politics Blog on C|Net News:
Forget scaling back the Patriot Act.
Instead, the controversial post-9/11 law would be expanded to give the FBI new powers to demand documents from companies without a judge's approval, according to a vote late Tuesday by the Senate Intelligence committee.
The final text of the Senate Intelligence committee's amendments was not immediately available, and reporters were barred from the secret session during which the vote was held.
But the proposal appears to grant the FBI more power to seek information from banks, hospitals, libraries, and so on through "administrative subpoenas" without prior judicial oversight. The subpoenas are only supposed to be used for terrorism or clandestine intelligence cases.
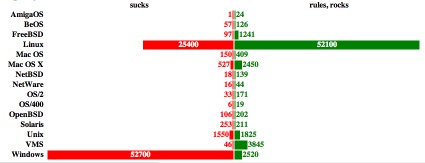
What OS-names are more commonly associated with "sucks" than "rules"?
This one is just too good to pass up.
Over on Boing Boing, Cory Doctorow posted:
The Operating System Sucks-Rules-O-Meter does periodic Altavista searches with the name of an operating system and the word "sucks" and "rocks" appended to it, and charts the results.
June 15 Release Set for Windows XP 'N'
Nate Mook writes on BetaNews:
Microsoft announced on Wednesday the release timetable for its version of Windows XP without Windows Media Player, simply branded with the additional moniker: N. The slimmed down OS will be available to European computer makers on June 15, with a retail launch slated for July 1.
It's not clear, however, if computer manufacturers will even be interested in the N editions, which carry the same price tag as versions with Windows Media Player.
Gartner: National Data Breach Law Inevitable
From the "no-duh" dept.--
Roy Mark writes on internetnews.com:
Congress is not going to ignore the spate of data breaches plaguing private enterprise and will pass new data protection laws, a Gartner analyst predicted.
Speaking at a Gartner IT security conference less than 24 hours after CitiFinancial admitted it had lost almost 4 million records with personally identifiable information, John Pescatore told a packed room that Congress is bound to respond with new laws.
"What will be the next Sarbanes-Oxley? It's going to be some type of identity theft or data security legislation," said John Pescatore, a vice president and analyst at Gartner. "That's such a politician-friendly issue, it's the next big one coming."
U.S. Feds Target Hackers
Via Red Herring.
The U.S. Department of Homeland Security will spend $11.7 million on research to secure the computer-aided control systems that operate the nation’s critical infrastructure.
The new funds announced Monday will help continue studies in cyber security that started last year at the U.S. Department of Energy’s Idaho National Laboratory (INL).
"We’re at the point where industry is beginning to recognize the potential threats of unsecured control systems and they are more willing to work with government agencies to improve the security of the nation’s critical infrastructure,” said Julio Rodriguez, department manager for critical infrastructure assurance at INL.
The expanding RSS universe
Michael Bazeley writes on SiliconBeat:
At some point, the numbers become so big that it's hard to know what to make of them, but we have a new data point from Bloglines about the size of the RSS world and the growth in publishing that supports it. The Ask Jeeves-owned service is announcing tomorrow [June 8] that it has 500 million blog and news feed articles stored in its database. From the news release:
"Bloglines' milestone reflects the meteoric rise in popularity of blogs as a new communication channel, the development of RSS-type technologies for content syndication, and the creation of user-friendly newsreaders to simplify the process of subscribing to blogs and news feeds of interest. Between January and June of this year, the size of the Bloglines index doubled. And each day Bloglines adds 2 million to 2.7 million new blog and news feed articles to the database, drawn from a diverse range of sources in many languages--from blogs about knitting to major online newspaper feeds."
Symantec sues Hotbar
Nick Farrell writes in The Inquirer:
SECURITY OUTFIT Symantec wants a court to allow its software to identify some programs made by Hotbar as adware.
Hotbar, which is made by a Microsoft partner, Hotbar.com, is a kids add-on that personalises email and browsers. It gives a range of smiley faces for users to play with and gives access to search, skins and yellow pages.
However, HotBar also tracks web site visits and also has an autoupdate feature. Some users find it tricky to remove.
Spyware researcher Ben Edelman,
here, said that Hotbar installs itself via banner ads on kid websites. He said Hotbar combines pop-up ads with other forms of advertising, including ads within web browser toolbars, automatically-opening sidebars, ads in ordinary Windows Explorer screens and desktop icons.
A Symantec spokesperson said the company did not want any damages as part of the suit and just needed a declaratory judgment affirming Symantec's assertion that certain Hotbar program files are adware and can be treated as computer security risks.
We assume this will keep Symantec out of legal hot water if Hotbar decides to sue the security company for deleting its software. Last month, Anti-Spyware outfit Sunbelt Software received a cease and desist letter from Hotbar, which took issue with Sunbelt categorising its toolbar as "low risk adware". µ
Hotmail users exposed to cookie snaffling exploit
John Leyden writes in The Register:
A cookie manipulation exploit that created a possible means for hackers to break into Hotmail accounts forced Microsoft into pulling a portion of its website last weekend.
The exploitable page - http://ilovemessenger.msn.com - has been updated to remove a cross site scripting flaw that was the subject of the exploit. But Alex de Vries, the Dutch security enthusiast who discovered the trick, warns that other portions of MSN's site are still vulnerable.
The exploit works in three stages. Hackers use security loopholes to inject hostile code onto MSN's web site. Hackers can then harvest Hotmail cookies from surfers redirected to this contaminated page by taking advantage of the use of Hotmail cookies across the MSN.com domain. Once hackers have a victim's cookie they can use tools to trick Hotmail into thinking they already logged on as this user.
European Commission mulls who should govern the internet
Via OUT-LAW.com.
The European Commission yesterday set out its priorities for a forthcoming international summit on developing the information society. Top of the agenda is the question of internet governance, currently in the control of US-based ICANN.
This will be the second World Summit on the Information Society (WSIS). The first one took place in Geneva in December 2003, with the aim of finding ways of using ICT to improve the global economy and tackle worldwide problems such as poverty.
It was hailed a success, resulting in a Declaration of Principles for governing the information society and an Action Plan for implementing them. But agreement was only reached by leaving the toughest issues to future discussion. Most controversial among these was the question of who should govern the internet.
Air France wins 'sucks' domain name
Via OUT-LAW.com.
The domain name AirFranceSucks.com will be transferred to Air France. But the airline's victory at arbitration was not without controversy: panellists disagreed about what the word 'sucks' really means to internet users.
The name was registered by Florida-based Virtual Dates Inc. in 1999. It was only in February 2005 that Air France took a claim before the World Intellectual Property Organisation (WIPO), alleging cybersquatting. The decision was made on 24th May and published today.
For most of the past six years, Virtual Dates pointed the domain name at a page of ePinions.com, an ad-supported site that rates and invites reader comments on everything from movies and barbecues to office supplies and zoos.
Accuracy of Commercial Data Brokers
Thanks to Bruce Schneier for bringing our attention to this study. Bruce writes in his blog, Schneier on Security:
PrivacyActivism has released a study of ChoicePoint and Acxiom, two of the U.S.'s largest data brokers. The study looks at accuracy of information and responsiveness to requests for reports.
It doesn't look good.
From the press release:
100% of the eleven participants in the study discovered errors in background check reports provided by ChoicePoint. The majority of participants found errors in even the most basic biographical information: name, social security number, address and phone number (in 67% of Acxiom reports, 73% of ChoicePoint reports). Moreover, over 40% of participants did not receive their reports from Acxiom -- and the ones who did had to wait an average of three months from the time they requested their information until they received it.
I spoke with Deborah Pierce, the Executive Director of PrivacyActivism. She made a couple of interesting points.
First, it was very difficult for them to find a legal way to do this study. There are no mechanisms for any kind of oversight of the industry. They had to find companies who were doing background checks on employees anyway, and who felt that participating in this study with PrivacyActivism was important. Then those companies asked their employees if they wanted to anonymously participate in the study.
Second, they were surprised at just how bad the data is. The most shocking error was that two people out of eleven were listed as corporate directors of companies that they had never heard of. This can't possibly be statistically meaningful, but it is certainly scary.
Chinese gamer sentenced to life
Via The BBC.
A Shanghai online gamer has been given a suspended death sentence for killing a fellow gamer.
Qui Chengwei stabbed Zhu Caoyuan in the chest when he found out he had sold his virtual sword for 7,200 Yuan (£473).
The sword, which Mr Qui had lent to Mr Zhu, was won in the popular online game Legend of Mir 3.
Attempts to take the dispute to the police failed because there is currently no law in China to protect virtual property.
Military 'hacker' freed on bail
Via The BBC.
A British man arrested for allegedly carrying out the "biggest military computer hack of all time" has been released on bail by magistrates.
Gary McKinnon, who is accused of hacking into 53 US military and Nasa computers in 2001 and 2002, appeared at Bow Street Magistrates Court in London.
The 39-year-old, of Wood Green, north London, will be back in court for an extradition hearing on 27 July.
His lawyer said he would contest extradition to the US "vigorously".
Mr McKinnon, an unemployed computer systems administrator, is known on the internet as "Solo."
He is accused of hacking into computer networks operated by Nasa, the US Army, US Navy, Department of Defence [sic] and the US Air Force.
One of the networks belonged to the Pentagon.
The US estimates the costs of tracking and correcting the problems he allegedly caused were around $1m (£570,000).
If he is extradited and found guilty, Mr McKinnon faces a maximum penalty of five years in prison and a £157,000 fine.
The Briton was indicted in 2002 by a federal grand jury on eight counts of computer-related crimes in 14 different states.
It claimed that he hacked into an army computer at Fort Myer, Virginia, obtained administrator privileges and transmitted codes, information and commands.
FCC chairman 'sympathetic' to fewer video rules
Justin Hyde writes for Reuters:
The chairman of the U.S. Federal Communications Commission said on Tuesday he was "sympathetic" to the arguments of large local telephone companies that want fewer legal barriers to launching video services.
The comments from FCC Chairman Kevin Martin came shortly after the chairman of Verizon Communications Inc. said the company would not "redline," or discriminate against poorer customers to the advantage of wealthier ones, as it rolls out its video service.
Both Verizon and SBC Communications Inc. are spending billions of dollars to launch residential video services over the next 12 months. They see the move as essential to compete with cable companies targeting their customers with telephone and high-speed Internet services.
U.S., Japanese companies team on voice set-top box
Via EE Times.
U.S.-based Amaru Group and its subsidiary M2B World Inc. have completed a deal with Japan IP provider United Power Co. Ltd. to distribute major entertainment content through a broadband-serviced, voice-activated set-top box.
According to the companies, the agreement reflects a breakthrough in Japan, where U.S.-based media companies have had difficulty securing such broad-scale distribution partnerships, and signifies the trend toward broadband streaming for global consumers seeking entertainment media.
Daily gapingvoid fix....
This time around: alcohol. :-)
Via gapingvoid.com. Enjoy!
Google now most valuable media company
Via Reuters.
Google Inc. took over the top spot as the most highly valued media company this week, surpassing Time Warner Inc. in just 10 months of trading as a public company.
Google's share price on the Nasdaq rose another $2.18, or 0.75 percent, to close at $293.12 on Tuesday, an all-time high. Stock market analysts have suggested the stock could go as high as $325 or $350 a share.
With a current stock market capitalization of more than $80 billion, Google is now worth more than any other media company in the world. That includes Time Warner, created five years ago when AOL purchased Time Warner for $106 billion in a much-hyped combination of old and new media.
Confusion over next generation Wi-Fi
Not surprising, given vendor deployment of products sporting "Pre-N" standards. Personally, I think that the more products that are in the market, especially in end-user's hands, before the final 802.11n specification is approved & available, the bigger the mess we'll have on our hands.
An AP newswire article on CNN sums it pretty good for the uninitiated:
The next generation of Wi-Fi will be so powerful that it's expected to be capable of carrying everything from Internet phone calls and music to high-definition television streams over the airwaves without a hiccup.
But it may be a while before we get to enjoy the full benefits of wireless communication.
The standard technically known as 802.11n does not exist yet and the final 802.11n specifications aren't expected to receive an official nod until late next year at the earliest.
Alcatel Launches Cell-WLAN Handoff Capabilities
Via Mobile Pipeline.
French telecommunications vendor Alcatel said Tuesday that it has started offering technology to wireless operators that enables data and voice handoffs between cellular, Bluetooth and Wi-Fi networks.
The technology uses Unlicensed Mobile Access (UMA), a specification that is being developed by a number of telecom equipment vendors. It is aimed at wireless operators that use GSM-based technology and would incorporated into those operators' base stations and other infrastructure equipment.
Microsoft Adds Sender ID Anti-Spoofing Protocol To Exchange 2003 SP2
Watch this spot for updates, because if I recall correctly, there was a lot of turmoil last year in the IETF when Microsoft wanted to use their sender ID authentication mechanism(s) as a draft standard... or maybe I'm confused.
In any event, this announcement comes to us via TechWeb News.
When it launches later this year, Exchange Server 2003 Service Pack 2 (SP2) will support Sender ID, Microsoft's sender authentication scheme, the Redmond, Wash.-based developer said.
The addition of Sender ID to Exchange 2003 SP2 will be the first time Microsoft's mail server includes an authentication technology, although Microsoft has been pushing the scheme for more than a year. It's also been using Sender ID on its free Hotmail e-mail service, where it claimed the authentication has reduced spam and phishing scams, although it hasn't released hard numbers.
Sender ID, like other authentication protocols, verifies the sending IP address against the purported owner of that domain. The goal is to reduce address spoofing, where spammers and phishers disguise their true identities.
Phone numbers of hundreds of Chinese celebrities posted on web
An AFP newswire article on Yahoo! News:
Hundreds of Chinese celebrities including movie star Zhang Ziyi have reportedly been bombarded with phone calls after their mobile numbers were posted online.
The numbers of around 600 writers, actors, sports stars and singers appeared on a website on Saturday and remained there for two days until the list was deleted, the Beijing Star Daily said.
Verizon says no 'redlining' to rich in video debut
Of course, this has been a huge issue here in Texas--the cable television operators have been running propaganda commercials on cable television for the past couple of months accusing the telcos of planning to do just this--cater only to the more wealthy neighborhoods in any "Video-over-foo" deployment-- to influnce the discussion on allowing telco's involvement in deploying video (read: television) services here in Texas.
Prior history here, and even earlier this morning here.
And now, Reuters brings us this revelation:
The chairman of Verizon Communications Inc. said on Tuesday the company would not "redline," or favor wealthier customers at the expense of poorer ones, as it rolls out its video service.
Ivan Seidenberg said that cable companies had used the threat of redlining as a "political tool" against Verizon and SBC Communications Inc., which want to compete against cable companies but without many of the legal restrictions.
Intelligence Changes Still Thwarted By Lack Of Information Sharing
An AP newswire article written by Lara Jakes Jordan in InformationWeek cites interagency confusion and mistakes by the FBI as key culprits:
Overlapping responsibilities among U.S. intelligence agencies could lead to failures in assessing terror threats, experts said Monday in examining changes at the CIA and FBI since the Sept. 11, 2001, attacks.
Part of the problem stems from the continued lack of a reliable information-sharing system within the intelligence community, according to panelists led by a member of the 9/11 Commission that investigated missteps leading to the attacks.
"There's a real vulnerability," former Attorney General Richard Thornburgh said during the two-hour discussion--the first of eight panels hosted this summer by the commission.
Supercomm 2005: The final Supercomm
Tim Greene writes in NetworkWorld:
Supercomm 2005 is the 18th and final Supercomm, with the two industry organizations that sponsored the event for the past five years splitting up.
Each group is organizing its own new show, both of which will debut next year.
The Telecommunications Industry Association (TIA), a group of vendors, is starting up GlobalComm, which will be held in Chicago June 5-8, 2006, roughly the same time that Supercomm did.
TIA's Supercomm partner, carrier group U.S. Telecom Association (USTA), is running off to Las Vegas to start TelecomNEXT, a carrier-focused show sheduled for March 19-25, 2006.
Vonage Teams Up To Deliver Cordless VoIP Phone
Matthew Friedman writes in Networking Pipeline:
Vonage is teaming up with Uniden America Corporation to develop a cordless phone to use with its broadband VoIP service.
Based on the Texas Instruments TNETV1060 VoIP gateway chipset, the Uniden UIP1869V telephone system will be compatible with Vonage's consumer broadband voice service. The phone features a base unit, which can support up to ten cordless handsets, that plugs directly into a broadband connection or router without a standalone adapter.
Nominet nobbles Oz fraudsters
Dinah Greek writes on Computeract!ve:
Nominet has won another legal victory in Australia against two men it accused of hacking into its database of .uk names.
The .uk internet domain name registry has now obtained an Australian Federal Court order to freeze the assets and bank accounts of Bradley Norrish and Chesley Rafferty, the individuals behind the UK Internet Registry scam.
The order prevents the defendants from moving their assets out of Australia or transferring them to third parties to avoid judgment.
Schneier: Threats shift to databases
Florence Olsen writes on FCW.com that:
Cryptography has diminished somewhat in importance as threats to information security shift from eavesdropping to attempts to gain control of computers and networks, a cryptographic expert said this week at the Gartner IT Security Summit in Washington, D.C.
Bruce Schneier, chief technology officer at Counterpane Internet Security, said protecting data while it is stored on networks and PC computers has emerged as a greater threat than unauthorized sniffing of data packets as they are transmitted over a network.
Seattle Tops List for Wireless Web Access
Huzzah! The Austin-San Marcos, TX. area makes the list as number 3!
An AP newswire story by Rachel Konrad on ABC Business News reports that:
Seattle and San Francisco are the most "unwired cities" in America top spots for computer junkies who send e-mail and surf the Web at restaurants, libraries or public plazas.
Metropolitan Seattle percolated past the San Francisco Bay area this year thanks to an abundance of Starbucks Corp. outlets, which have wireless "hot spots" where patrons linger over latte and laptops, according to Intel Corp.'s annual ranking. Seattle also benefited from wireless access at its Pike Place Market and the Space Needle.
San Francisco finished second, thanks to wireless hubs at bars, convention centers, office parks and strip malls from Oakland to San Jose. Hundreds of residents build wireless access towers on their roofs, providing free connections for neighbors.
Siemens Sells Cell Phone Unit to BenQ
Nate Mook writes in BetaNews:
Siemens said on Tuesday it was selling its mobile phone unit to Taiwanese tech firm BenQ, in exchange for a 2.5-percent stake in the company and an undisclosed sum of money. Siemens has been struggling to turn around its ailing cell phone division, which has accumulated hundreds of millions of dollars in losses.
BenQ will retain the Siemens brand name for five years, along with any current sponsorship agreements. The move is expected to give BenQ more market exposure, along with doubling its annual revenues. "With this partnership we have found a sustainable perspective for our mobile phones business. BenQ and Siemens complement one another ideally," Siemens CEO Klaus Kleinfeld said in a statement.
University of Texas hacker trial begins
Local news for us here in Austin.
Steven Kreytak writes in the Austin American Stateman (registration required):
Christopher Phillips is a computer nerd who hacked the University of Texas' network as a challenge and kept the names and Social Security numbers he retrieved as trophies, his lawyer told a federal jury in Austin on Monday.
"There will be no evidence that he used any of them to harm a soul," Steve Brittain said at the start of Phillips' trial before U.S. District Judge Lee Yeakel.
The 22-year-old former UT computer sciences student is facing up to five years in prison on each of the four counts against him. Federal prosecutors say that in 2002 and 2003 he stole 37,000 names and Social Security numbers of faculty, students and others whose personal information was in the university's computer network.
"He found a back door into the entire UT system," Assistant U.S. Attorney Mark Roomberg said in his opening statement.