Programming Note: Light Posting Next Week - ISOI V
 Tallinn, Estonia
Tallinn, EstoniaPosting to the blog will probably light to almost non-existent next week, as I am traveling to
Tallinn, Estonia, tomorrow for (among other things) meetings with the Estonian CERT (
CERT-EE) and the 5th Internet Security Operations and Intelligence meeting (
ISOI V).
I'll try to post as the situation and time allows, but posting will probably not get back to normal until the following week.
Cheers,
- ferg
Israeli Hacker Known as 'The Analyzer' Suspected of Hacking Again
Kim Zetter writes on Threat Level:
Canadian authorities have announced the arrest of a 29-year-old Israeli named Ehud Tenenbaum whom they believe is the notorious hacker known as "The Analyzer" who, as a teenager in 1998, hacked into unclassified computer systems belonging to NASA, the Pentagon, the Israeli parliament and others.
Tenenbaum and three Canadians were arrested for allegedly hacking the computer system of a Calgary-based financial services company and inflating the value on several pre-paid debit card accounts before withdrawing about CDN $1.8 million (about U.S. $1.7 million) from ATMs in Canada and other countries. The arrests followed a months-long investigation by Canadian police and the U.S. Secret Service.
Tenenbaum faces six counts of fraudulent use of credit card data and one count of fraud over $5,000. He remains in custody in Calgary without bail, though the three other suspects -- Priscilla Mastrangelo, 30, Jean Francois Ralph, 28, and Sypros Xenoulis, 33 -- have been released on bond, according to a Canadian media report.
An Israeli media outlet contacted Tenenbaum's mother, but she didn't know if it was her son who had been arrested. She told the reporter that her son spends time in France and Canada and that she tried to contact him after news of the arrest went public, but she was unable to reach him.
More
here.
U.S. Spy Agencies Prepare for Administration Change
Ben Bain writes on FCW.com:
The next president will inherit the new structure, which includes the Office of the Director of National Intelligence (ODNI) as the head of that community, and a workforce that has gotten younger and larger since 2001.
Sen. Barack Obama (D-Ill.) received an ODNI briefing Sept. 2, and ODNI has also offered one to Sen. John McCain (R-Ariz.). President Bush recently authorized ODNI to begin briefing the candidates on topics at their request, said Tom Fingar, ODNI’s deputy director for analysis. As senators, both candidates have already had clearance to access to intelligence assessments.
“One of the bottom line realities is that [ODNI] has never before been through a transition,” Fingar said last week at the Intelligence and National Security Alliance’s Analytic Transformation 2008 conference in Orlando, Fla. “And simple questions like how many and which members of the senior staff are expected to hand in letters of resignation or expected to stay on into the next administration or to be around for just a period of transition,” have no precedent.
Roughly 55 percent to 60 percent of the people in the intelligence community have joined just since the 2001 attacks, and many on ODNI’s staff are on detail from other agencies, Fingar said.
More
here.
Researchers Use Facebook App to Create Zombie Army
Ryan Singel writes on Threat Level:
Computer researchers built a tool that silently turns Facebook users into a powerful zombie army that can attack other websites or scout for vulnerable sites on the net.
All that is necessary to create the Facebook Botnet is to have users choose install a rogue Facebook application written by an outside developer -- in this case, one called Photo of the Day.
Once the user chooses to install the application, the unsuspecting user is inducted into the hacker's army and unknowingly follows orders any time he or she logs into Facebook.
The researchers -- mostly affiliated with the Greece-based Institute of Computer Science -- describe their innovation in a paper [.pdf] as a demonstration of an "anti-social network" -- essentially a hijacked social network that can be used for a number of nefarious purposes.
More
here.
Note: See related articles on this issue at
Dark Reading and the
ZDNet "Zero Day" Blog.
-ferg
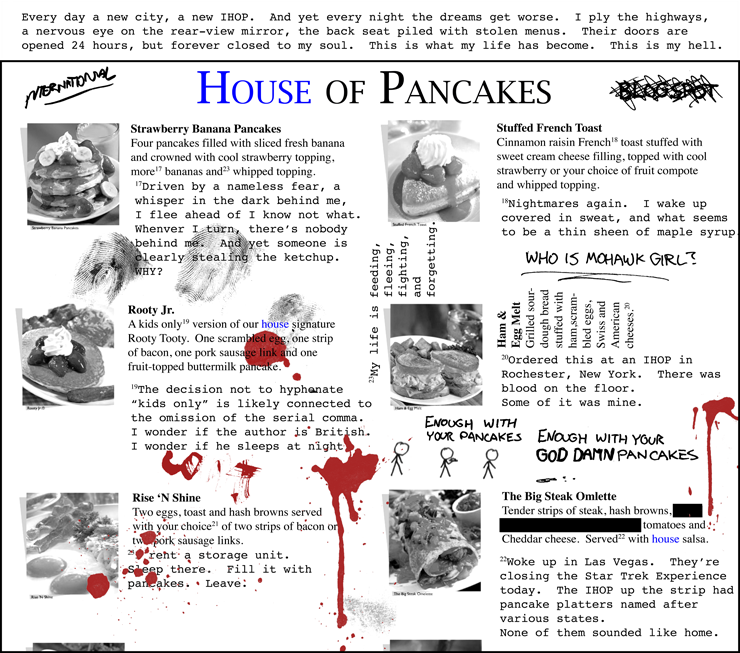
Pulp xkcd: House of Pancakes
Click for larger image.
Yes, we absolutely love
xkcd!
Enjoy!- ferg
U.S. Telecom Reporting Rule May Be Eased
Cecilia Kang writes in The Washington Post:
Phone giants AT&T, Verizon Communications and Qwest today are expected to win approval to report less information to the Federal Communications Commission on such matters as consumer complaints and infrastructure investments.
A decision by the FCC to curtail the information may, however, open the gates for a broader review of data collected by the commission and could be expanded to include cable, satellite and wireless phone providers that are not currently required to submit similar reports.
The reports offer rich details into the number of consumer complaints, waiting times for repairs and money put into technological upgrades by the largest phone service providers.
As consumers rely more on technology -- spending $150 to $200 a month per household on Internet, phone and television services -- consumer groups say the reports are often the only source for detailed data that show how the providers are responding to service complaints and whether companies are investing enough in upgrading their networks.
More
here.
French Issue Call to Storm 'Electronic Bastille'
A Reuters newswire article by Estelle Shirbon, via MSNBC.com, reports that:
Opposition to a new security database is gaining momentum in France as people return to work after a summer break during which the government authorized the state to store personal information on people as young as 13.
The decree creating the "Edvige" electronic database appeared in the official gazette on July 1, when the country was winding down for the summer, but news of its content has been gradually filtering out and is now stirring fierce criticism.
More
here.
Whistleblower Prompts Review of German Data Protection Laws
Joel Hruska writes on ARS Technica:
Germany's Interior Minister, Wolfgang Schäuble, vowed today to tighten the laws governing how data on German consumers can be gathered, sold, and traded. Schäuble's declaration comes after a call center whistleblower, Detlef Tiegel, handed a CD containing the banking details of some 17,000 German citizens over to the authorities. The information in question had been obtained (possibly purchased) by the unidentified company that employed Tiegel. The initial 17,000 records were only a fraction of the roughly 1.5 million records Tiegel claimed he could produce.
German officials took the man's claims seriously enough to open their own investigation, and were dismayed when they were able to purchase 6 million records of personally identifiable information (PII) for a paltry €850 (~$1,220). Minister Schäuble called a meeting today in Berlin to address the situation and share his concerns with multiple ministers within the German government. Attendees included data protection commissioner Peter Schaar, Justice Minister Brigitte Zypries, Economy Minister Michael Glos, and Consumer Affairs Minister Horst Seehofer. Representatives from several German states were also in attendance.
More
here.
TIGTA: The IRS Lacks Secure Web Servers
Mary Mosquera writes on FCW.com:
Unauthorized and insecure Web servers connect to the Internal Revenue Service’s network, which puts the agency’s computers and entire network at risk of unauthorized access to taxpayer and personally identifiable information, the Treasury Inspector General for Tax Administration said in a recent report.
The IRS has 1,811 unapproved internal Web servers on the network and 2,093 internal Web servers that have some security weaknesses, the TIGTA report, released Sept. 3, states.
The IRS requires that business units register all internal Web sites and Web servers with the Modernization and Information Technology Services organization, but some fail to register their servers, the report states. The IRS might block unregistered servers from sharing information with the network.
Because no office had responsibility for the Web registration program, the IRS has not enforced the requirement, allowing Web servers to connect to the network without proper authorization and accountability, the report states.
More
here.
GAO: U.S., Canada Can't Agree on Fingerprints, Info Sharing
Alice Lipowicz writes on FCW.com:
Negotiations between U.S. and Canadian officials about a proposed joint border management office broke down last year because the officials disagreed on the authority to collect travelers’ fingerprints and share their information, according to a new Government Accountability Office report [.pdf].
DHS and Canadian officials jointly terminated talks in April 2007 because they could not resolve several major issues, including U.S. demands for sovereign authority to take fingerprints and share applicants’ information with law enforcement agencies, the GAO report states.
More
here.
Hackers Break Into UAE Credit Network to Fund U.S. Purchases
Hugh Naylor writes in TheNational.ae:
An international investigation is under way to find hackers believed to have stolen information from financial servers in the UAE to make fraudulent credit and debit card purchases in the US.
The scheme came to light after a number of employees at the US Embassy – and a handful of other US citizens – had unauthorised purchases show up on their credit and debit cards in recent months, prompting the embassy to issue a warning on its website.
"To date, all of the reported fraudulent charges have been made from the United States," the message said. "We are aware of no fraudulent transactions originating in the UAE."
MasterCard is co-operating with law enforcement officials and banks to investigate the issue, Chris Monteiro, the head of the company’s worldwide communications, wrote in an e-mail.
Visa, when contacted, did not respond to questions or comment on the case.
More
here.
Hat-tip: Pogo Was Right
Forrester: Data Security Now 10% of IT Operating Budgets
Jon Brodkin writes in NetworkWorld:
IT security budgets are on the rise, reflecting growing concern over data breaches and increasing CEO involvement in the task of protecting sensitive data, Forrester Research analysts say.
Ten percent of IT operating budgets is devoted to security in 2008, an increase from 8% last year, a Forrester study released Thursday revealed. In a survey of 1,255 security decision-makers at North American companies, 21% expect to increase IT security spending in 2009, compared with 6% who expect security spending to decrease. The rest will keep their security budgets stable.
More
here.
Ex-U.S. Spy Recalls Years On No-Fly List
Randall Mikkelsen writes on the Reuters Global News Blog:
Decades of passing lie detector tests and the most stringent background checks count little when it comes to the U.S. no-fly terrorist watch list, the Pentagon's former spy chief recalled on Monday.
Retired Lt. Gen. Patrick Hughes, once the director of the Defense Intelligence Agency and a top Homeland Security Department intelligence official, said after he entered the private sector in 2005 he was denied boarding on a flight because his name was on the no-fly list. It has taken him ever since to clear up the confusion.
Security screenings were nothing new to Hughes — he said had passed them going back to the 1960s — but he was stopped short when the watch list flagged an Irish Republican Army member with the same name.
"It’s all about the name. I don’t see anything really subversive about Patrick... Hughes, but it appears there’s an IRA guy out there who has the same name. Probably equally handsome," he said.
Hughes's was one of about 50,000 names on the no-fly list, which has mushroomed since the Sept. 11 attacks, when it contained just 16 people considered threats to aviation.
More
here.
Vice Chief of U.S. Cyber Command Reassigned
Bruce Rolfsen writes in The Air Force Times:
The Air Force’s latest reassignment list for general officers reflects the service’s move away from an independent cyber command.
The provisional command’s vice commander, who has been on the job for one month, is being reassigned to the Pentagon, the Air Force said in an Aug. 29 statement. No replacement was named.
Maj. Gen. Randal D. Fullhart, who assumed the vice commander post in August, is moving to the Air Staff to join the Office of the Assistant Secretary of the Air Force for Acquisition as director of global reach programs. Fullhart is a career mobility pilot, but he served with the National Security Agency as the deputy chief for the Central Security Service for two years before moving to the cyber post.
The service’s plans to establish a cyber command were put on hold in August as newly appointed Chief of Staff Gen. Norton Schwartz and acting Secretary of the Air Force Michael Donley began a wide-ranging review of projects advocated by the leaders they replaced, now-retired Gen. T. Michael Moseley and former secretary Michael Wynne.
More
here.
Hat-tip: InfoSec News
Mark Fiore: Fun With John & Sarah

Perhaps the most brilliant Mark Fiore creation. Ever.
Via The San Francisco Chronicle.
Enjoy!
- ferg
UN e-Mail Hacker Jailed
John Leyden writes on The Register:
A worker who hacked into his UN diplomat boss's email account has been jailed for three months.
The 24-year-old Egyptian was jailed in Abu Dhabi after he was convicted of breaking into a personal email account set up by a UN worker from the UAE and threatening to expose her sensitive private information, ArabianBusiness.com reports. The miscreant - named only as MN - was employed as the woman's secretary at the time he gave his victim a two-day ultimatum to meet his demands or risk the exposure of private emails and pictures.
The would-be blackmailer faces deportation after he serves his time behind bars, news monitoring service Periscope IT adds. His victim found out that many of her files had been accessed when she contacted her service provider to reset her password after realising she'd been locked out of her account.
More
here.
UK Crime Fighters Grapple With iPhone Wipe Threat
Nick Heath writes on Silicon.com:
Criminals can remotely destroy incriminating evidence by exploiting security features on the Apple iPhone, a leading digital forensics expert has warned.
The head of the Serious Fraud Office digital forensics unit Keith Foggon cautioned that the ability to remotely wipe the iPhone and other smart phones used by enterprises could be exploited by lawbreakers.
Foggon said: "The 3G iPhone is brand new, there are not many tools for dealing with it and it can be remotely wiped. It's a bit like the BlackBerrys where users can carry out remote deletion."
He added the unit took precautions to guard against the feature being exploited. "Because we isolate the devices immediately, and never reconnect them to their network, the remote wiping capability does not present us with much of a problem," he noted.
More
here.
Scandal As UK Crime Domain Sold to German
Tom Jowitt writes on TechWorld:
The now-defunct government agency responsible for investigating computer crime, the NHTCU, no longer owns its domain name after it was sold to an enterprising German internet marketer.
The National Hi-Tech Crime Unit (NHTCU) was established in 2001 to fight high tech crime, but its duties came to an abrupt end in April 2006, when it was transferred to the Serious Organised Crime Unit (SOCA).
While the ownership of a defunct website does not sound overly troublesome, it a serious issue, because many websites around the world still have links pointing to the old NHTCU website. This includes a link to the old NHTCU website on the Home Office's own web pages.
More
here.
3,400 Ballots Missing in Florida Election: Recount Flips Race
Kim Zetter writes on Threat Level:
Palm Beach County, Florida, is in the news again for another election mishap. This time the culprit isn't the county's infamous butterfly ballot that made headlines in the 2000 presidential race. Instead, the problem is ballots used with the county's new $5.5 million optical-scan machines made by Sequoia Voting Systems.
More than 3,000 optical-scan ballots have mysteriously disappeared since the county held an election last Tuesday.
According to tallies a week ago, a total of 102,523 ballots were cast in the election. But according to a recount of one of the races, which was completed this last Sunday, the total number of cast ballots was only 99,045 -- a difference of 3,478. Election officials say they can't explain the discrepancy, though critics are concerned that this is a precursor to problems that could arise in the November presidential election.
More
here.
Controversy Snarls Upgrade Of Terrorist Data Repository
Robert O'Harrow Jr. writes in The Washington Post:
A major effort to upgrade intelligence computers that hold the government's master list of terrorist identities is embroiled in controversy about the project's management and the work of contractors hired for the job, documents and interviews show.
The Terrorist Identities Datamart Environment, or TIDE, serves as the central repository of information about more than 400,000 suspected terrorists around the world. Operating at the National Counterterrorism Center, TIDE and other systems each day deliver files of information to watch-list programs that screen people traveling into the United States, or they make data available online to intelligence analysts across the government.
Authorities said TIDE has revolutionized many national security tasks. But because it was built quickly after the Sept. 11, 2001, terror attacks, it is limited and lacks many features needed by the intelligence community, documents show. Those limitations in TIDE and related systems hamper the ability of intelligence analysts to discover patterns and make connections among the growing pools of data they amass from around the world. TIDE also has suffered periodic outages of up to two hours, according to interviews with government officials and contractors involved with the project.
More
here.
Number of Botnet-Infected PCs Jumps Four-Fold in 90 Days
Shaun Nichols writes on vnunet.com:
The number of computers currently controlled by botnets has exploded in recent months, say researchers.
Recent figures recorded by the Shadowserver Foundation revealed that in the last 90 days, the number of computers infected by botnets has quadrupled.
The increase comes despite a slight drop in the number of botnets, leading researchers to believe that the increase has largely been to the benefit of the large, established operators in the market.
The increase has also come despite little to no increase in the volumes of new malware and viruses being discovered in the wild, leading some researchers to believe that computers are being infected through web-based attacks, most specifically, SQL injection.
More
here.
Google Chrome Vulnerable to 'Carpet-Bombing' Flaw
Ryan Naraine writes on the ZDNet "Zero Day" Blog:
Google’s shiny new Web browser is vulnerable to a carpet-bombing vulnerability that could expose Windows users to malicious hacker attacks.
Just hours after the release of Google Chrome, researcher Aviv Raff discovered that he could combine two vulnerabilities — a flaw in Apple Safari (WebKit) and a Java bug discussed at this year’s Black Hat conference — to trick users into launching executables direct from the new browser.
Raff has cooked up a harmless demo of the attack in action, showing how a Google Chrome users can be lured into downloading and launching a JAR (Java Archive) file that gets executed without warning.
In the proof-of-concept, Raff’s code shows how a malicious hacker can use a clever social engineering lure — it requires two mouse clicks — to plant malware on Windows desktops.
The Google Chrome user-agent shows that Chrome is actually WebKit 525.13 (Safari 3.1), which is an outdated/vulnerable version of that browser.
Apple patched the carpet-bombing issue with Safari v3.1.2.
More
here.
Skype Ignoring PayPal-Siphoning Hijack Scheme?
Dan Goodin writes on The Register:
One day last month, when Klaus Zimmerman tried to log into his Skype account, he got an error message indicating his username and password didn't match. Concerned something was awry, Zimmerman, a computer repairman living in Wexford County, Ireland, phoned his brother and asked him to check his online status.
"I saw you on earlier, but your picture was gone," the brother reported. "You're now listed as living in Germany." On top of that, the person logged in was no longer answering the brother's queries.
Forum threads [...] and Google searches [...] suggest Zimmerman's experience is by no means unusual. The Register has contacted many victims, and a common pattern has emerged. Around the same time the victims are locked out of their accounts, they receive emails indicating their PayPal accounts are being charged for funds that are credited to the purloined Skype accounts. Frantic emails reporting the problem remain unanswered for weeks or months by Skype and PayPal representatives.
More
here.
Love of Cats Was Six Flags Hacker's Downfall
David Kravets writes on Threat Level:
A San Francisco hacker faces up to 10 years imprisonment for intruding into the computers of theme park giant Six Flags, posting a message of love for his girlfriend and inundating the company with bot-produced job applications reading "THIS SITE WAS HACKED."
Over a five-day period in 2004, Mark Kahn, 27, left messages in the amusement park company's network to his girlfriend: "I Love you, Laura," the authorities said.
The IP address from where the hacking originated were traced to web sites used by Kahn, including his personal web site where he posted blogs, pictures of his girlfriend Laura and pictures of cats, according to South Carolina U.S. Attorney W. Walter Wilkins, South Carolina's U.S. attorney.
One picture of a cat helped the authorities nab Kahn, who pleaded guilty last week to one count of hacking. Authorities enlarged one picture with a cat on a keyboard and saw a web address to a site in which the hacker described the intrusion.
More
here.
In Passing: Don LaFontaine

In Passing: Jerry Reed

S.Korean Army Officers Targeted by N.Korean Spyware
Via Chosun.com.
A North Korean spyware e-mail was reportedly transmitted to the computer of a colonel at a field army command via China in early August. The e-mail contained a typical program designed automatically to steal stored files if the recipient opens it. It has not been confirmed whether military secrets were leaked as a result of the hacking attempt, but their scale could be devastating given that the recipient is in charge of the South Korean military's central nervous system -- Command, Control, Communication, Computer & Information (C4I).
The incident shows that North Korea has enlarged its list of hacking targets to officers at field army commands, in addition to the homepages of Cheong Wa Dae, the Defense Ministry and top military brass to steal South Korean military secrets.
It is also evident that Won Jeong-hwa, who was arrested for posing as a defector while spying for the North, delivered the name cards of 100 South Korean military officers she had collected to a North Korean official. Some officers whose email addresses are on their name cards have suffered hacking attacks. Early this year, a National Security Council official lost files stored in his computer after a hacking attack from China. North Korea has clearly widened the scope of cyber attacks.
More
here.
Hat-tip: Graham Cluley
Quote of The Day: Matthew Rosenquist
"Security policy is like a seatbelt. It will not protect you every time, but it is guaranteed to fail if you choose not to use it."
- Matthew Rosenquist, writing of his Fortune Cookie advice for August on the IT@Intel Blog.
Fringe: Beer Maker Wins Fight to Market 'Legal Weed'

Eric Bailey writes in The Los Angeles Times:
The brewer who dared market "Legal Weed" has won.
Vaune Dillmann took on federal regulators this year when they ordered his Mt. Shasta Brewing Co. in the Northern California town of Weed to stop topping beer bottles with caps bearing the play on words, "Try Legal Weed."
Regulators cited federal law prohibiting drug references on alcoholic beverages.
A plain-talking 61-year-old former cop, Dillmann refused to back down, and his high-spirited appeal drew widespread media attention as well as support from beer lovers and civil libertarians far and wide.
Now, facing a storm of bad publicity and the prospect of a drawn-out court battle, authorities at the federal Alcohol and Tobacco Tax and Trade Bureau have quietly reversed course. The agency finalized approval of Dillmann's controversial cap Thursday.
More
here.
'Cyber War' Fears Grow After Georgia Websites Attacked
Via NewScientist.com.
Attacks that hit Georgian government and news websites after Russian tanks rolled across the border into South Ossettia last month have US officials concerned that bands of independent "cyber militias" will increasingly wield power over international relations.
The attacks in Georgia were distributed denial of service (DDoS) attacks that coordinate many computers to request information from a website simultaneously, causing it to crash or work only sporadically.
The Georgian government accused the Kremlin, saying the attacks were part of its war plan. US analysts agree they originated in Russia but say they were more likely the work of politically motivated hackers, dubbed "hacktivists".
US government officials are worried that groups with little or no connection to any state can now assert such influence. "In future warfare, governments aren't going to be the only ones waging war," said a senior US military official, who wished to remain anonymous.
More
here.
Happy Labor Day

North Pole Becomes An 'Island' For First Time in History

Fiona Macrae writes in The Daily Mail:
The North Pole has become an island for the first time in human history.
Startling satellite pictures taken three days ago show that melting ice has opened up the fabled North-West and North-East Passages - making it possible to sail around the Arctic ice cap.
The opening of the passages has been eagerly awaited by shipping companies which hope they will be able to cut thousands of miles off their routes.
But to climate change scientists it is yet another sign of the damage global warming is inflicting on the planet.
Mark Serreze, a sea ice specialist, described the images as an 'historic event' - but warned they added to fears that the Arctic icecap has entered a 'death spiral'.
More
here.
Image source: Daily Mail
California Bill Forces Retailers to Protect Data
An AP newswire article, via The San Jose Mercury News, reports that:
Retailers in California would not be allowed to store customers' personal information unless they took stringent steps to prevent identity theft under a bill state lawmakers approved Sunday.
Assemblyman Dave Jones, D-Sacramento, said many businesses fail to take even the most basic measures to protect that information, creating an opening for identity thieves.
His bill would prohibit, under most circumstances, any company that takes credit card or debit card information from retaining account numbers, verification codes or personal identification numbers.
Companies that do keep the information, such as those that accept recurring payments, would be required to follow specific guidelines to protect it. Those guidelines were established by the credit card industry.
More
here.
Off Topic: GOES Watches Gustav

We're watching this monster closely. It's looking quite perilous in the Louisiana Gulf region, and New Orleans especially.
Via The U.S. National Weather Service GOES Eastern US SECTOR IR Image at 00:15 UTC, 31 August 2008.
More later.
- ferg
ACH Fraud: The Bank Account That Sprang a Leak
Diana B. Henriques writes in The New York Times:
[What is at issue...] is called automated clearing house fraud, theft involving unauthorized electronic transfers through the automated networks of the circulatory systems that connect the world’s bank accounts.
When a consumer writes a check, the merchant that accepts it is entitled to have the specified amount taken from the customer’s bank account and sent electronically to the merchant’s account.
But once someone has certain routing numbers for a customer’s account, fraudulent transfers become possible unless the customer carefully scrutinizes all of the transactions on the monthly account statement.
If the consumer reports a clearly unauthorized transaction within 60 days, federal banking rules require the bank to cover the loss, Ms. Hillebrand said. If not, and if the bank informed the customer in advance about the 60-day deadline, the bank has no liability.
More
here.
Hat-tip: /.
Russian Web Dissident Killed
A Reuters newswire article, via InformationWeek, reports that:
The owner of an opposition Internet news site in Russia's troubled Ingushetia region was shot dead on Sunday after police detained him, his colleagues said.
Magomed Yevloyev, owner of the Ingushetiya.ru Internet site, was a vocal critic of the region's Kremlin-backed administration which is accused by critics of crushing dissent and free speech.
Interfax quoted the Russian prosecutor's office as saying an investigation into the death had been launched.
A posting on Yevloyev's site -- which has been the subject of repeated official attempts to close it down -- said he was shot after police detained him when he landed in Ingushetia's airport.
It said he was taken to hospital but died from his injuries. The site also called on "all those who are not indifferent" to his killing to gather for a demonstration in Nazran, Ingushetia's biggest town.
More
here.
Note: According to a
report on
RIA Novosti, the police say he was "shot accidentally".
Hat-tip: IntelFusion.net. -ferg
Mortgage Fraud Up Sharply - Internet Is Key Facilitator
Kenneth R. Harney writes in The Los Angeles Times:
A benchmark quarterly study released Monday by the mortgage industry's principal compiler of fraud reports, the Mortgage Asset Research Institute, or MARI, found that the number of cases jumped by 42% between the second quarter of 2007 and the same period this year.
Tough market conditions appear to increase pressures to commit fraud, said institute Vice President Merle D. Sharick.
"Mortgage fraud used to be a crime of opportunity," he said. "Now it's a crime of necessity for people who are desperate to maintain lifestyles they became accustomed to" during the housing boom years.
The Internet is a key facilitator of their activities, Sharick said, with "dozens of sites" hawking fake income and employment verifications, tax filings, credit scores, deposit verifications and other forms of deception.
More
here.