UK: Ministry of Justice Loses 45,000 Personal Records
Kevin Dowling writes on The Times Online:
The Government’s reputation for protecting people’s sensitive electronic data has been dealt yet another blow with the revelation that the Ministry of Justice (MoJ) lost the records of 45,000 people.
The information included dates of birth, national insurance numbers, criminal records, and in a single incident, the loss of bank details and other information belonging to 27,000 people working for suppliers to the department.
In another case, officials lost an “inadequately protected” laptop storing the job applications of 13 people who were applying for judicial positions with the service.
The revelations in the department’s annual accounts come after similar blunders saw two CDs with the child benefit records of 25 million families lost in the post and the loss of 658 laptops by the Ministry of Defence.
More
here.
Hat-tip: Pogo Was Right
Wyoming Teen Pleads Guilty to Computer Crime - Created Nugache Worm
Via LocalNews8.com (AP).
A 19-year-old Wyoming resident has pleaded guilty to a felony charge related to the development of a program that took over thousands of computers nationwide to steal credit card information.
Jason Milmont of Cheyenne pleaded guilty Wednesday in a Casper federal courtroom to a charge of unauthorized access to a computer to conduct fraud.
Milmont faces up to five years in prison for the charge. The U.S. Attorney's Office says Milmont has already agreed to pay more than $73,000 in restitution.
According to prosecutors, Milmont developed a malicious computer code called the Nugache Worm, a modification of "peer-to-peer" software.
More
here.
U.S. May Ease Police Spy Rules
Spencer S. Hsu and Carrie Johnson write in The Washington Post:
The Justice Department has proposed a new domestic spying measure that would make it easier for state and local police to collect intelligence about Americans, share the sensitive data with federal agencies and retain it for at least 10 years.
The proposed changes would revise the federal government's rules for police intelligence-gathering for the first time since 1993 and would apply to any of the nation's 18,000 state and local police agencies that receive roughly $1.6 billion each year in federal grants.
Quietly unveiled late last month, the proposal is part of a flurry of domestic intelligence changes issued and planned by the Bush administration in its waning months. They include a recent executive order that guides the reorganization of federal spy agencies and a pending Justice Department overhaul of FBI procedures for gathering intelligence and investigating terrorism cases within U.S. borders.
Taken together, critics in Congress and elsewhere say, the moves are intended to lock in policies for Bush's successor and to enshrine controversial post-Sept. 11 approaches that some say have fed the greatest expansion of executive authority since the Watergate era.
More
here.
U.S. Toll in Iraq, Afghanistan

Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Friday, Aug. 15, 2008, at least 4,143 members of the U.S. military have died in the Iraq war since it began in March 2003, according to an Associated Press count.
The figure includes eight military civilians killed in action. At least 3,368 died as a result of hostile action, according to the military's numbers.
The AP count is one fewer than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
As of Friday, Aug. 15, 2008, at least 500 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Sunday at 10 a.m. EDT.
Of those, the military reports 355 were killed by hostile action.
More
here and
here.
And as always, the
Iraq Coalition Casualty Count keeps the grim watch on their website
here.
Honor the Fallen.
UK: Government Admits National DNA Database Holds Records of 40,000 Innocent Children
Ian Drury writes on The Mail Online:
Nearly 40,000 innocent children have been placed on the Government's enormous DNA database for life, ministers admitted last night.
The number of ten to 17-year-olds who have done nothing wrong yet have had their genetic profiles seized by police has soared by 60 per cent in two years.
The news will fuel mounting fears that forces are arresting youngsters who have committed no crime simply to build up their DNA database by 'stealth'.
More
here.
Defense Tech: Inside the Cyber Command Turf Battle

Via Defense Tech.
Reports by the Associated Press who obtained a memo on the subject said this week the Pentagon delayed and may even kill the Air Force's planned Cyberspace Command. Why exactly is up for speculation, but according to one insider who absolutely did not want to be identified - "It's a dollar Grab".
The insider went on to say that "with an estimated $30 billion being spent on cyber capabilities, who can blame them?"
As I tally it, the Army, Air Force, CIA, NSA, DIA, DHS, StratCom and two unidentified black-ops units have already begun developing cyber warfare capabilities. Anyone with an ounce of sense would not want to get in the middle of that group! The Pentagon has to be thinking it would be better to have one unified cyber command rather than all these dispirit efforts.
Cyber warfare is a highly desirable command area -- it is new, it's exciting, it's a real threat and arguably the hottest topic in military circles. Multiple security experts, including myself, have warned that significant and very special resources and expertise are required to execute the core elements of the Bush administration's cyber security plan.
More
here.
Image source: DefenseTech.org / Kevin Coleman
Hacker Reportedly Kidnaps and Tortures Informant, Posts Picture as a Warning to Others
Kevin Poulsen writes on Threat Level:
A Turkish computer hacker who was helping that country's media and national police investigate computer crimes was kidnapped and tortured by a notorious ATM hacker, according to a report from the Turkish press.
The victim, known online as "Kier," had been leaking information to Turkish reporters about an underground figure called Cha0, when he briefly disappeared. He resurfaced in May, and described being abducted and beaten by Cha0 and his henchmen.
More
here.
U.S. Unprepared For Cyber Attack as Russia-Georgia Online War Rages
A Cox News Service article by David Ho, via The Austin American-Statesman, reports that:
As Russia and Georgia teeter between cease-fire and war, combat is still raging in cyberspace with hackers continuing an onslaught against Georgian Web sites, e-mail and communication services.
About 20 government, banking and media sites were offline Thursday, said Scott Borg, director of the U.S. Cyber Consequences Unit, an independent research group that advises the government. Some sites have fled to hosting computers in other countries and even to Atlanta, where they continue to take digital fire.
The disruptions have played a significant role in the conflict, impairing Georgia's ability to respond to Russia's military attacks, Borg said.
The ongoing online battle, which appears to have begun before the first shots were fired, is a preview of a new era in warfare — one the United States is not ready for, government officials and security experts say.
More
here.
Toon of The Day: Soul Food

Enjoy.
- ferg
Quote of The Day: Jeffrey Carr
"Memo to Dancho Danchev: Stop looking at Estonia for answers. Look at Chechnya."
- Jeffrey Carr, writing on IntelFusion, regarding the "behind the scenes" puppetry of the ongoing Georgian cyber attacks. Jeff and I agree. So does Don Jackson at SecureWorks...
'How I Joined Russia's Cyber War' + Commentary
Noah Shachtman writes on Danger Room:
Evgeny Morozov has written perhaps the smartest story yet on the online conflict between Russia and Georgia:
"Not knowing exactly how to sign up for a cyberwar, I started with an extensive survey of the Russian blogosphere. ...As I learned from this blog post... all I needed to do was to save a copy of a certain Web page to my hard drive and then open it in my browser..."
More
here.
Note: Let's be clear here -- there had been, and continues to be, grass-roots hacktivist attacks against Georgian web properties. But let's also be clear that
other forces are also clearly at work here, and were in play long before this became a hacktivist issue.
Anyone suggesting that this is not the case is clearly naive.
-ferg
Cyber Attacks on Georgian Websites Are Reigniting a Washington Debate
Siobhan Gorman writes on The Wall Street Journal:
The cyberattacks in Georgia are re-energizing a debate over whether the laws of war apply in cyberspace. Among the biggest questions: When is a cyberattack an act of war?
As Russia continued military actions inside Georgia, in apparent violation of a Tuesday cease-fire agreement, some Georgian government Web sites, including the president's office, remained under attack.
Cyberweapons are becoming a staple of war. The Georgian conflict is perhaps the first time they have been used alongside conventional military action. Governments and private cyberwarriors can exploit Internet security gaps to not only take down government Web sites but also take control of power grids and nuclear reactors.
U.S. officials have begun to consider the legal and policy problems that cyberwarfare presents, but cybersecurity experts said the government has been slow to resolve them in the face of an increasing likelihood that cyberattacks will be used to augment, or even supplant, typical military action.
More
here.
U.S.: Tracking Russia-Georgia Hostilities is 'Frustrating'
 A convoy of Russian troops makes its way through the Caucasus Mountains.
A convoy of Russian troops makes its way through the Caucasus Mountains.An AP newswire
article by Deb Riechmann, via
SFGate.com, reports that:
The White House grasp of developments in war-battered Georgia has been hampered by confusing reports from the ground and intelligence resources that initially were focused more on Iraq and Afghanistan than the former Soviet republic.
One-sided and possibly exaggerated accounts of actions from both sides and the Bush administration's difficulty in independently verifying information about the war have left the White House standing on an ever-changing platform from which to speak out on the crisis.
At least three times on Wednesday, President Bush referred to being concerned about "reports" that Russia had violated its pledge to a provisional cease-fire. White House press secretary Dana Perino hedged her answers to questions about the conflict, too.
More
here.
Image source: Dmitry Kostyukov/AFP/The Boston Globe
Documents Detailing Early Spy Network Released
 Julia Child
Julia ChildAn AP newswire
article, via
MSNBC.com, reports that:
Famed chef Julia Child shared a secret with Supreme Court Justice Arthur Goldberg and Chicago White Sox catcher Moe Berg at a time when the Nazis threatened the world.
They served in an international spy ring managed by the Office of Strategic Services, an early version of the CIA created in World War II by President Franklin Roosevelt.
The secret comes out Thursday, all of the names and previously classified files identifying nearly 24,000 spies who formed the first centralized intelligence effort by the United States. The National Archives, which this week released a list of the names found in the records, will make available for the first time all 750,000 pages identifying the vast spy network of military and civilian operatives.
More
here.
Russia's Chechen Model for its Georgia Cyber Attack
Via IntelFusion.
Cyber warfare as a military strategy is still in its infancy, and Western conceptions of just what cyber warfare is are in sharp contrast to that of Russia and China. In fact, just last year, General James Cartwright called the U.S. cyber warfare effort “dysfunctional“. And today, 18 months later, the USAF top leadership pulled the plug on its own 8th Air Force Cyber Command (h/t Danger Room), which is very interesting timing in light of Russia’s recent cyber and military attack against Georgia.
Unlike the U.S. effort, which is hugely complex, costly, and confusing, Russia has opted for a more efficient, low cost model that outsources the work to hacker groups like the Russian Business Network or the Eurasian Union of the Youth (ESM) who were responsible for last year’s cyber attack against the Ukrainian Security Service’s Web site.
While there isn’t unanimous consent among computer security firms and consultants that Russian hackers are working on behalf of the Federal Security Service (FSB), there is ample evidence to suggest that very thing.
More
here.
Mark Fiore: Private Contracting Games

More Mark Fiore brilliance.
Via Mother Jones.
Enjoy!
- ferg
AOL Phisher Gets Seven Year Sentence
Robert McMillan writes on PC World:
A West Haven, Connecticut, man has been sentenced to seven years in prison for masterminding a phishing scheme that targeted AOL users over a four-year period.
Michael Dolan, 24, was sentenced Wednesday in Connecticut federal court. The seven-year sentence was the maximum he could have received, said Assistant U.S. District Attorney Edward Chang, via e-mail. Dolan was also sentenced to three years' supervised release, and a US$200 special assessment, he added.
Last year Dolan pleaded guilty to fraud and aggravated identity theft charges.
More
here.
Security Researcher Asserts Russian Role in Georgia Cyber Attacks
Brian Prince writes on eWeek:
A security researcher claims to have uncovered evidence suggesting a link between the Russian government and the cyber-attacks launched against Georgia.
Don Jackson, director of threat intelligence at Atlanta-based SecureWorks, said in an interview with eWEEK there may have been multiple forces pulling the digital strings behind the attacks. According to Jackson, incident responders in Georgia supplied logs showing traffic to and from bots on their own networks with command and control IP addresses that are in ranges that belong to state-operated companies for which no previous record of activity of any kind exists.
“We know that the Russian government controls those servers theoretically, if they have not been pwned by somebody else,” he said.
According to SecureWorks, most of the changes in routing information that block traffic to Georgian IP address space were carried out by government-run ROSTELECOM and the Moscow-based COMSTAR network. Those networks were also the launch points for DDoS (distributed-denial-of-service) attacks and cache poisoning attempts targeting DNS servers for major Georgian networks as well, as were parts of Turkish networks controlled by members of the RBN.
More
here.
Security Researchers' Accounts Ransacked in Embarrasing 'Hacklash'
Dan Goodin writes on The Register:
On Sunday morning, security consultant Alan Schimel woke to discover that his personal blog, which is frequented by countless peers and reporters, was pointing to a website featuring explicit gay porn. Equally disturbing, he found someone had cracked open his Yahoo! Mail account and aired sensitive documents he filed with the Internal Revenue Service.
Oh, and while the miscreants were at it, they sent crude pornographic images to parents on the Little League baseball team Schimel coached.
The chief strategy officer for security firm StillSecure, Schimel is one of three high-profile researchers in the security world known to have been attacked by unknown criminals over the past week. A personal Gmail account belonging to Petko D. Petkov, of the GNUCitizen ethical hacking collective, was ransacked and 2GB of its contents made public. And logs believed to come from the home blog of Security-Protocols.com researcher Tom Ferris have also been exposed.
More
here.
Note: Actually,
pdp (Petko D. Petkov)
denies that his Gmail account was compromised.
-ferg
Experts Accuse Bush Administration of Foot-Dragging on DNS Security Hole
Ryan Singel writes on Threat Level:
Despite a recent high-profile vulnerability that showed the net could be hacked in minutes, the domain name system -- a key internet infrastructure -- continues to suffer from a serious security weakness, thanks to bureaucratic inertia at the U.S. government agency in charge, security experts say.
If the complicated politics of internet governance continue to get in the way of upgrading the security of the net's core technology, the internet could turn into a carnival house of mirrors, where no URL or e-mail address could be trusted to be genuine, according to Bill Woodcock, research director at the nonprofit Packet Clearing House.
"The National Telecommunications and Information Administration, an agency of the Department of Commerce, is the show-stopper here," Woodcock said.
More
here.
Cyber Attacks on Georgia's Websites Continue

Ben Bain writes on FCW.com:
As a shaky truce that halted the military conflict between Russia and Georgia took hold today, Georgia’s Internet infrastructure continued to be plagued by cyberattacks, according to observers who have been monitoring the attacks.
Today, more than 20 Georgian government Web sites, three commercial financial institutions and two media outlets remain off-line, said John Bumgarner, the research director for Security Technology at the U.S. Cyber Consequences Unit. He has been monitoring the situation from the United States. The US-CCU is an independent, nonprofit research institute, originally established at the request of senior U.S. government officials.
More
here.
DHS Awards $11.7M for Cyber Research
Alice Lipowicz writes on FCW.com:
The Homeland Security Department today awarded $11.7 million in grants for cybersecurity research to 13 recipients from industry and academia.
The department’s Science and Technology Directorate made some awards to focus research and development on botnets and malware, composable and scalable secure systems, cybersecurity metrics and data anonymization tools. Other awards will be used for research on insider threat detection and mitigation, Internet tomography and topography; network data visualization for information assurance; process control system security and routing security management tools, DHS said.
Some recipients are Applied Visions, Inc. of Northport, N.Y.; Computer Associates Inc. of Islandia, N..Y.; Colorado State University and Digital Bond Inc. of Fort Lauderdale, Fla. The others are Georgia Tech Research Corp.; IBM Corp.; ITT/Dolphin Technology; Johns Hopkins University; Packet Clearing House Inc.; Sandia National Laboratories; Secure64 Software Corp. of Greenwood Village, Colo.; the University of California-San Diego and Washington State University.
More
here.
Homeland Security Contractor Accused of 'Prolific' Child Porn
Freeman Klopott writes on Examiner.com:
A computer specialist for the Department of Homeland Security was arrested Thursday for being one the nation’s most prolific disseminators of child pornography.
After a months-long investigation, FBI agents tracked Peter W. North to his home in Alexandria where they discovered 80 gigabytes — the equivalent of 25,000 pictures or 250 hours of video on your iPod — of child pornography in an external hard drive, according to a sworn statement by FBI agent Chad J. Gallagher.
North had come to Gallagher’s attention after the agent reviewed a list of the “most prolific offerors of apparent child pornography in the United States” that had been pieced together by a Wyoming-based federal task force. Working with Comcast, North’s Internet provider, Gallagher was able to use an Internet Protocol address assigned to North to find his home.
More
here.
Hat-tip: Washington Technology
UK: £68M 'Snooping' Database Will Have Little Impact on Serious Crime
Nick Heath writes on Silicon.com:
Powers to snoop on the UK's email and internet records will be of limited use in tackling serious crime, the government has admitted.
Home Office proposals for phone, email and internet records - including VoIP - to be kept for 12 months are expected to cost taxpayers up to £68m to set up and £39m per year to run.
Consultation papers released this week show the government wants to keep the "who", "when" and "where" of communication to "assist in the investigation, detection and prosecution of serious crime".
But a spokeswoman for the Home Office admitted the proposals would be of restricted use against organised criminals or terrorist organisations, as they were likely to disguise their communications.
More
here.
Air Force Suspends Cyber Command Program
Bob Brewin writes on NextGov.com:
The Air Force on Monday suspended all efforts related to development of a program to become the dominant service in cyberspace, according to knowledgeable sources. Top Air Force officials put a halt to all activities related to the establishment of the Cyber Command, a provisional unit that is currently part of the 8th Air Force at Barksdale Air Force Base in Louisiana, sources told Nextgov.
An internal Air Force e-mail obtained by Nextgov said, “Transfers of manpower and resources, including activation and reassignment of units, shall be halted.” Establishment of the Cyber Command will be delayed until new senior Air Force leaders, including Chief of Staff Norton Schwartz, sworn in today, have time to make a final decision on the scope and mission of the command.
The Cyber Command, headed by Maj. Gen. William Lord, touted on its Web site its capabilities to “secure our nation by employing world-class cyberspace capabilities” and had ambitious plans to have a cyber command presence in all 50 states.
More
here.
Breaking: 3-Alarm Fire Burns At Apple Cupertino Campus
Via CBS5.com.
A three-alarm fire burned Tuesday night at the Apple campus in Cupertino, according to the Santa Clara County Fire Department.
The fire department received a report of smoke at about 10 p.m. at 20605 Valley Green Drive, at a building known as Valley Green 6.
No injuries are reported and the building was cleared, according to a fire dispatcher, who said that the fire department was not certain when the blaze would be under control.
More
here.
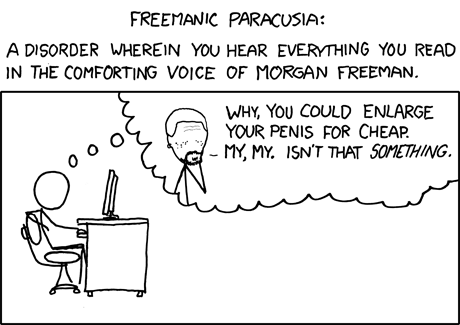
Classic xkcd: Freemanic Paracusia
Click for larger image.
Yes, we
love xkcd.
Enjoy!
- ferg
Indicted Federal Informant Allegedly Strong-Armed Hacker Into Caper That Drew 9-Year Sentence
Kevin Poulsen writes on Threat Level:
Four years after pleading guilty to an abortive scheme to steal customer credit card numbers from the Lowe's hardware chain, hacker Brian Salcedo learned from prison last week that a co-conspirator who pressured him to go through with the hack attack was working for the feds at the time.
Salcedo, 25, is serving a record-breaking nine-year prison term for a 2003 intrusion into Lowe's corporate network. Salcedo and another hacker had parked outside a Lowe's in Southfield, Michigan and tapped into the store's unsecured WiFi network. Over the course of weeks, they used their foothold to penetrate Lowe's servers at stores across the country, where they eventually planted software that would sniff and store customer credit card numbers as they flew from cash registers to a processing server in North Carolina.
The hackers' downfall was seemingly straightforward. According to court records, Lowe's detected an intrusion and called in the FBI, who staked out the Southfield store's parking lot and eyeballed Salcedo and his partner working from a Pontiac Grand Prix. Salcedo pleaded guilty without even looking at the thousands of pages of "discovery" in the case -- the government's evidence.
More
here.
U.S. Homeland Security Setting Up Counter-Intelligence Unit

An AP newswire article by Eileen Sullivan, via The Boston Globe, reports that:
Concerns about foreign spies and terrorists have prompted the Homeland Security Department to set up its own counterintelligence division and require strict reporting from employees about foreign travel, according to a memo obtained by The Associated Press.
The new directive comes as the federal government increases its counterspy efforts across all agencies and raises the awareness of intelligence vulnerabilities in the private industry as well as in protecting government secrets.
Homeland Security is creating a counterintelligence system now, because there is currently no place for such a function in the department -- which was formed by 22 disparate agencies -- said a senior U.S. government official who requested anonymity because he is not authorized to publicly discuss intelligence.
More
here.
Report: U.S. Fails to Prosecute Internet Fraud Cases
Via Reuters.
While Web users drown in spam and fend off scams aimed at stealing their money, U.S. federal and state law enforcement authorities are doing little to resolve what has become a multi-billion-dollar problem, a think tank said on Monday.
In the 20 states that give a number for consumer complaints, there were roughly 20,000 Internet-related complaints in 2007, said the group, which surveyed officials in all 50 states but received widely varying amounts of data.
Eight states put Internet-related complaints among their top-three consumer headaches in 2007 while 24 states had some form of online fraud in their top 10 complaints, according to the Center for American Progress (CAP), which worked with the Center for Democracy and Technology.
And the complaints are not unfounded; spyware, viruses and phishing cost consumers $7.1 billion in 2007, up from $2 billion the previous year, the report said.
More
here.
Pentagon Hacker McKinnon Earns Extradition Delay
John Leyden writes on The Register:
Pentagon hacker Gary McKinnon has been granted a short reprieve from possible extradition to the US while a European court decides whether or not to intervene.
Law lords rejected McKinnon's appeal against extradition last month, leaving the European Court of Human Rights as his final avenue of appeal. McKinnon's solicitors Kaim Todner have lodged an appeal to the European court arguing that strong arm tactics used by US authorities during plea bargaining negotiations and concerns that McKinnon may be subject to a military tribunal constitute a violation of his human rights.
In a brief statement, Kaim Todner said the court had granted McKinnon "interim relief" against extradition until 28 August, in order for his application to considered before the full chamber of presidents of the European Court of Human Rights. David Dinkeldein, a solicitor at Kaim Todner, explained that the injunction prevents McKinnon's extradition until at least 28 August. The case will be considered on the basis of written papers, and no hearing has been scheduled.
More
here.
Missing SFO Clear Laptop Was Stolen, Not Misplaced

Via CBS5.com.
A laptop containing the personal information of 33,000 applicants to a program that allows air travelers to bypass airport security lines was likely stolen then returned, not just misplaced for more than a week, investigators said Monday.
The Transportation Security Administration announced a week ago that it had suspended new enrollments to the program, known as Clear, after the unencrypted computer went missing from a locked office at San Francisco International Airport.
The TSA also told officials at SFO and other airports that used Clear to cease use of any unencrypted computers and secure devices until encryption can be installed.
The day after TSA's announcement, the laptop reappeared in a locked cabinet in the same office where it was last seen.
Verified Identity Pass Inc., which runs the Clear program, said at the time the company did not know whether its computer was actually stolen or had just been overlooked.
Investigators are now treating the disappearance as a theft and are interviewing Verified Identity Pass employees to figure out who took the laptop and why, said San Mateo County Sheriff's Sgt. Wes Matsuura.
It was "highly doubtful" that a random member of the public swiped the computer and then returned it to the locked office, which is not in a visible location at the airport, Matsuura said.
More
here.
Global Trail of an Online Crime Ring
Brad Stone writes in The New York Times:
The indictments last week of 11 people involved in the group give a remarkably comprehensive picture of how the Internet is enabling new kinds of financial crimes on a vast international scale.
In interviews over the last few days, investigators detailed how they had tracked Mr. Gonzalez and other members of a ring that extended from Ukraine, where a key figure bought and sold stolen numbers over the Internet, to Estonia, where a hacker infiltrated the servers of a Dallas-based restaurant chain.
The criminals stored much of their data on computer servers in Latvia and Ukraine, and purchased blank debit and credit cards from confederates in China, which they imprinted with some of the stolen numbers for use in cash machines, investigators say.
“This was the largest hacking and theft of credit and debit card information ever successfully investigated and prosecuted within the United States,” said Craig Magaw, special agent in charge of the Secret Service’s criminal investigative division. “This case shows that there are no more boundaries.”
More
here.
U.S. Justice Dept. Wants State Criminal Intelligence Systems to Include Terrorism Info
Ben Bain writes on FCW.com:
The Justice Department wants state criminal intelligence data systems to specifically include more intelligence about terrorism.
According to a proposed rule, state and local organizations should gather and include terrorism-related information in their federally funded criminal intelligence data systems.
The rule also would extend the length of time that the systems contain information without review from five to ten years. Justice said the change is necessary because new data analysis technologies might reveal useful intelligence from the data later.
More
here.
Wells Fargo Codes Used to Illegally Access Consumer Data
Jaikumar Vijayan writes on ComputerWorld:
Wells Fargo Bank NA is in the process of notifying some 7,000 individuals that a thief may have accessed their Social Security numbers and other personal information by illegally using the financial services firm's access codes.
The bank learned of the compromise on July 1 when MicroBilt Corp., a reseller of consumer data, notified it of suspicious transactions made using the Wells Fargo access codes, a spokeswoman for the San Francisco-based bank said today. The codes are used by Wells Fargo employees to gain access to consumer credit data.
She said the records belonged to "random individuals," only a small number of whom were Wells Fargo customers.
The compromise was first reported by The Breach Blog, which posted a link to a July 31 letter sent by Wells Fargo to New Hampshire Attorney General Kelly Ayotte notifying her that nine state residents were affected by the breach.
More
here.
Georgian President's Website Moves to Atlanta
An AP newswire article by Peter Svensson, via SFGate.com, reports that:
The Web site of the president of Georgia, the small nation that is battling Russian forces over a breakaway enclave, was moved to a U.S. hosting facility this weekend after allegedly being attacked by Russian hackers.
The original servers located in the country of Georgia were "flooded and blocked by Russians" over the weekend, Nino Doijashvili, chief executive of Atlanta-based hosting company Tulip Systems Inc., said Monday.
The Georgian-born Doijashvili happened to be on vacation in Georgia when fighting broke out on Friday. She cold-called the government to offer her help and transferred president.gov.ge and rustavi2.com, the Web site of a prominent Georgian TV station, to her company's servers Saturday.
Speaking via cell phone from Georgia, Doijashvili said the attacks, traced to Moscow and St. Petersburg, are continuing on the U.S. servers. The president's site was intermittently available midday Monday.
More
here.
Renesys: Georgia Clingin' to The Net
Earl Zmijewski writes on the Renesys Blog:
When you consider the geography of the region, Georgia has few options for connectivity via land routes, namely Turkey, Armenia, Azerbaijan, and Russia. As it turns out, most of those 309 Georgian prefixes get routed via Turkey's TTnet (AS 9121) or Azerbaijan's Delta Telecom (AS 29049). Traffic to Delta Telecom then heads to Russia via JSC Rostelcom (AS 12389). During the hostilities, we've seen no significant changes in routing. In particular, we saw no apparent attempts to limit traffic via Russia, but then again, most traffic from Georgia seems to currently transit Turkey.
So with respect to connectivity, Georgia is ultimately dependent on either Turkey or Russia, and of course, the Turks have their own problems with the PKK. But Georgia has been planning ahead and just announced the completion of the first stage of a cable to Bulgaria under the Black Sea to give them a direct conduit into Europe. As of today, this fiber does not appear to be lit, as we see no evidence of Georgian traffic routed directly via Europe.
More
here.
IT Security Oversight May Have Enabled Countrywide Data Breach
Nancy Gohring writes on ComputerWorld:
A former employee accused of stealing customer data from Countrywide Financial Corp. may have been able to download the information to a thumb drive because of an oversight by the home mortgage lender's IT department.
Rene Rebollo, a former financial analyst at Countrywide, was arrested Aug. 1 in Pasadena, Calif., for allegedly stealing and selling the data, which included names, Social Security numbers and contact information.
According to affidavits filed in U.S. District Court in Los Angeles, Rebollo told FBI agents that most of the computers in the office where he worked had a security feature that prevented the use of thumb drives -- but he had found one system that didn't.
He estimated that he downloaded about 20,000 customer profiles weekly over two years, according to the affidavits.
More
here.
RIA Novosti Hit By Cyber-Attacks As Conflict With Georgia Rages
Via RIA Novosti.
RIA Novosti news agency's website was disabled for several hours on Sunday by a series of hacker attacks, as the conflict between Russia and Georgia over breakaway South Ossetia continued for a third day.
Websites in both Russia and Georgia have been hit by cyber attacks since Georgia launched a major ground and air offensive to seize control of South Ossetia on Friday. Russia responded by sending in tanks and hundreds of troops.
"The DNS-servers and the site itself have been coming under severe attack," said Maxim Kuznetsov, head of the RIA Novosti IT department.
RIA Novosti's servers are now functioning as normal.
More
here.
In Passing: Isaac Hayes

Shadowserver: Georgian Government Websites Under Attack

Via The Shadowserver Foundation.
With the recent events in Georgia, we are now seeing new attacks against .ge sites. www.parliament.ge & president.gov.ge are currently being hit with http floods. In this case, the C&C server involved is at IP address 79.135.167.22 which is located in Turkey.
More
here.
Note: For what it's worth, it is well-known in security circles that TTNet (Turk Telekom) has had some very serious problems with Russian/Ukrainian cyber criminals operating from within their network(s) for a couple of years now:
AS | IP | AS Name
9121 | 79.135.167.22 | TTNET TTnet Autonomous System
Also, Brian Krebs
points out that
Jart Armin has also been blogging about this over on
RBNExploit.
-ferg