Banks Failing on ATM Security
Ian Williams writes on vnunet.com:
Banks and financial institutions are leaving customers' personal details vulnerable to hackers by failing properly to secure their ATMs, according to a new report.
Managed security firm Network Box cited three main threats to ATMs: IP worms, disruption of the IP network and denial of service, and the harvesting of transaction data for malicious purposes.
The company said that ATM security risks have increased because of the changing ways in which they operate.
Many ATMs were built on proprietary hardware, software and communications protocols.
But it is estimated that 70 per cent of current ATMs are based on PC/Intel hardware and commodity operating systems using standard IP networking with some additional peripherals housed in a secure vault-like box.
More
here.
Now the Pentagon Tells Bush: Climate Change Is Real And Will Destroy Us
Mark Townsend and Paul Harris write on The Observer:
Climate change over the next 20 years could result in a global catastrophe costing millions of lives in wars and natural disasters..
A secret report, suppressed by US defence chiefs and obtained by The Observer, warns that major European cities will be sunk beneath rising seas as Britain is plunged into a 'Siberian' climate by 2020. Nuclear conflict, mega-droughts, famine and widespread rioting will erupt across the world.
The document predicts that abrupt climate change could bring the planet to the edge of anarchy as countries develop a nuclear threat to defend and secure dwindling food, water and energy supplies. The threat to global stability vastly eclipses that of terrorism, say the few experts privy to its contents.
'Disruption and conflict will be endemic features of life,' concludes the Pentagon analysis. 'Once again, warfare would define human life.'
The findings will prove humiliating to the Bush administration, which has repeatedly denied that climate change even exists. Experts said that they will also make unsettling reading for a President who has insisted national defence is a priority.
More
here.
Early Morning Flashback: Bruce Springsteen - Born In The U.S.A.

A message we need to hear, again.
Enjoy.
- ferg
Australian Police Unveil $1M Internet Scam
Via The Sydney Morning Herald.
Police have uncovered a $1 million internet scam with links to Nigeria during a raid at a home in Perth's southern suburbs.
Western Australia Police Computer Crime Squad detectives arrested a Nigerian citizen after raiding the house in Treasure Road, Queens Park about 7pm (WDT) yesterday.
Police allege the 29-year-old is involved in an international syndicate, and pretending to be a foreign diplomat to convince his victims of his credentials and defraud them of significant amounts of money.
The raid was part of Operation Dunkley, which was formed after continual cases of West Australians being deceived by African fraudsters were recorded by the Computer Crime Squad.
More
here.
U.S. Toll In Iraq, Afghanistan

Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Friday, Feb. 22, 2008, at least 3,969 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes eight military civilians. At least 3,228 died as a result of hostile action, according to the military's numbers.
The AP count is six higher than the Defense Department's tally, last updated Friday at 10 a.m. EST.
As of Friday, Feb. 22, 2008, at least 415 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Feb. 16 at 10 a.m. EST.
Of those, the military reports 283 were killed by hostile action.
More
here and
here.
And as always, the
Iraq Coalition Casualty Count keeps the grim watch on their website
here.
Honor the Fallen.
Shocker: Enzyte Maker Found Guilty of Fraud
 Enzyte Character Spokesperson, "Smiling Bob".
Enzyte Character Spokesperson, "Smiling Bob".An AP newswire
article, via
SFGate.com, reports that:
A federal court jury on Friday found the owner of a company that sells "male enhancement" tablets and other herbal supplements guilty of conspiracy to commit mail fraud, bank fraud and money laundering.
Steve Warshak, whose conviction was reported Friday by The Cincinnati Enquirer, is founder and president of Berkeley Premium Nutraceuticals, which distributes Enzyte and a number of products alleged to boost energy, manage weight, reduce memory loss and aid restful sleep.
Warshak, 40, could face more than 20 years in prison and his company could have to forfeit tens of millions of dollars.
Prosecutors claimed customers were bilked out of $100 million through a series of deceptive ads, manipulated credit card transactions and the company's refusal to accept returns or cancel orders. They said unauthorized credit card charges generated thousands of complaints over unordered products.
Warshak's mother, Harriett Warshak, also was convicted of conspiracy, bank fraud and money laundering.
More
here.
Monster Investigated by FTC Concerning Data Security
Via Workforce.com.
The U.S. Federal Trade Commission has launched an investigation into information security practices at electronic job board Monster.com.
Monster disclosed the probe in a filing with the U.S. Securities and Exchange Commission, and said the inquiry stemmed from a computer attack announced last year that resulted in the illegal downloading of contact information for 1.3 million job seekers.
“On October 29, 2007, the Company was requested to voluntarily provide information to the staff of the Federal Trade Commission in connection with a non public inquiry into certain information security practices of Monster.com,” Monster disclosed in an SEC filing. “The inquiry arises as a result of the attack.”
FTC investigations as a rule are nonpublic unless the firm under investigation acknowledges the probe. The agency in recent years has been going after companies with alleged failures related to the protection of sensitive consumer information. In a number of cases, organizations have settled FTC charges and agreed to new data security policies.
More
here.
Hat-tip: Pogo Was Right
Fear-Mongering 101: U.S. Says It Has Missed Intelligence After Spy Act Expired
A Reuters newswire article by Randall Mikkelsen, via The Boston Globe, reports that:
U.S. spy agencies have missed intelligence in the days since terrorism surveillance legislation expired, the Bush administration said on Friday, but Democrats accused it of fear mongering and blamed it for any gaps.
U.S. Attorney General Michael Mukasey and Director of National Intelligence Michael McConnell fired the latest shot in the administration's battle with Congress to obtain new legislation to wiretap terrorism suspects.
But House Speaker Nancy Pelosi said Republican lawmakers and the administration had failed to participate on Friday in congressional staff negotiations over the bill, and noted President George W. Bush opposed extending the temporary act.
"The president and congressional Republicans have only themselves to blame," for any missed intelligence, said Pelosi, a California Democrat.
More
here.
DNI Report Details Data Mining Programs
Steven Aftergood writes on Secrecy News:
The Office of the Director of National Intelligence provided an overview of U.S. intelligence data mining development programs in a new report [.pdf] to Congress.
Data mining is used by intelligence agencies to search through databases in order to discern patterns of activity that could indicate a threat to national security.
The new report presents brief descriptions of several data mining-related intelligence projects, some of which have previously been publicly identified and others that appear to be newly disclosed.
More
here.
TSA Security Officer Joins Contractor Under Investigation for Security Lapses
Kim Zetter writes on Threat Level:
Patricia Titus, chief information security officer for the Transportation Security Administration, is leaving the TSA next month to take a job with Unisys, a Department of Homeland Security and TSA contractor.
This might strike some people as odd, given that Unisys is currently under FBI investigation for criminal fraud for failing to protect the DHS computer network from intrusions.
Unisys won a $1 billion contract with the DHS in 2002 to secure and manage the IT network for the DHS and TSA but, according to congressional investigators, failed to properly install and manage intrusion detection systems on the networks then allegedly falsely certified to the DHS that the network had been protected to cover up its neglect.
More
here.
Employees Snoop on Customer Data
An AP newswire article by Ryan J. Foley, via USA Today, reports that:
A landlord snooped on tenants to find out information about their finances. A woman repeatedly accessed her ex-boyfriend's account after a difficult breakup. Another obtained her child's father's address so she could serve him court papers.
All worked for Wisconsin's largest utility, where employees routinely accessed confidential information about acquaintances, local celebrities and others from its massive customer database.
Documents obtained by The Associated Press in an employment case involving Milwaukee-based WE Energies shine a light on a common practice in the utilities, telecommunications and accounting industries, privacy experts say.
Vast computer databases give curious employees the ability to look up sensitive information on people with the click of a mouse. The WE Energies database includes credit and banking information, payment histories, Social Security numbers, addresses, phone numbers, and energy usage. In some cases, it even includes income and medical information.
More
here.
RFID: The Hands-Free Way to Steal a Credit Card
Robert Vamosi writes on the C|Net "D3F3NS3 1N D3PTH" Blog:
Adam Laurie, an RFID security expert, used the Black Hat DC 2008 conference here, to demonstrate a new Python script he's working on to read the contents of smart-chip-enabled credit cards.
As part of his presentation Wednesday, Laurie asked for someone from the audience to volunteer a smart card. Without taking the card out of the volunteer's wallet, Laurie both read and displayed its contents on the presentation screen--the person's name, account number, and expiration clearly visible.
Demonstrations like that show the potential misuse of RFID technology in the near future. Without touching someone, a thief could sniff the contents of an RFID-enabled credit card just in passing. The same is true for embedded RFID chips in the human body, work access badges, some public transit cards, and even the new passports in use in more than 45 countries.
More
here.
Insurance Company Reimburses TJX Almost $19 Million For Data Breach
Evan Schuman writes on StorefrontBacktalk:
In the middle of a better-than-expected earnings report from TJX on Wednesday, the retailer whose databreach of 100 million cards was the worst in credit card history reported that it was paid somewhat less than $19 million by its insurance company.
Referring to $178 million the chain had set aside to deal with data-breach-related costs, TJX said that on Jan. 26, 2008, "TJX reduced the reserve by $19 million, primarily due to insurance proceeds with respect to the computer intrusion, which had not previously been reflected in the reserve, as well as a reduction in estimated legal and other fees as the Company has continued to resolve outstanding disputes, litigation and investigations."
More
here.
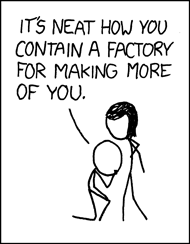
Yet Another xkcd Gem: Advanced Technology
We
love xkcd.
- ferg
Another Liechtenstein Bank Suffers Theft of Client Data
David Crawford and Mike Esterl write in The Wall Street Journal:
Tiny Liechtenstein's reputation as a reliable and discreet tax haven for wealthy Europeans is coming under fresh attack.
German prosecutors say they are investigating the internal theft of confidential client data from Liechtenstein bank Liechtensteinische Landesbank AG, or LLB. Investigators say the bank, which is the alpine principality's second largest, paid blackmailers millions of euros to try to keep the affair secret.
Liechtenstein already is wrestling with fallout from a widening tax-evasion probe in Germany sparked by a then-employee's alleged theft of client data from LGT Group, the principality's largest bank.
In both cases, prosecutors allege, bank employees culled sensitive client information electronically, then hawked it to prospective buyers -- foreign authorities in the case of LGT, and the bank itself and the bank's clients in the case of LLB. While such leaks aren't unprecedented, they are "very, very unusual," said Franz-Hermann Brüner, who heads the European Commission's antifraud office in Brussels.
More
here.
Hat-tip: Pogo Was Right
Experts Hammer Web 2.0 Security
Matt Hines writes on InfoWorld:
Even as social networking darling Facebook prepares a version of its online networking application aimed specifically at enterprise users, legions of security experts are getting behind the idea that the sites represent a serious threat to businesses and other organizations.
From the ability of malware, adware, and spam distributors to use the sites as delivery vehicles for their latest work to the opportunity for cyber-criminals to craft extremely targeted attacks using information garnered from individual profiles posted on pages of Web 2.0 properties, social networking is rapidly becoming a serious pain point, researchers maintain.
Recent examples of malware and adware distribution schemes carried out on the existing services operated by Facebook and MySpace represent merely the tip of the iceberg, they said, with many attackers likely already hard at work creating new methods for duping users of the sites into exposing themselves and the companies that they work for.
More
here.
Defense Tech: Analyzing the Threat of Cyber Attack
Kevin Coleman writes on Defense Tech:
Did you know that the Bush administration is pushing to spend $6 billion on cyber security in 2008? (Wall Street Journal)
Would you like to know why? If so read the facts below.
Did you know that AL QAEDA'S top cyber terrorist used phishing schemes and other cyber attacks to steal credit card accounts and buy $3 million worth of terrorist equipment? (FBI)
Did you realize that in the past minute over 5,000 significant incidents were reported to HackerWatch.org? (Hackerwatch.org)
Did you realize that the financial impact of computer viruses in 2005 was over $14 billion and continues to grow? (Computer Economics)
More
here.
Reed Elsevier Seeks to Acquire ChoicePoint for $4.1B
Ellen Nakashima writes in The Washington Post:
Reed Elsevier PLC, the owner of the LexisNexis Group, is seeking to acquire ChoicePoint Inc. in a $4.1 billion cash deal that would create a global data brokering service.
By combining database giants LexisNexis and ChoicePoint, Reed Elsevier would handle information about hundreds of millions of people and sophisticated software to handle it. Both companies play key roles in law enforcement, homeland security and intelligence, as well as providing information to the private sector.
Both also have been hit by identity theft and security problems.
More
here.
UK: Call to Scrap Children's Database
Via The BBC.
The government faces calls to scrap a database containing the details of every child in England after a report said it could never be secure.
The report, by accountants Deloitte and Touche, was ordered after last year's missing data discs crisis.
Ministers say they accept its call for "further controls" on the £224m ContactPoint child protection system.
But they have come under fire from the Lib Dems and Tories for refusing to publish the full report.
More
here.
Banks: Losses From Computer Intrusions Up in 2007
Brian Krebs writes on Security Fix:
U.S. financial institutions reported a sizable increase last year in the number of computer intrusions that led to online bank account takeovers and stolen funds, according to data obtained by Security Fix. The data also suggest such incidents are becoming far more costly for banks, businesses and consumers alike.
The unusually detailed information comes from a non-public report assembled by the Federal Deposit Insurance Corporation, the federal entity that oversees and insures more than 9,000 U.S. financial institutions. The statistics were gathered as part of a routine quarterly survey called the Technology Incident Report, which examines so-called suspicious activity reports (SARs). In this case, SARs that were filed in the 2nd Quarter of 2007. SARs are federally mandated write-ups that banks are required to file anytime they spot a suspicious or fraudulent transaction that amounts to $5,000 or more.
A copy of the report was provided by a trusted source who asked to remain anonymous. An FDIC spokesperson could not be immediately reached for comment.
More
here.
Mark Fiore: The Big Beef Recall

"Doreen the Downer", by Mark Fiore.
Via The San Francisco Chronicle.
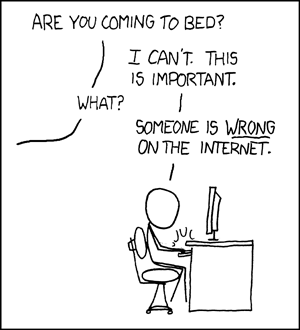
Another xkcd Gem: Duty Calls
We
love xkcd.
Australia: Telstra Helps Phishers pwn Its Customers
Liam Tung writes on the ZDNet.co.au "Securify This!" Blog:
Following a rash of Telstra customers reporting phishing attacks, the telco has issued advice on how to discern the real Telstra from fake ones -- but the advice it gives is more likely to help phishers than its customers.
Telstra customers will continue receiving marketing e-mails, despite being targeted by phishing e-mails and fake Telstra doorknockers.
"We do communicate with clients by e-mail. That always includes the full company name and ABN (Australian Business Number). We also ask customers to log in to the Mybigpond secure Web page. We never ask customers to send confidential e-mails, we don't include links to download and only include attachments if there is a strong reason to explain why," a Telstra spokesperson said.
Well, this is pretty handy information. If you're a phisher, simply type "Telstra ABN" into Google and you're half way there to gaining a user's trust.
More
here.
Canada: Quebec Police Bust Alleged Hacker Ring
A Canwest News Service article by Jan Ravensbergen, via The National Post, reports that:
Quebec provincial police said Wednesday they have dismantled what they called the largest and most damaging computer-hacking network ever uncovered in Canada.
They collared 17 hacking suspects aged 17 to 26. All are male except for one, a 19-year-old woman.
"This is a new form of organized crime," [investigator Capt. Frederick Gaudreau] proclaimed to reporters summoned to SQ headquarters in Montreal.
Savvy youngsters who've grown up with computers can take advantage of lax or inattentive users connected via broadband to the Internet.
That's what this ring did, Capt. Gaudreau alleged, adding that its operators extended their electronic tentacles from some of Quebec's smaller towns to seize control, via sophisticated remote-access software, of almost a million computers in more than 100 countries.
More here.
Online Gaming Sites Attacked by Botnets
Vin Narayanan writes on Casino City Times:
Distributed denial of service attacks (DDoS) wreaked havoc at online gaming sites earlier this week. Full Tilt Poker, Titan Poker, Virgin Games and Party Poker were among the sites attacked by a web-based botnet, according to the Shadowserver Foundation, a watchdog group of security professionals that gathers, tracks, and reports on malware, botnet activity, and electronic fraud. Some e-commerce sites were also attacked.
The full impact of these attacks is not immediately clear. Full Tilt Poker's Web site was inaccessible for parts of Sunday and Monday. And Full Tilt had to "pause" the final table of the FTOPS VII Main Event for a brief period with just three players remaining when its client lost connectivity with the Full Tilt servers.
More
here.
Hat-tip: FIRST.org Global Security News
Securing The Wrong Spaces: A Lesson
Mike Masnick writes over on techdirt.com:
A brand new Japanese warship that apparently has the country's latest and greatest radar system, was unable to spot a fishing boat in its path, leading to a collision and two missing fishermen. This is raising all sorts of questions about the quality of the radar system, but some are saying that the collision was really due to human error and that the radar system is designed more to watch out for missiles in the air, rather than ships below it.
That's a fair enough response, but does point out that vulnerabilities come from all directions -- and you can make the best system in the world, but if it's looking for the wrong thing, it won't stop something bad from getting through. It does seem rather ironic to set this ship up to be the best in the world at spotting threats from the sky -- and forget to include a decent system to find threats right next to it in the sea.
More
here.
Note: There is a great security lesson to be learned here -- if you're focused on securing only a subset of the entire threat landscape, the insecurities will generally occur in the places you're not focusing on. Focus on the
Big Picture.
-ferg
Hackers Look for People Who Know Other Languages
An AP newswire article by Jordan Robertson, via SFGate.com, reports that:
Wanted: computer virus writers. Must be fluent in Mandarin. Or Russian. Or Portuguese.
These hacker help-wanted ads are appearing on underground Internet channels as malicious code designers increasingly want programmers with foreign-language skills to help launch country-specific attacks, security vendor McAfee Inc. said in a report released today.
Hackers want to craft compelling and grammatically correct Web pages and spam e-mails - which are crucial in fooling people to download viruses or reveal personal information like credit card numbers, according to the report.
More
here.
U.S. Security Concerns Scuttle Bain/Huawei Bid for 3Com
Grant Gross writes on InfoWorld:
A deal for Bain Capital Partners and China's Huawei Technologies to buy 3Com is on hold because the companies were unable to come to agreement with the U.S. Committee on Foreign Investment in the United States (CFIUS) about security concerns.
The three companies have withdrawn their joint filing with CFIUS, although they remain committed to continued discussions, they announced Wednesday.
Among the critics of the deal was U.S. Representative Thaddeus McCotter, a Michigan Republican. Huawei's stake in 3Com, which markets intrusion detection systems, would "gravely compromise" U.S. national security, he said in a House floor speech in October. The U.S. Department of Defense uses 3Com intrusion detection products, and Chinese hackers have targeted the agency, McCotter said.
More
here.
U.S. Navy Destroys Crippled Spy Satellite
An AP newswire article by Robert Burns, via MSNBC, reports that:
The Defense Department shot down a dying and potentially deadly U.S. spy satellite, using a high-tech missile fired from a ship in the Pacific.
The timing was tricky. For the best chance to succeed, the military awaited a combination of favorable factors: steady seas around the Navy cruiser that would fire the missile, optimum positioning of the satellite as it passed in polar orbit and the readiness of an array of space- and ground-based sensors to help cue the missile and track the results.
More
here.
Rogue Spy Satellite's Rotten, $10 Billion Legacy
Noah Shachtman writes on Danger Room:
That satellite that's due to be shot down this week was bad news, even before it got off the ground. The failed orbiter, USA-193, is widely believed to be part of a classified surveillance in space program known as Future Imagery Architecture, or FIA.
And FIA is known as one of the biggest defense-technology boondoggles in recent history -- "perhaps the most spectacular and expensive failure in the 50-year history of American spy satellite projects," The New York Times once wrote.
More
here.
UK Government 'Lost' DNA Data Disc On 2,000 Criminal Suspects
Siobhan Chapman writes on ComputerWorld UK:
The government is being urged to explain why a data disc, containing DNA profiles of 2,000 offenders whom the Dutch authorities wished to trace had been missing for almost a year.
The latest data controversy to hit the government came about after the Dutch authorities tried to track down 2,000 Dutch citizens who were on the run after committing serious crimes. In January 2007, they sent a disc containing the DNA samples of the offenders to Britain's Crown Prosecution Service (CPS) to be checked against the national DNA database.
But, the disc was not acted upon and possibly mislaid for a year before being found and sent to the National Policing Improvement Agency (NPIA), the overseer of the DNA database. The checks started this month and 15 matches have been found, including 11 who have committed further crimes in Britain during the past year.
More
here.
March Rollout for FBI's Data Sharing System
Wilson P. Dizard III writes on GCN.com:
The FBI's Criminal Justice Information Service (CJIS) plans to launch the first increment of its National Data Exchange (N-Dex) law enforcement information sharing system March 19, according to program manager Kevin Reid.
Speaking to GCN this afternoon in a telephone interview, Reid said that CJIS and the N-Dex vendor, Raytheon Intelligence and Information Systems, expected to bring in the first increment of N-Dex at a cost of about $41 million—approximately $3 million less than the project budget specified.
Raytheon won the N-Dex contract in February 2007. At the time, the FBI and Raytheon said they expected to complete the first increment by the end of this month.
The first increment of the system will include the features that CJIS' user community specified as the most urgently needed capabilities, including the ability to capture incident and case reporting data and to conduct "entity resolution" on the information.
More
here.
Security Experts Doubt UK Can Tackle e-Crime
Tom Young writes on Computing:
Not a single member of the UK’s largest group of IT security professionals believes the country is adequately equipped to deal with electronic crime.
And nearly two-thirds (65 per cent) of Information Systems Security Association (ISSA) members believe the current situation is wholly inadequate.
The results are a strong message to the government, said ISSA president Geoff Harris.
“As increasing numbers of the criminal fraternity become aware of the weakness in UK law enforcement capability, the gap between safe online e-commerce and e-crime will continue to spiral out of control,” he said.
In April 2006, the former National Hi-Tech Crime Unit (NHTCU) was absorbed by the newly created Serious Organised Crime Agency (SOCA).
SOCA claims that staffing levels and commitment to tackling e-crime have remained the same, but businesses have been highly critical of the organisation’s lack of performance.
More
here.
DoS Attack Prevents Access to WordPress.com Blogs
Elizabeth Montalbano writes on InfoWorld:
The WordPress.com blog-hosting service suffered a DoS (denial-of-service) attack that began Saturday and was still preventing users from logging in or posting to their blogs on Tuesday.
Matt Mullenweg, spokesman for Automattic, confirmed that the service experienced a DoS attack with spikes of up to 6 gigabits of incoming traffic, which was making some blogs inaccessible for about five to 15 minutes on Tuesday. Though service had mostly been restored, Automattic, which maintains WordPress.com, was still working on returning service to normal levels on Tuesday afternoon, he said.
"Obviously that [is not good] and is pretty unusual for our service," he said. "All our people who can are working on the issue."
More
here.
Got Malware? Now You Can Bank Online Anyway
Liam Tung writes on ZDNet.com.au:
The CSIRO has developed a tool it says will prevent criminals snooping on online communications, but hacking experts say the system is not foolproof.
The tool, dubbed the Trust Extension Device (TED), developed by the government research body, is a set of software tools loaded on to a portable storage device, which the CSIRO claims will allow online banking customers to create a quarantined desktop environment on computers that have been compromised by trojans, viruses or other malware.
More
here.
Experian Sues LifeLock, Alleges Fraud
Bob Sullivan writes on the MSNBC "The Red Tape Chronicles" Blog:
Credit bureau Experian is suing the identity theft prevention firm LifeLock, accusing it of deception and fraud in its familiar advertising campaign, which includes a spot in which CEO Todd Davis reveals his Social Security number and then brags about the effectiveness of the company’s protections.
In the lawsuit, filed in U.S. District Court on Feb. 13, Experian contends that LifeLock's advertising is misleading and that the firm is breaking federal law in the way it goes about protecting consumers.
LifeLock CEO Davis, in an interview with msnbc.com on Wednesday, called the lawsuit is baseless and said that Experian is simply upset that his firm is challenging its business model.
"This lawsuit is not about helping consumers," he said. "They just want to make more money selling their data."
More
here.
Toon of The Day: Dear Mr. Spam Filter...

We love Mr. Fish.
- ferg
Black Hat: Security Researchers Claim To Hack GSM Calls
J. Nicholas Hoover writes on InformationWeek:
Security researchers presenting Wednesday at the Black Hat D.C. conference in Washington, D.C., demonstrated technology in development that they say will be able to greatly decrease the time and money required to decrypt, and therefore snoop on, phone and text message conversations taking place on GSM networks.
Many mobile operators worldwide use GSM networks, including T-Mobile and AT&T in the United States. The 64-bit encryption method used by GSM, known as A5/1, was first cracked in theory about 10 years ago, and researchers David Hulton and Steve, who declined to give his last name, said today that expensive equipment to help people crack the encryption has been available online for about 5 years.
More
here.
U.S.Government Falling Short On Cyber Crime
Dennis Fisher writes on SearchSecurity.com:
The federal government is falling farther and farther behind its fight against cybercrime and, despite an increase in the amount of resources being allocated to address the problem, it will continue to struggle without a lot of help from law enforcement agencies at the state, local and international levels, current and former government security officials say.
Currently, the vast majority of the work being done on cybercrime and national computer security issues is done at the federal level by agencies as diverse as the FBI, Treasury Department, Department of Homeland Security and Department of State. And while these agencies all have teams of highly trained security professionals, the sheer volume of investigations that they're asked either to run or assist with far outweighs the amount of time, money and personnel available.
Jerry Dixon, former executive director of the National Cyber Security Division at DHS and current vice president for government relations for Infragard's National Member Alliance, said in a keynote speech at the Black Hat D.C. conference here Wednesday that the only way to help stem this tide is with a big shift in the way that lower-level law enforcement agencies deal with computer security cases.
"We need more trained law enforcement personnel at the state and local level," he said. "The feds are swamped. We need a tiered approach."
More
here.
SecureWorks: Linux Kernel Vmsplice Vulnerability
Sean Caulfield writes on the SecureWorks Research Blog:
I spent some time this week analyzing the recently disclosed vulnerability in the Linux kernel syscall, vmsplice. Several POC’s have been released and I was curious as to how they exploited the kernel.
Background on the vulnerability: the vmsplice function is a system call that allows a programmer to map an I/O vector (basically, an array of buffers) to a pipe.
The kernel adjudicates the whole transaction, dutifully mapping/copying the user specified memory to the pipe’s buffers or vice versa.
The trouble is that the routine for sys_vmsplice didn’t follow best practices for kernel programming and check the pointers passed from userspace for validity.” In at least three places in fs/splice.c, data in the user-specified iov array was copied to or from without verifying it’s validity via access_ok().
More
here.
Additional background
here.
-ferg
RBNExploit: Russian Hosting Network Running a Protection Racket
Gregg Keizer writes on ComputerWorld:
The Russian Business Network, a notorious hacker and malware hosting network, runs a protection racket that extorts as much as $2,000 a month in fees for "protective Web services" from borderline sites, a researcher alleged today.
The RBNExploit blog -- which is authored by one or more anonymous researchers -- spelled out the racket run by the group, which is thought to be headquartered in St. Petersburg, Russia, and has been pegged by security professionals as a major source of malware and cybercriminal activity.
"The business model RBN uses is quite simple and effective," said a post published today on the blog. "Its affiliates and resellers comb various niche market forums and discussion areas for Web masters using or discussing protective web services, i.e. DDoS [Distributed Denial of Service] prevention. Carry out a DDoS attack on the Web site and then provide a third-party sales approach to the Web master to 'encourage' a sign-up for their DDoS prevention services."
The price for "protection:" $2,000 per month.
More
here.
Dallas Police Website Defaced
An AP newswire article, via The Houston Chronicle, reports that:
The Dallas Police Department Web site was shut down Monday night after a hacker took over the site with anti-American rants.
Whoever hacked into the site also posted a doctored photograph showing American troops watching over four people lined up against a wall.
Each of the four prisoners had lines leading away from their faces to individual head shots of President Bush, Vice President Dick Cheney, Secretary of State Condoleezza Rice and Sen. John McCain, the Republican presidential contender, Dallas-Fort Worth TV station KTVT reported.
"My understanding is that no internal police data has been affected," said Lt. Vernon Hale, a police spokesman.
Hale said the department's technology staff will work to get the site back up. He said he was unaware of hackers ever taking over the site before.
More
here.
Analysis: Terrorist Use of The Internet
Shaun Waterman writes for UPI:
Lawmakers in the United States and elsewhere should not to try to censor Islamic extremists' use of the Internet, says a new report from a global think tank.
"There is no censorship option," Greg Austin, vice president of the East West Institute, told United Press International. "Trying to suppress anything (on the Internet) except direct operational use by terrorists is a mistake."
Austin said a careful distinction had to be drawn between extremist sites "advocating violent ideologies or asserting the right to use violence in general" and terrorist sites that "call for or support specific terrorist attacks."
The report urges that, rather than try to close extremists sites, the private sector and religious and community groups should step up, countering extremists' propaganda strategy with messages that promote peaceful dialogue and emphasize the human cost of extremist violence.
More
here.
Undersea Cables May Have Been Cut By Saboteurs
Via The National Terror Alert Response Center.
Damage to several undersea telecom cables that caused outages across the Middle East and Asia could have been an act of sabotage, the International Telecommunication Union said on Monday.
“We do not want to preempt the results of ongoing investigations, but we do not rule out that a deliberate act of sabotage caused the damage to the undersea cables over two weeks ago,” the UN agency’s head of development, Sami al-Murshed, said.
More
here.
Note: I'm not quite sure how I fell about posting this information, since I feel that the accuracy of it might be highly suspect, if not completely disingenuous. In any event, I present it here for your perusal.
Plus, my previous experiences of working with the ITU has been quite negative in the past -- they do not seem to have a firm grasp of reality.
-ferg
New Zealand: Banks Suppress Info About Security of Online Banking
Via Stuff.co.nz.
New Zealand's mainstream banks have suppressed information about the level of concern about the security of online banking.
Polling company Neilsen, which conducts surveys for the Bankers' Association, today published a news release showing the uptake of online banking, but when asked about security questions, spokesman Donald Sheppard said banks didn't want that information released.
"The banks we work with didn't really want that going to press because it's a little bit of a can of worms for them," he told NZPA.
"People are naturally concerned about online banking and that kind of thing and there's been a lot of info in the press about all these scams and phishing and all of that.
"We do monitor it... but our clients are the four main banks and they didn't want that going out into the public arena because they didn't want another song and dance about that," he said.
More
here.
Note: I can't image why people might be
concerned?
-ferg
CSRF Exploits Could Tarnish Forensics
Dennis Fisher writes on SearchSecurity.com:
Web application vulnerabilities have gotten more than their fair share of attention in the last few years, especially the widespread problem of cross-site scripting. But another flaw that many security experts consider a disaster waiting to happen is proving to be a serious problem for law enforcement agents and forensics investigators.
Known as cross-site request forgery (CSRF), the vulnerability often is used by attackers to force a victim into unknowingly submitting requests to third-party Web sites. In this way, an attacker could force a user to retrieve images, submit or retrieve data or perform any number of other functions on a site, which can seriously muddy the waters when an investigator is trying to trace a user's online actions. Experts say this is becoming an increasingly common problem in cases in which someone is accused of downloading illicit material or taking other illegal actions online.
"I see this in a lot of cases where the defendant definitely could say that it was CSRF," said Chuck Willis, a principal consultant at Mandiant in Alexandria, Va., and a former special agent in U.S. Army Counterintelligence. "It's a problem for forensics people who aren't as familiar with it and might not understand whether it's possible that CSRF could be blamed for what the defendant is accused of."
More
here.
Australia Becomes The Latest to Consider Forcing ISPs to Police Internet Traffic
Heath Gilmore and Kerrie Armstrong writes on The Sydney Morning Herald:
As the internet threatens to kill the established music industry, the Rudd Government is considering a three-strikes policy against computer users who download songs illegally.
The Government will examine new legislative proposals being unveiled in Britain this week to target people who download films and music illegally. Internet service providers (ISPs) there might be legally required to take action against users who access pirated material.
More
here.
U.S. Army: Wikis Too Risky
David Axe writes on Danger Room:
They might not build $150-million F-22 stealth fighters, but in other ways insurgents and terrorists are amazingly tech savvy. For one, they're hip to using grungy, bare-bones websites to spread tactics and ideology across the planet on the cheap, transforming once-isolated local and regional conflicts into genuine threats to global stability. Author John Robb calls this "open-source warfare," and believes it's the most important force shaping the 21st century.
If so, we're screwed. Seven years after the launch of Wikipedia -- the user-edited online encyclopedia that brought the "open source" concept to the masses -- the U.S. Army is still playing catch-up. The Army's idea of harnessing the 'net is to launch isolated websites, put generals in charge and lock everything behind passwords, while banning popular open-source civilian websites. Colonel James Galvin, head of the Army's "Battle Command Knowledge System," openly admits that when it comes to the collaborative internet, the bad guys have a "niche advantage."
More
here.
Wikileaks.org Ordered Offline by California Court - UPDATE
Via The BBC.
A controversial website that allows whistle-blowers to anonymously post government and corporate documents has been taken offline in the US.
Wikileaks.org, as it is known, was cut off from the internet following a California court ruling, the site says.
The case was brought by a Swiss bank after "several hundred" documents were posted about its offshore activities.
Other versions of the pages, hosted in countries such as Belgium and India, can still be accessed.
However, the main site was taken offline after the court ordered that Dynadot, which controls the site's domain name, should remove all traces of wikileaks from its servers.
The court also ordered that Dynadot should "prevent the domain name from resolving to the wikileaks.org website or any other website or server other than a blank park page, until further order of this Court."
More
here.
UPDATE: 14:31 PST: As Mike Masnick
points out, you can still reach the Wikileaks website if you know the
IP address.
-ferg
Programming Note: NANOG 42

I'll be attending NANOG 42 here in San Jose over the course of the next few days, so posts to the blog may be somewhat sporadic...
Thanks!
- ferg
U.S. Toll in Iraq

Via The Boston Globe (AP).
As of Sunday, Feb. 17, 2008, at least 3,963 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes eight military civilians. At least 3,225 died as a result of hostile action, according to the military's numbers.
The AP count is three higher than the Defense Department's tally, last updated Friday at 10 a.m. EST.
More
here.
And as always, the
Iraq Coalition Casualty Count keeps the grim watch on their website
here.
Honor the Fallen.
Cartoon of The Day: Congressional Circus
Click for larger image.
Via Truthdig.com.
UK: 3 Internet Providers in Deal for Targeted Ads
Eric Pfanner writes in The New York Times:
For years, Internet service providers have watched with envy as the likes of Google, Yahoo and Microsoft sliced up the online advertising pie. Selling Internet access has been a good business, but selling Web advertising has been an even more lucrative one.
Now, three Internet providers in Britain have teamed up to try to obtain a piece of online advertising for themselves. The three companies — BT, Carphone Warehouse and Virgin Media — announced a deal last week with a company called Phorm, whose technology tracks Web users and sends them ads related to their interests.
Phorm said it would set up a new online advertising platform called the Open Internet Exchange, which any Web site would be allowed to join. Proceeds from ads shown on these publishers’ sites will be shared with BT, Carphone Warehouse and Virgin Media, which together represent more than two-thirds of Britain’s Internet access market.
More
here.
New Zealand: ASB Bank to Review Net Fraud Liability
Via Stuff.co.nz.
ASB Bank will decide this month whether to back down on its hardline stance over customer liability for Internet banking fraud.
Since July, ASB's 550,000 Internet banking customers have been liable for losses from phishing attacks and other fraud if they use computers without up- to-date anti-virus and firewall software and operating systems.
Spokeswoman Debby Bell says the bank has in the past always reimbursed fraud victims who weren't running up- to-date software, but it won't guarantee it will do this.
ASB will release updated terms and conditions for Internet banking towards the end of this month, she says.
More
here.