Particle Accelerator Used to Decipher Text
Alex Dominguez (AP) writes via ABC News:
A particle accelerator is being used to reveal the long-lost writings of the Greek mathematician Archimedes, work hidden for centuries after a Christian monk wrote over it in the Middle Ages.
Highly focused X-rays produced at the Stanford Linear Accelerator Center were used last week to begin deciphering the parts of the 174-page text that have not yet been revealed. The X-rays cause iron in the hidden ink to glow.
MPAA Blames BitTorrent for Star Wars Distribution
Over on /.
Posted by timothy on Saturday May 21, @06:18PM
from the what-do-you-burn-apart-from-witches? dept.
AI Playground writes "Slyck News reports on the MPAA's press release (.doc) blaming the BitTorrent protocol for the leak of Episode III. MPAA President and CEO Dan Glickman: 'There is no better example of how theft dims the magic of the movies for everyone than this report today regarding BitTorrent providing users with illegal copies of Revenge of the Sith. The unfortunate fact is this type of theft happens on a regular basis on peer to peer networks all over the world.'"
Hacking the Grid
Via Red Herring.
Security experts warn it wouldn’t be hard for a cyberpunk or terrorist to turn off the lights in a large portion of the U.S. (First of three parts.)
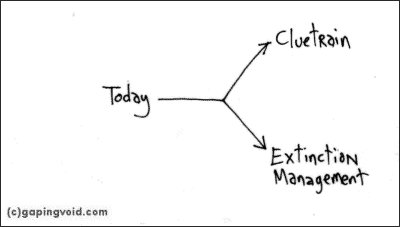
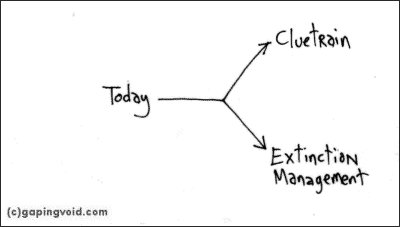
Our grandparents had Laurel and Hardy
Via gapingvoid.
ISP, Enterprise Data Concerns Merge at ISPCon
Caron Carlson writes on eWeek:
With the bright line between enterprise network access and end-user Internet access fast fading, vendors are reaching out to service providers and enterprises to address growing concerns about security, reliability and bandwidth use and to encourage improved network management.
Who Really DDOS'd SCO - No, *Not* the Linux Community
Via Groklaw.
Finally, the truth comes out. The Linux Community had nothing to do with the MyDoom attack on SCO. If you want to know who did it, read Business Week's account about "Hacker Hunters" and their roundup of criminal gangs.
Firefox 1.0.3 exploits released
FrSIRT has released 3 exploits against Firefox 1.03; If you haven't upgraded to 1.04 (or Netscape 8.0.1), this is yet another good reason to do so without delay.
Vonage given stick to beat BT
Peter Jidge writes on TechWorld.com:
Voice-over-IP (VoIP) provider Vonage has launched in the UK, with full approval from Ofcom to offer stiff competition to BT.
"We will offer call quality as good or better than BT," said chief executive Jeffrey Citron, at the London launch. The £9.99-a-month flat rate service allows customers to use any existing phone, which they plug into a Vonage-enabled broadband router. Calls are then free, except international calls and calls to mobiles. The Linksys-made routers will be available from Staples for about £25.
Vonage staff said that Ofcom had welcomed its arrival in the UK, and had gone to some lengths to allow it to make its service (which has been in tests in the UK since January) competitive. For instance, customers will be allowed to keep their Vonage number when they move house, severing the geographical link between dialling code and area. If a customer gets a "London" number, they call and receive calls on that London number, whether their router is connected to the Net in London or Cardiff.
Report: Internet Retail Sales Up 24 Pct.
An AP newswire report on Yahoo! News:
First-quarter retail Internet sales rose 23.8 percent to $19.8 billion in the United States from $16 billion a year ago, according to preliminary numbers released Friday by the Department of Commerce.
E-commerce sales during the first quarter rose 6.4 percent from the fourth quarter, when they were $18.6 billion.
Iowa Mother Helps Nap Internet Predator
An AP newswire article on ABC News:
A mother posed as her daughter on the Internet and helped police nab a man who was trying to solicit the 14-year-old for sex, authorities said.
Richard H. Johanson, 36, of Short Hills, N.J., was being held Saturday in the Hancock County jail. He has been charged with attempted third-degree sexual abuse and enticing away a minor.
Cox Broadband Blacks Out
Colin C. Haley writes on internetnews.com:
More than 2 million Cox Communications broadband customers lost their connections Friday after the cable operator's Internet backbone went down, a spokesman for the Atlanta company confirmed.
"We're still investigating the root cause of the problem," Bobby Amirshahi, a Cox spokesman, told internetnews.com.
Amirshahi said the outage affected all of Cox's broadband customers -- both consumers and businesses.
In some markets, service was restored in 30 minutes, he said. However, one Cox customer in Orange County, Calif., reported that his firm's service had been dark for two hours.
Service has now been restored to all customers, Amirshahi said. The company will gather information on what caused the problem over the next few hours.
Aggressive, Mass-Mailed Sober.p Worm Poised To Smack Users
Gregg Keizer writes on TechWeb News:
Monday may be a very bad day, a security researcher said Friday as he warned that the aggressive Sober worm of early May is timed to download new code the first day of next workweek.
Sober.p, the mass-mailed worm that spread voraciously by virtue of its offer of free World Cup tickets, is poised to launch another attack Monday, said Dmitri Alperovitch, a research engineer with an Alpharetta, Ga.-based security firm CipherTrust.
"At the moment, the payload is unknown, but it may be another form of spam, like Sober.q; more malicious code, like another virus; or a denial-of-service attack."
Deleting Emails Costs Morgan Stanley $1.45B
Shamelessly lifted from /.
Posted by Zonk on Friday May 20, @05:55PM
from the that-was-important-and-i-forgot-it dept.
DoubleWhopper writes "The financial giant Morgan Stanley lost a $1.45 billion judgement yesterday due, in part, to their failure to retain old email. The judge in the case, 'frustrated at Morgan Stanley's repeated failure to provide [the plaintiff's] attorneys with e-mails, handed down a pretrial ruling that effectively found the bank had conspired to defraud' their former client. The CEO of a record retention software company noted, 'Morgan Stanley is going to be a harbinger'."
Nintendo @ E3 - DSpeak: VoIP via Nintendo DS
Via Engadget.
This is still just a concept demo, but it’s reportedly a working demo: DSpeak is basically Voice over IP calling using the wireless capabilities of the Nintendo DS. Using a connected headphone/microphone, DSpeak allows you to hold conversations with other DS users via WiFi, and the audio quality is reportedly “perfectly fine, as good as a mobile phone.” Plus, you get little Mario and Wario icons moving their mouths when you speak — come on, Vonage, how you gonna beat that? The software itself will be available as a free download, and the booth boy told us that they’ll be including headsets with DSpeak-compatible games (the headset will probably also be available for sale separately for some nominal fee). Otherwise that’s about all we know—we couldn’t squeeze a release date out of them, and no one at the Nintendo booth knew a damn thing about the actual technology they were demoing.
Analysts expect massive HP layoffs
Stephen Shankland writes over on C|Net News:
Hewlett-Packard is likely to lay off thousands more employees, financial analysts have projected after new Chief Executive Mark Hurd presented his inaugural assessment of quarterly earnings.
Hurd didn't reveal specific layoff plans after the earnings report, but he did make clear HP's intent to cut expenses and said his company has "a cost structure that is off benchmark in many areas." Now the analysts are weighing in with their assessments of the printer and computer maker's future.
Time Warner CEO: no AOL spinoff for now
A Dow Jones newswire article on CNN/Money:
Time Warner Inc. Chairman and Chief Executive Dick Parsons said the media conglomerate recently considered spinning off America Online but decided such a move was unnecessary for now.
At the company's annual shareholder meeting, Parsons told investors that executives had considered spinning off the unit as a separately traded stock to create a currency for the unit to make acquisitions.
The move would have been similar to the company's planned spinoff of its cable-television unit following the completion of its acquisition of Adelphia Communications Corp., he said.
But AOL management deemed the move was unnecessary "at this point in time," he said.
Update: 802.11n Debate Remains Unresolved
Mark Hachman writes in ExtremeTech:
Having failed to secure enough votes for standards approval, the debate over which proposal to back for the next-generation 802.11n standard moves back to square one.
At an IEEE meeting in Cairns, Australia, the TGn Sync proposal failed to win the 75 percent approval that it required to become the draft 802.11n standard. According to the IEEE's bylaws, the lack of compromise means that the TGn Sync as well as the opposing WWiSE proposal must now be reconsidered, most probably to enact a merged standard.
Apple Patches Widget Malware Hole in Tiger
Ian Betteridge writes in eWeek:
Apple Computer Inc. has quietly patched several security holes in Mac OS X 10.4, also known as "Tiger," including one that allows potentially malicious widgets to be downloaded and installed into Dashboard.
The security patches were released as part of an OS X 10.4.1 update earlier this week, but the company has only just released details of them. The update patches four security holes, the most well-known of which is the problem where widgets—small applications working in the software's Dashboard system—could be downloaded and installed without any specific user confirmation. Under 10.4.1, automatic installation of Widgets is blocked, and users must specifically approve the installation of each Widget.
Cisco tips hand on new business unit
Martin LaMonica writes on C|Net News:
Cisco Systems gave a peek at the work going on in its new business unit this week, signaling the company's push to drive sales of its networking gear.
Taf Anthias, vice president and general manager of Cisco's AON business unit, demonstrated two Cisco devices under development at SAP's customer conference here Thursday.
AON stands for application-oriented networking, which is one of Cisco's initiatives to add more "intelligence" to its networking gear, Anthias said. Industry executives have said that products from the AON business will compete with existing makers of XML processing hardware products.
Another Sober Variant Set To Hit In Germany
An AP newswire story on Security Pipeline:
German officials warned Friday of a new variation of a computer virus that in the past has sent out far right-wing spam e-mails.
The so-called "Sober.p'' virus is expected to start infecting computers on Monday based on analyses of the virus's source code, the Bonn-based Federal Office for Information Technology Security said.
The expected effects are unclear, but Internet users should update their virus protection software, spokesman Michael Dickopf said.
The bug is a variant of the Sober virus family that first appeared on the Internet in October 2003. It is a "Trojan horse,'' a hacker back door, that can be used to turn victims' PCs into relayers of spam e-mail.
Last week, another variant of the virus hit the United States, Germany, and elsewhere, sending out a blast of e-mails with subject lines in German such as "60 years of Freedom: Who's Celebrating?'' referring to the end of World War II, and containing links to the NPD, a German far-right party.
U.S. to Unveil Web Site on Sex Offenders
An AP newswire report on Yahoo! News:
State-by-state information on sex offenders will be available on a new Internet site run by the federal government, Attorney General Alberto Gonzales announced Friday.
Participation by states is voluntary, and the Justice Department said it hopes to have the site up and running within two months.
The announcement was being made to coincide with National Missing Children's Day.
The site won't provide any information not already made available on the Internet by 48 states, the District of Columbia and U.S. territories. But it will be designed to allow someone to do a national search to determine whether an individual who has been convicted in one state has moved to another.
Nortel taps IBM for R&D assistance
Via Reuters.
Communications equipment maker Nortel Networks Corp. is set to announce on Friday plans to work with IBM on research and development, helping Nortel to cut costs and marking a victory for IBM as it pushes into contract engineering services.
Executives from Brampton, Ontario-based Nortel and IBM of Armonk, New York, said they are setting up a joint research and development center in Research Triangle Park, North Carolina, where both have large, established research operations.
Financial terms were not disclosed.
BitTorrent enemies face new hurdle
Renai LeMay writes on C|Net News:
Antipiracy operatives have lost an edge over illegal downloaders of movies and software thanks to a new feature in BitTorrent.
BitTorrent creator Bram Cohen has eliminated the need for Web site hosting of centralized files, known as "trackers," in the latest beta of the peer-to-peer software. These easily located files have been a key resource for antipiracy units in identifying people downloading and sharing copyrighted material.
The change may cause problems in shutting down the illegal online distribution of software and content, according to the Business Software Alliance, an industry group.
Vonage UK opens for business
Tony Smith writes in The Register:
US-based VoIP call company Vonage formally set up shop in the UK today, moving its no-time-limit call package for £10 a month out of the testing phase it's been in since January.
The tenner, paid up front by rolling credit-card billing, gives you free calls to other Vonage users and to landlines in the UK and the Republic of Ireland. Calls to mobile phones are priced at 5-15p a minute, depending on whether you call at weekends, in the evening or during working days.
Revealed: the Australian patent the Wi-Fi giants want to squash
Peter Judge writes in Techworld.com:
Some of the biggest names in the wireless industry are taking legal action against claims that the Australian government owns patents for basic wireless LAN technology.
Microsoft, Dell, HP, Intel, Apple and Netgear, wish to nullify a patent held by the Australian government research body, the Commonwealth Scientific and Industrial Research Organization (CSIRO), that apparently covers all IEEE 802.11 wireless LAN equipment.
"The patent is considered essential for implementing wireless local area networks that comply with several IEEE standards, and is now a standard feature of most notebook computers and many other devices," said a CSIRO release, in which the organisation promises to defend itself.
New super-safe Netscape squashed by bugs
Matthew Broersma writes in Techworld.com:
Netscape has published a security update to its Netscape 8 browser fixing more than 40 security holes, just hours after the browser's official launch.
Version 8 of the browser is the first major update to the browser since 2002 and includes a number of new security features designed to protect users from remote attacks and malicious websites. It is based on the increasingly popular open-source Firefox browser, but didn't include any of the security patches released in Firefox 1.0.4.
"The browser is like a hybrid car that combines the usability of Internet Explorer with the security of Firefox," Andrew Weinstein, a spokesman for AOL/Netscape, told Reuters. Critics have pointed out however that the initial release combines the security vulnerabilities of both browsers.
The unpatched vulnerabilities - fixed in Firefox back in March - include a bug in the handling of gif images that could allow an attacker to run malicious code on a user's system. The vulnerability could be exploited by, for example, luring users to a site displaying specially crafted images.
The unpatched holes led to the release of Netscape 8.0.1 a few hours after the release of version 8.0. The update includes the Firefox 1.0.4 security fixes, according to Netscape. Netscape's advisory is available here.
Lycos Germany will no longer store dynamic IP address info
Jan Libbenga writes in The Register:
Lycos DSL in Germany says it will no longer store dynamic IP addresses of its customers, now that a specialist on data privacy laws from Frankfurt University has threatened to sue the company.
Jonas Breyer had asked Lycos what data was kept on him and whether that information was shared with backbone providers, but the ISP refused to co-operate. Probably to avoid further law suits, Lycos has now decided to ditch IP storage altogether.
Microsoft UK recruits FBI man
John Leyden writes in The Register:
Microsoft has head-hunted a senior legal officer from the FBI to become its chief security advisor in the UK. Ed Gibson joins Microsoft in July from the FBI, where he has held senior positions as a special agent for 20 years. Since 2000, he has served as the FBI’s assistant legal attaché in the UK, where he has been responsible for establishing intelligence alliances between UK police agencies, security services, the FBI and private sector companies.
Phone-Cable TV Battle Heats Up In Texas
An AP newswire article in Advanced IP Pipeline got my attention this evening, since it involved issues here in Texas (and I can tell ya, we've been seeing our share of special interest group commercials):
A bill that would make it easier for companies such as SBC and Verizon to sell TV service over their lines into their customers' homes was stalled in the Texas legislature on Wednesday.
The issue has turned into one of the biggest business issues facing House lawmakers this session, pitting telephone companies against the cable industry. Both sides pushed advertisements on TV and in the newspapers, claiming they were siding with consumers.
LexisNexis Hacking Probe Examined
An AP newswire article by Mark Sherman appearing on Yahoo! News:
Federal agents have carried out searches in at least two states as part of the investigation of the theft of Social Secuity numbers and other personal information from database giant LexisNexis Inc.
Secret Service and FBI agents executed search warrants in Minnesota, while FBI agents conducted 10 searches in northern California, federal law enforcement officials said Thursday.
"It's definitely the LexisNexis case," Mike Brooks, an FBI spokesman in Ohio, said about the searches in Minnesota.
No arrests have been made in conection with the searches, which were carried out in recent days.
Dayton-based LexisNexis declined to comment Thursday. Secret Service officials did not immediately provide comment.
Update: John Murrell writes on "Good Morning, Silicon Valley" that it's no coincidence--this is related to the Paris Hilton incident. Read: "Devious data thieves actually joy-riding script kiddies."
House Elevates Cyber Czar Position
Gregg Keizer writes for TechWeb News:
The House late Wednesday passed a $34 billion budget for the Department of Homeland Security that among its provisions, would elevate the nation's head cybersecurity official to Assistant Secretary status, a move that's been urged by security industry leaders for almost a year.
By a vote of 424 to 4, the House passed H.R. 1817, the "Department of Homeland Security Authorization Act," a $34.2 billion budget for Homeland Security in 2006.
Among the bill's provisions is one that would elevate the head of the National Cyber Security Davison (NCSD) to Assistant Secretary level.
"PH"BI (FBI) phishing
The good folks over at the Internt Storm Center (ISC) report in their Daily Incident Handler's Diary today:
"PH"BI (FBI) phishing
One contributor submitted information on a hack involving a php flame module ending in a phishing scam. According to the submission he was notified that a co-worker "was looking at a notice claiming to be from the FBI that they were monitoring this range of IP addresses for suspicious activity regarding financial transactions" and sure enough at the end of the phish you were asked "that you re-enter your payment data to help them track the fraudsters." The site was reported to dish up the phish intermittently "as you could hit reload 10 times before it appears again". According to the contributor "The correct URL always appeared unchanged in the browser's address bar, but the content I was looking at was nowhere in the actual documentroot directory for that domain." The contributor asked for some assistance, and any contributor who cares to toss out recommendations on security issues related to "any configuration settings that would disallow modules from being loaded" will be thanked and I'll pass them on to the person who reported this "PH"BI (FBI) phish.
Caspian Networks raises big money
Matt Marshall posts on SiliconBeat:
We were asked to hold this until Monday, but the cat is (partly) out of the bag, since PE Week mentions it today in its wire (no link today, it's broken).
PE didn't get the full news though. It reporting that Caspian Networks, the next generation San Jose router company, raised $31.4 million, according to a regulatory filing it found. But the real number is actually way higher -- which perhaps PE missed by reporting early.
Caspian has raised a huge amount of money over the years, including a $120 million in 2002, but it is now finally getting traction. We'll drag the cat out entirely on Monday, including how it is taking on Cisco and Juniper in some cutting-edge areas...
Google announces personalized home page
An AP newswire article on Yahoo! News reports:
Web search leader Google Inc. on Thursday introduced a personalized Google home page, moving in a direction rivals such as Yahoo Inc. and Microsoft Corp.'s MSN portal have already been moving in.
The personalized Google home page integrates other already available Google features, such as its e-mail service Gmail, news, weather, stocks, driving directions, movie listings and the like.
Engineering groups call for visa reform
Via EE Times.
Engineering and scientific groups are joining forces to reform the U.S. visa system used to attract researchers, scholars and foreign students.
Forty engineering, scientific and academic associations unveiled recommendations on Thursday (May 19) for fixing the U.S. visa system. They also urged the Bush administration to accelerate effort to reform the system.
Among the groups backing the recommnedations are the International Society of Optical Engineering (SPIE), the National Academy of Sciences and the American Association of the Advancement of Science.
Flight Security Plan Still Hasn't Taken Off
An AP newswire story on Security Pipeline reports:
The government is three months late in coming up with a plan ordered by Congress to avoid diverting international flights because of concerns about their passengers.
Twice in the past week, Boston-bound planes from Europe were diverted from their destinations when a passenger's name was found to be similar to a name on the "no-fly list'' of people considered threats to aviation.
US Census Bureau halts Internet 'phishing' scam
An AFP newswire story on Yahoo! News reports:
The U.S. Census Bureau said it was able to shut down a scam using e-mails directing people to a fake website in a bid to collect credit card numbers.
The scam, known in the Internet field as "phishing," began with e-mails offering a five-dollar cash reward to participate in a bogus online "Operation Iraqi Freedom 2005 Survey."
The e-mail included a link that took users to a "spoof" or fake Web page that appeared to be the official Census Bureau Internet site, where they were asked to answer questions and then provide their bank card number and authorization code to receive the reward.
The Census Bureau said the site was shut down Wednesday, within hours of the first reports, and that the FBI was investigating.
China hires 'cyber-agents' to control public opinion on the Internet
Via AFP newswire story on Yahoo! News:
The Chinese government has started using "cyber-agents" to spread positive political messages on the Internet and better control public opinion, state media reported.
Several cities have set up special "online propaganda troops" who pose as ordinary Internet users in chatrooms and other cyber-forums as they spread favorable spin for the government, the Southern Weekend newspaper said.
SBC, BellSouth, Vonage Pen 911 Deal
Well, today seems to be the day for VoIP news.
Ed Oswald writes in BetaNews:
Vonage on Thursday announced that it had signed deals with SBC and BellSouth to provide enhanced 911 services to its customers in three out of four major service areas of the the two companies. The talks had been ongoing since April. This comes before an expected ruling on Thursday by the FCC to force traditional and VoIP phone companies to work together within a certain period of time or face possible sanctions.
Vonage penned a deal with Verizon on May 4 that will give it access to enhanced 911 services across the phone providers coverage area.
Congress pushes 911 mandate on VoIP
Declan McCullagh writes on C|Net News:
Internet telephone companies would be required to link up to the emergency 911 network, according to a new bill in Congress.
The 10-page measure, which has been introduced in both the Senate and House of Representatives, also would permit state and local governments to levy taxes on voice over Internet Protocol (VoIP) companies in exchange for providing access to 911 operators.
The timing of the bill--it was made public hours before a Federal Communications Commission meeting devoted to Internet 911 regulations--effectively ratcheted up pressure on the commission to move in a specific direction.
Revenge of the Sith leaked online
Via The BBC.
The final Star Wars film has been leaked on to an internet file-sharing network just hours after the movie opened in cinemas.
A "work print copy" of Star Wars: Episode III - Revenge of the Sith with a time code, rather than the finished version, appeared online on Thursday.
A tracker site showed more than 16,000 people were downloading the film.
Also, see Boing Boing: "Star Wars III online, all studio countermeasures futile, Lucas still rich"
Interest In IPv6 Found To Be Lagging
No big surprises here....
Matthew Friedman writes in Networking Pipeline:
Although it has been in the work for a decade, the next-generation Internet protocol IPv6 has failed to excite the interest of key decision makers in the federal government and private sector, according to a survey by equipment vendor Juniper Networks.
Juniper's Federal IPv6 IQ Study found that less than 7% of respondents consider IPv6 "very important to achieving their IT goals," despite the fact that the protocol is designed to address, among other things, many of the quality of service, security, and network management issues that concern them. The Federal government is particularly indifferent to IPv6 and lags well-behind the private sector in migration planning and awareness.
VoIP operators given 120-day deadline to implement E911 services
An AP newswire article by David Pace on Yahoo! News:
Federal regulators voted Thursday to require that Internet phone service providers connect their customers to the same emergency 911 capabilities as callers with traditional service within four months.
The Federal Communications Commission left it to the providers to determine how to meet the new requirement for the service, known as Voice Over Internet Protocol.
The 4-0 vote came after FCC Chairman Kevin J. Martin invited families impacted by the inability to reach emergency response centers over Internet phones to tell their stories. A Florida woman described how her infant daughter died while she was unable to reach an emergency dispatcher through her Internet phone.
"By moving quickly, we will save lives," said Commissioner Michael J. Copps.
Popular Japanese Web site hard hit by major hack
Via InfoWorld.
Japan's largest price comparison Web portal, Kakaku.com, said Trojan horse programs were installed on the company's servers during an unauthorized intrusion on May 11. The company detected the intrusion soon after it occurred. Instead of closing the site, Kakaku.com decided to keep it open until May 14 in an attempt to trace the hack, company president Yoshiteru Akita said at a news conference in Tokyo Wednesday. The Trojan programs have been identified as "trojandownloader.small.AAO" and "PSW.Delf.FZ," and can affect PCs running Windows 95, 98, ME, XP, 2000, and NT operating systems, Kakaku.com said. Delf is a Trojan program that installs a keystroke logger and remote control software. The programs record all keystrokes made on an infected PC. If a PC gets hit and the user logs into a server, the attacker can get the user's password for the server and access the user's account. The company said the site wouldn't be back in operation until May 23 at the earliest.
MSN Gets Ready for RSS Push
Matt Hicks writes in eWeek:
Vowing to make RSS friendly to the everyday Web user, an MSN executive demonstrated upcoming services on Wednesday that build syndication feeds into the messaging alerts, a Windows screen saver and Web search.
During a keynote at the Syndicate Conference here, MSN Director Phil Holden said that Microsoft Corp's Internet division is taking RSS (Really Simple Syndication) seriously and will integrate the technology across even more of MSN's online services throughout the year.
VDSL2: 100 Mbps over Copper next...
As a residential DSL subscriber, this is exciting. But as someone who has worked in the service provider space, this article and associated references doesn't mention much about the cost of forklift upgrades, ISP ROI, connectivity bandwidth planning, and time-to-market issues -- these are very important when it comes to actual deployment.
It does leave one to imagine, however, how this plays into the overall schemes of FTTH, which would inavriably deliver the same amount of bandwidth.
Om Malik posts on his Broadband Blog:
Very High Bit Rate DSL 2 (VDSL2), a new standard is likely to be ratified by next week, making it possible for carriers to provide upto 100 megabits per second connections (both up and down) over copper lines. VDSL2 standard has been under review with the International Telecommunications Union for sometime now, and the decision on the standard could come early next week.
Online Vigilantes Fight Back Against Phishing Fraudsters
Oh, this is great -- ya gotta see these screen captures. :-)
Courtesy of Netcraft.
As fraudsters continue to target their victims with increasingly elaborate phishing sites, the surprise appearance of anti-phishing vigilantes is now hampering their operations.
Cisco Vulnerability in a Variant of the TCP Timestamps Option
Cisco yesterday reported a vulnerability with some implementations of the Transmission Control Protocol (TCP) Timestamps option (RFC1323) are vulnerable to a Denial of Service (DoS) attack from specifically crafted packets. Cisco also states that only certain implementations of the TCP Timestamps option are vulnerable.
The entire security alert can be found here.
China hits net gambling hard
Tim Richardson writes on The Register:
More than 1,300 people have been detained in Shanghai after Chinese authorities continued to clampdown on internet gambling.
Two of those arrested on Tuesday were on a national list of "most wanted" and collared in connection with running online gambling services. Net cafes, night-clubs and homes were raided as part of the crackdown, reported Xinhua Online.
Netflix Takes Over Wal-Mart DVD Rentals
An AP newswire article by Michael Liedtke on Yahoo! News:
Wal-Mart Stores Inc. is turning over its online DVD rental business to Netflix Inc., signaling that the world's largest retailer couldn't beat the Internet upstart at its own game.
Netscape 8.0 released
Well, it's here!
The Netscape 8.0 Browser has a bunch of new features, including warning you if you come across possible spyware sites, tabbed browsing (actually, nothing new here), a toggle which allows switching between Mozilla and Microsoft's rendering engines as needed, and a new "passcard manager" to remember all your screen names and passwords and auto-fill that information on sites.
Actor Freeman warns film industry of piracy threat
It would appear, at first blush, that having to go to the WIPO Arbitration and Mediation Center to get a domain-squatter to relinquish control of www.morganfreeman.com has perhaps given Morgan Freeman a highly biased view of DRM issues in cyberspace (see: Freeman Wins Rights to Name in Cyberspace).
Mike Collett-White writes for Reuters:
With high-speed Internet connections on the upswing, piracy could hit the movie industry as hard as it did the music business, Hollywood actor Morgan Freeman warned.
Freeman is telling movie makers that they must wise up quickly to stay ahead of illegal downloaders and file sharers who are using new software and high-speed broadband connections.
Platform Shift Will Knock 40K BofA Customers Offline
Clint Boulton writes on internetnews.com:
The Bank of America (BofA) is steeling itself and potentially irate customers for a computer system changeover that will render some 40,000 accounts inaccessible via online banking, ATM card access and automated phone.
The lockdown will begin June 16 and extend to July 25, cutting off Northeast customers who rely on computerized banking through the fourth of July holiday. Customers will be able to make payments, withdrawals and other transactions by going to a BofA branch, or by speaking to a BofA customer service representative over the phone.
Calling the transition an "unfortunate necessity," BofA spokesman Ernesto Anguilla said the bank expected the online service disruption and sent very specific letters to customers who will be affected.
New TCP/IP Flaw Haunts Windows
Ryan Naraine writes in eWeek:
Microsoft on Wednesday issued a prepatch advisory to counter the publication of exploit code for a newly discovered vulnerability in its implementation of TCP/IP.
The Redmond, Wash., company's confirmation of the flaw is the first public test of the software giant's new security advisories pilot project, which is meant to provide instant feedback, guidance and mitigations when third-party researchers release vulnerability details and exploits before a patch is available.
VeriSign buys RFID consulting boutique
Well, this is interesting......
Alorie Gilbert writes in C|Net News:
VeriSign has purchased technology consulting firm R4 Global Solutions for $15 million, expanding its presence in the emerging radio-frequency identification market.
The company completed the all-cash deal on Wednesday. It expects the transaction to be neutral to its earnings per share for the year.
R4 Global Solutions has 26 employees with headquarters in San Francisco. It specializes in helping businesses use RFID technology to monitor their supplies and prevent inventory snags.
U.S. taps Entrust for e-passports
Alorie Gilbert writes in C|Net News:
The U.S. State Department is assembling the technology for the new e-passport, selecting tools from Entrust to help ensure the authenticity of the next-generation document.
The contract, which Entrust announced on Wednesday, calls on the Dallas company to supply a key component in a government plan to introduce new U.S. passports this year. The passports will contain an identification chip, and the State Department will use Entrust software to stamp each ID chip with a tamper-proof digital code, or digital signature, the company said.
Netscape ready to launch antiphishing browser
Joris Evers writes over on C|Net News:
Netscape is expected to release on Thursday the final version of Netscape 8, a Web browser designed to protect users against online scams such as phishing.
Early test versions of the new browser--so-called alpha and beta releases--have been available since February. Netscape has promised that the final version, like the previous ones, will include features to better safeguard systems while people surf the Web. Netscape 8 is also expected to have a cleaner look and feel, but not to be dramatically different from the public beta released in March.
Enterprise Employees Clueless About Phishing
Gregg Keizer writes in TechWeb News:
Enterprise employees are at a much bigger risk from phishing attacks than they think, according to a survey conducted by pollster Harris Interactive. In fact, a huger majority don't even know what phishing is, said the poll's sponsor, San Diego-based Websense on Wednesday.
The survey of 500 American workers and more than 350 IT decision makers pointed out a major disconnect between what employees think they're doing, and what their companies' IT staff sees them doing, said Dan Hubbard, the senior director of security and technology research at Web security and content filtering firm Websense.
Bogus Microsoft Security Update Circulates
Via TechWeb News.
Hackers again tried to bamboozle Windows users with bogus e-mails purporting to contain a comprehensive update to Internet Explorer, Outlook Express, and Outlook.
The newest e-mails--a sample which TechWeb received--play off the recent news that Microsoft released its May patch, a tactic so common that scams like this appear virtually every month.
"This is the latest version of security update, the 'May 2005, Cumulative Patch' update which resolves all known security vulnerabilities affecting MS Internet Explorer, MS Outlook and MS Outlook Express," the official-looking e-mail reads.
Astute recipients will know that Microsoft did release a patch in May, but only for a bug in Windows 2000, not IE or Redmond's e-mail clients.
Users who click on the Download Update link embedded in the e-mail will be infected with the Pinfi virus, and an as-yet-undetermined Trojan horse.
Government says Wi-Fi networks not secure
Via Reuters.
A hacker on a park bench could log onto dozens of U.S. government computer networks thanks to slipshod security standards at many agencies, according to a congressional report released on Tuesday.
The report by the Government Accountability Office found that few government agencies can ensure that their wireless networks are protected from unauthorized access.
Experts Debate Internet Security
Michael Cohn writes in InternetWeek:
A recent hacker attack that compromised some of the crucial equipment powering the Internet has sparked a debate on whether the stolen Cisco Systems code used to penetrate the complex systems still poses a threat to the web.
Experts have argued for years whether software that has its source code freely distributed is more, or less, secure than proprietary applications. Code for the open-source Linux operating system, for example, is available to anyone, and many experts argue that makes it more secure than Microsoft's proprietary Windows.
Silex Releases USB Server For Sharing USB Devices On LANs
Hey, this is pretty cool....
Matthew Friedman writes in Networking Pipeline:
Silex Technology America Inc. has unveiled a universal serial bus (USB) device server that will allow small business and home users to share USB 2.0 Hi-Speed devices such as scanners, printers and external hard drives over a local area network (LAN).
The SX-2000U2 is a one port, 10/100 Base-TX USB 2.0 device server that instantly converts USB 2.0 Hi-Speed devices into shared network resources. When connected, USB devices appear and function as locally connected devices to any system on the LAN. The SX-2000U2 provides IP filtering for enhanced security and is compatible with both Windows XP and Windows 2000. The unit includes the SX Virtual Link utility, which allows users to manage all of the networked USB devices on the LAN in a single window.
The most accurate clock of all time
Paul Marks writes in a Special Report from the New Scientist Print Edition:
IF TIME waits for no man, then neither does human ingenuity in measuring its passing.
Throughout history, more stable and accurate clocks have led to advances in communications and navigation. Now a clock 1000 times more accurate than any of its predecessors has set another benchmark, and could even be used to create a more precise definition of how long a second is.
The new clock is a variant on the atomic clocks that appeared in the 1950s. Atomic clocks usually work by measuring the frequency at which atoms resonate. For instance, the outer electrons of a caesium-133 atom resonate between two energy states exactly 9,192,631,770 times each second, emitting microwaves of exactly that frequency as they do so. This property has been used since 1967 to define what we mean by 1 second - it is officially the time it takes for a caesium atom to resonate 9,192,631,770 times.
Personal Data for the Taking
Tom Zeller Jr. writes in the New York Times:
Senator Ted Stevens wanted to know just how much the Internet had turned private lives into open books. So the senator, a Republican from Alaska and the chairman of the Senate Commerce Committee, instructed his staff to steal his identity.
"I regret to say they were successful," the senator reported at a hearing he held last week on data theft.
Latvian police bust alleged software counterfeiting ring
An AFP newswire article on Yahoo! News:
A branch of the Latvian police set up to track down high-tech counterfeiters has arrested two people and shut down an operation that allegedly made and sold millions of pirated copies of Microsoft software.
The illegal business had been operating for several years and caused losses to the US software producer of about 3.0 million dollars (two million euros), police spokeswoman Kristine Mezaraupe said Wedesday.
Yahoo's 'Voice Over IM' Targets Skype
Exactly what I was thinking. :-)
Ryan Naraine writes in eWeek:
Looking to cash in on the growing buzz around PC-to-PC voice over IP services, Yahoo on Wednesday added voice calling capabilities to a new beta of its instant messaging client.
The Yahoo Messenger makeover puts the Sunnyvale, Calif.-based Web portal up against startups Skype Technologies S.A. and Teleo Inc., two companies that have found success by offering IM and voice connection services from a downloadable application.
NIST tackles measurement
Florence Olsen writes on FCW.com:
The National Institute of Standards and Technology will lead a series of workshops this year to gather information for improving the nation's measurement capabilities in critical areas such as broadband communications, data storage technologies and new health care and homeland security technologies.
The initiative, announced last week, will help the agency uncover new measurement needs and set 21st century priorities, said NIST spokesman Mark Bello. NIST will host a U.S. Measurement Summit in early 2006, which will provide a venue for discussing how to address the nation’s new measurement priorities.
Porn Valley Goes Blogging
A fascinating article about the Blogging in the Porn Industry.
Susannah Breslin writes in Wired News:
On the long list of things the world needs now, more sex talk on the internet is probably a no-show. Still, as porn becomes ever more inescapable, a growing line of aficionados and insiders have stepped forward with detailed behind-the-scenes accounts of the industry -- capped by the recent documentary Inside Deep Throat, a look at one of the most notorious porn flicks of all time.
Porn stars, porn gossip scribes and porn production workers are turning to blogs to expose what it's really like to live and work in the San Fernando Valley-based sex industry.
Microsoft to offer checkout software for retailers
Somehow, I can't help but imagine that there will be several interpretations for the acronym, "POS"...
Via Reuters.
Microsoft Corp., the world's largest software maker, said on Wednesday it would launch new software for small retail stores that allows owners to replace cash registers and automate sales and inventory management.
Microsoft Point of Sale, which will be offered from June, is part of Microsoft's push to sell more software to small- and mid-sized businesses.
Can telecoms wring profit from enterprise IP?
This is indeed an interesting conundrum for IP services--although they seem to be extremely popular, there is a question on their profitability.
Marguerite Reardon writes on C|Net News:
This is an era of mixed blessings for two of the nation's biggest phone companies.
AT&T and MCI not only are grappling with the mix of promise and regulatory issues associated with their respective acquisitions by SBC and Verizon, they are finding it difficult to make money off some of their fastest-growing IP services.
At the heart of the problem are the relatively thin profit margins on the telcos' sales of enterprise-data IP services such as Internet protocol virtual private networks (IP VPNs). The remedy, experts say, is fairly straightforward but not necessarily easy to implement: The phone companies need to develop and sell more add-on IP VPN products and services to boost their returns.
Online stores come under attack
Mark Ward writes for The BBC:
Cyber criminals are turning their attention to the programs that run many online shops, say experts.
The move to target the databases and programs that power online shops is a significant change in tactics.
In one case, an attacker got hold of a PC maker's entire customer list and sent everyone on it a nasty note.
"It's kind of like an arms race. It's the next logical step to go after the application itself," said Rob Straight from software firm Compuware.
Insurgents Post Sniper Training Exercises Online
In an ABC News Exclusive:
Web sites maintained by Iraqi insurgents and their supporters contain chilling instructions that tell recruits how to become snipers and how to inflict the maximum damage, ABC News has learned.
A Defense Department document is being disseminated to U.S. commanders in Iraq to inform them about the insurgency's newest tactic, ABC News has learned.
Release of Honeywall CDROM 'Roo'
In addition to the "KYE: Phishing" paper:
The Honeynet Project and Research Alliance are excited to announce the release of our new Honeywall CDROM 'Roo'. The purpose of the new CDROM is to make honeynets easier to deploy, maintain, and analyze. This new version has been redesigned from the ground up and represents the latest in our GenIII (third generation) technologies.
New features include:
- Automated, headless installation to your local hard drive.
- Robust, hardened OS base that includes automated updates of OS and Honeywall packages.
- Vastly improved hardware and international keyboard support.
- New GUI "Walleye" for remote administration and robust, real time data analysis.
- Optional command-line tool 'hwctl' for administration.
- Integration of the new Sebek format, 3.x.
- Designed as a distributed solution.
You can download the new GenIII Honeywall CDROM Roo and find the Online User Manual at:
http://www.honeynet.org/tools/cdrom/
In addition, we have released a KYE paper that gives you an overview of the history, design and future of the Honeywall CDROM Roo. You can find this at:
KYE: Honeywall CDROM Roo
http://www.honeynet.org/papers/cdrom
Know Your Enemy: Phishing
Lance Spitzner dropped me a line last night to notify me of their latest paper, "Know Your Enemy: Phishing; Behind the Scenes of Phishing Attacks", which he, and the other fine folks over at the Honeynet Project and Research Alliance, just published. It's definately worth a read.
Lance explains, "What makes this paper new/different is that it focuses on behind the scenes of how attackers build, use and maintain their infrastructure of hacked systems. Its based on data collected in the UK and Germany, and is similar in technical detail to our previous Botnet paper."
A brief excerpt:
Phishing is the practice of sending out fake emails, or spam, written to appear as if they have been sent by banks or other reputable organisations, with the intent of luring the recipient into revealing sensitive information such as usernames, passwords, account IDs, ATM PINs or credit card details. Typically, phishing attacks will direct the recipient to a web page designed to mimic a target organisation's own visual identity and to harvest the user's personal information, often leaving the victim unaware of the attack. Obtaining this type of personal data is attractive to blackhats because it allows an attacker to impersonate their victims and make fraudulent financial transactions. Victims often suffer significant financial losses or have their entire identity stolen, usually for criminal purposes. This KYE white paper aims to provide practical information on the practice of phishing and draws on data collected by the German Honeynet Project and UK Honeynet Project. This paper focuses on real world incidents that the Honeynet Project has observed in the wild, but does not cover all possible phishing methods or techniques. Attackers are constantly innovating and advancing, and there are likely to be new phishing techniques already under development or in use today.
Thanks, Lance!
Microsoft looks to "monkeys" to find Web threats
Robert Lemos writes on SecurityFocus:
Researchers for the software giant are building a system of Windows XP clients that crawl the web finding sites that use unreported vulnerabilities to compromise unsuspecting users.
Researchers at Microsoft are creating their own version of a million monkeys to crawl the internet looking for threats in an effort to secure the web for Windows.
The software giant's Cybersecurity and Systems Management (CSM) research group are building a system of virtual Windows XP computers that crawl the web looking for sites that use unreported vulnerabilities to compromise customer's PCs. Dubbed "honeymonkeys," the virtual machines run a full version of Windows XP with monitoring software and crawl high-risk areas of the web looking for trouble.
Washington State Outlaws Spyware
Shamelessly snipped from /.
Posted by timothy on Tuesday May 17, @06:11PM
from the good-luck-with-all-that dept.
An anonymous reader submits "Today, the Governor of Washington signs a a bill outlawing spyware (bill history) which imposes penalties of $100,000 per violation. Spyware is broadly defined. It includes everything from changing a browser's bookmarks or homepage settings, "Opening multiple, sequential, stand-alone advertisements in the owner or operator's internet browser", keystroke-logging, taking over control of the computer, modify its security settings, and even "Falsely representing that computer software has been disabled." But here is my favorite: "Prevent, through intentionally deceptive means, an owner or operator's reasonable efforts to block the installation or execution of, or to disable, computer software by causing the software that the owner or operator has properly removed or disabled automatically to reinstall or reactivate on the computer." Microsoft and Ebay both testified in support of the bill. On May 10th, a similar law banning Internet and email phishing was also passed."
Unhappy and indebted workers
Ed Frauenheim writes over on the C|Net Workplace Blog:
The American worker today: more disgruntled, deeper in debt.
At least that's the portrait that emerges from a couple of recent reports. The first, an essay by consultant Tony DiRomualdo, discusses a conference titled the World Congress on the Future of Work. The prevailing view of attendees at this April forum was that the workplace is not a better and more fulfilling place than it was 10 years ago, he writes.
"Today, the majority of workers still go to offices every day even though information and communications technology increasingly allows them to work from anywhere," DiRomualdo says. "They still work in facilities that are designed to minimize operating costs and preserve hierarchy and status, not inspire creativity and fuel collaboration among workers."
Swindle: 'Somebody Has Got to Pay'
Roy Mark writes on internetnews.com:
Corporate America is acting irresponsibly in protecting consumer data, Orson Swindle of the Federal Trade Commission (FTC) said today. The payback for that irresponsibility, he predicted, will be painful.
In impromptu comments made during a think-tank panel discussion on international cyber crime, Swindle, a Republican FTC commissioner, took broad swipes at both private enterprise and Congress for their efforts on consumer data protection.
"Everybody's screaming, all the political figures up on [Capitol] Hill, about identity theft," he said. "It's not identity theft, it's the theft of information."
And, he added, in today's global, digital marketplace, that information is currency.
Secret Service head calls for cybersecurity cooperation
Grant Gross (IDG News Service) writes in InfoWorld:
Companies with compromised data have a duty to report that information to investigators as a way to keep others from being victimized, the director of the U.S. Secret Service said Tuesday.
The Secret Service, which has jurisdiction to investigate financial crimes as well as protect the U.S. president, is working hard to prevent Internet-related crimes such as identity theft, but it needs assistance from private companies, said Ralph Basham, Secret Service director, speaking at an event on organized cybercrime in Washington, D.C.
Why workers sabotage office computers
An AP newswire article on MSNBC reveals that:
Corporate insiders who sabotage computers so sensitive they risk endangering national security or the economy commonly are motivated by revenge against their bosses, according to a government study released Monday.
The study, paid for by the Department of Homeland Security, examined dozens of computer-sabotage cases over six years to determine what motivates trusted insiders to attack and how their actions damage the country's most sensitive networks and data.
Update: John Paczkowski writes today over on Good Morning, Silicon Valley:
Timothy Lloyd would probably be the first person to tell you: Don't mess with a network administrator. Lloyd, an employee of high-tech measurement and instrumentation manufacturer Omega Engineering was convicted in May 2000 of planting the logic bomb that destroyed the company's manufacturing programs. The attack, inspired by Lloyd's demotion after 11 years as the Omega's chief programmer, cost the company millions of dollars and some 80 employees their jobs. Today, it figures prominently in a study by the U.S. Secret Service and CERT that found that employees who sabotage corporate networks often do so because they're angry at their bosses. According to Threat Study: Computer System Sabotage in Critical Infrastructure Sectors, 84 percent of the forty-nine instances of network sabotage it examined were motivated by a desire to seek revenge. Said Dawn Cappelli, senior member of the technical staff with CERT: "The power of a terminated employee with system administrator access should not be underestimated."
DOD Takes Bids for Spyware Contract
Paul F. Roberts writes over on eWeek:
The U.S. Department of Defense is soliciting bids for a massive anti-spyware software contract that will protect systems across the military.
The deal could be a major opportunity for anti-spyware startups to score a victory against established anti-virus vendors.
The solicitation from the DISA (Defense Information Systems Agency) is for an automated spyware detection, eradication and protection technology, referred to as SDEP.
FCC set to require 911 services for VoIP
Jeremy Pelofsky writes for Reuters:
Internet telephone providers will soon have to offer full emergency 911 calling services under an order U.S. regulators are expected to adopt Thursday in response to incidents of customers having trouble getting help.
Internet calls, known as Voice over Internet Protocol (VOIP), are sent over a high-speed Internet connection but they do not always provide 911 response centers with the caller's address and often they are routed to administrative lines.
With pressure from state law enforcement agencies and Congress, the U.S. Federal Communications Commission plans to require VOIP companies to provide 911 services to customers within 120 days of its order being published, two officials familiar with the FCC plan said.
New Microsoft Security Toolkit to Take Aim at Shared-Computer Users
Mary Jo Foley writes in Microsoft Watch:
Microsoft is readying a new security tool to add to its arsenal.
The newest member of Microsoft's growing security-focused product family is the "Microsoft Shared Computer Toolkit for Windows XP," according to beta testers who requested anonymity.
The toolkit, which is currently in private beta test, is designed for users who are sharing computers in businesses and homes. It is especially focused on users of shared computers in libraries, cafés, schools and other similar environments, testers said.
Base closings hit Army IT
Frank Tiboni writes on FCW.com:
The Defense Department has recommended closing a New Jersey base that has housed many of the Army's warfighting and business information technology organizations.
Fort Monmouth, N.J., houses the Communications-Electronics Life Cycle Management Command, which oversees development and acquisition of the Army’s warfighting IT and intelligence, surveillance and reconnaissance systems. The site also contains some offices of the Program Executive Office for Enterprise Information Systems, which manages the service's procurement and implementation of business IT systems. The Army Small Computer Program Office, for example, resides at Fort Monmouth.