Quote of the Day: Swa Fantzen
"I guess I need to say thanks to those who created and run .name for this 'wonderful' scheme. I'm sure those up to no good will love you for it."
- Swa Frantzen, writing on the SANS Internet Storm Center Daily Handler's Diary, about the fact that the ".name" registry wants to be paid to reveal who registered domain names.
Symantec Issues Bogus Warning of Full-Scale Internet Meltdown
Gregg Keizer writes on ComputerWorld:
Symantec Corp.'s early warning system gave its enterprise customers a brief scare late Friday when it erroneously sent an alert that said an Internet-crippling attack was in progress.
The message, which went out to users of Symantec's DeepSight advanced alert system around 8:40 p.m. EDT, had a subject head that simply read: "DeepSight Increased ThreatCon from 1 to 4 Alert."
ThreatCon uses a 1-through-4 scoring system, with 1 being the least alarming and 4 the most dire, to indicate Symantec's take on the current state of Internet security. According to the company's own definition, Level 4 is tagged as "Full alert" and reserved for those times when "extreme global network incident activity is in progress. Implementation of measures in this Threat Condition for more than a short period probably will create hardship and affect the normal operations of network infrastructure."
More
here.
Let's Review: Fascist America, In 10 Easy Steps

Given the political and governmental situation in the United States, let's review Naomi Wolfe's Countdown to Fascism in America, which originally appeared in The Guardian, a non-U.S.-based publication.
1. Invoke a terrifying internal and external enemy
2. Create a gulag
3. Develop a thug caste
4. Set up an internal surveillance system
5. Harass citizens' groups
6. Engage in arbitrary detention and release
7. Target key individuals
8. Control the press
9. Dissent equals treason
10. Suspend the rule of law
We are well on our way to ruin.
I urge each and every one of you to read, and comprehend,
this article -- and the implications.
Wake up, America. You are being screwed.- fergBonus link: The Colbert Report: Naomi Wolfe on Fascism in America
Welcome, Autumnal Equinox
Via StarDate.org.
One of the great rhythms of the sky is the up-and-down "nodding" of the Sun. Over the course of a year, the Sun moves north and south on the sky. That means it rises and sets at different points on the horizon, and it moves higher or lower at noontime.
This weekend, the Sun's right in the middle of that annual migration -- a point known as the equinox. It rises due east and sets due west, so if you want to find east and west from your house, this is the time of year to do it. And the Sun stands at its highest point in the sky at exactly local noon -- something that isn't always the case on other days of the year.
More
here.
U.S. Effort To Collect Traveler Information More Extensive Than Previously Known
Ellen Nakashima writes in The Washington Post:
The U.S. government is collecting electronic records on the travel habits of millions of Americans who fly, drive or take cruises abroad, retaining data on the persons with whom they travel or plan to stay, the personal items they carry during their journeys, and even the books that travelers have carried, according to documents obtained by a group of civil liberties advocates and statements by government officials.
The personal travel records are meant to be stored for as long as 15 years, as part of the Department of Homeland Security's effort to assess the security threat posed by all travelers entering the country. Officials say the records, which are analyzed by the department's Automated Targeting System, help border officials distinguish potential terrorists from innocent people entering the country.
But new details about the information being retained suggest that the government is monitoring the personal habits of travelers more closely than it has previously acknowledged. The details were learned when a group of activists requested copies of official records on their own travel. Those records included a description of a book on marijuana that one of them carried and small flashlights bearing the symbol of a marijuana leaf.
More
here.
Gapingvoid: Zappa Anthem
Via gapingvoid.com. Enjoy!

U.S. Toll in Iraq, Afghanistan
Iraq and Afghanistan statistics via The Boston Globe (AP).
As of Friday, Sept. 21, 2007, at least 3,793 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,095 died as a result of hostile action, according to the military's numbers.
The AP count is five higher than the Defense Department's tally, last updated Friday at 10 a.m. EDT.
As of Friday, Sept. 21, 2007, at least 375 members of the U.S. military had died in Afghanistan, Pakistan and Uzbekistan as a result of the U.S. invasion of Afghanistan in late 2001, according to the Defense Department. The department last updated its figures Sept. 21, 2007.
Of those, the military reports 249 were killed by hostile action.
More
here and
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Mortgage Data Leaked Over P2P File Network - UPDATE
An AP newswire article by Anick Jesdanun, via MSNBC, reports that:
Three spreadsheets containing more than 5,000 Social Security numbers and other personal details about customers of ABN Amro Mortgage Group were inadvertently leaked over an online file-sharing network by a former employee.
Tiversa Inc., a Pittsburgh company that offers data-leakage protection services, traced the origins of the ABN data to a Florida computer with the BearShare software installed.
BearShare, LimeWire and scores of other programs are designed to distribute and find songs, movies and other files over the Gnutella file-sharing network.
Tiversa Chief Executive Robert Boback said file-sharing programs are commonly misconfigured to share documents their owners never intended to make public.
More
here.
UPDATE: 17:32 PDT: Lisa Vass has more information on this over on
eWeek:
"Citigroup Customer Data Leaked on LimeWire".
Colorado Sheriff Creates Roadblock to Collect DNA Samples for Private Firm
Declan McCullagh writes on PoliTech:
The Gilpin County Sheriff's Office in Colorado, a rural area not that far west of Denver, recently set up a highway checkpoint where motorists were stopped and, at least in some cases, not allowed to leave until they gave breath, blood, and saliva samples for the benefit of a private research firm. A report by Ernie Hancock says the National Highway Traffic Safety Administration was involved as well.
[A Denver Post article is here.]
The Post says the private organization in question is the Pacific Institute for Research and Evaluation, or PIRE, in Calverton, MD.
Much, much more
here.
Zango Gets all Emotional
Angel Djambazov writes on ReveNews:
Understandably miffed that Kaspersky and PC Tools can continue to classify the free service they provide to "discerning consumers" as spyware, Zango has decided to release their pent up feelings. In celebration of the 25th Anniversary of the Emoticon, Zango is adding to their download arsenal new packs of emoticons that "integrate directly" into Windows Live Messenger.
What I find deliciously ironic is the two emoticons they chose to highlight in their press release. Surely they are indicative of how Zango perceives its audience.
More
here.Note: This is a riot, given Zango's
colorful history.
- ferg
French Plan to Screen DNA of Visa-Seekers Draws Anger
Molly Moore writes in The Washington Post:
The French National Assembly on Thursday approved a controversial proposal authorizing the use of DNA testing to determine whether foreigners applying for visas are actually related to family members they seek to join in France.
The plan, part of President Nicolas Sarkozy's efforts to make it tougher for foreigners from Middle Eastern and African countries to immigrate to France, prompted outrage from human rights groups, opposition politicians and some members of the president's cabinet.
More
here.
FAA Computer Glitch Grounds Bay Area Flights
Via CBS5.com.
Some flights departing from and for the Bay Area were halted for about 20 minutes Friday morning after the primary computer for air traffic control at the Federal Aviation Administration's Oakland center shut down unexpectedly, an FAA spokesman said.
The computer system went down at about 8:50 a.m. and paused all flights departing for the Bay Area from airports within an hour flight distance of the region, FAA spokesman Ian Gregor said.
All flights departing from Bay Area airports scheduled to fly to other Bay Area airports and to Reno airports were stopped as well, according to Gregor.
More
here.
Quote of the Day [2]: Cory Doctorow
"Nice going, Germany -- between this and the new anti-hacker laws, you've managed to criminalize every productive member of the information society. Enjoy the caves and flint axes."
- Cory Doctorow, writing on Boing Boing, that "Germany's parliament on Friday approved a copyright law, which makes it all but illegal for individuals to make save and make copies of television, films and music, even for their own use. It goes into effect in 2008."
Quote of the Day: Lauren Weinstein
"But it's all an ad hoc mess, and in the meantime subscribers are continuing to get royally screwed."
- Lauren Weinstein, discussing on his blog the problem with text message (SMS) scams, and the inability of cellular carriers to effectively address the problem.
Oops: Another XSS In Google Search Appliance
RSnake writes on ha.ckers.org:
Google’s search appliance appears to be vulnerable to another XSS vulnerability, according to Mustlive’s disclosure. It comes complete with a Google dork. Not good. Mustlive has contacted Google, who to my knowledge has not let their customers know that they are vulnerable - if I’m wrong, someone please correct me.
Here are a few examples: gsa.icann.org and search.york.ac.uk.
This obviously puts any site that uses Google’s search appliance with this particular vulnerability in it at risk (there are, as of this writing 186,000 listings on the Google dork). Time to patch up - once Google comes out with one, that is.
More
here.
London Politicians: CCTV Cameras Don't Solve Crimes
Peter Sayer writes on PC World:
Surveillance cameras in London are not helping solve crime, according to local politicians.
The city has over 10,000 publicly funded CCTV cameras in public areas, but only one in five crimes are solved, said Dee Doocey, a spokeswoman for the Liberal Democrats political party on the London Assembly, the elected body which determines transport and policing policy for London's 32 boroughs and the City of London itself.
More
here.
Connecticut Sues Accenture Over Lost Data
William Welsh writes on Washington Technology:
Connecticut Attorney General Richard Blumenthal said this week that he is suing Accenture Ltd. over the loss of confidential taxpayer data and hundreds of state bank account and purchasing card numbers.
Blumenthal, on behalf of the state, is suing the Hamilton, Bermuda-based consultant for negligence, unauthorized use of state property and breach of contract. The lawsuit is asking for reimbursement for state resources that will be spent to protect and secure the information and the return of some money already paid to the company.
The lawsuit stems from an incident in June when a backup device containing information for a similar project in Ohio was stolen. The lawsuit alleges that Accenture converted state property to its own use without state permission and acted negligently to allow sensitive data from Connecticut to be placed on a computer tape for an Ohio project.
More
here.
Companies Forced to Fight Phishing
Brian Krebs writes in The Washington Post:
Kate Trower never found out who was trying to trick her company's customers into giving up their credit card information, but she did learn about their taste in music.
Trower, a fraud investigator for Atlanta-based Internet service provider EarthLink, chased the "German phishers" for months. The scammers built Web pages designed to look like an EarthLink-affiliated site, then sent e-mails to EarthLink customers, prompting recipients to offer up their private financial data and Internet account passwords. Every time the company shut one site down, another would pop up.
More
here.
Australia Pushes Further Web Censorship
Jo Best writes on C|Net News:
A bill introduced this week by Australia's Parliament would give the Australian federal police the power to control which sites can and cannot be viewed by Australian Web surfers.
Introduced on Thursday, the bill--titled the Communications Legislation Amendment (Crime or Terrorism Related Internet Content) Bill 2007--would empower the federal police to alter the "blacklist" of sites that are currently prohibited by the Australian Communications and Media Authority.
The list currently includes pornography and "offensive material." However, under the amendment, federal police would be able to add other sites to the list, including content that the AFP Commissioner "has reason to believe...is crime- or terrorism-related content."
More
here.
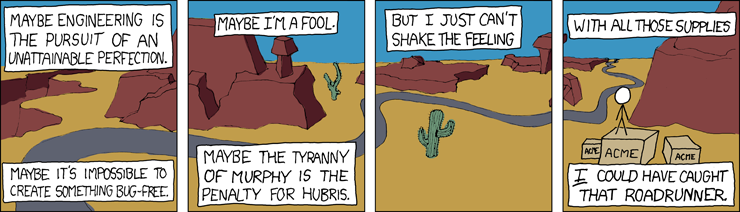
xkcd: Engineering Hubris
Click for larger image.
So very excellent. We
love xkcd.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Thursday, Sept. 20, 2007, at least 3,791 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,094 died as a result of hostile action, according to the military's numbers.
The AP count is five higher than the Defense Department's tally, last updated Thursday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
USAF Eyes 'Cyber-Craft' to Surf The Internet
Via UPI.
The U.S. Air Force is developing cyber-craft -- software that can move through the Internet like planes fly through the air -- and will deploy them by 2010.
Cyber-craft are “collections of intelligent software agents that work together as a unit, analogous to the airframe, payload and pilot associated with physical aircraft,” reported the magazine Defense Systems this week, citing U.S. Air Force technology official Paul Phister.
“As with real platforms, the cyber-craft can perform numerous types of operations” both offensive and defensive, he said.
Students attending the Air Force Research Laboratory’s Cyber Security Boot Camp last year built the first cyber-craft, the magazine reported -- launching it on its maiden “flight” in August 2006.
More
here.
Yes, Its True: Hackers Control PCs While Users Unaware
Jim Finkle writes for Reuters:
A few weeks ago Candace Locklear's office computer quietly started sending out dozens of instant messages with photos attached that were infected with malicious software.
She was sitting at her desk, with no sign that the messaging software was active. By the time she figured out what was going on, several friends and colleagues had opened the attachments and infected their computers.
It took eight hours for a technician to clean up her computer. But because the malicious software worked so secretly, she's still not convinced that all's clear.
"I'd like to think that it's gone. But I just don't know," said Locklear, 40, a publicist in San Francisco. "That's what is so frustrating."
Computer security experts estimate that tens of millions of personal computers are infected with malicious software like the one that attacked Locklear's machine. Such programs, generally classified as malware, attack companies along with consumers.
More
here.
Quote of the Day: Scott Adams
"And what is up with the pizza place that presumably delivered to him five times a day? Did it ever concern them that their Customer of the Month was two pizzas away from forming a black hole?"
- Scott Adams, writing on The Dilbert Blog.
Shocker: White House e-Mails Still Missing
Roy Mark writes on eWeek:
The Bush administration may be running out the clock in its efforts to resist a congressional inquiry and two lawsuits seeking the whereabouts and contents of more than 5 million missing White House e-mails, according to one of the organizations that has filed a suit.
"The White House has known for a number of years the e-mails were missing and refused to do anything about it," Anne Weisman, chief counsel for CREW (Citizens for Responsibility and Ethics in Washington), told eWEEK.
Covering more than a two years, the missing e-mails came to light as part of congressional inquiries into the White House's firing of U.S. attorneys.
More
here.
Lawsuit Alert: Employee Fired for Reporting Breach
Deborah Perelman writes on eWeek:
For one of the biggest healthcare data breaches in history, the lawsuits haven't stopped yet.
In December 2005, thieves broke into the parked van of an IT systems analyst for Providence Home Services, a Washington state health care company, stealing a computer bag with ten unencrypted tapes and disks holding information on what would turn out to be more than 365,000 hospice and home health care patients—everything from Social Security numbers and birth and death dates to diagnoses, prescriptions and insurance numbers. Data on doctors, including their Medicare and Medicaid and state license numbers, names, addresses and phone numbers were also missing.
Executives waited three weeks before informing patients about the stolen data, in what turned out to be the biggest data breach ever reported in Oregon. The state investigation and class-action lawsuit that followed ended in a $95,000 settlement payment by the healthcare provider to the state of Oregon to cover the cost of the investigation.
More
here.
NSA to Defend Against Hackers? Right...
Siobhan Gorman writes in The Baltimore Sun:
In a major shift, the National Security Agency is drawing up plans for a new domestic assignment: helping protect government and private communications networks from cyberattacks and infiltration by terrorists and hackers, according to current and former intelligence officials.
From electricity grids to subways to nuclear power plants, the United States depends more than ever on Internet-based control systems that could be manipulated remotely in a terrorist attack, security specialists say.
The plan calls for the NSA to work with the Department of Homeland Security and other federal agencies to monitor such networks to prevent unauthorized intrusion, according to those with knowledge of what is known internally as the "Cyber Initiative." Details of the project are highly classified.
More
here.
Hat-tip: Threat Level
The Secret Lobbying Campaign Your Phone Company Doesn't Want You to Know About
Michael Isikoff and Mark Hosenball writes in Newsweek:
The nation’s biggest telecommunications companies, working closely with the White House, have mounted a secretive lobbying campaign to get Congress to quickly approve a measure wiping out all private lawsuits against them for assisting the U.S. intelligence community’s warrantless surveillance programs.
The campaign—which involves some of Washington's most prominent lobbying and law firms—has taken on new urgency in recent weeks because of fears that a U.S. appellate court in San Francisco is poised to rule that the lawsuits should be allowed to proceed.
If that happens, the telecom companies say, they may be forced to terminate their cooperation with the U.S. intelligence community—or risk potentially crippling damage awards for allegedly turning over personal information about their customers to the government without a judicial warrant.
“It’s not an exaggeration to say the U.S. intelligence community is in a near-panic about this,” said one communications industry lawyer familiar with the debate who asked not to be publicly identified because of the sensitivity surrounding the issue.
More
here.
FBI to Automate Wiretap Database
Wilson P. Dizard III writes on GCN.com:
The FBI is working to build an automated system to track its National Security Letter wiretap cases in a bid to eliminate cumbersome and error-prone manual entry of data about the eavesdropping projects. The bureau currently relies on Microsoft Access software to track wiretap requests in the Office of General Counsel (OGC) database.
FBI deputy director John Pistole told the House Permanent Select Committee on Intelligence earlier this year that although “the OGC database was a giant technological step forward from three-by-five index cards once used to track NSLs, it is not an acceptable system given the significant increase in use of NSLs since 9/11.”
The new NSL database management system will use a Java Enterprise Edition application server from Red Hat subsidiary JBoss using Oracle software and is due to roll out Dec. 31.
More
here.
U.S. Spy Chief: Eavesdrop Debate 'Will Cost Lives'
Randall Mikkelsen writes for Reuters:
A debate in Congress over eavesdropping on terrorism suspects will cost American lives by exposing intelligence techniques, the Bush administration's spy chief said on Thursday.
At a congressional hearing, National Intelligence Director Michael McConnell faced sharp questioning from Democratic lawmakers who deeply mistrust surveillance programs which the administration put in place after the Sept 11, 2001 attacks.
He said debate over the programs was important to ensure authorities had proper tools to fight suspected terrorists, but that the open discussion would also help U.S. enemies.
More
here.
What? U.S. Airport Screeners Are Watching What You Read

Ryan Singel writes on Wired News:
International travelers concerned about being labeled a terrorist or drug runner by secret Homeland Security algorithms may want to be careful what books they read on the plane.
Newly revealed records show the government is storing such information for years. Privacy advocates obtained database records showing that the government routinely records the race of people pulled aside for extra screening as they enter the country, along with cursory answers given to U.S. border inspectors about their purpose in traveling.
In one case, the records note Electronic Frontier Foundation co-founder John Gilmore's choice of reading material, and worry over the number of small flashlights he'd packed for the trip. The breadth of the information obtained by the Gilmore-funded Identity Project (using a Privacy Act request) shows the government's screening program at the border is actually a "surveillance dragnet," according to the group's spokesman Bill Scannell.
"There is so much sensitive information in the documents that it is clear that Homeland Security is not playing straight with the American people," Scannell said.
More
here.
Image source: MEMRI
Nightmare or Dreamscape? Security is Everyone's Problem
Munir Kotadia writes on ZDNet Australia:
It is not just the hackers, spam and DDoS activity we need to worry about. These days it isn't even safe to simply surf Internet because there is no way of knowing if a Web site has or hasn't been compromised -- take the IE-exploiting Facebook ad, for example, or the Sydney Opera House Trojan.
These are legitimate sites and yet people have most likely put themselves at risk by simply visiting them.
So how do you go about protecting your organisation in such a hostile environment? According to Graham Andrews, the CIO of PricewaterhouseCoopers, the task is "a nightmare".
More
here.
Image of the Day [2]: Don't Tase Me, Bro!

It has a life of it's own now. Go figure.
Via Boing Boing.
SecurityCartoon: Botnet Puppet Masters
Click for larger image.
Nice.
Via SecurityCartoon.com.- ferg
Quote of the Day: Chris Walsh
"If there's anything stupider than banning a woman from breastfeeding in public, it is banning a picture of a woman breastfeeding on the grounds that it is "obscene", which is what the morons at Facebook have done, as reported (for example) by the Toronto Star."
- Chris Walsh, writing on Emergent Chaos.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Wednesday, Sept. 19, 2007, at least 3,790 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,092 died as a result of hostile action, according to the military's numbers.
The AP count is seven higher than the Defense Department's tally, last updated Wednesday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
Hacker Decries U.S. & Israel On Vietnam Memorial Website
Josh White writes in The Washington Post:
A computer hacker promoting Turkish nationalism posted a video and message on a U.S. Vietnam memorial Web site in recent days, blocking one of the site's search functions while defacing the site with a statement against the United States and Israel.
Users of the Vietnam Veterans Memorial site -- at http://www.thewall-usa.com-- who searched for U.S. casualties by date were sent to an all-red Web page adorned with a symbol from the Turkish flag, a short video, and messages in Turkish and English. The English messages attacked Kurds, the United States, Israel and Armenia.
According to translations, the Turkish message read: "Is there any equal or likeness to our martyrs at Gallipoli?" It is an apparent reference to the Battle of Gallipoli in 1915 during World War I, during which soldiers from the Ottoman Empire repelled an Allied operation to capture Istanbul, suffering heavy casualties of more than 250,000. The video called it a "story written in blood."
A "Turk Defacer" took credit for the hack, which users reported yesterday to the FBI, the National Park Service and the 4/9 Infantry Manchu Vietnam Association, which maintains the site. The message was removed and the search function restored by last night.
More
here.
Industrial Cybercrime: Targeting Internet Hosting Services
Dan Sullivan writes on the McAfee Realtime Messaging and Web Security Blog:
It would seem that the cybercrime industry is bifurcated: there is the attack-the-unsecure-home-PC segment that goes after vulnerable Windows PCs and turns them into bots or infects them with keyloggers to steal bank account information; and then there is the segment that targets commercial and government operations, hacking databases, probing for vulnerabilities, disrupting operations with DDoS attacks (thanks to the botnets provided by the first segment), and either stealing data in bulk or going after targeted intellectual property.
I posted another comment today on comment on McAfee CEO David DeWalt's comment that cybercrime is now bigger than the drug trade. I'm thinking we're going to see more and more about the professionalization of cybercrime. At some point, we'll start to see the adoption of techniques that are used to combat professional, organized crime to how we control cybercrime.
More
here.
eBay Warning: Hacking Software Available in Auctions
A ComputerWorld article by Matthew Sainsbury, via PC World, reports that:
Programs covering the full range of hacking software, from Trojans to keyloggers to step-by-step tutorials on how to effectively hack Web sites and personal information have now entered auction house eBay, raising the concern of one security company.
"It's a simple matter of searching for it now" said Magida Ezzat, marketing communications manager at PC Tools.
"It's also very, very cheap - it's possible to even get it for free." Although the programs have become readily available on the Internet outside of eBay, the concern is that eBay is a site accessed by the general public, and the sale of hacking software through it is raising awareness with new audiences. "People don't need to be highly technical to access and use hacking software," Ezzat said.
Although awareness of how to obtain and use hacking software is on the rise, policing and preventing the sale of the software remains difficult.
More
here.
Outrage at the Possibility of Democratic Concessions on Wiretapping
Via EFF DeepLinks.
Should telecom companies like AT&T be given a “get out of jail free” card for their participation in the Bush administration’s warrantless wiretapping program? That’s what Director of National Intelligence Mike McConnell and Department of Justice Assistant Attorney General Ken Wainstein asked for on Tuesday in a House committee. Strangely enough, it appears that Congressional Democrats are seriously considering playing along.
As the New York Times reported in an article on the House committee hearings, “Democratic Congressional aides say they believe that a deal is likely to provide protection for the companies.”
Any deal of this sort is a direct attempt to affect EFF’s case against AT&T — in which we allege that the telecom giant participated in an illegal wiretapping program — as well as other pending lawsuits challenging illegal surveillance. But EFF isn’t the only group outraged by the willingness of Congressional Democrats to buckle at a moment’s notice…
More
here.
Federal Agent Indicted for Using Government Computer to Track Ex-Girlfriend
Connie Skipitares writes in The Mercury News:
A federal agent for the U.S. Department of Commerce is facing charges of illegally accessing computer information about a former girlfriend who jilted him and lying to government officials about it.
Benjamin Robinson, 40, of Oakland, was indicted today by a federal grand jury in San Jose on one count of unlawfully obtaining information from a protected computer and another count of making a false statement to his employer about his alleged acts. Robinson was a special agent for the U.S. Department of Commerce, Office of Export Enforcement, Bureau of Industry and Security.
Robinson is accused of logging on to the government's internal computer system at least 163 times over a period of months between mid-2003 and mid-2004 to track the travel patterns of the girlfriend who left him, and her family.
More
here.
ISPs Try on Anti-Botnet Services Model?
 Click for larger image.
Click for larger image.
Kelly Jackson Higgins
writes on
Dark Reading:
ISPs, under siege from increasingly more powerful and sophisticated botnet-based attacks, are fighting back -- with an anti-botnet business model.
Some service providers are looking at ways to productize their botnet research and investigations into anti-botnet managed security services -- a strategy designed to help them fund the buildout of more secure infrastructures that can better mitigate the attacks.
So far, anti-botnet services have mainly centered around distributed denial of service (DDOS) managed services that filter out and "scrub" traffic, such as AT&T's Internet Protect and Verizon Business's DoS Defense Mitigation. According to Arbor Networks's recent survey of ISPs, the number of service providers who offer managed security services jumped from six to 40 during the period of July 2006 through June of this year. And most were DDOS services, according to Arbor.
More
here.
Note: Well, I say
"Show Me".
Our
statistics, above, show that ISPs have a loooong way to go.
- ferg
U.S. Security Official Defends Satellite Surveillance Plan
Andrew Noyes writes on GovExec.com:
The Homeland Security Department has gone "above and beyond what is called for by law" in assessing potential privacy implications of its plan to coordinate the use of satellites for domestic surveillance, a high-ranking official told the agency's privacy advisory committee Wednesday.
John Kropf, Homeland Security's director of international privacy programs, said the department has conducted a full "privacy impact assessment" on the recently unveiled National Applications Office, even though security systems are exempt from the federal rule requiring such action.
His boss, Hugo Teufel, briefed the House Homeland Security Committee on the initiative earlier this month. The committee's chairman, Bennie Thompson, D-Miss., and others were outraged that they had not been told about the project before its existence was reported in the media.
Kropf indicated that the agency's 19-member privacy panel was kept in the dark until now. "You may have read about this in the paper," he told committee before briefly describing the plan. No members pressed him for additional details.
More
here.
GAO Study: Veterans Personal Data Still At Risk
An AP newswire article by Hope Yen, via Military.com, reports that:
Veterans' personal data and health information remain at risk of identity theft because the Veterans Affairs Department has yet to implement several safety measures, government investigators say.
The report by the Government Accountability Office, released Wednesday, comes more than one year after the VA pledged renewed security efforts after the loss of personal information for 26.5 million veterans and active-duty personnel.
It found that the VA had not yet fully secured access to its computer network and department facilities nor worked to ensure that only authorized changes and updates to VA computer programs were made.
Moreover, the VA has operated without a chief information security officer since June 2006 to oversee changes and still lacks clear and adequate procedures for quickly notifying veterans when their sensitive data is lost, the report said.
More
here.
Image of the Day: 'Don't Tase Me, Bro!'

Image source: Christina Arasmo, via Threat Level.
Off Beat: USSR Still Alive on Internet and Won't Go Quietly

James Kilner writes for Reuters:
Russian Internet enthusiasts are locked in a tussle with an international body over a relic of the Soviet past -- the .su domain name assigned to the country just before the Soviet Union collapsed.
The U.S.-based body that oversees the World Wide Web's structure, ICANN, says the name is out of date and wants to kill it off. But thousands of Internet users still use the suffix -- in part for its nostalgia value -- and are fighting to save it.
Though nearly 16 years have passed since the end of the Soviet Union, .su is increasingly popular with businesses, clubs and political groups and Russian lobbyists on Wednesday said they had started negotiations with ICANN to keep it.
"We want to try and save it," Alexei Platonov, director of the independent Russian Institute of Public Networks, which promotes technology use, said at a news briefing.
More
here.
Web Hosting Breach May Have Exposed Passwords for 6,000 Clients
Dan Goodin writes on The Register:
Layered Technologies has been targeted by malicious hackers who may have stolen passwords and other personal details on as many as 6,000 of its clients, the Texas-based web host provider warned. It is advising customers to change login credentials for all host details submitted in the past two years.
The Monday evening breach was executed by attacking an off-the-shelf application integrated into the company's support desk that manages help tickets submitted by customers, according to Layered Technologies President Todd Abrams. It remains unclear if the intruders actually took the information, but the attack had the potential to expose names, addresses, phone numbers, email addresses and server login details for five to 6,000 clients.
More
here.
Internet Pipes Not Quite Ready to Burst After All

Bob Brown writes on NetworkWorld:
Despite the fact that more people are dishing up video and other bandwidth-saturating content, Internet traffic growth rates are actually slowing down, according to a new Web site at the University of Minnesota.
The Minnesota Internet Traffic Studies (MINTS) site, which we first learned about late last year, shows that Internet traffic growth rates have settled in at about 50% to 60% in the United States and worldwide as the Internet matures. That’s a far cry from the doubling rates every year or even every 100 days that some like WorldCom claimed in the mid-to-late 1990s.
More
here.
Tap Dancing Around Wiretaps
Via EFF DeepLinks.
During yesterday's testimony before the House Judiciary Committee, the Director of National Intelligence Mike McConnell tap danced around a critical question about tapping communications. When asked how many Americans were tapped he responded only by saying "there is confusion of what the word tap means," and then downshifted his discussion to "targets." Unfortunately, Chairman Conyers' followup question asked changed the term again, asking who was "overheard."
If you listen closely, you'll hear a lot of semantic parsing in the Administration's testimony, careful word choices that obscure the truth. McConnell denies "spying on Americans," using an undefined term, but - when pressed - keeps his denial to warrantless surveillance "targeted" on Americans, and only after February of this year. "Overheard," "listening in," "spying," these are all words that missing the critical question - whether or not the feds have been collecting the communications of millions of ordinary Americans without a warrant as part of a massive domestic dragnet.
More
here.
Custom DDoS Capabilities Within Malware
 Click for larger image.
Click for larger image.:
DDoS capabilities within a malware are nothing new and are in fact becoming a commodity feature, but compared to the average DDoS-ers with up to two different DoS attack approaches, or the types of malware with hardcoded IPs to be attacked, there's a disturbing trend to diversify the DoS techniques used as much as possible to improve the chances of a successful attack, let's not mention the allocation of automatic self-defensive DDoS back at curious parties due to the oversupply of infected hosts.
As you can see in this particular malware -- high detection rate -- the DDoS variables within are not only diverse enough to cause a lot of damage, but also, simultaneous combinations are also possible.
More
here.
Image source: Dancho Danchev
'Coordinated' Hackers Steal Internet Retailer Customer Credit Cards
Sharon Gaudin writes on InformationWeek:
Despite running what he thought was a well-secured network, the president of a publishing company has disclosed that a "coordinated and sophisticated" group of hackers broke in and stole customers' credit card information.
Vertical Web Media said its network was breached in August and hackers made off with customers' names, addresses, phone numbers and e-mail addresses, along with credit card numbers and expiration dates. Jack Love, president of the Chicago-based publisher of Internet Retailer magazine added that only a portion of the company's customers were compromised because the data was pulled offline as soon as the publisher was alerted by a customer that there was a problem.
More
here.
Toon of the Day: What's The Worst That Could Happen?
Click for larger image.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Tuesday, Sept. 18, 2007, at least 3,787 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,092 died as a result of hostile action, according to the military's numbers.
The AP count is four higher than the Defense Department's tally, last updated Tuesday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
China's Cyber Attacks Signal New Battlefield Online

Larry Greenemeier writes on Scientific American:
The uproar over claims that the People's Republic of China launched a series of network-based cyber attacks earlier this month against the U.K., France, Germany, and the U.S. has died down. But few expect China to back off efforts to gain the upper hand in the battle of bits and bytes. China's own stated military goals include improving the country's ability to wage information warfare.
The most recent cyber attacks against the U.S. stand out because they were traced back to the Chinese government. "Normally it is not possible to attribute the source of an attack, because source addresses can be spoofed," says Alan Paller, director of research at the SANS (SysAdmin, Audit, Network, Security) Institute in Bethesda, Md., which trains and certifies technology workers in cyber security. In China's case, though, analysts tracked the cyber assaults to 20 computer workstations in China's Guangdong province, Paller says.
More
here.
Image source: ABC News
Firefox 2.0.0.7 'Fixes' QuickTime Attack Vector
Ryan Naraine writes on the ZDNet Zero Day Blog:
Mozilla has hurried out a new version of Firefox to block code execution attacks from Apple’s QuickTime media player.
The fix (Firefox 2.0.0.7) comes just six days after the release of proof-of-concept exploits to show how rigged QuickTime files can be used to hijack Windows machines if Firefox is set as the default Web browser.
More
here.
Off Beat: Did CIA Kidnap Vacationer? It's a State Secret
Warren Richey writes in The Christian Science Monitor:
In December 2003, German citizen Khaled el-Masri boarded a bus in Germany for a holiday in Skopje, Macedonia.
Instead of a restful vacation, the Muslim man of Lebanese heritage says he ended up in a Central Intelligence Agency isolation cell in Afghanistan as a suspected terrorist. He was released after five months of interrogation with no explanation justifying the action or apology if it was a mistake.
Now, nearly four years later, his lawyers are asking the US Supreme Court to examine whether the Bush administration has the power to prevent Mr. Masri from seeking recourse in American courts.
Masri's lawyers claim that the CIA kidnapped and tortured an innocent man. The government has never responded directly to the accusation. Instead, Justice Department lawyers asked a US judge to throw the case out of court to prevent disclosure of state secrets. He did.
More
here.
DoJ Testimony Alludes to Massive Scope of Wiretapping
Via EFF DeepLinks.
In a House Judiciary hearing today, Department of Justice Assistant Attorney General Ken Wainstein testified in support of the Administration's request to give the telecom companies a 'get out of jail free' card for their participation in warrantless wiretapping. Wainstein breathlessly warned that the telecoms might otherwise face "crushing liability." But the statutory penalties for warrantless wiretapping are relatively small per person -- even if AT&T was ordered to pay the maximum penalty, a few hundred illegal wiretaps would amount to less than a rounding error in the phone companies' quarterly statements (AT&T reported revenues of $29.4 billion for the quarter ending June 30).
If the NSA was truly limiting its spying to suspected terrorists, the potential liability would be like an annoying gnat on an elephant. So why are the companies so worried? Perhaps the telecoms are actually concerned because they helped the feds intercept the communications of millions of ordinary Americans.
More
here.
U.S. Spy Chief Seeks More Eavesdropping Power
An AP newswire article, via MSNBC, reports that:
The top U.S. intelligence official asked Congress Tuesday for even more changes to a law that he says has limited the government's ability to eavesdrop - not just on terrorists but also on more traditional potential adversaries.
Mike McConnell, the director of national intelligence, said China and Russia are aggressively spying on sensitive U.S. facilities, intelligence systems and development projects, and their efforts are approaching Cold War levels.
More
here.
House Committee Chair Wants Info on Cancelled DHS Data-Mining Programs
Jaikumar Vijayan writes on ComputerWorld:
Bennie Thompson (D-Miss.), chairman of the House Committee on Homeland Security, has asked Department of Homeland Security Secretary Michael Chertoff to provide a detailed listing of all IT programs that have been canceled, discontinued or modified because of privacy concerns.
He also asked for details on the amount of money the DHS spent on each program, the names of contractors who were awarded the projects, and information about the measures being taken to address privacy issues.
Thompson's demand was prompted by the recent cancellation of the agency's Analysis Dissemination Visualization Insight and Semantic Insight (ADVISE) data-mining program, which was shelved because of privacy concerns after $42 million had been poured into it. In a letter to Chertoff yesterday, Thompson expressed concern about the "apparent litany" of DHS programs that have been canceled or otherwise modified after millions of dollars have been spent because of a failure to assess their privacy ramifications early on.
DHS officials could not be reached for comment.
More
here.
Cisco Grabs Wireless Startup Cognio
Cassimir Medford writes on Red Herring:
Networking equipment market leader Cisco Systems on Tuesday said it plans to acquire wireless spectrum management startup Cognio for an undisclosed sum.
The acquisition of the seven-year-old, Germantown, Maryland-based Cognio steps up the pressure on Cisco’s smaller rivals in the still-emerging corporate wireless local area network market.
More
here.
Storm Worm Botnet Attacks Anti-Spam Firms
Sharon Gaudin writes on InformationWeek:
There's no need to warn the anti-spam researchers at the Spamhaus Project about the Storm worm authors' ability to launch massive denial-of-service attacks. They've been fending them off for several months. And they've lived -- or at least stayed online -- to tell the tale.
"It's been a pretty constant battle to stay online," Vincent Hanna, an investigator for the non-profit Spamhaus Project, told InformationWeek. "It's an arms race. They try something. We block it. They try something else. We block it. It goes on and on. Sometimes it's fine and sometimes we spend hours a day on this."
Spamhaus is one of the anti-spam organizations that have been targeted in recent months by the Storm worm authors. The malware writers have amassed a giant, international botnet of compromised computers. Estimates of its size range wildly -- from one or two million up to 50 million bots. Regardless of its specific size, though, security researchers say it's definitely large enough to wreak a lot of havoc with a company's network, a government agency, an ISP, or possibly even an entire country, if they use that illegal grid to launch a denial-of-service (DoS) attack.
More
here.
McAfee CEO: Cyber-Threats Outpace Security Measures
Richard Martin writes on InformationWeek:
Despite the increase in government compliance requirements and the proliferation of security tools, companies continue to underestimate the threat from phishing, data loss, and other cyber vulnerabilities, new McAfee CEO David DeWalt said Tuesday.
In a keynote address at the InformationWeek 500 conference in Tucson, DeWalt said "it's amazing how low the awareness is of cyber-security threats" among both government officials and corporate executives. "As the world has flattened, we've seen a significant amount of emerging threats from increasingly sophisticated groups attacking organizations around the world."
Citing recent highly publicized corporate data breaches that have beset major companies like Ameritrade, Citigroup, and Bank of America, DeWalt said that cyber-crime has become a $105 billion business that now surpasses the value of the illegal drug trade worldwide.
More
here.
The LOBSTER Project: Passive Internet Traffic Monitors Detect Attacks

Via TERENA News.
The LOBSTER project, which has developed a pilot European infrastructure for accurate Internet traffic monitoring, concludes this week with its final review on 18 September.
Within the past four months, the number of passive monitoring sensors installed in the LOBSTER infrastructure has risen to 50, with around 200,000 new cyberattacks being detected. This is in addition to the 400,000 attacks that were captured during the previous year, and reflects the expansion of the sensor network and improved detection methods.
Sensors are now deployed in several European countries, as well as Singapore and the United States. They continue to monitor more than 2 million IP addresses, with the aggregate traffic capacity on the monitoring links exceeding 75 gigabits per second. The locations of sensors in the network can be viewed using Google Maps, where a click on each icon allows their traffic data to be examined.
A selection of the cyberattacks captured by LOBSTER’s sensors have also had their payload traces anonymised and have been made publicly available for research purposes via an 'attack trace repository'.
More
here.
Gartner: 'Manage Your IT Risk or Lose Your Good Name'
Leo King writes on ComputerWorld UK:
Businesses must properly manage IT risks or face heavy damage to their strategic plans and their reputation, analysts have warned at Gartner’s IT Security Summit in London.
Many companies are failing to adjust their IT decision-making and risk management processes, Gartner said, despite the smooth running of IT becoming ever more integral to business success.
Gartner vice president Richard Hunter said: “IT risk has changed. Incidents now harm constituencies within and outside companies. They damage corporate reputations and expose weaknesses in management teams.
“Most importantly, uncontrolled IT risk dampens an organisation’s ability to compete.”
More
here.
The Threat of Reputation-Based Attacks
Brian Krebs writes on Security Fix:
CastleCops.com is accustomed to being attacked by online crooks: The volunteer-led cybercrime-fighting group has endured nearly a month long siege by thousands of criminally-controlled PCs aimed at crippling its Web site. So when the latest attack failed to prevent legitimate users from visiting the site, the bad guys unveiled an unlikely secret weapon: bogus donations.
The unauthorized contributions all came in via PayPal, the online payment service owned by eBay. Some were sent via PayPal accounts that attackers had hijacked in phishing scams; others were submitted through PayPal's e-check option using compromised checking account numbers. A few donations were for as little as $1, while other fake donations ranged as high as $2,800.
To the victims of the stolen PayPal accounts, it looks as if CastleCops is the one stealing their money, when in reality, it's the attackers. Also, the fraudulent activity seeks to ruin their relationship with PayPal.
More
here.
Consumers Unhappy With E-Commerce Experiences
A ComputerWorld article by Linda Rosencrance, via PC World, reports that:
Despite the growth of e-commerce, consumers are still unhappy with their online experiences, with nearly nine out of 10 saying they have had problems conducting transactions online, according to a new survey.
The Harris Interactive survey also found that 42 percent of consumers who have problems during transactions end up abandoning them or taking their business to another online company.
Customer service centers also took a blow: 76 percent of users who said they had had a bad customer service experience stopped doing business with the company, cut the amount of business they do with the company or complained to the Better Business Bureau.
More
here.
Gapingvoid: Chaos
Via gapingvoid.com. Enjoy!

Tor Node Operator After Run-In With Police: 'I Can't Do This Any More'
Ryan Paul writes on ARS Technica:
Alexander Janssen, a Tor node operator located in Germany, has shut down his node after a second confrontation with police several months ago. Law enforcement agents entered Janssen's home, handcuffed him, and searched the premises.
Janssen was informed that he was a suspect in a bomb threat investigation involving an Internet forum. He was then taken to the police barracks where he was interrogated. After Janssen was released, a German state security official informed him that the detainment was a misunderstanding.
More
here.
U.S. Spy Chief: China, Russia Spying on U.S.
An AP newswire article by Pamela Hess, via The Boston Globe, reports that:
China and Russia are spying on the United States nearly as much as they did during the Cold War, according to the top U.S. intelligence official.
Mike McConnell, the director of national intelligence, says in testimony prepared for a Tuesday congressional hearing that a law passed last month expanding the U.S. government's eavesdropping power is needed to protect not just against terrorists but also against more traditional potential adversaries, such as those two Cold War foes.
"China and Russia's foreign intelligence services are among the most aggressive in collecting against sensitive and protected U.S. systems, facilities and development projects, and their efforts are approaching Cold War levels," McConnell says in his testimony. "Foreign intelligence information concerning the plans, activities and intentions of foreign powers and their agents is critical to protect the nation and preserve our security."
The new law will also enable the intelligence agencies to identify "sleeper cells" of terrorists in the United States, according to McConnell's statement to the House Judiciary Committee.
More
here.
U.S. Toll in Iraq
Via The Boston Globe (AP).
As of Monday, Sept. 17, 2007, at least 3,782 members of the U.S. military have died since the beginning of the Iraq war in March 2003, according to an Associated Press count. The figure includes seven military civilians. At least 3,086 died as a result of hostile action, according to the military's numbers.
The AP count is nine higher than the Defense Department's tally, last updated Monday at 10 a.m. EDT.
More
here.
And as always,
cryptome.org keeps a very, very extensive list
here, as does the
Iraq Coalition Casualty Count website
here.
NYT (Finally) Ditches Pay Firewall for Content
An AP newswire article by Seth Sutel, via SFGate.com, reports that:
The New York Times is scrapping a two-year-old program to charge fees for access to parts of its Web site, including op-ed columnists and archives dating back to 1987.
As of midnight Tuesday, the Times will discontinue its TimesSelect feature, which cost $49.95 per year or $7.95 by the month. Home delivery subscribers were able to sign up for free.
The Times announced the decision late Monday after a story about it appeared on the paper's Web site.
The move reflects a growing shift in thinking in the media industry, where it had once been thought that charging for access to some or all of a Web site was the best strategy for making money.
More
here.
Quote of the Day: Jack Cafferty

"I bought the whole song and dance about WMDs. I was caught up in the national hysteria that followed 9/11, and was captive to the political manipulation, if you will, that took place of all of us."
"I was drinking the Kool-Aid on the run-up to that war."
- Jack Cafferty, who I very much admire for his honesty and curmudgeon-ness.
Report: Attacks on ISP Nets Intensifying
Kelly Jackson Higgins writes on Dark Reading:
Increasingly-intense distributed denial-of-service (DDoS) attacks on ISP backbones are surpassing providers' capacity and knocking customers offline, according to a new survey of service providers by Arbor Networks.
While most large ISPs have upgraded their backbones to 10-Gbit/s speeds over the past two years, three respondents said they have experienced sustained attacks from 20- to 22 Gbit/s, and one hosting services provider in the survey reported a 24-Gbit/s DNS-targeted attack. The most powerful sustained attack previously was 17 Gbit/s, which was reported in last year's survey by Arbor.
Thirty-six percent of the ISPs that responded to the survey -- which covers activity from July 2006 through June 2007 -- had suffered from sustained attacks of 1 Gbit/s or more over the past 12 months.
More
here.