Fergie's Tech Blog
Saturday, October 13, 2007
U.S. Toll in Iraq
As of Saturday, Oct. 13, 2007, at least 3,826 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,115 died as a result of hostile action, according to the military's numbers.More here.
The AP count is eight higher than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
And as always, cryptome.org keeps a very, very extensive list here, as does the Iraq Coalition Casualty Count website here.
Friday, October 12, 2007
License Plate Recognition Tools Led to Abduction Arrest
Demian Bulwa writes in The San Francisco Chronicle:
The swift arrest of a San Jose man in the abduction of a 12-year-old girl this week was aided by an eye-opening gadget that can scan the license plates of a street full of cars and instantly alert police to which vehicles have been reported stolen.More here.
It was a breakthrough moment for license plate recognition, a technology that is spreading to law enforcement around the Bay Area - and is prompting privacy concerns.
Russian Business Network: Shadowy Firm Seen as Conduit for Cybercrime
Brian Krebs writes in The Washington Post:
Law enforcement agencies say these kinds of Internet companies are able to thrive in countries where the rule of law is poorly established. "It is clear that organized cybercrime has taken root in countries that don't have response mechanisms, laws, infrastructure and investigative support set up to respond to the threat quickly," said Ronald K. Noble, secretary general of Interpol, an organization that facilitates transnational law enforcement cooperation. He declined to discuss the Russian Business Network specifically.Much more here and here and here.
The company isn't a mainstream Internet service provider, as Comcast and Verizon are. Rather, it specializes in offering Web sites that will remain reachable on the Internet regardless of efforts to shut them down by law enforcement officials -- so-called bulletproof hosting.
Though there are thousands of Web sites that bear the Russian Business Network name on registration records, the company is unchartered and has no legal identity, computer security firms say.
Note: Brian Krebs gets my praise for this in-depth exposé. Kudos. - ferg
U.S. Toll in Iraq, Afghanistan
Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Friday, Oct. 12, 2007, at least 3,823 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,115 died as a result of hostile action, according to the military's numbers.More here and here.
The AP count is five higher than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
As of Friday, Oct. 12, 2007, at least 383 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Oct. 6, 2007.
Of those, the military reports 256 were killed by hostile action.
And as always, cryptome.org keeps a very, very extensive list here, as does the Iraq Coalition Casualty Count website here.
Montana State University Computers Hacked
Montana State University security experts have determined that an unknown hacker remotely accessed a computer server that housed records containing credit card numbers and social security numbers of students who enrolled online for MSU Extended University courses during the last two years.More here.
The data in question were encrypted, and there is no evidence that personal information was stolen. However, the Extended University is sending information by mail to 1,400 people known to have personal information on the server. The letter includes information on how to receive a free credit report, flag a credit file with a fraud alert and monitor accounts for suspicious activity.
House Panel Approves VoIP E911 Bill
Roy Mark writes on eWeek:
Under legislation approved by a House panel, VOIP providers would have direct access to the nation's E911 system in order to comply with Federal Communications Commission rules mandating Internet telephone companies provide customers with emergency calling services.More here.
Currently, E911 calls from VOIP (voice over IP) customers are routed to third parties, such as telephone companies that then connect the calls to the E911 operator. In 2005, the FCC ordered VOIP providers to comply with E911 mandates, but did not require telecoms to open their infrastructure for the providers to directly connect the calls.
The 911 Modernization and Public Safety Act, approved Oct. 10, would give VOIP providers direct access to the E911 system backbone. In addition, the legislation would extend liability protections to VOIP service providers in much the same manner as traditional landline and wireless carriers.
Note: It is unclear right now what the integration challenges will be, but one thing is for sure -- it will mean much more stringent efforts in the area of VoIP security because people's lives are on the line. - ferg
U.S. Government Seeks To Deny The Internet To Its Enemies
Thomas Claburn writes on InformationWeek:
Cyberspace may become a more active battlefield in the Bush administration's war on terrorism.More here.
The new National Strategy for Homeland Security, issued earlier this week by the White House, places a greater emphasis on the "uninterrupted use of the Internet and the communications systems, data, monitoring, and control systems that comprise our cyberinfrastructure."
While such sentiment was clearly evident in the government's 2002 National Strategy for Homeland Security, the new guidelines show more concern for and about the Internet, in keeping with the government's 2006 National Infrastructure Protection Plan.
One measure of that is the frequency with which word "Internet" appears in the two national security plans. In the 2002 guidelines, "Internet" appears five times; in this year's version, it appears nine times.
Labor Wants DHS Pledge on Union Data
Labor leaders have written to U.S. Homeland Security Secretary Michael Chertoff urging him to declare he will not collect information about union membership.More here.
John Sweeney, president of the AFL-CIO, and Edward Wytkind of its Transportation Trades Department say they are concerned about language in an agreement the Department of Homeland Security struck with the European Union regarding the transfer of data about airline passengers.
The agreement covers a category of sensitive information, such as “personal data revealing racial or ethnic origin, political opinions, religious or philosophical beliefs, (and) trade union membership.”
Vermont Attorneys Accuse Feds of Tapping Phone, Hacking
Allan Holmes writes on GovExec's Tech Insider:
This news item certainly will heap more suspicion on the Bush administration’s tactics for fighting terrorism.More here.
A law firm in Vermont, which represents a client in Afghanistan and a prisoner at Guantanamo Bay, is accusing the federal government of tapping its phones and hacking into a computer used by one of the firm's partners, according to an article posted by the Burlington Free Press. Three partners in the law firm Gensburg, Atwell & Broderick recently sent a letter to clients telling them the firm "can't guarantee their communications were confidential," according to the article. The firm said it had found its phone lines crossed and that a computer forensic examination of the computer used by Robert Gensburg "found an application that disabled all security software and would have given someone access to all information on the computer," according to the article.
Gensberg said there may be an innocent explanation for the problems -- such as he may have accidentally downloaded some malware from the Internet -- but "we are quite confident that it is the United States government that has been doing the phone tapping and computer hacking," the lawyers wrote in their Oct. 2 letter to clients.
FCC Lifts AT&T Pricing Restrictions
Brad Reed writes on NetworkWorld:
Despite the objections of some telecom providers, the FCC announced today that it will grant AT&T relief from pricing restrictions for its broadband infrastructure and fiber capabilities.More here.
In a 3-2 vote, the commission granted AT&T forbearance from federal limits on the amount that the company can charge others for using its infrastructure to deliver last mile connections to customers. FCC chairman Kevin Martin said today that granting AT&T relief would give it “the flexibility to further deploy its broadband services and fiber facilities without overly burdensome regulations.”
Martin also said that the majority of the commission thought there was significant enough competition within the broadband industry to allow AT&T leeway in determining prices.
Windows Update Automatically Changing User Settings (Again)
Mary Jo Foley writes on All About Microsoft:
After Patch Tuesday this week (October 9), some Windows Vista users noticed something strange: Windows Update had changed their Automatic Update settings and rebooted their machines automatically without their consent.More here.
The new report comes on the heels of recent complaints regarding Windows Update performing stealth updates on users’ machines who had turned off Automatic Updates. (Microsoft officials subsequently explained that glitch by saying that Windows Update requires self-updating before it is able to recognize that new updates are available. Microsoft promised to be clearer, in the future, in communicating this requirement.)
The AeroXperience Web site reported a new Windows Update problem on October 10, and was told by Microsoft that the company was aware of the issue and were digging into what happened and why.
Storm Trojan Flaunts Crazy Cat to Build Out Botnet

Gregg Keizer writes on ComputerWorld:
After lying low for several weeks, hackers responsible for spreading the Storm Trojan have returned to the attack with e-mail that leads to an exploit-filled Web site and a laughing cat, said researchers today.More here.
Storm -- also known as Nuwar or Peacomm -- is a Trojan horse designed to compromise Windows-powered computers, then add those machines to a growing botnet. Although the size of the botnet Storm has acquired has been disputed, the most conservative estimates put it in the hundreds of thousands.
The malware has been seeded using several attack vectors, but the most common have been e-mail campaigns that contain attachments, or which link to malicious Web sites. Those sites then infect visiting vulnerable PCs using drive-by downloads or by convincing users to click on additional links that then download an executable.
Image source: F-Secure
Opinion: Congress Should Not Assist in a Cover-Up of NSA Spying
The EFF's Cindy Cohn writes in The San Francisco Chronicle:
When Congress rushed to pass the so-called "Protect America Act" on its way out the door for its August recess, San Francisco's Nancy Pelosi, speaker of the House of Representatives, expressed great regret, telling the New York Times on Aug. 5 that the new law "does violence to the Constitution of the United States." She vowed to take steps to correct the temporary measure long before it expires in February 2008.More here.
Now is the time for Speaker Pelosi to make good on that promise, or at least prevent any further harm. In the last couple of weeks, the Bush administration has stepped up the pressure on Congress to surrender even more of individual citizens' privacy and civil liberties. At the top of the Bush administration's list: granting retroactive immunity to the telecommunications companies that have been participating with the National Security Agency in the widespread and incontrovertibly illegal warrantless surveillance of ordinary Americans since 2001. Granting this immunity would prevent the courts from ever ruling on the legality of the "dragnet" surveillance and from imposing needed restraints. Not content with the sweeping new powers granted to it by Congress in August, the Bush administration is essentially demanding that the now Democratic-led Congress cave in to a cover-up.
Thursday, October 11, 2007
Quote of the Day: Alexander Wolfe
"I'm sorry to disappoint the record companies, but the Recording Industry Association of America's legal victory against Jammie Thomas, who was ordered by a Minnesota court to pay $220,000 in damages for sharing songs over Kazaa, changes nothing. Kids still steal most of their music, and the recording industry hasn't accepted the reality that it has to bag both the CD and DRM before it has a prayer of reviving itself."
- Alexander Wolfe, writing on the InformationWeek blog "Wolfe's Den".
U.S. Toll in Iraq
As of Thursday, Oct. 11, 2007, at least 3,821 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,114 died as a result of hostile action, according to the military's numbers.More here.
The AP count is five higher than the Defense Department's tally, last updated Thursday at 10 a.m. EDT.
And as always, cryptome.org keeps a very, very extensive list here, as does the Iraq Coalition Casualty Count website here.
CIA Investigates Conduct of Its Own Inspector General
Greg Miller writes in The Los Angeles Times:
CIA Director Michael V. Hayden has mounted a highly unusual challenge to the agency's chief watchdog, ordering an internal investigation of an inspector general who has issued a series of scathing reports sharply critical of top CIA officials, according to government officials familiar with the matter.More here.
The move has prompted concerns that Hayden is seeking to rein in an inspector general who has used the office to bring harsh scrutiny of CIA figures from former Director George J. Tenet to undercover operatives running secret overseas prison sites.
Oregon: Virus Cripples Computers at Two Lake Oswego Schools
Students and staff at Lake Oswego High School and Lake Oswego Junior High have been learning in a lower-tech style since Tuesday, when a file-deleting virus forced the shutdown of nearly 400 computers, school officials said.More here.
So far, the Lake Oswego School District has been unable to determine the extent of the damage, said Donna Atherton, director of secondary education.
Teachers could not use computerized "chalk boards," counselors could not access student files, and students could not work on projects stored in classroom computer files.
The virus infected so-called executables, such as Word and Excel programs, said Jeff Kelso, the district's director of computer services. When software couldn't clean the virus out, he said, "it deleted the executable."
Programming Note: Skunk

So, I'm walking my dogs earlier this evening, and they lunge for some critter under a truck in a nearby parking lot.... Yeah, you can guess the rest.
They got skunked.
I had almost forgotten what a horrible, nasty, smelly mess it can be.
One of the dogs got it right in the face -- freaked out and went running through the house when we got back. And now the whole house smells like... skunk.
Yuck.
So after several hours of washing dogs, towels, etc., I still can't get the smell out of my nose.
Yuck. Yuck. Yuck.
- ferg
Documents: Qwest Was Targeted Because of Spying Refusal
Sara Burnett and Jeff Smith write in The Rocky Mountain News:
The National Security Agency and other government agencies retaliated against Qwest because the Denver telco refused to go along with a phone spying program, documents released Wednesday suggest.More here.
The documents indicate that likely would have been at the heart of former CEO Joe Nacchio's so-called "classified information" defense at his insider trading trial, had he been allowed to present it.
(Props, Pogo Was Right.)
.Asia Registry to Crack Down on Phishy Domains

Jeremy Kirk writes on InfoWorld:
The registry for the new .asia TLD (top-level domain) plans to ban domain names that are consistently used for phishing sites.More here.
DotAsia Organization has agreed to implement a policy to ban domain names associated with phishing, said Laura Mather, of the Anti-Phishing Working Group (APWG), a consortium of companies and government groups that studies phishing. She is also a senior scientist at MarkMonitor.
It's the first time that a registry has undertaken such a drastic action to stop the proliferation of fake Web sites designed to dupe people into divulging sensitive personal data.
Feds Appealing Patriot Act Ruling
The Bush administration is appealing a ruling by a federal judge in Oregon who struck down key portions of the USA Patriot Act as unconstitutional.More here.
U.S. District Judge Ann Aiken ruled last month the act cannot be used to authorize secret searches and wiretapping to gather criminal evidence - instead of intelligence gathering - without violating the Fourth Amendment ban on unreasonable searches and seizures.
The ruling came in a challenge to the act by Brandon Mayfield, a Portland lawyer whose home and office were secretly searched and bugged after the FBI misidentified a fingerprint in the Madrid train bombings that killed 191 people in 2004.
NIST Updates 'Guidelines on Securing Public Web Servers'
Joab Jackson and John Rendleman write on GCN.com:
Setting up a public Web page for your agency or department? Take a look at a newly revised set of recommendations from the National Institute of Standards and Technology, “Guidelines on Securing Public Web Servers” (Special Publication 800-44) [.pdf].More here.
The second draft, researched and published by the computer security division at NIST’s Information Technology Laboratory, is intended to help government organizations install, configure and maintain secure public Web servers. It replaces NIST’s first version of the guidelines, published in 2002.
Microsoft Issues IE Security Alert
Andy Patrizio writes on internetnews.com:
Microsoft has issued a rare out-of-pocket security alert concerning the current version of Internet Explorer. The newly discovered vulnerability affects Windows XP, Server 2003 and Windows 2000 but not Vista, and it does affect Internet Explorer 6.0 or earlier. It only involves XP/2000/Server 2003 running IE 7.More here.
In a posting to its security blog, Microsoft said the threat presents itself when Windows does not correctly handle specially crafted URLs or URIs that are passed to it.
Internet Explorer 7 updates a Windows component, which modifies the interaction between Internet Explorer and Windows Shell when handling URLs and URI’s. Applications that pass un-validated URIs or URLs to Windows can be leveraged to exploit this vulnerability.
Wednesday, October 10, 2007
U.S. Toll in Iraq
As of Wednesday, Oct. 10, 2007, at least 3,820 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,114 died as a result of hostile action, according to the military's numbers.More here.
The AP count is four higher than the Defense Department's tally, last updated Wednesday at 10 a.m. EDT.
And as always, cryptome.org keeps a very, very extensive list here, as does the Iraq Coalition Casualty Count website here.
TJX: The Unsurpassed Geniuses At Playing Dumb
Evan Schuman writes on StorefrontBacktalk:
As I look back at the 10 months of this soap opera known as the TJX data breach—the biggest ever, in case someone forgot—I keep being reminded of a wonderful piece of dialogue in the 1990s TV show, The West Wing.More here.
One of the characters—a White House deputy communications director named Sam Seaborn—was arguing with another character when she told him, "Don't play dumb with me." He replied: "I'm not playing dumb. I really am dumb. Most of the time, I'm playing smart."
The TV joke was that this character truly was smart and was a smart guy playing dumb beneath playing smart. (Shades of Victor/Victoria but let's not go there.) This brings us back to TJX.
Australia: The Dangers of Technological Ineptitude - UPDATE
Liam Tung writes on ZDNet Australia:
Brett Soric, a local security and computer enthusiast, was reported to the Australian Federal Police after he created a script that exploited a common flaw in Labor and Liberal's official Web sites. Soric claimed he hasn't done anything wrong.More here.
"So far I've been assuming that the police will understand what's happened before trying to find me," Soric, the so-called "hacker" told ZDNet Australia in an e-mail interview today.
ZDNet Australia on Tuesday reported that cross-site scripting (XSS) vulnerabilities found in the Web sites of both major political parties allowed the public, via a Web site created by Soric, to insert comments that appear to be generated by the Liberal and Labor parties.
Note: Let's hope the Australian police realize that the problem lies in the insecurity of the political websites which allow XSS abuses. - ferg
UPDATE: 21:50 PDT: The guy is "off the hook".
Merchants Putting PCI Certification Above Actually Improving Security?
Lisa Vaas writes on eWeek:
Security experts are starting to grumble about the Payment Card Industry Data Security Standard, saying that some merchants just want to get PCI-certified as cheaply and easily as possible—and that the PCI certification system is set up to help them do just that.More here.
"The entire system seems to be set up not to find vulnerabilities," Jeremiah Grossman, chief technology officer and founder of WhiteHat Security, based in Santa Clara, Calif., and one of 135 security firms on the PCI Security Council's list of ASVs (Approved Scanning Vendors), said in an interview with eWEEK.
"We've had customers that wanted to debate the severity of certain issues because they needed to pass PCI. We sent them to another vendor we thought would pass them more easily. The last thing I want is a customer to get hacked on a vulnerability I didn't find."
Security Experts Say Rock Phish Widening Net
Jon Swartz writes in USA Today:
A recent surge in phishing — fraudulent e-mail and websites designed to "fish" sensitive personal information such as passwords and credit card numbers — is the handiwork of a small, shadowy cybergang, computer security experts say.More here.
Rock Phish, a group of technically savvy hackers who oversee phishing websites and provide tools on the Internet that let others phish, is "the major driving force behind a worsening situation, and they are difficult to track down," says Zulfikar Ramzan, senior principal researcher at Symantec's Security Response Group.
Rock Phish got its name because of its use of the word "rock" in the Web addresses of phishing websites. It is believed to be in Eastern Europe, based on the widespread availability of its phishing tools on websites hosted in that region.
FBI spokesman Paul Bresson says it is aware of the group. But U.S. authorities have little legal recourse to bust the foreign group and tamp down the surge in phishing, says Paul Henry, vice president of technology evangelism at Secure Computing.
Researchers Warn of New Attack Methods Against Cisco IOS
Bill Brenner writes on SearchSecurity.com News:
Cisco Systems' Internetwork Operating System (IOS) is susceptible to attacks in which hackers could cause a denial of service or launch malicious code, according to an analysis conducted by researchers at London-based Information Risk Management (IRM).More here.
IRM Chief Research Officer Andy Davis conducted the Cisco IOS security analysis over a two-month period along with senior consultants Gyan Chawdhary and Varun Uppal. The analysis includes videos demonstrating three different shellcode techniques the researchers used to gain remote level 15 (root) exec VTY (shell) access to IOS.
Each piece of shellcode was written in PowerPC assembly language and launched from within a development environment rather than the payload to an exploit, the researchers noted, adding that the development server is connected to the Cisco router 2600 Series via a serial cable and Ethernet for TCP/IP communications. "It takes a short while for the shellcode to start functioning as it has been hooked into the IOS image checksumming routine that runs every 30-60 seconds," the researchers said. "When each starts running, the arbitrary text '' is displayed on the console to indicate successful execution of the shellcode."
Quote of the Day: Steven Aftergood
"If foreign terrorists set out to undermine confidence in the American legal system as an arbiter of justice, they could hardly do more damage than the Bush Administration has done by its use of the 'state secrets' privilege."
- Steven Aftergood, writing on Secrecy News (from the Federation of American Scientists Project on Government Secrecy).
Security Researcher Warns About Citrix Vulnerability
Thomas Claburn writes on InformationWeek:
A security consultancy has identified a vulnerability that could allow an attacker to gain "user access level on integrated remote Citrix servers."More here.
GnuCitizen, which identifies itself as a "cutting-edge think tank" and a "creative hacker organization," has posted a warning about a cross-site request forgery attack that can be made in conjunction with a malicious Web site to trick a Citrix user into opening a specially crafted Citrix independent computer architecture (ICA) file that would compromise his or her system.
If successful, the attacker could gain the ability to execute remote commands at the victim's access level.
NSA's Lucky Break: How the U.S. Became Switchboard to the World

Ryan Singel writes on Wired News:
A lucky coincidence of economics is responsible for routing much of the world's internet and telephone traffic through switching points in the United States, where, under legislation introduced this week, the U.S. National Security Agency will be free to continue tapping it.More here.
Leading House Democrats introduced the so-called RESTORE Act Tuesday that allows the nation's spies to maintain permanent eavesdropping stations inside United States switching centers. Telecom and internet experts interviewed by Wired News say the bill will give the NSA legal access to a torrent of foreign phone calls and internet traffic that travels through American soil on its way someplace else.
But contrary to recent assertions by Bush administration officials, the amount of international traffic entering the United States is dropping, not increasing, experts say.
Bush Threatens Veto of Eavesdropping Bill - UPDATE
An AP newswire article by Jennifer Loven, via The Washington Post, reports that:
President Bush said Wednesday that he will not sign a new eavesdropping bill if it does not grant retroactive immunity to U.S. telecommunications companies that helped conduct electronic surveillance without court orders.More here.
A proposed bill unveiled by Democrats on Tuesday does not include such a provision. Bush, appearing on the South Lawn as that measure was taken up in two House committees, said the measure is unacceptable for that and other reasons.
UPDATE: 15:08 PDT: Declan McCullagh and Anne Broache have written a very thorough overview on the current status of this situation over on C|Net News.
Commerce Bank Says Hacking Damage Was Limited
Jeremy Kirk writes on InfoWorld:
A regional bank in the U.S. said it was able to deflect most of a hacking attempt on its database, but not before some customer information was divulged.More here.
Commerce Bank, which operates banks in five U.S. states, said Tuesday that a hacker gained access to a database with about 3,000 customer records and accessed data belonging to 20 of them. The bank is contacting those who may have been affected.
The hacking was quickly detected and stopped, according to Commerce Bank, which then notified law enforcement.
It wasn't clear how the hacker accessed the bank's database. A common method is by passing malicious data through Web-based forms, known as a SQL (Structure Query Language) injection, which can force the database to reveal other information it holds.
U.S. Telecoms And Bush Team Up For Another Drive For Wiretapping Immunity

Eric Lichtblau writes in The New York Times:
Whether telecommunication utilities should have legal immunity for having helped the National Security Agency conduct eavesdropping without warrants emerged on Tuesday as the pivotal issue in the debate over wiretapping powers.More here.
The Bush administration, urged by the telecommunication industry, is pushing hard for Congress to include immunity for past actions in any package to protect them from a series of civil suits.
House Democrats promised on Tuesday to block any deal for immunity unless the White House agreed to turn over internal records showing the utilities’ role in the eavesdropping.
Background.
Tuesday, October 09, 2007
White House Tries Another Terror Ruse Before FISA Debate
A Reuters newswire article, via MSNBC, reports that:
Al-Qaida remains the "most serious and dangerous" terrorism threat and is expected to intensify attempts to place agents inside the United States, a White House report said on Tuesday.More here.
Despite efforts to destroy the group responsible for the September 11 attacks, al-Qaida has protected its top leadership, replenished its lieutenants and "regenerated a safe haven" in Pakistan's tribal areas, the report said.
Al-Qaida also continues to pursue weapons of mass destruction and is trying to acquire and use chemical, biological, radiological or nuclear material, said the "National Strategy for Homeland Security" report.
Note: Why does this sound familiar? Oh, yeah. - ferg
Australia: Most Organizations Sweep Security Breaches Under The Carpet
Liam Tung writes on ZDNet Australia:
Australian Federal Police agent, Nigel Phair, said most Australian organisations sweep security breaches under the carpet to avoid public scrutiny in the courts.More here.
"A lot of this is kept under the radar," Phair said at a Logica CMG conference in Sydney yesterday. "A lot of organisations don't report security breaches to police. For some organisations, it's easier to sweep under the carpet ... and move on."
The problem with reporting security breaches, according to Phair, is that taking the matter to police means the facts and the company name are dragged through the courts -- an outcome most organisations prefer to avoid.
Note: I gotta tell ya, Liam -- I think Australia is no different in this respect than any other place on Planet Earth, sadly. - ferg
AT&T, California Settle Over Fraudulent Phone Charges
CBS 5 has learned a first-of-its-kind settlement has been reached between the State of California and the state's largest wireless phone company for charging customers when their phones are stolen.More here.
Attorney General Brown will file the court settlement on Wednesday fining AT&T, formerly Cingular Wireless for $500,000 and will order the company to stop charging for fraudulent calls.
ConsumerWatch reporter Jeanette Pavini sat down with the Attorney General on Tuesday to discuss the settlement between the State and AT&T.
Pavini asked Brown if cell phone companies were breaking state law for charging customers for the calls.
"Oh yeah," Brown said. "They were breaking the law in our opinion."
Quote of the Day [2]: Ian Rogers
"8 years. How much opportunity have we lost in those 8 years? How much naivety and hubris did we have when we said, 'if we build it they will come'? What did we spend? And what did we gain? We certainly didn’t gain mass user adoption or trust, two prerequisites to success on the Internet."
- Ian Rogers, Yahoo! Music's GM, quoted in this EFF article on the continual retarded, and self-defeating, policy of DRM.
Also, fantastic commentary by my good friend and colleague Alex Eckelberry at Sunbelt Software on this same topic, singing Ian Rogers' praise as a new hero.
U.S. Toll in Iraq, Afghanistan
Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Tuesday, Oct. 9, 2007, at least 3,818 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,109 died as a result of hostile action, according to the military's numbers.More here and here.
The AP count is seven higher than the Defense Department's tally, last updated Tuesday at 10 a.m. EDT.
As of Tuesday, Oct. 9, 2007, at least 381 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Sept. 29, 2007.
Of those, the military reports 254 were killed by hostile action.
And as always, cryptome.org keeps a very, very extensive list here, as does the Iraq Coalition Casualty Count website here.
Malware as a Service
Most of the time us webappsec people are a world’s apart from the traditional A/V and malware industry involved in reverse engineering rootkits, creating signatures, taking down botnets, tracking fraud, etc. We read the headline snippets sure, but don’t really have the time to keep up with what’s happening at ground level.More here.
So when Scott Berinato of CIO.com passed along his latest and VERY in depth thee-part article documenting the evolution Malware Industry through infiltrating fraud rings, I was definitely interested. The text is definitely illuminating as it talks about groups such as the Russian Business Network, ShadowCrew, HangUp Team, 76service and others and how they’re turning the industry into “Malware as a Service” (MaaS).
Web 2.0 models are for everyone I guess.
Nine Inch Nails Becomes a Free Agent With No Record Label

Scott Beale writes on Laughing Squid:
Yesterday Trent Reznor wrote an amazing post on the Nine Inch Nails blog stating that he no longer has a record contract and that NIN is now a free agent.More here.
This, along with Radiohead’s pay what you want release of their new album “In Rainbows”, are both signs of big changes to come in the record industry.
Ex-Spies Blast Today's Spooks for al-Qaeda Breach
Noah Shachtman writes on Danger Room:
Former spies are blasting their former colleagues for blowing the cover of a private investigation into Al-Qaeda's "intranet." Rita Katz, head of the jihadist-monitoring SITE Institute, says her operation was compromised hours after she gave the White House and the National Counterterrorism Center an advance look at an Osama Bin Laden online video.More here.
On his blog Haft of the Spear, signals and human intelligence veteran Michael Tanji says "without a doubt SITE is justified in feeling like the gov’t screwed things up."
TJX Revises Consumer Settlement, Agrees To Pay Cash
Evan Schuman writes on StorefrontBacktalk:
Hours before a federal judge demanded that TJX address key concerns about its proposed settlement, the merchant behind the biggest retail data breach ever agreed to some key changes, including offering a cash alternative to its voucher offer.More here.
The biggest objection to the initial proposed settlement had been that consumer victims were only offered $30 vouchers for making purchases at TJX. Under a new proposed settlement that was filed late Tuesday, attorneys for both sides are now proposing giving consumers a choice: either the $30 voucher or a $15 check.
Paper: A Multi-Perspective Analysis of the Storm Worm
A Multi-perspective Analysis of the Storm (Peacomm) WormHere.
Phillip Porras, Hassen Saidi, and Vinod Yegneswaran
Computer Science Laboratory, SRI International
Since early 2007 a new form of malware has made its presence known on the Internet by its prolific growth rate, its ability to distribute large volumes of spam, and its ability to avoid detection and eradication. Storm Worm (or W32.Peacomm, Nuwar, Tibs, Zhelatin), as it is known, is a highly prolific new generation of malware that has gained a significant foothold in unsuspecting Microsoft Windows computers across the Internet. Storm, like all bots, distinguishes itself from other forms of malware (viruses, Trojan horses, worms) by its ability to establish a control channel that allows its infected clients to operate as a coordinated collective, or botnet. However, even among botnets Storm has further distinguished itself by being among the first to introduce a fully P2P control channel, to utilize fast-flux to hide its binary distribution points, and to aggressively defend itself from those who would seek to reverse engineer its logic.
Despite all the hype and paranoia surrounding Storm, the inner workings of this botnet largely remain a mystery. Indeed, Storm is believed to have an automated distributed denial of service (DDoS) feature to dissuade reverse engineering, which gets triggered based on situational awareness gathered from its overlay network, e.g., when the count of spurious probes crosses a certain threshold. It has also been reported that these defenses have been turned on those that have posted their analysis results of Storm. In this paper, we attempt to partially address voids in our collective understanding of Storm by providing a multi-perspective analysis of various Storm clients. Our analysis includes a static dissection of the malware binary and the characteristics of the Storm worm's network dialog as observed from multiple infection traces. Finally, we do not only seek to analyze Storm for the greater understanding, but also to develop solutions that can help detect its presence, even as we expect Storm to continue to evolve and elude host security products.
Quote of the Day: Charles Arthur
"In what must have domain registrars around the world rubbing their hands with glee and ordering new yachts, we now have another TLD that nobody can quite remember asking for (is it like the gherkin in a fastburger?) which will coin it from all the companies that feel they have to register their name just to make sure that nobody else does. Which especially means all the banks and other brands, but which equally means that typosquatters and phishers can have a new way to play havoc with everyone's lives."
- Charles Aurthur, writing on The Guardian Technology Blog, regarding "What's the point of the .asia top-level domain?"
Australia: XSS Flaw Makes PM Say: 'I want to suck your blood'
Liam Tung writes on ZDNet Australia:
The Web sites of Australia's two major political parties contain cross-site scripting (XSS) flaws, which could be exploited to fraudulently acquire political donations, say security experts.More here.
A short line of script developed by a security enthusiast, Bsoric, causes the Liberal Party's Web site to read: "John Howard says: I want to suck your blood", while another script caused a window to pop up on the Labor Party's Web site, urging viewers to "Vote Liberal!"
How Russia Became a Malware Hornet's Nest
Bill Brenner writes on SearchSecurity News:
That Russia is a hornet's nest of malicious cyber activity is nothing new. The question for some in the information security community is why people from that part of the world are so determined to earn a living writing attack code.More here.
A dismal economy and lax law enforcement is fueling the problem, say two well-known security researchers. It has helped nudge Russian computer programmers into an underground market where easy money can be made creating programs used to steal credit card and Social Security numbers.
"[Russian hackers] don't see themselves as doing anything criminal," Kaspersky Labs CEO Eugene Kaspersky said during an interview at his company's U.S. facility in Woburn, Mass., last week.
He explained that many Russian programmers compare themselves to weapons manufacturers -- they build the technology but are not the ones using it. In other words, they're not responsible if someone else is pulling the trigger. Meanwhile, Kaspersky said, the Russian economy is still shaky enough that people are looking for ways to make a steady living, and building malware for online gangsters is one way to do it.
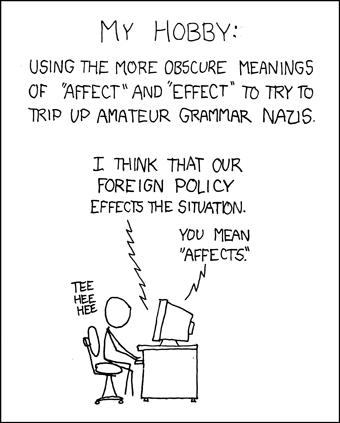
From xkcd to Reality: The ANT Censuses of the Internet Address Space

Paul McNamara writes on the NetworkWorld Buzzblog:
No door-to-door canvassing here: This census involved the direction of some 3 billion pings toward 2.8 million allocated Internet addresses from three machines over the course of two months.More here.
And, oddly enough, the researchers say their project – designed to help predict future trends and improve ‘Net security -- received data-presentation advice from an unexpected source: a comic strip, albeit one fittingly made popular by the Web.
Such a comprehensive census of the “visible Internet” had not been undertaken since 1982 when David Smallberg conducted a full accounting of what was then a mere 315 allocated addresses, according to researchers at the University of Southern California Information Sciences Institute.
Image source: xkcd
Image of the Day: 'Hello My Name Is Inigo Montoya'

I know Gadi will love this...
Image source: Laughing Squid
Monday, October 08, 2007
Image of the Day: Dr. Strangebush

Be afraid. Very afraid.
And it's more like $600B now, Bush meister.
Quote of the Day: Tim Lee
"Can someone remind me what the point of having an opposition party was supposed to be? I’m pretty sure this wasn’t it."
- Tim Lee, writing on The Technology Liberation Front.
The Protect America Scam: An Open Letter to California Legislators
A copy of a message I have e-Mailed to:
Representative, and Chairwomen of the House, Nancy Pelosi
Representative Zoe Lofgren
Senator Diane Feinstein
Dear [Elected Official],I urge you to do the same. Now.
As a registered voter, and a resident of California, I am EXTREMELY concerned about the prospect of Democratic compromising on the "Protect America Act" -- I DO NOT want to see this travesty perpetuated without proper judicial oversight.
It is my fear that, unchecked, this could lead to a very troubling and corrosive imbalance in the checks and balances that frame the law of the land -- giving too much unchecked power to the executive branch and trivializing the need for oversight.
Please do not allow a compromise on this issue.
I can assure you that I will vote my conscience in the next term -- and will not vote for any legislator that compromises on this issue.
I beg you to not cave in on this important issue.
Respectfully yours,
Paul Ferguson
San Jose, California
California Resident, Voter, Constituent
Before it is too late.
Democratic Concessions Are Expected on Wiretapping
Eric Lichtblau and Carl Hulse write in The New York Times:
More here.
Two months after vowing to roll back broad new wiretapping powers won by the Bush administration, Congressional Democrats appear ready to make concessions that could extend some of the key powers granted to the National Security Agency.
Bush administration officials say they are confident they will win approval of the broadened wiretapping authority that they secured temporarily in August as Congress rushed toward recess, and some Democratic officials admit that they may not come up with the votes to rein in the administration.
As the debate over the N.S.A.’s wiretapping powers begins anew this week, the emerging legislation reflects the political reality confronting the Democrats. While they are willing to oppose the White House on the conduct of the war in Iraq, they remain nervous that they will be labeled as soft on terrorism if they insist on strict curbs on intelligence gathering.
Just "Say No".
BT Home Router Wide Open to Hijackers
Dan Goodin writes on The Register:
If you rely on BT for high-speed internet or VoIP, there's a good chance a pair of UK-based researchers know how to enable a backdoor in your router that leaves you wide open to eavesdropping, caller spoofing and other nasty attacks.More here.
The vulnerability resides in the BT Home Hub, one of the UK's most popular home routers, according to Adrian Pastor and Petko D. Petkov. A constellation of bugs in the router, which is made by Thomson/Alcatel, make it possible to bypass the device's password authentication system and gain complete administrative control.
All an attacker needs to do to exploit the weaknesses is lure the victim to a maliciously crafted website, according to this post on the GNUCitizen blog. The exploit doesn't require knowledge of the administrator password.
Mother Earth Tech: American Electric Power to Pay Unprecedented $4.6B Environmental Fine

An AP newswire article, via MSNBC, reports that:
One of the nation’s largest power generators has agreed to end a years-long federal lawsuit by paying $4.6 billion to reduce pollution that has eaten away at Northeast mountain ranges and national landmarks, The Associated Press has learned.More here.
The settlement requires American Electric Power, based in Columbus, Ohio, to reduce chemical emissions that cause acid rain by at least 69 percent over the next decade.
It also fines AEP an additional $15 million in civil penalties and another $60 million in cleanup and mitigation costs to help heal parkland and waterways that have been hurt by the pollution.
U.S. Toll in Iraq
As of Monday, Oct. 8, 2007, at least 3,816 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,105 died as a result of hostile action, according to the military's numbers.More here.
The AP count is 10 higher than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
And as always, cryptome.org keeps a very, very extensive list here, as does the Iraq Coalition Casualty Count website here.
Absurdity Alert: UK Boy Arrested for Anarchist Cookbook
A 17-year-old in the UK was arrested for "collection or possession of information useful in the preparation of an act of terrorism" due to his possession of the Anarchist Cookbook. Strange that a book freely available on amazon.co.uk can get you arrested.More here.
The teenager faces two charges under the Terrorism Act 2000.
The first charge relates to the possession of material for terrorist purposes in October last year.
The second relates to the collection or possession of information useful in the preparation of an act of terrorism.
Hacker Breaks Into eBay Server, Locks Out Users
Juan Carlos Perez writes on InfoWorld:
A malicious hacker broke into an eBay server on Friday and temporarily suspended the accounts of a "very small" number of members, the company said.More here.
"We were able to block the fraudster quickly before any permanent damage had been done. At no point did the fraudster get any access to financial information or other sensitive information," eBay spokeswoman Nichola Sharpe said via e-mail.
eBay has "secured and restored" the affected accounts and is calling the affected users, she said, without specifying how many accounts the hacker accessed and tinkered with.
"The fraudster did this by accessing externally visible servers, not by hacking into the eBay site," Sharpe said.
Space.com Video: North Korean Nuclear Reactors Revealed
IKONOS Satellite data produces 3D fly-through of YongByon reactor complex.Watch it here.
Credit: Satellite Imaging Corp & GlobalSecurity.org. Story by SPACE.com.
The Technology Behind the Formula One Scandal
Justin Mullins writes in IEEE Spectrum:
In Europe and Asia, Formula One is the undisputed king of motor sports. No other form of motor racing can compete with the glamour, money, and technology that F1 teams draw on. But for much of this racing season, the sport has been engulfed in a spying scandal wherein members of one team allegedly acquired secret details about the technology used by a competitor.More here.
That team, the UK-based McLaren, was recently fined an unprecedented US $100 million. As details of the affair have leaked out, fans have been shocked by the confessions and betrayals behind the scandal, which would seem more at home in an airport thriller than a multibillion-dollar sport.
The technical secrets at issue remain just that—secrets. But enough information has emerged from the scandal's investigation to put together a picture of what happened and what McLaren stood to gain.
U.S. NGA Taps Lockheed for Geospatial Intelligence

Patrick Marshall writes on GCN.com:
The National Geospatial-Intelligence Agency has awarded a contract estimated to be worth approximately $20 million over five years to Lockheed Martin Integrated Systems and Global Services, which will develop a pilot program for demand-based geospatial intelligence.More here.
The goal of DBGI is to provide federal agencies access to the most recent geospatial intelligence data immediately upon demand and in a format appropriate for the user’s needs. Currently, NGA produces hard-copy maps using large-format, five-color offset lithographic presses. This process has been necessary to meet military requirements that charts and maps be printed in specific spot colors to ensure readability in poor lighting conditions.
Image source: Federation of American Scientists
U.S. 'State Secrets' Case May Get Airing - UPDATE [2]
David G. Savage writes in The Los Angeles Times:
The Supreme Court is set to decide as early as Tuesday whether the government can invoke the doctrine of "state secrets" to quash a legal claim that CIA bungling resulted in a man being abducted, imprisoned and tortured.More here.
After five months of such treatment, CIA agents apparently realized that the man in custody, Khaled el-Masri, a German citizen of Lebanese descent, was not the wanted terrorist Khalid al-Masri.
The case has attracted wide public attention in Europe, but El-Masri has been unable to gain a court hearing in the United States because the government has so far successfully invoked the argument that it cannot be taken to court when doing so might expose state secrets.
UPDATE: 12:00 PDT: Apparently, this issue is also getting visibility in the UK. Details here.
UPDATE [2]: 10:31 PDT, 8 October 2007: Unfortunately it appears that Mr. El-Masri will not get his day in court.
Sunrocket VOIP Mix-Up Exposes Customer Call Data
Brian Krebs writes on Security Fix:
Bill Adler was relieved to get his old phone number back. The Washington-area resident's digits were marooned shortly after his former Internet-based phone service provider -- Sunrocket -- abruptly closed its doors in mid-July. Relieved, that is, until he received an odd phone call from a local man who'd inherited Adler's phone records along with his old temporary phone number.More here.
Adler had signed up with ViaTalk, one of several voice-over-IP providers who scrambled to absorb Sunrocket's 200,000 stranded customers. ViaTalk gave him a temporary number while it was negotiating the recovery of his old one. A few weeks after ViaTalk secured his old number, Adler heard from the ViaTalk customer who had inherited his temporary digits.
"I couldn't believe it, and at first I thought it was a crank call," Adler said. "The guy was reading me our inbound and outbound phone records [created] during the one month we were using that temporary number."
Sunday, October 07, 2007
Turkish Hackers Target Swedish Websites
An AP newswire article by Malin Rising, via The Boston Globe, reports that:
Hackers in Turkey have attacked more than 5,000 Swedish Web sites in the past week, and at least some of the sabotage appears linked to Muslim anger over a Swedish newspaper drawing that depicted the Prophet Muhammad's head on a dog's body.More here.
Around 1,600 Web sites hosted by server-provider Proinet and 3,800 sites hosted by another company have been targeted, Proinet spokesman Kjetil Jensen said Sunday. Jensen said hackers, operating on a Turkish network, at times replaced files on the sites with messages.
According to Swedish news agency TT, the Web site of a children's cartoon called Bamse was replaced by a message saying Islam's prophet had been insulted.
The incidents have been reported to the police.